The document covers principles and algorithms in cryptography, focusing on block ciphers like the Data Encryption Standard (DES) and public key cryptography such as RSA. It elaborates on encryption definitions, methods, and differential cryptanalysis, discussing the structure and design of modern ciphers, particularly highlighting the evolution from DES to the Advanced Encryption Standard (AES). Additionally, it addresses the importance of encryption modes for practical application, along with the strengths and weaknesses associated with these cryptographic systems.
![ADVANTAGES AND LIMITATIONS OF CBC
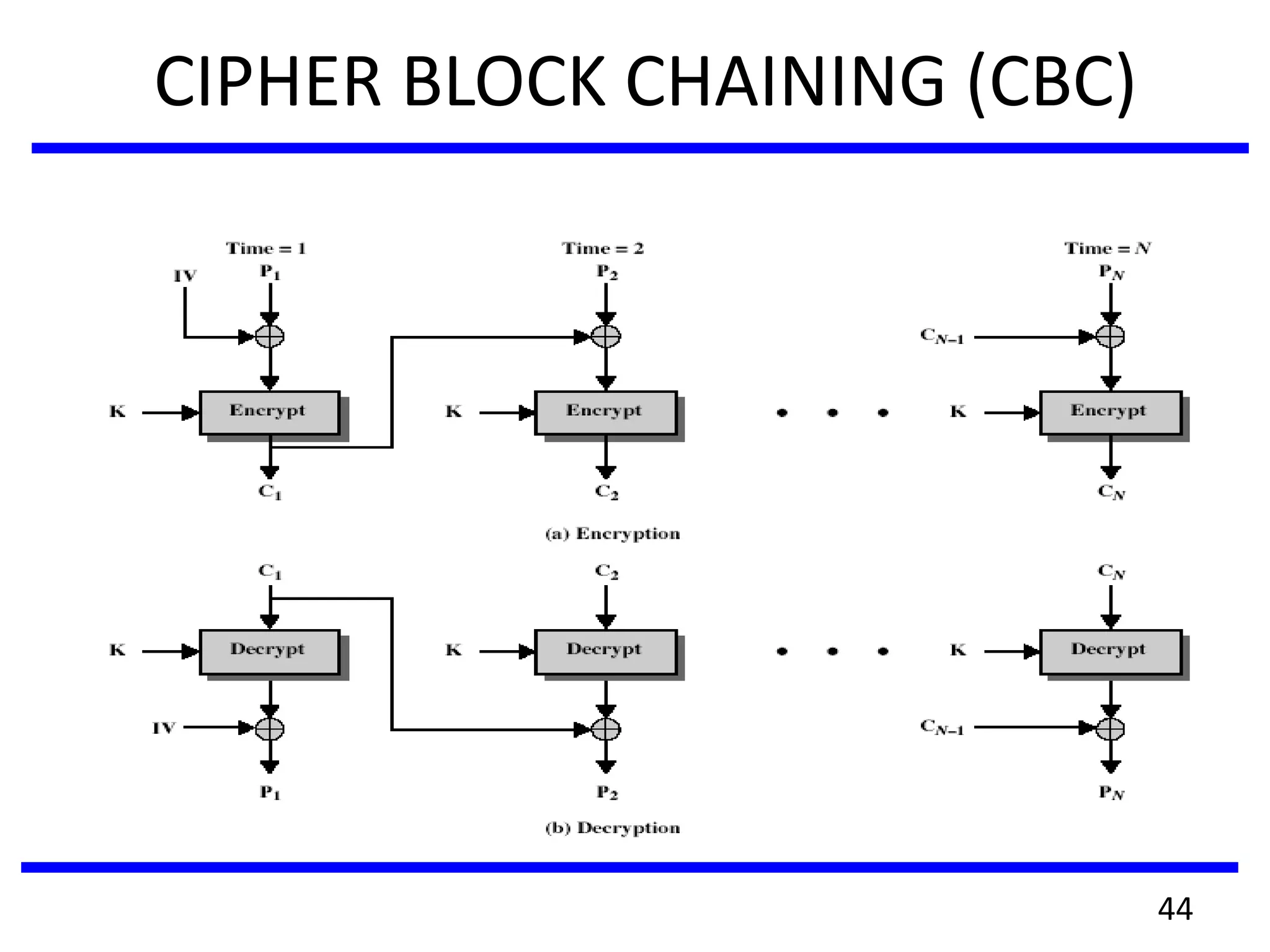
• each ciphertext block depends on all message blocks
• thus a change in the message affects all ciphertext blocks after
the change as well as the original block
• need Initial Value (IV) known to sender & receiver
– however if IV is sent in the clear, an attacker can change bits
of the first block, and change IV to compensate
– hence either IV must be a fixed value (as in EFTPOS) or it
must be sent encrypted in ECB mode before rest of message
• at end of message, handle possible last short block
– by padding either with known non-data value (eg nulls)
