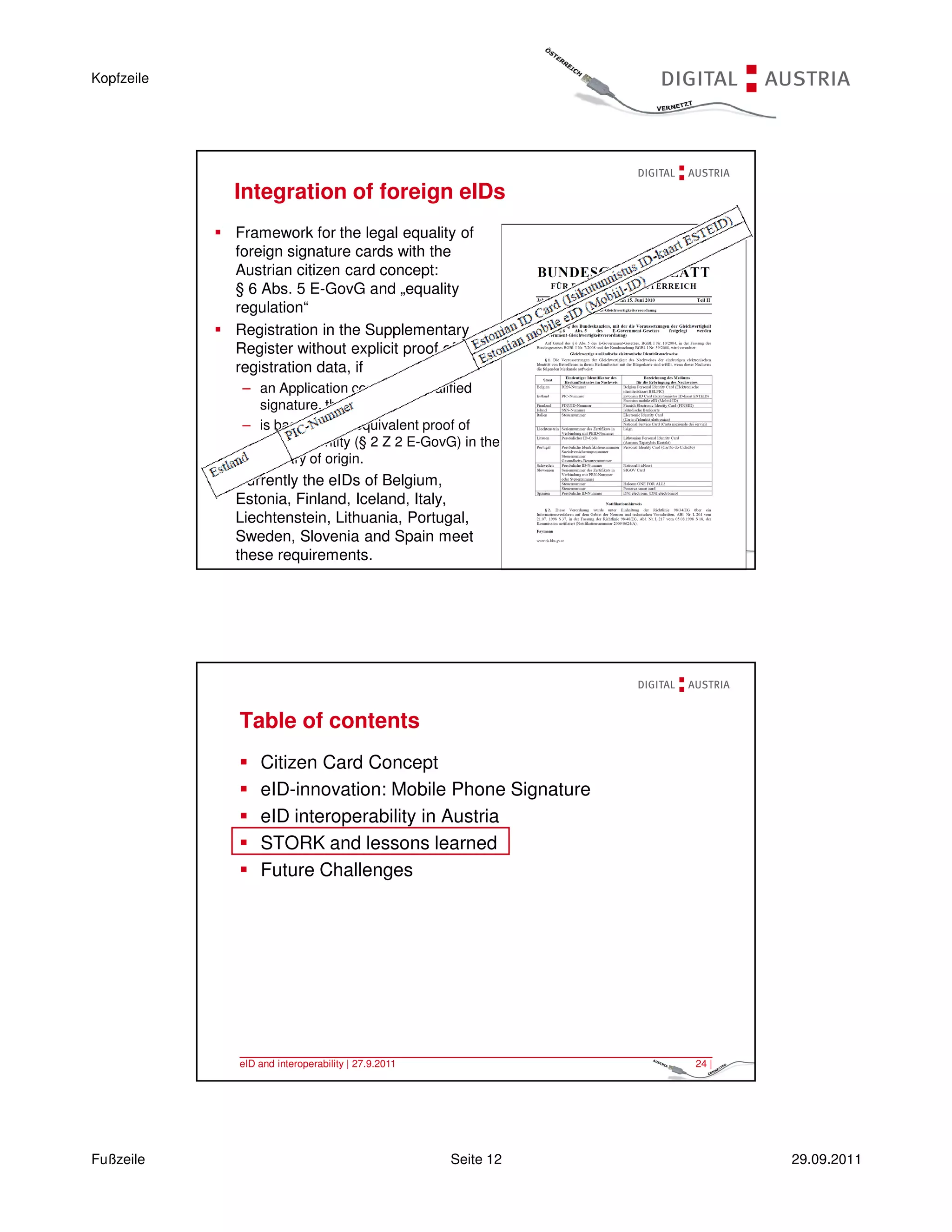
The document discusses electronic identification (eID) in Austria, including:
