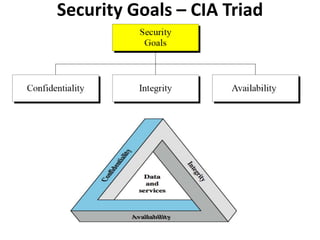
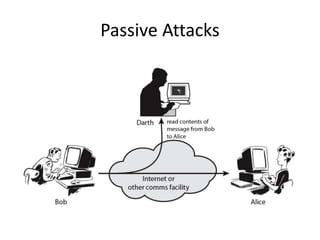
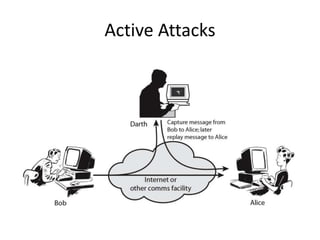
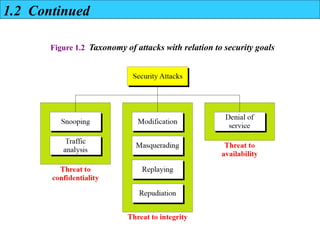
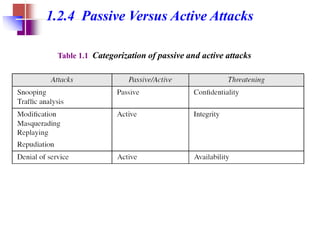
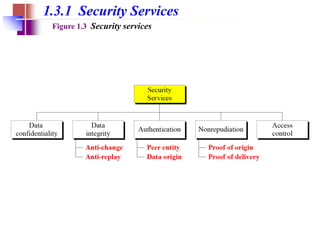
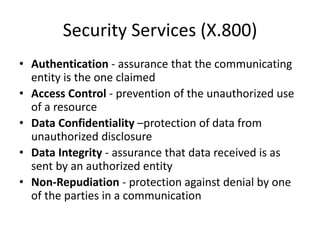
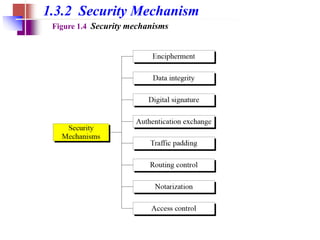
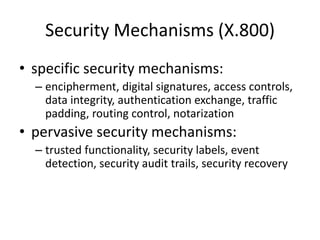
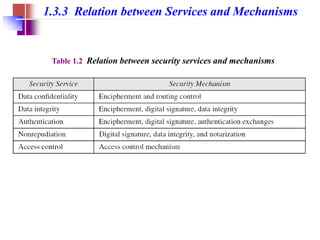
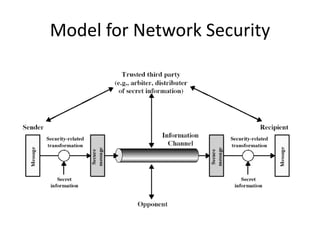
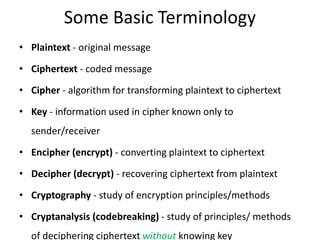
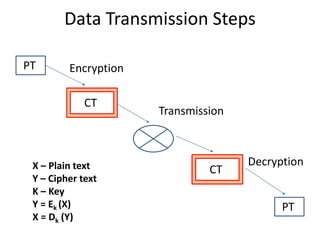
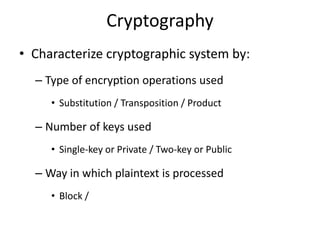
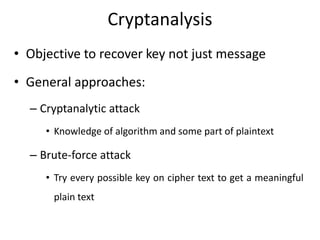
The document covers the basics of cryptography and network security, emphasizing the importance of securing information at various levels through mechanisms and policies. It outlines the goals of security, specifically focusing on the CIA triad: confidentiality, integrity, and availability, while categorizing various security attacks and the mechanisms employed to counter them. Additionally, it discusses modern security practices and the significance of cryptographic techniques in protecting data transmission.