– or pad last block with count of pad size
• eg. [ b1 b2 b3 0 0 0 0 5] <- 3 data bytes, then 5 bytes
pad+count
45](https://image.slidesharecdn.com/unit2-170615083353/75/CS6701-CRYPTOGRAPHY-AND-NETWORK-SECURITY-45-2048.jpg)
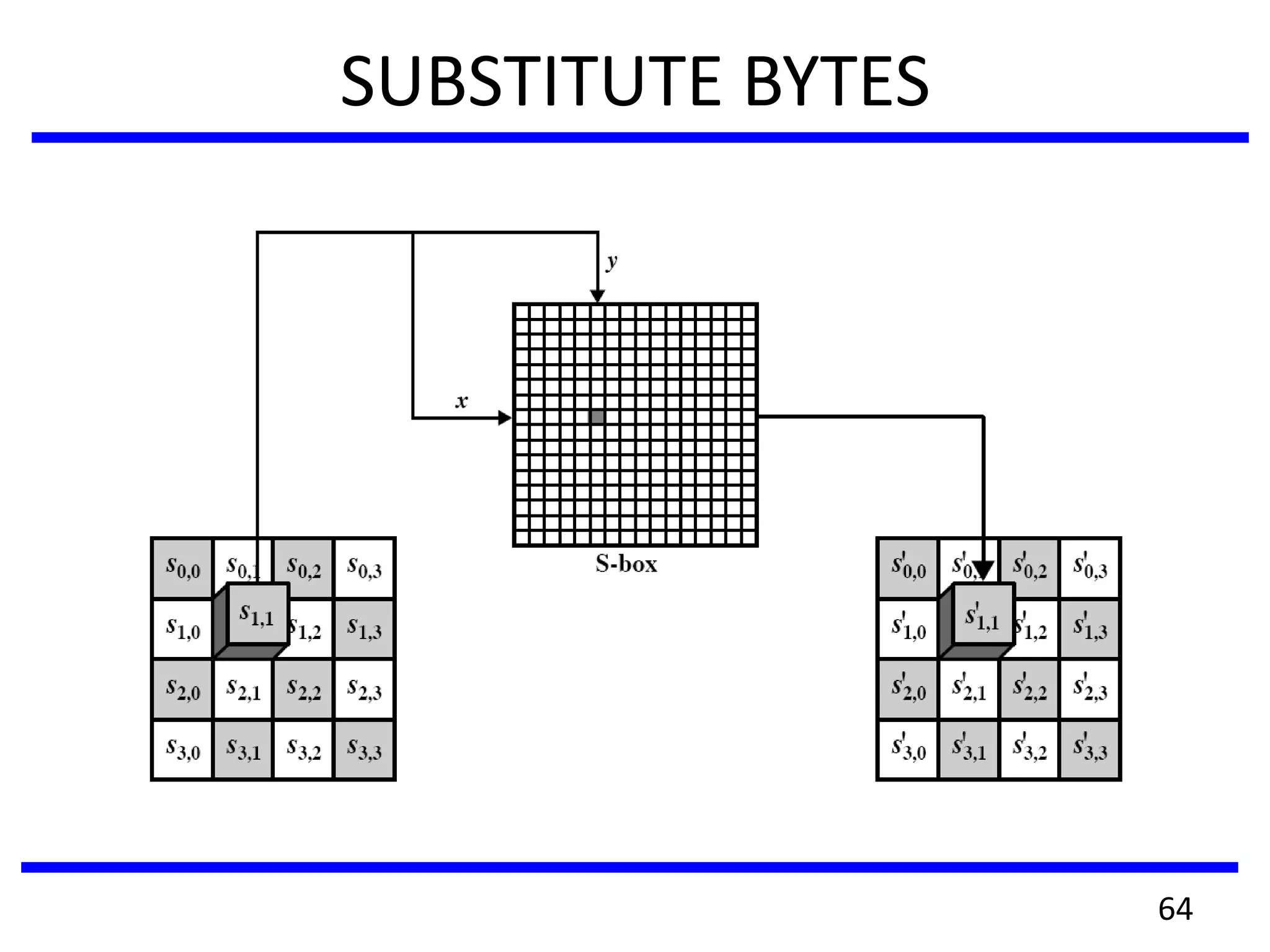
![SUBSTITUTE BYTES
• GF(28) = 2[x] / (x8+x4+x3+x+1)
SubBytes(a7a6a5a4a3a2a1a0)
1. z ← BinaryToField(a7a6a5a4a3a2a1a0)
2. if z ≠ 0
3. then z ← FieldInv(z)
4. (a7a6a5a4a3a2a1a0) ← FieldToBinary(z)
5. (c7c6c5c4c3c2c1c0) ← (01100011)
6. for i ← 0 to 7
7. do bi ←
(ai+ai+4+ai+5+ai+6+ai+7+ci) mod 2
8. return (b7b6b5b4b3b2b1b0)
65](https://image.slidesharecdn.com/unit2-170615083353/75/CS6701-CRYPTOGRAPHY-AND-NETWORK-SECURITY-65-2048.jpg)
![GF(28)[x] / (x4+1)
• GF(28) = 2[x] / (x8+x4+x3+x+1)
• Let
a(x) = a3x3+a2x2+a1x+a0, ai 2 GF(28)
b(x) = b3x3+b2x2+b1x+b0, bi 2 GF(28)
• Addition
a(x) + b(x) = (a3+b3)x3+(a2+b2)x2+(a1+b1)x+(a0+b0)
• Multiplication
c(x) = a(x) b(x) = c6x6 + c5x5 + c4x4 + c3x3 + c2x2 + c1x1 + c0
c0 = a0b0 c4 = (a3b1 + a2b2 + a1b3)
c1 = (a1b0 + a0b1) c5 = (a3b2 + a2b3)
c2 = (a2b0 + a1b1 + a0b2) c6 = a3b3
c3 = (a3b0 + a2b1 + a1b2 + a0b3)
70](https://image.slidesharecdn.com/unit2-170615083353/75/CS6701-CRYPTOGRAPHY-AND-NETWORK-SECURITY-70-2048.jpg)
