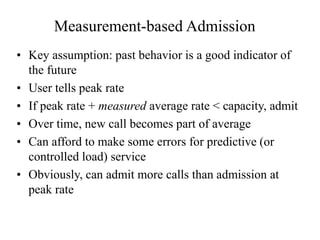
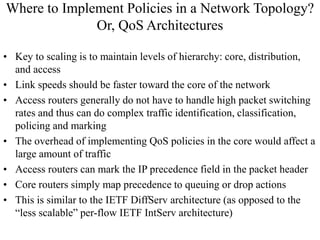
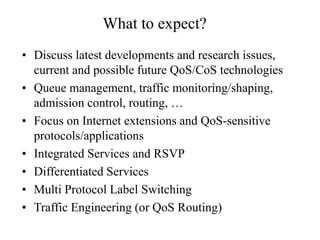
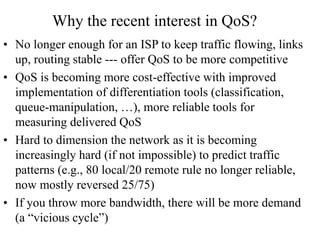
This document discusses quality of service (QoS) networking. It will cover topics like queue management, traffic shaping, admission control, routing protocols, Integrated Services, Differentiated Services, MPLS, and traffic engineering. The course will include proposals, paper presentations, quizzes, and participation. QoS aims to provide predictable network performance by prioritizing some types of traffic over others. It allows resources to be allocated to high priority services at the expense of lower priority traffic. The document discusses challenges in providing these guarantees and techniques like resource reservation, traffic contracts, scheduling algorithms, and statistical approaches.





![Why end-to-end control not enough?
• Problem: with common FCFS schedulers at routers, delay and delay
variance increase very rapidly with load
• For an M/M/1 model:
average delay = 1 / [ServiceRate - ArrivalRate]
= 1 / [ServiceRate (1 - Load)]
delay variance = 1 / [ (1 - Load)]
• As load increases, buffer overflows and router starts dropping packets
• Solution: TCP reduces load (slow start and congestion avoidance
algorithm)
• 2 TCP users on different hosts sharing the same bottleneck may get
different share of the bandwidth (uncontrolled unfairness) ==>
users should not trust network
• Some users may not “play by the rules” and reduce their sending rates
upon congestion, i.e. not TCP-friendly sources like a voice or video
UDP-based application ==> network should not trust users
2
e
ServiceRat](https://image.slidesharecdn.com/qosintro-230417091735-9f6d6974/85/QoSintro-PPT-8-320.jpg)


![Token Bucket
• Allows “bounded” burstiness
• Tokens generated at rate “rho” are placed in bucket with
depth “sigma”
• An arriving packet has to remove token(s) to be allowed
into the network
• A flow can never send more than [sigma + rho * t] over an
interval of time t
• Thus, the long-term average rate will not exceed rho
• More accurate characterization of bursty flows means better
management of network resources
• Easy to implement, but harder to police
• Can add a peak-rate leaky bucket after a token bucket](https://image.slidesharecdn.com/qosintro-230417091735-9f6d6974/85/QoSintro-PPT-12-320.jpg)