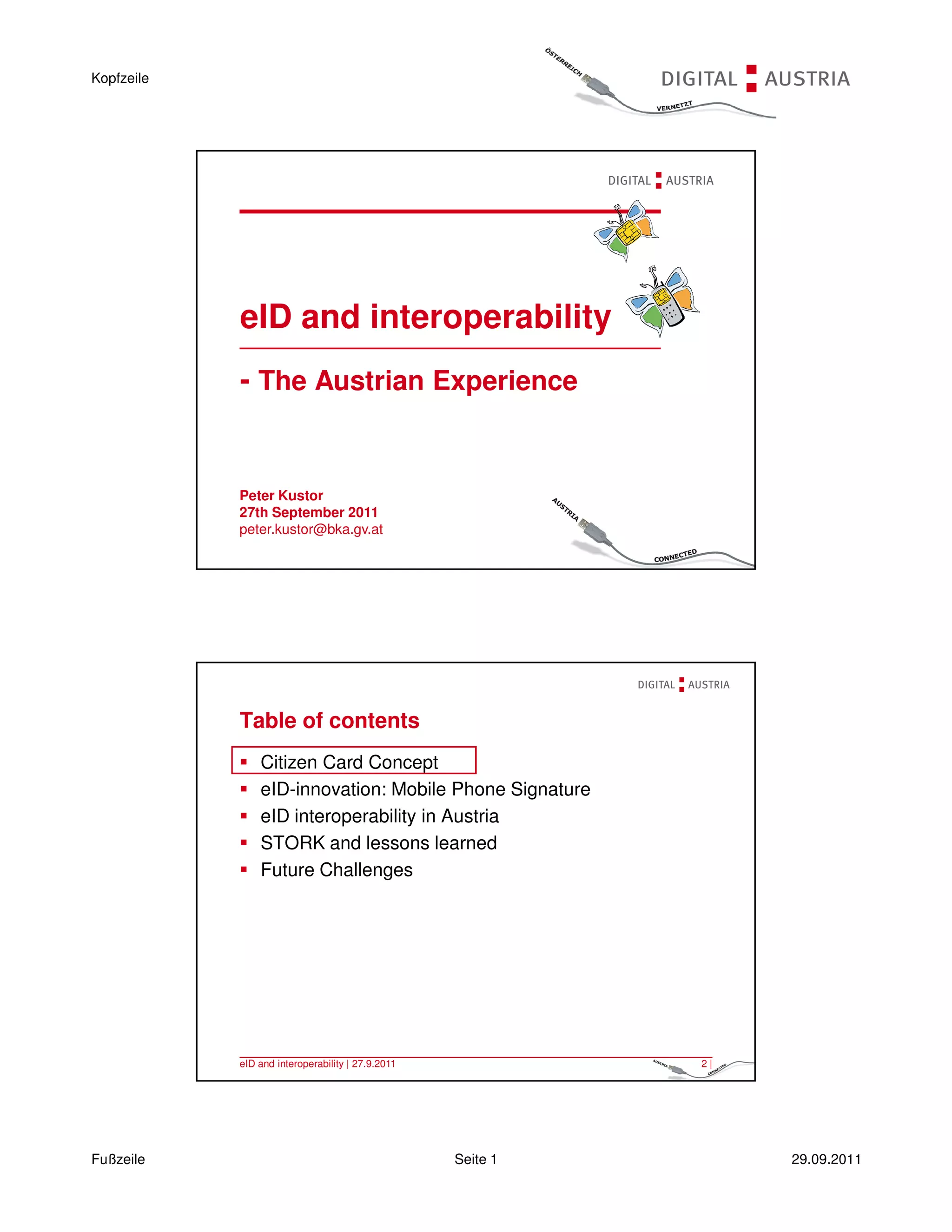
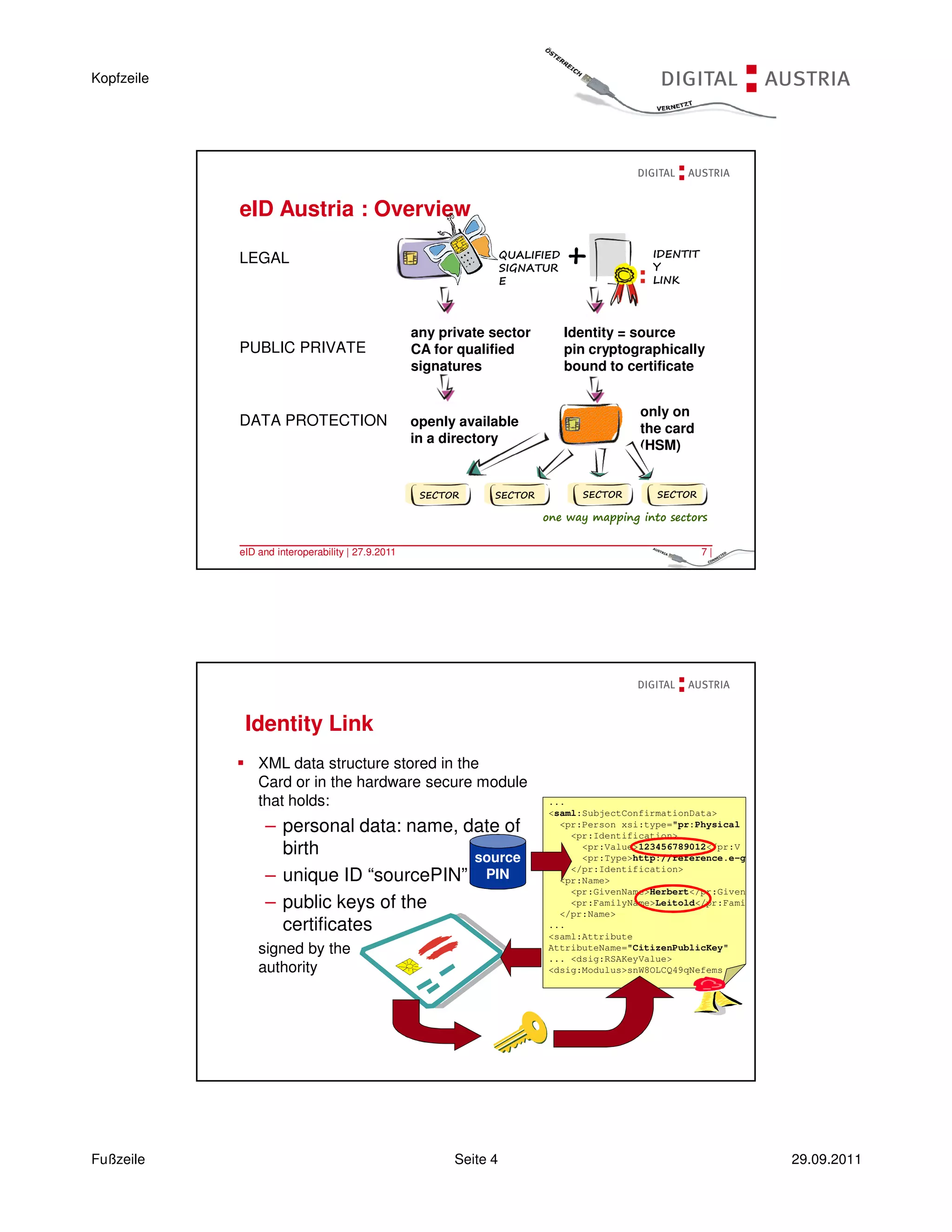
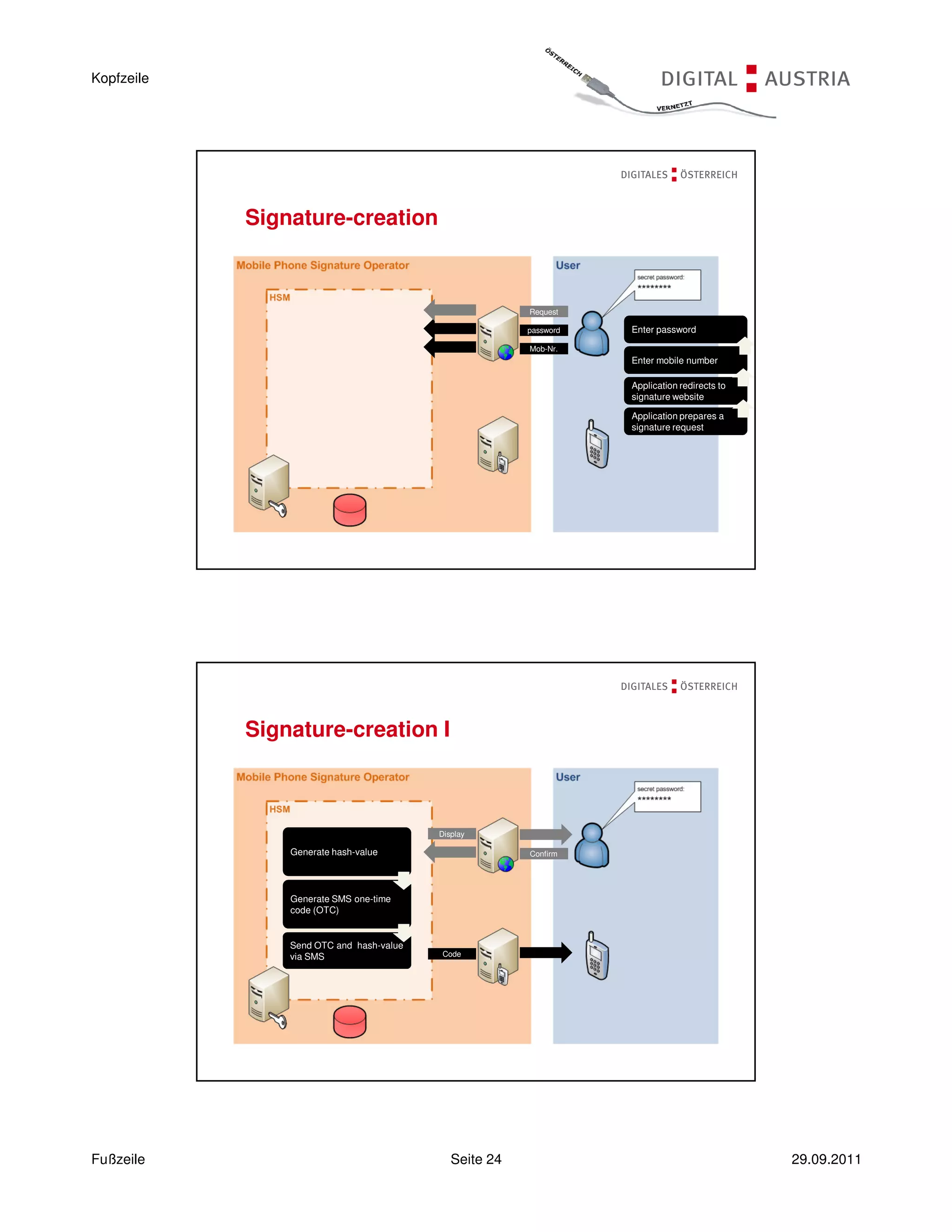