![GF(28)[x] / (x4+1)
d(x) = c(x) mod (x4+1)
= c6x6 + c5x5 + c4x4 + c3x3 + c2x2 + c1x1 + c0
= c3x3 + (c2+c6)x2 + (c1+c5)x + (c0+c4)
= d3x3 + d2x2 + d1x + d0
d0 = a0b0 + a3b1 + a2b2 + a1b3
d1 = a1b0 + a0b1 + a3b2 + a2b3
d2 = a2b0 + a1b1 + a0b2 + a3b3
d3 = a3b0 + a2b1 + a1b2 + a0b3
d0 a0 a3 a2 a1 b0 d0 02 03 01 01 b0
d1 a1 a0 a3 a2 b1 d1 01 02 03 01 b1
d2 a2 a1 a0 a3 b2 d2 01 01 02 03 b2
d3 a3 a2 a1 a0 b3 d3 03 01 01 02 b3
=
a(x) = {03}x3+{01}x2+{01}x+{02}
=
71](https://image.slidesharecdn.com/unit2-170615083353/75/CS6701-CRYPTOGRAPHY-AND-NETWORK-SECURITY-71-2048.jpg)
![AES Key Expansion
KeyExpasion(key)
1. RCon[1] ← 0x01000000
RCon*2+ ← 0x02000000
RCon[3] ← 0x04000000
RCon*4+ ← 0x08000000
RCon*5+ ← 0x10000000
RCon*6+ ← 0x20000000
RCon*7+ ← 0x40000000
RCon*8+ ← 0x80000000
RCon*9+ ← 0x01B00000
RCon*10+ ← 0x36000000
2. for i ← 0 to 3 do
3. w*i+ ← (key*4i+,key*4i+1+,key*4i+2+,key*4i+3+)
4. for i ← 4 to 43 do
5. temp ← w*i-1]
6. if i 0 mod 4 then
7. temp ← SubWord(RotWord(temp))© Rcon[i/4]
8. w*i+ ← w*i-4]© temp 75](https://image.slidesharecdn.com/unit2-170615083353/75/CS6701-CRYPTOGRAPHY-AND-NETWORK-SECURITY-75-2048.jpg)
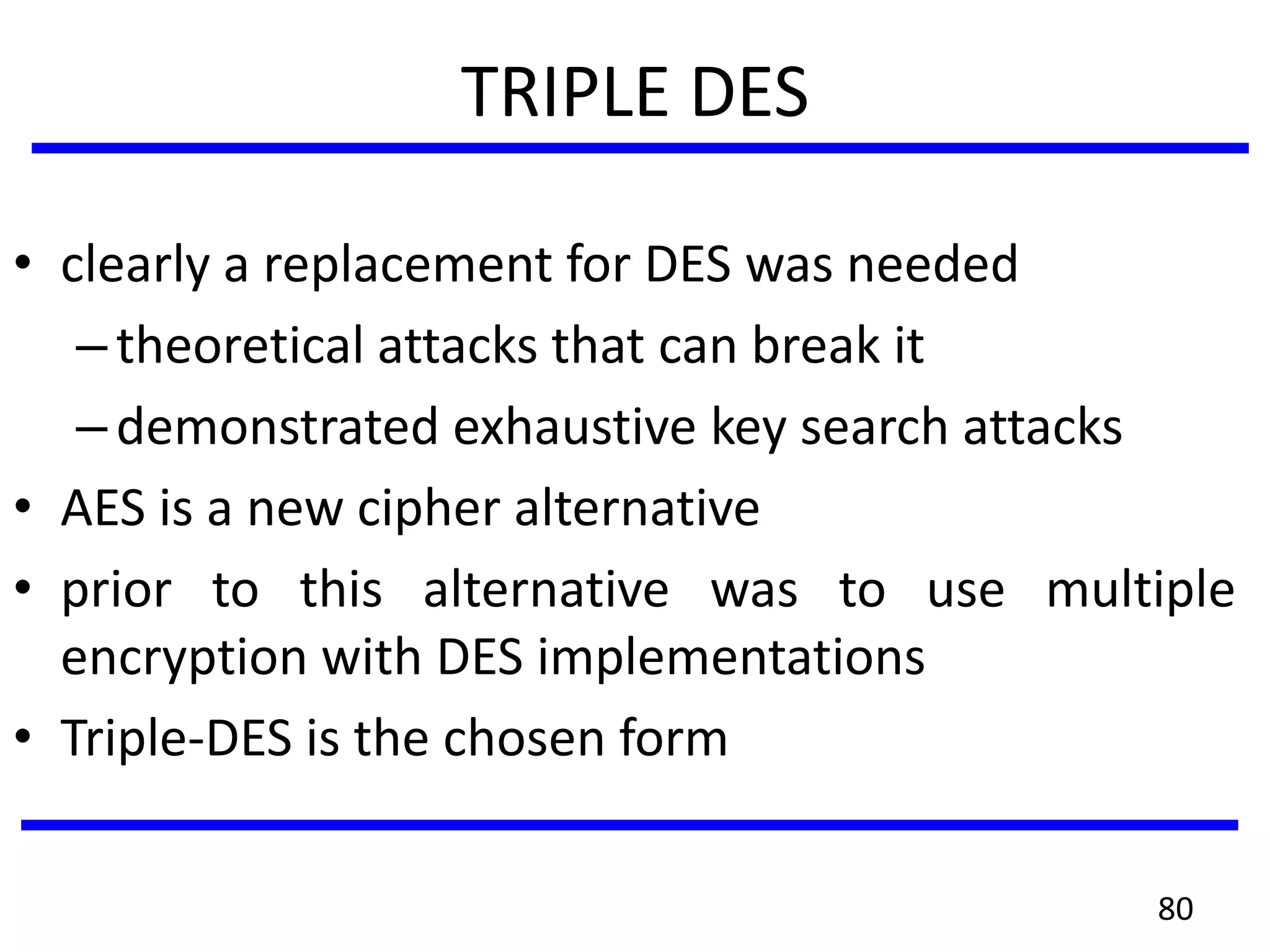
![WHY TRIPLE-DES?
