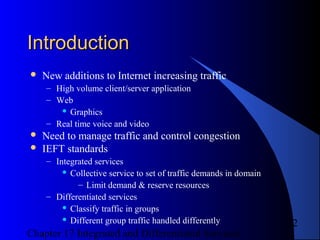
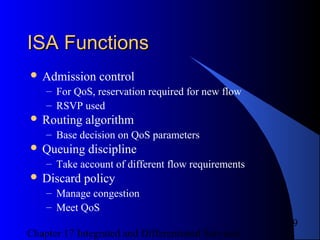
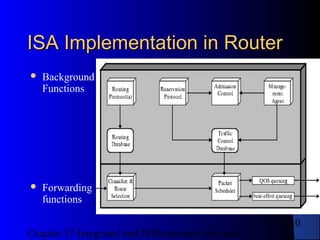
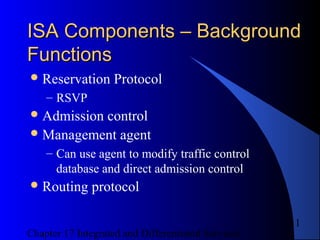
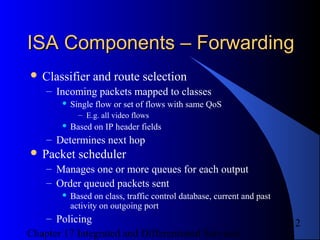
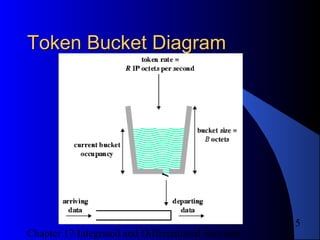
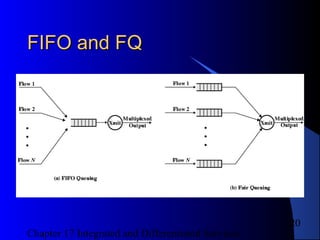
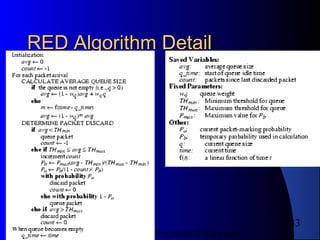
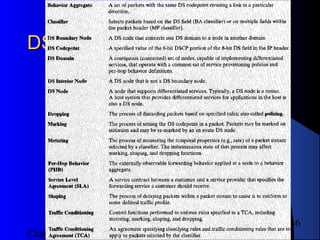
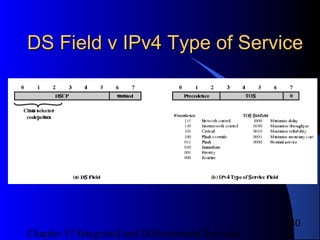
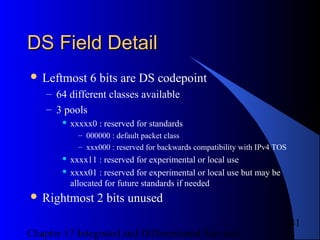
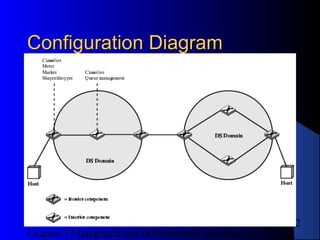
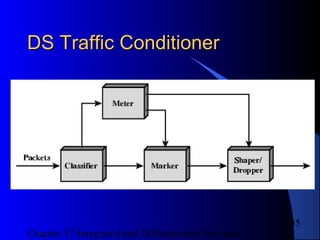
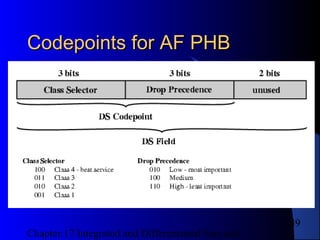
The document discusses integrated and differentiated services for managing internet traffic. Integrated services (ISA) allow traffic to reserve resources and receive guaranteed quality of service. Differentiated services classify traffic into groups that receive different treatment. Interior routers implement per-hop behaviors like expedited forwarding to give preferential treatment based on packet codes. Boundary routers condition traffic to enforce service level agreements.