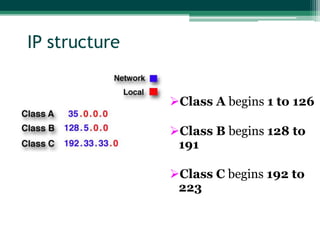
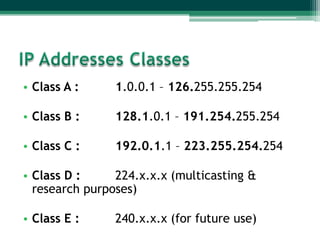
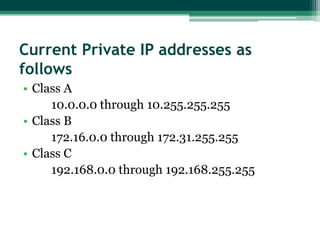
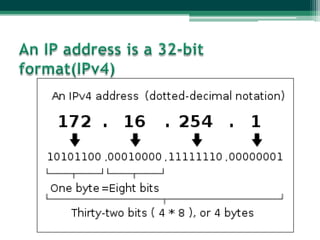
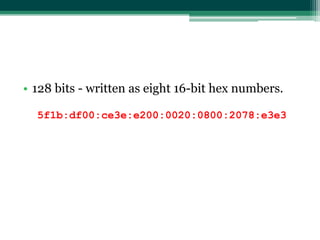
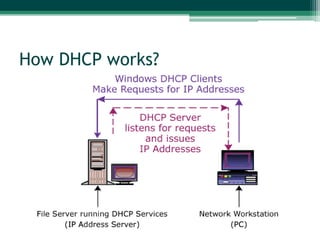
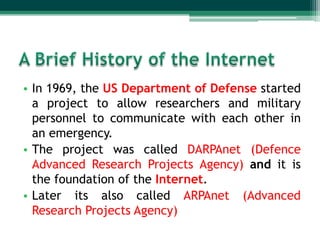
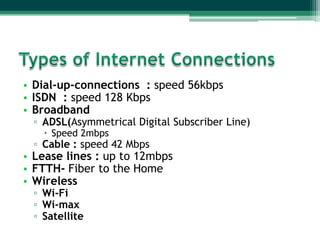
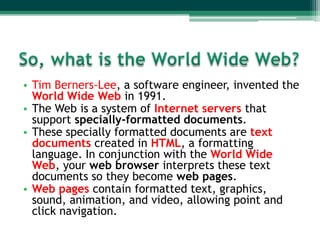
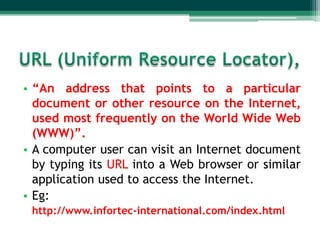
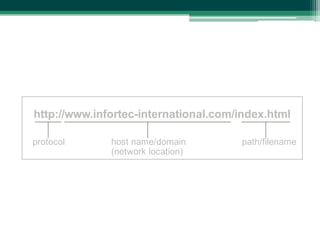
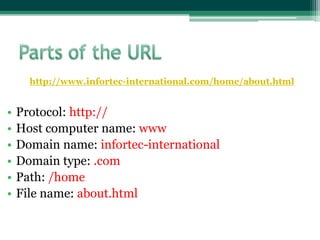
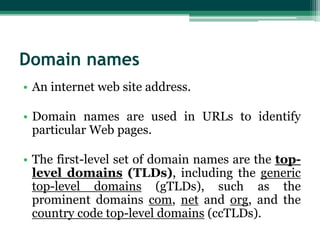
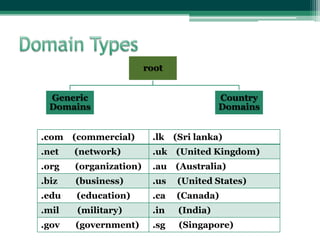
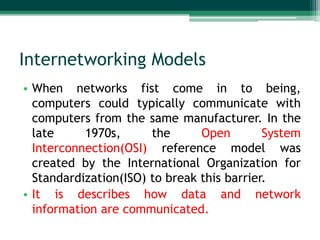
The document provides an overview of the history and development of the Internet. It discusses how the Internet began as a US military network called ARPAnet in 1969 and expanded throughout the 1970s. While initially used by researchers and the military, the creation of the World Wide Web in the early 1990s led to widespread commercial and public use of the Internet with over 1.9 billion users currently. The document also outlines the various technologies and standards that underpin modern Internet infrastructure like IP addressing, domains, and connection types.











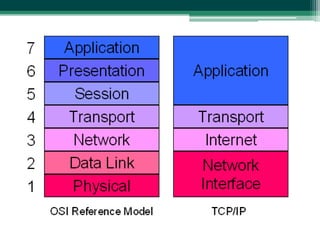
![7. Application
6. Presentation
5. Session
4. Transport
3. Network
2. Data Link
1. Physical
Provides the user interface to
communicate to the computer. Eg HTTP
----------------------------------------------------Presents data to the 7th layer and data
translation like encryption, conversion
----------------------------------------------------Manage presentation layers entities. (keep
different application data separately)
----------------------------------------------------Performs error correction before
retransmit.[Segments]
----------------------------------------------------Manages the device addressing.(IP
addressing) , Routes data. [Packets]
----------------------------------------------------Combines packets in to bytes and error
detection. [Frames]
----------------------------------------------------Moves bits between devices(physical
connection/cabling, electronic singnals)
[Bits]](https://image.slidesharecdn.com/networkinglesson-120115093046-phpapp01-131104083454-phpapp01/85/Networkinglesson-120115093046-phpapp01-71-320.jpg)