• why not Double-DES?
–NOT same as some other single-DES use, but
have
• meet-in-the-middle attack
–works whenever use a cipher twice
–since X = EK1[P] = DK2[C]
–attack by encrypting P with all keys and store
–then decrypt C with keys and match X value
–can show takes O(256) steps
81](https://image.slidesharecdn.com/unit2-170615083353/75/CS6701-CRYPTOGRAPHY-AND-NETWORK-SECURITY-81-2048.jpg)
![TRIPLE-DES WITH TWO-KEYS
• hence must use 3 encryptions
– would seem to need 3 distinct keys
• but can use 2 keys with E-D-E sequence
– C = EK1[DK2[EK1[P]]]
– nb encrypt & decrypt equivalent in security
– if K1=K2 then can work with single DES
• standardized in ANSI X9.17 & ISO8732
• no current known practical attacks
82](https://image.slidesharecdn.com/unit2-170615083353/75/CS6701-CRYPTOGRAPHY-AND-NETWORK-SECURITY-82-2048.jpg)
![TRIPLE-DES WITH THREE-KEYS
• although are no practical attacks on two-key Triple-
DES have some indications
• can use Triple-DES with Three-Keys to avoid even
these
– C = EK3[DK2[EK1[P]]]
• has been adopted by some Internet applications, eg
PGP, S/MIME
83](https://image.slidesharecdn.com/unit2-170615083353/75/CS6701-CRYPTOGRAPHY-AND-NETWORK-SECURITY-83-2048.jpg)
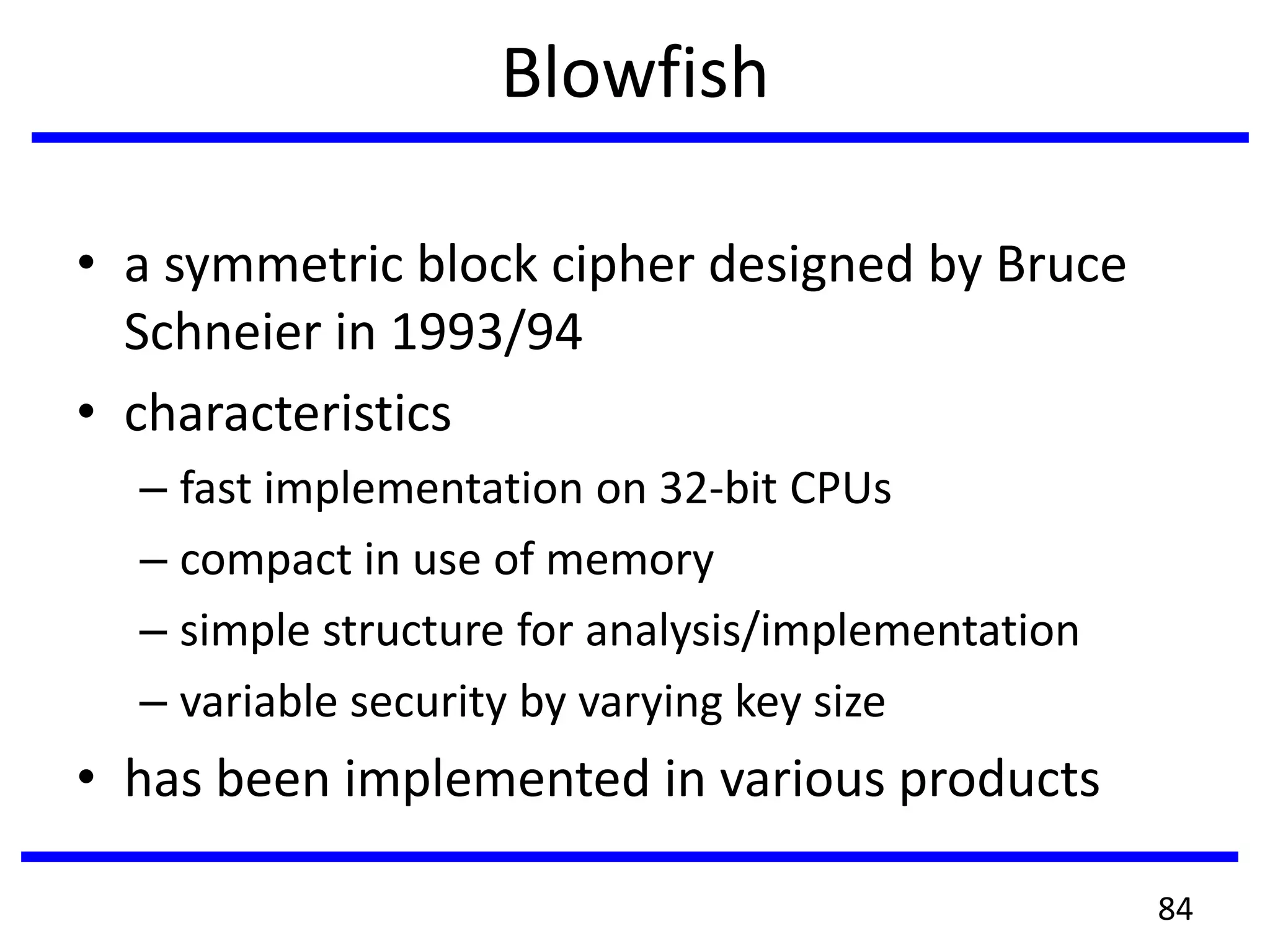
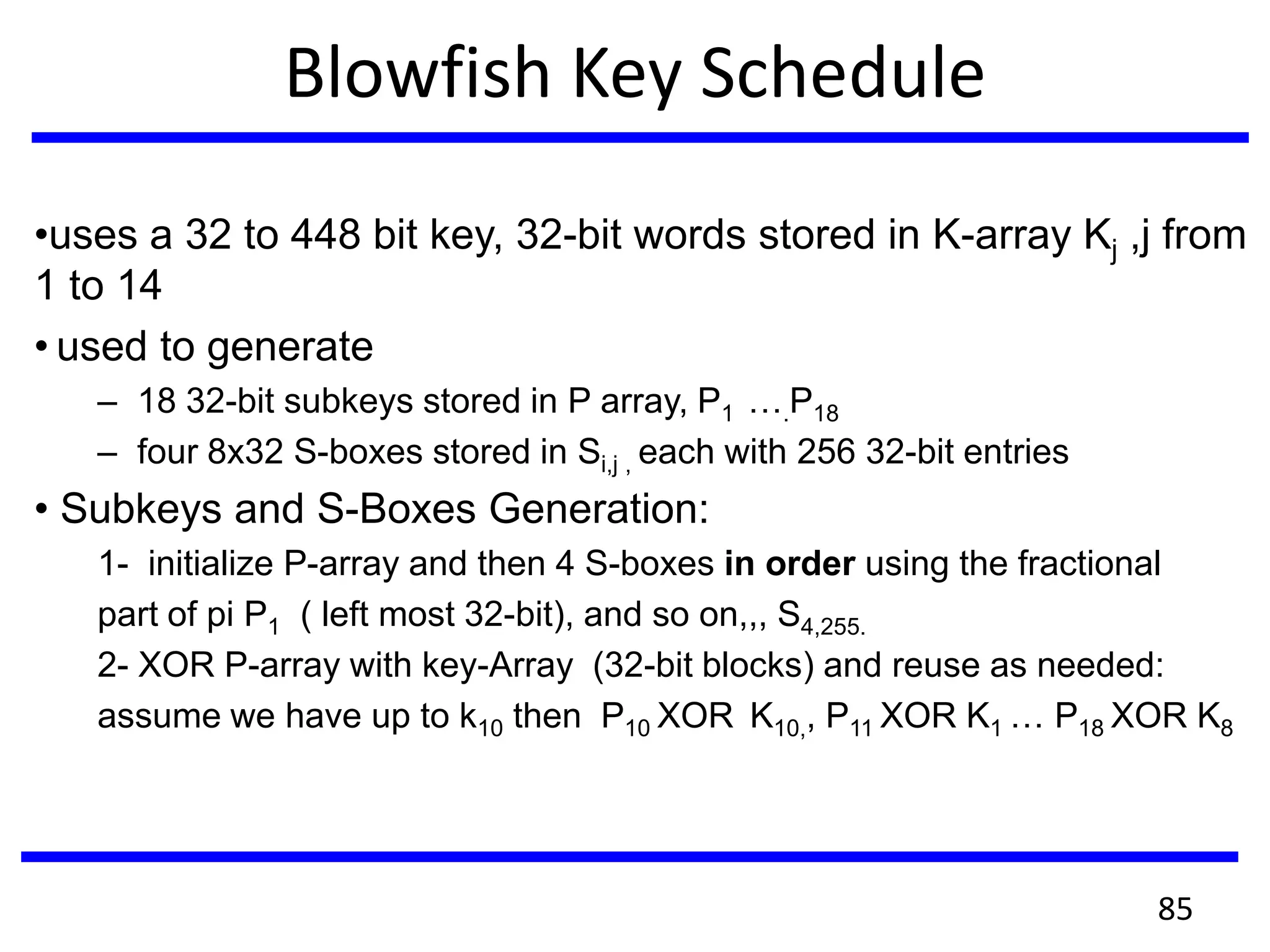
