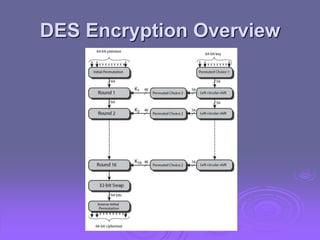
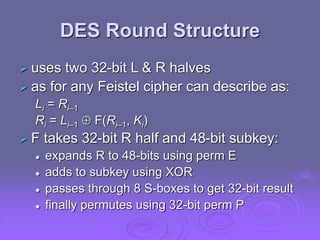
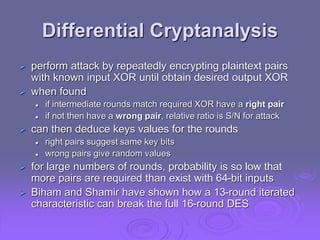
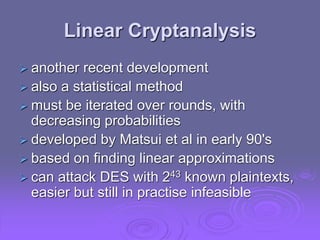
This document discusses block ciphers and the Data Encryption Standard (DES) by exploring their fundamental principles, structures, and historical context. It highlights the significance of Feistel ciphers, confusion and diffusion concepts, and various attack methodologies such as differential and linear cryptanalysis. The document also addresses the controversies surrounding the design of DES, particularly regarding key size and security implications.
![Linear Cryptanalysis
find linear approximations with prob p != ½
P[i1,i2,...,ia] C[j1,j2,...,jb] =
K[k1,k2,...,kc]
where ia,jb,kc are bit locations in P,C,K
gives linear equation for key bits
get one key bit using max likelihood alg
using a large number of trial encryptions
effectiveness given by: |p–1/2|](https://image.slidesharecdn.com/ch03-240602155626-e2c07596/85/ch03-network-security-in-computer-sys-ppt-34-320.jpg)
![DES Design Criteria
as reported by Coppersmith in [COPP94]
7 criteria for S-boxes provide for
non-linearity
resistance to differential cryptanalysis
good confusion
3 criteria for permutation P provide for
increased diffusion](https://image.slidesharecdn.com/ch03-240602155626-e2c07596/85/ch03-network-security-in-computer-sys-ppt-35-320.jpg)