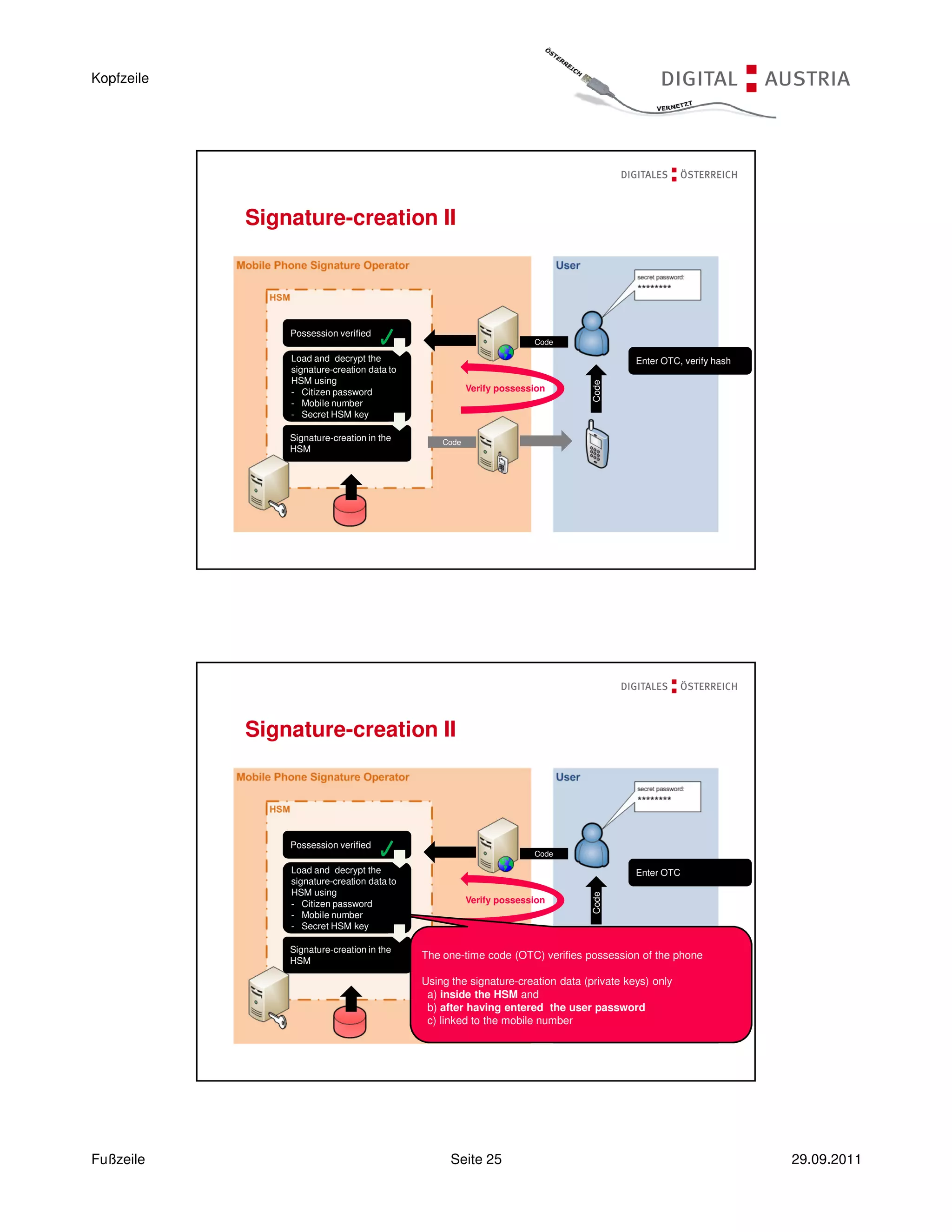
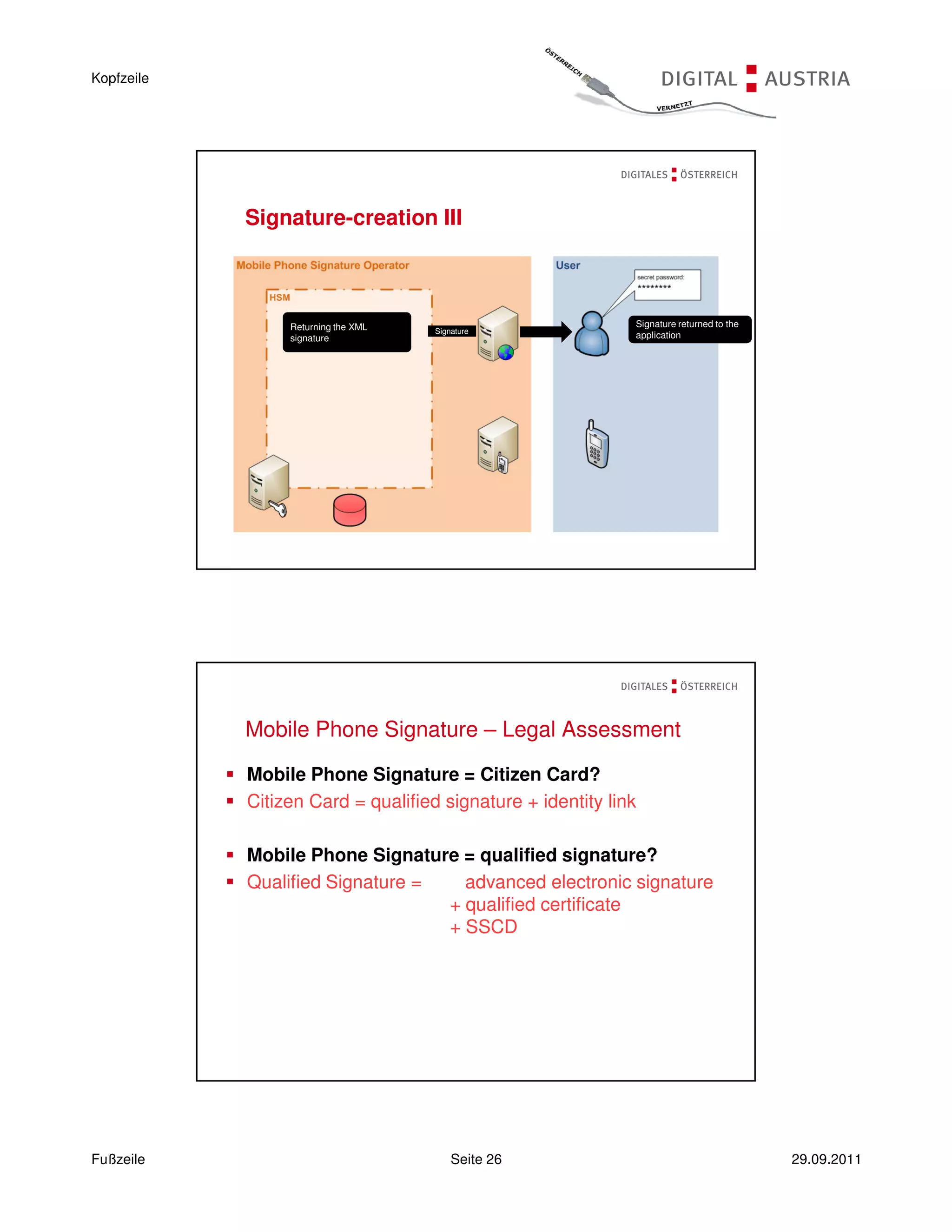
- The Austrian citizen card concept combines electronic signature, unique electronic identity, and representation data.