![Blowfish Encryption
• uses two main operations: addition modulo 232 , and
XOR
• data is divided into two 32-bit halves L0 & R0
for i = 1 to 16 do
Ri = Li-1 XOR Pi;
Li = F[Ri] XOR Ri-1;
L17 = R16 XOR P18;
R17 = L16 XOR P17;
• where
F[a,b,c,d] = ((S1,a + S2,b) XOR S3,c) + S4,d
87](https://image.slidesharecdn.com/unit2-170615083353/75/CS6701-CRYPTOGRAPHY-AND-NETWORK-SECURITY-87-2048.jpg)
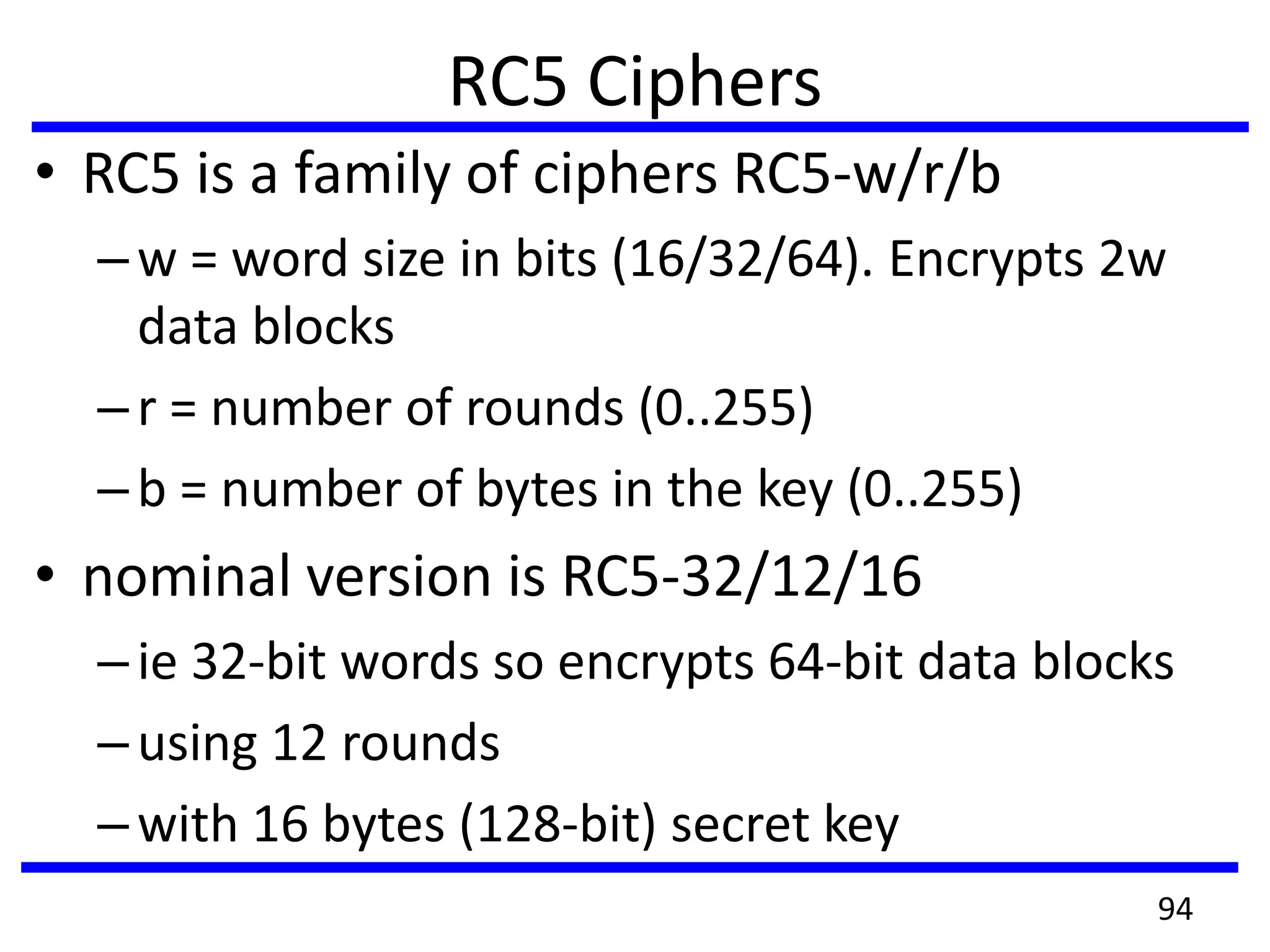
![RC5 Key Expansion
• RC5 uses t=2r+2 subkey words (w-bits)
• subkeys are stored in array S[i], i=0..t-1
• then the key schedule consists of
–initializing S to a fixed pseudorandom value,
based on constants e and phi
