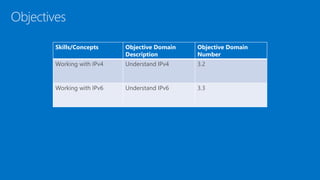
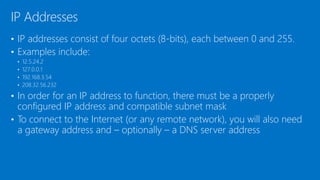
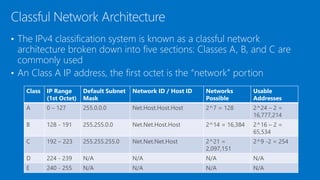
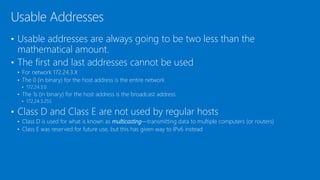
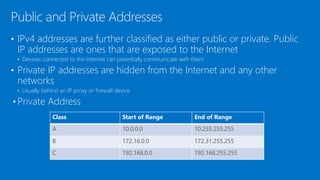
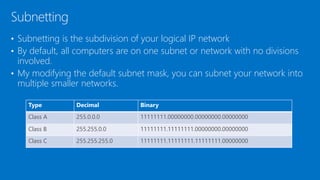
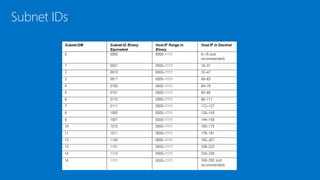
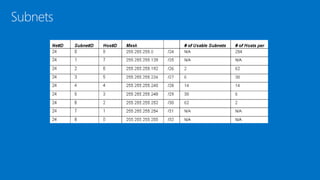
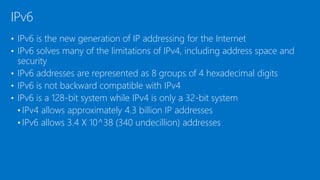
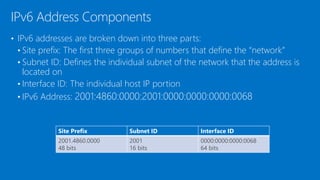
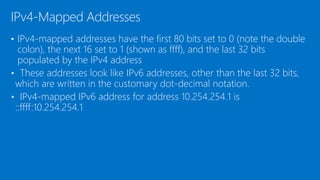
The document provides an overview of Internet Protocol version 4 (IPv4) and IPv6, including key concepts such as IP addresses, subnetting, network address translation (NAT), and dual IP stacks. It defines the core components and classifications of IPv4 and IPv6 addressing, and how devices configure TCP/IP settings like default gateways and DNS servers.