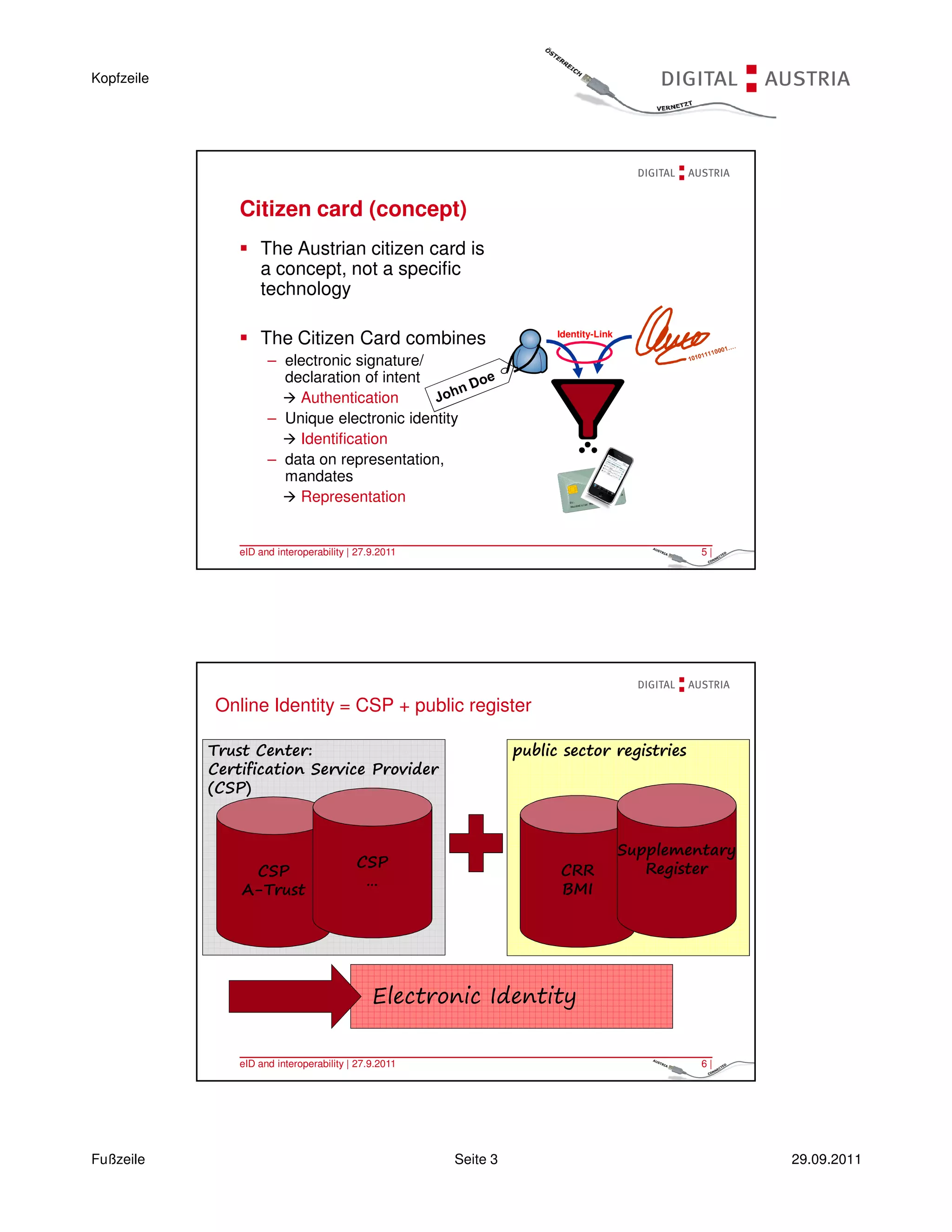
- A valid legal basis is provided by the E-Government Act, which mandates electronic IDs from various sectors that are linked to a citizen's identity.