–the byte key is copied into a c-words array L
–a mixing operation then combines L and S to
form the final S array
95](https://image.slidesharecdn.com/unit2-170615083353/75/CS6701-CRYPTOGRAPHY-AND-NETWORK-SECURITY-95-2048.jpg)
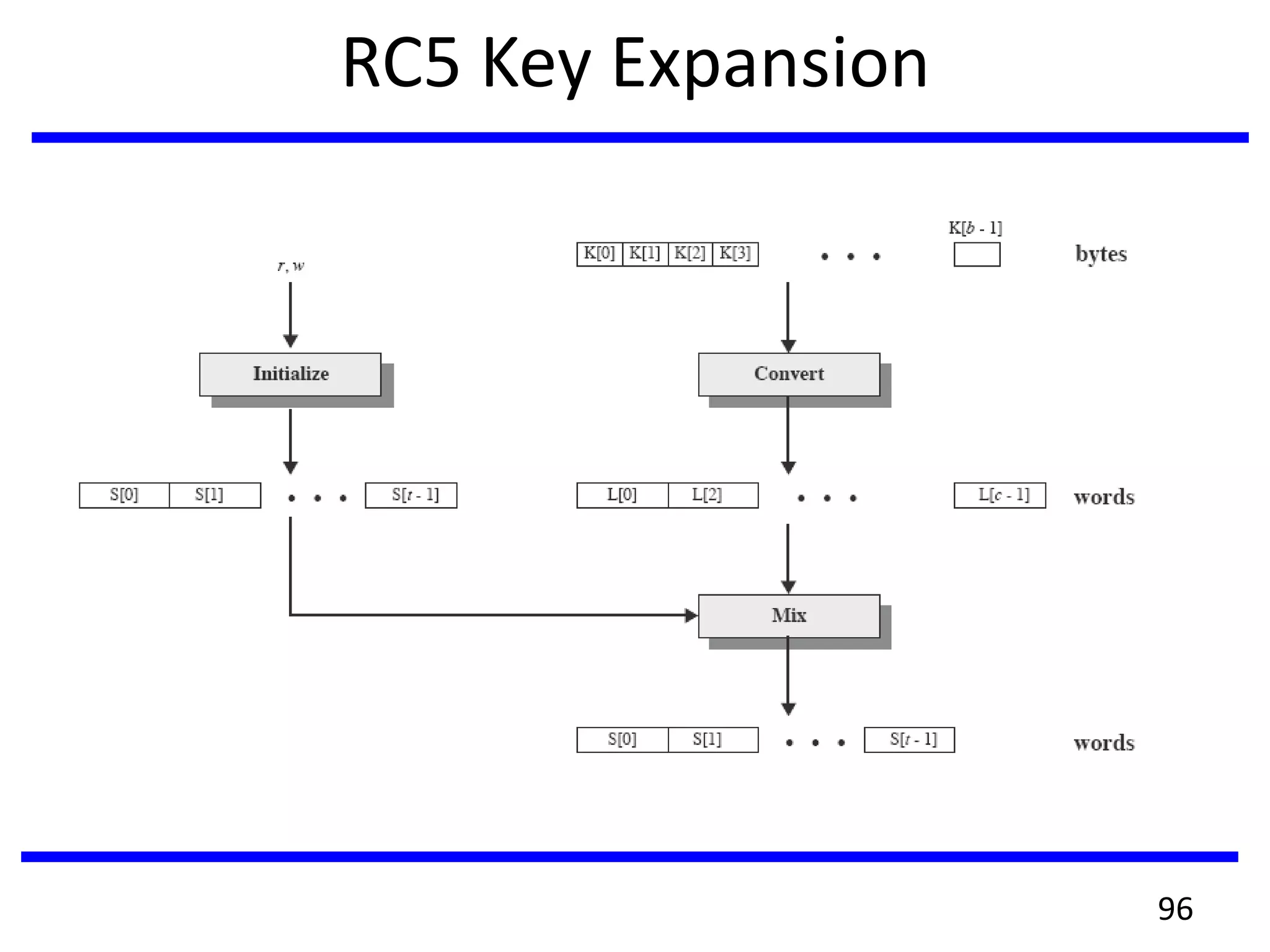
![RC5 Encryption
• Three main operations: + mod 2w, XOR, circular left shift
<<<, and there inverses used.
• split input into two halves A & B (w-bits each)
L0 = A + S[0];
R0 = B + S[1];
for i = 1 to r do
Li = ((Li-1 XOR Ri-1) <<< Ri-1) + S[2 x i];
Ri = ((Ri-1 XOR Li) <<< Li) + S[2 x i + 1];
• each round is like 2 DES rounds
• note rotation is main source of non-linearity
• need reasonable number of rounds (eg 12-16)
97](https://image.slidesharecdn.com/unit2-170615083353/75/CS6701-CRYPTOGRAPHY-AND-NETWORK-SECURITY-97-2048.jpg)
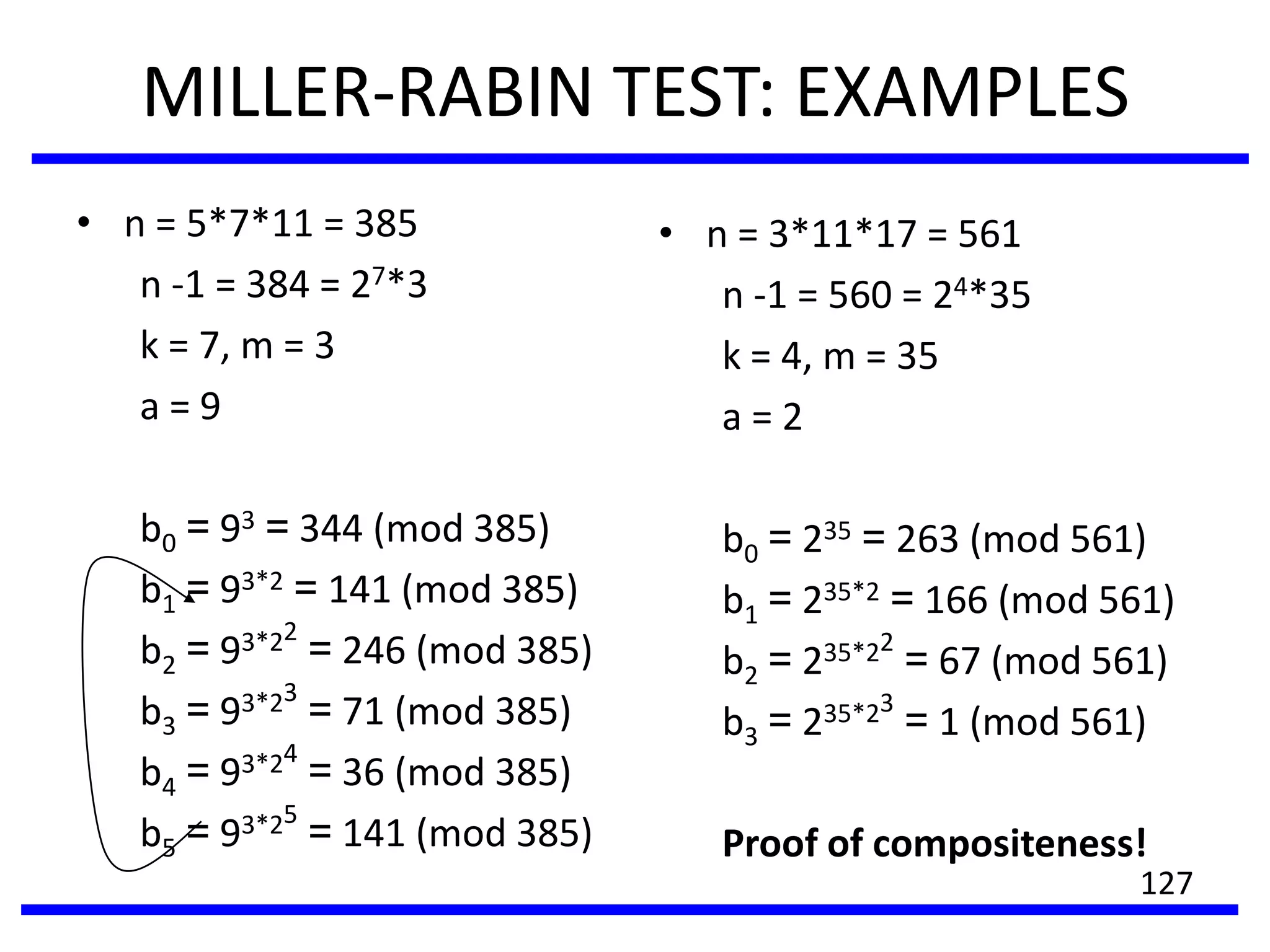
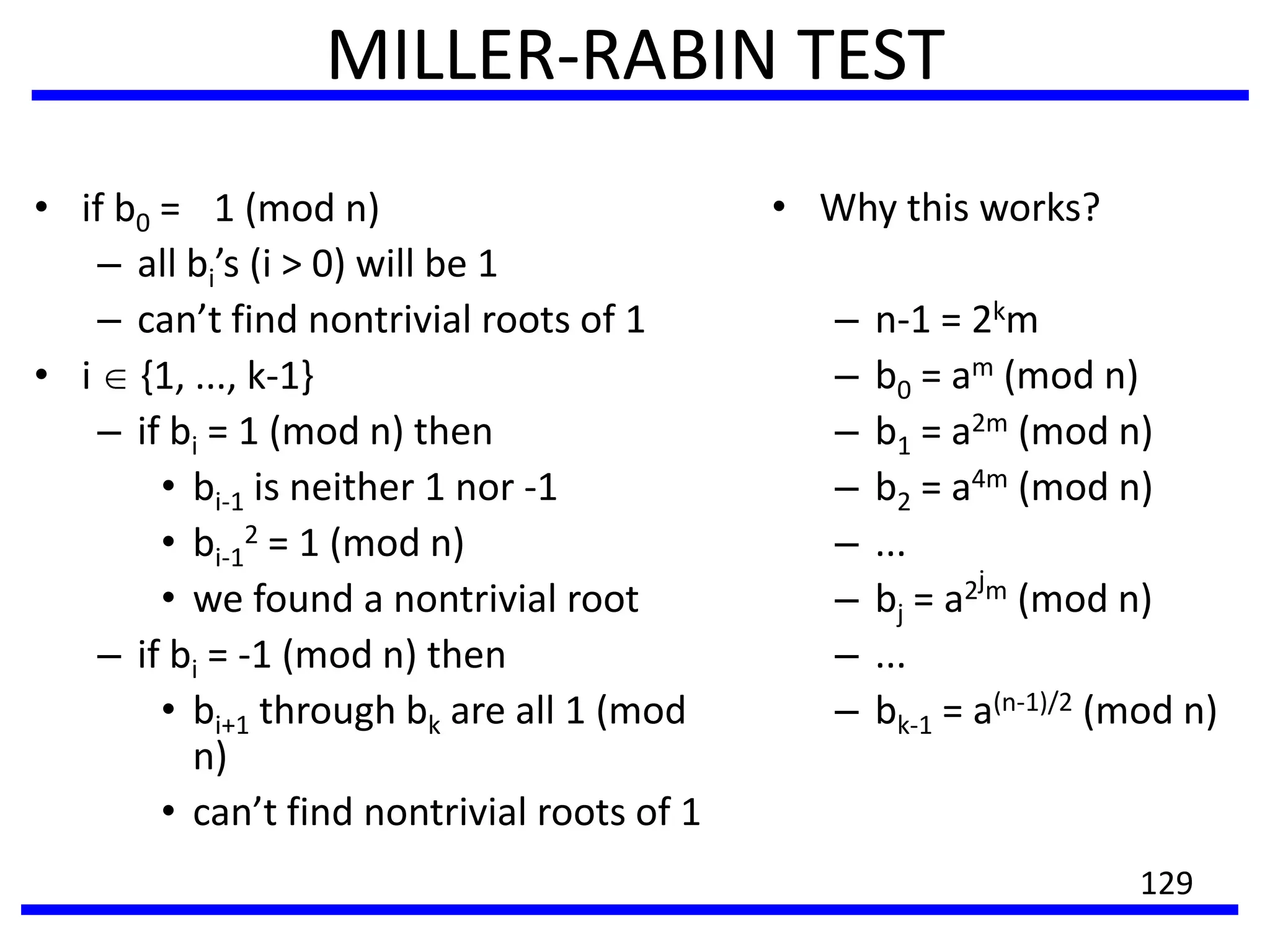
![MILLER-RABIN TEST: QUALITY
• MR test is probabilistic
• Answer
– composite – the
number is certainly
composite
– prime – the number
is prime with high
probability
• Errors
– MR(n) says prime but
n is composite
– Pr[error] ≤ ¼
– Repeat the test to
downgrade the prob.
of error
130](https://image.slidesharecdn.com/unit2-170615083353/75/CS6701-CRYPTOGRAPHY-AND-NETWORK-SECURITY-130-2048.jpg)