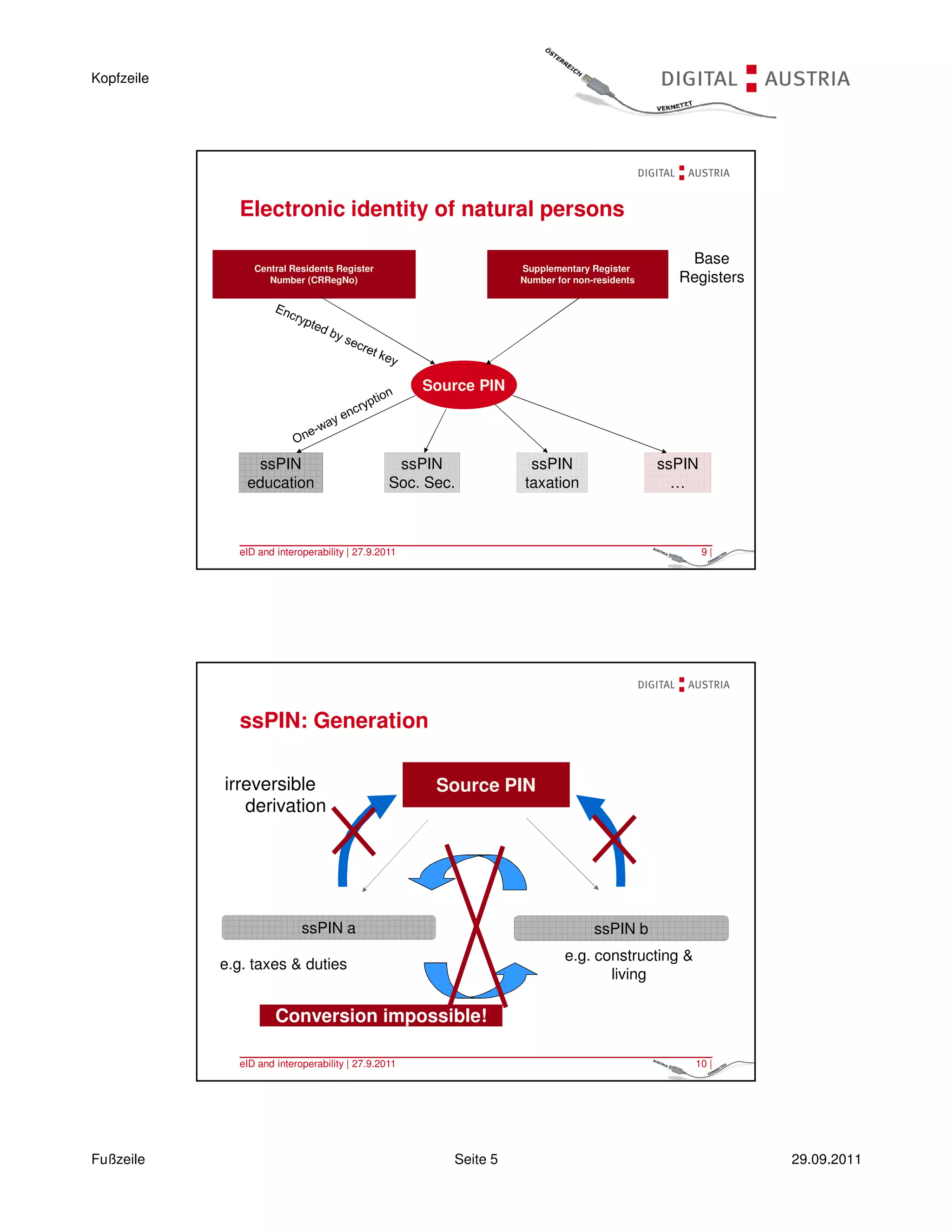
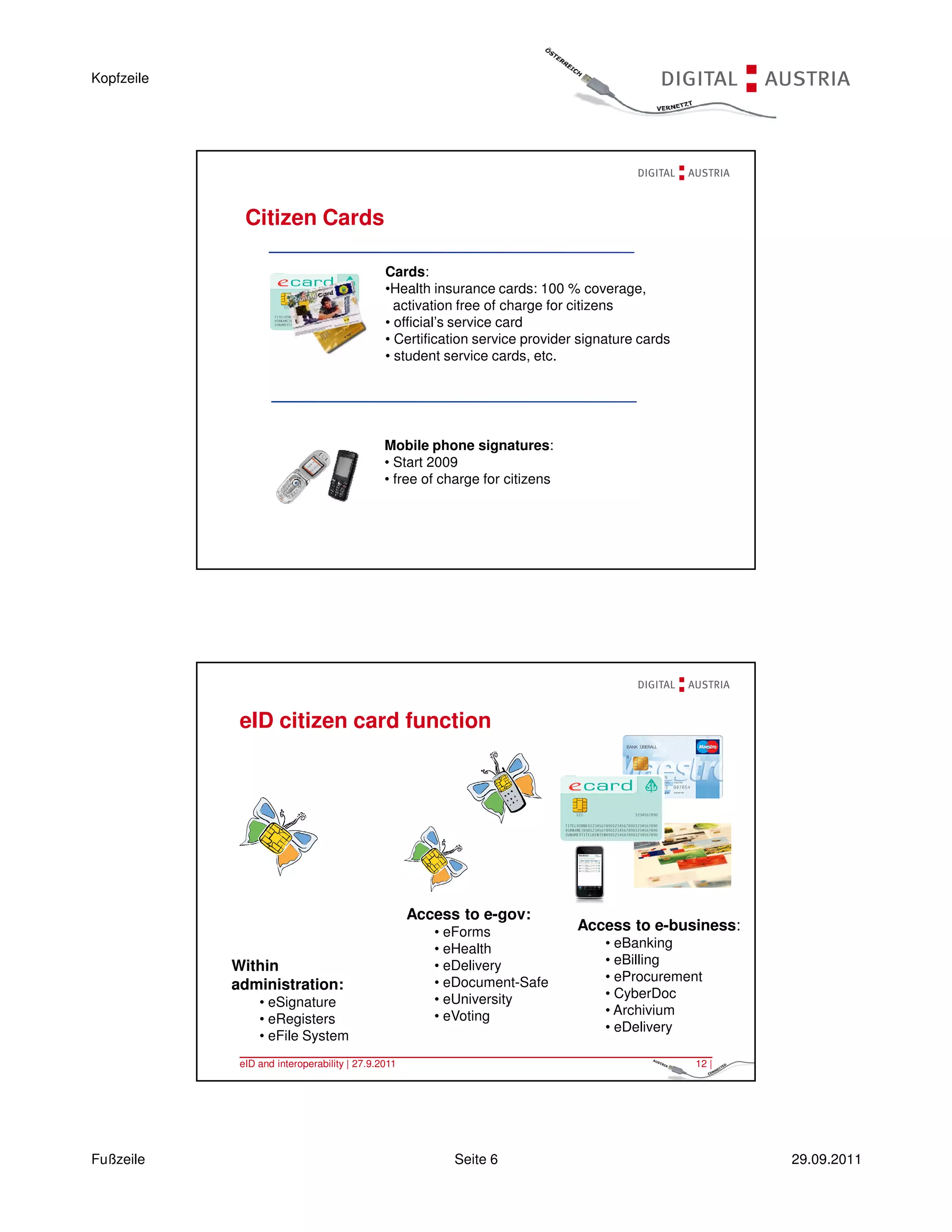
- Identity is comprised of a citizen's unique "sourcePIN" cryptographically bound to their public key certificate from an accredited certification services provider.
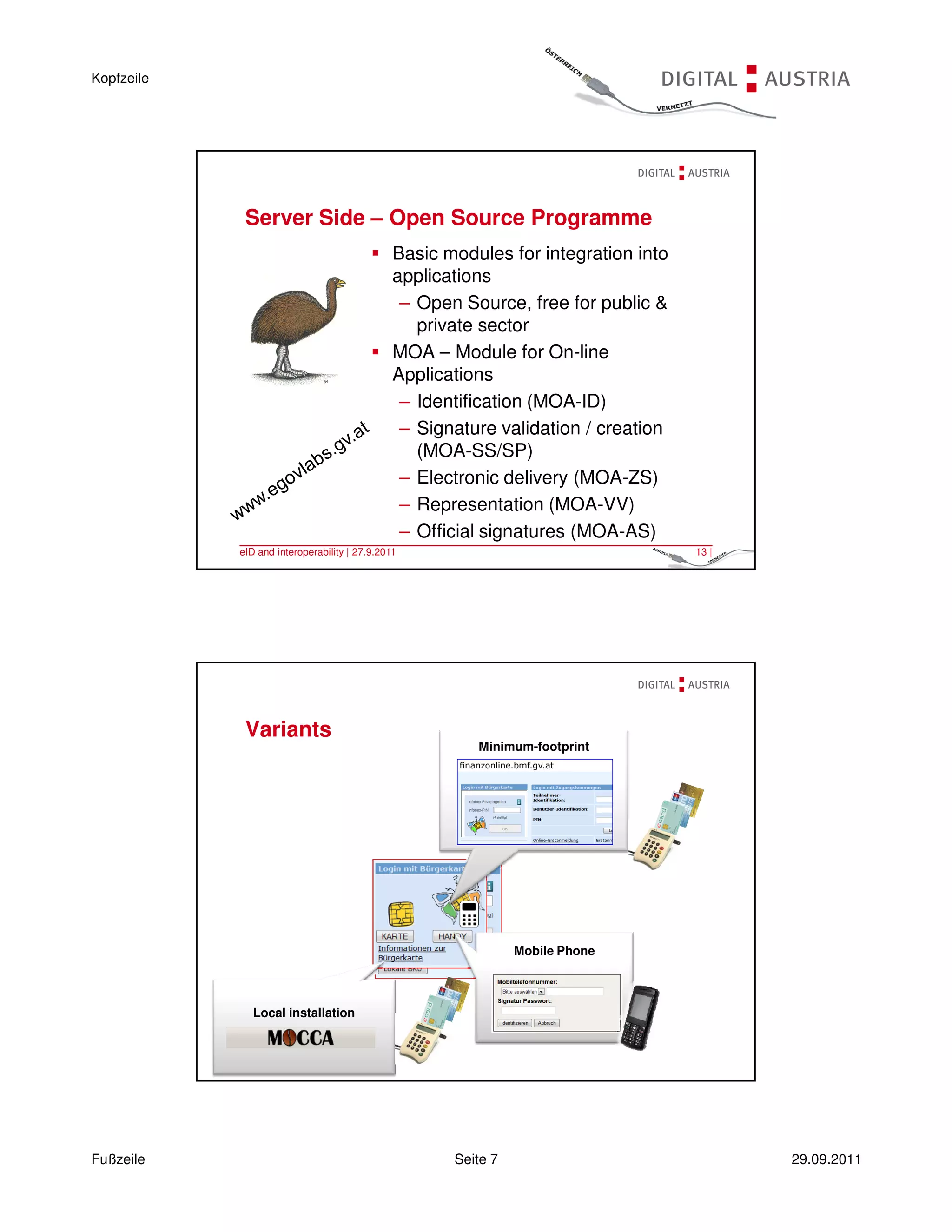
- Citizen cards have been issued on physical cards like health insurance cards as well as digitally through mobile phone signatures.
![Kopfzeile
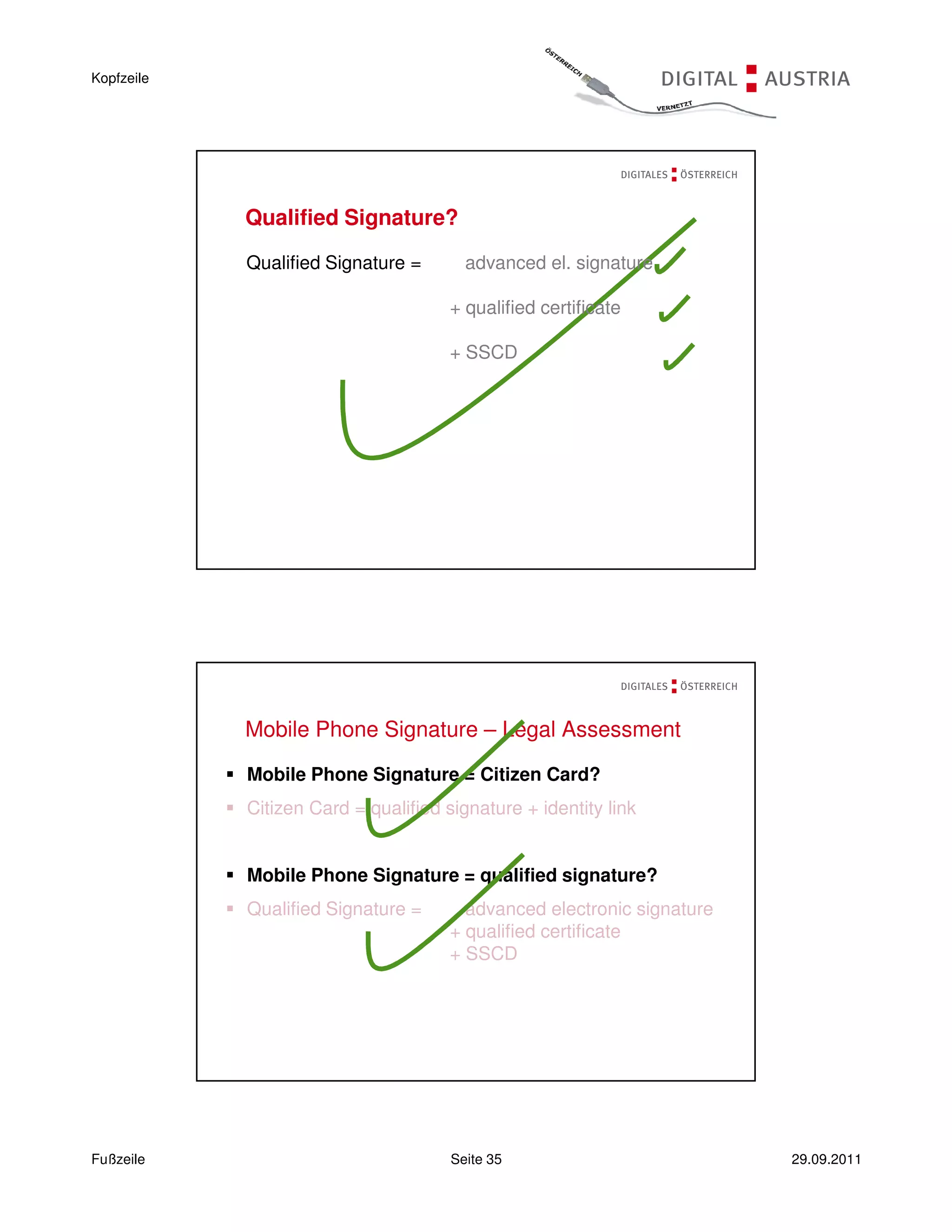
„using means that the signatory can maintain under
his sole control “
Signature-creation authorised only by the signatory
Multifactor authentication: knowledge and possession
Does “can maintain under sole control” mean that it must
be ensured by hardware means? NO!
„…to be assumed that ‘sole control’ can be achieved with appropriate
technical or organisational means even with software certificates
[…] … security measures need to be in place providing that the
signatory can enforce his sole control…“ (RV 293 BlgNR 23. GP)
– see also FESA - working paper on advanced
electronic signatures and “Public Statement on Server
Based Signature Services”: “…FESA members believe that
sole control at least of the signature creation data can be achieved
and that advanced electronic signatures can be created by a
server based signature service…“!
Advanced Electronic Signature
is uniquely linked to the signatory
it is capable of identifying the signatory
it is created using means that the signatory can maintain
under his sole control
it is linked to the data to which it relates in such a manner
that any subsequent change of the data is detectable
Fußzeile Seite 30 29.09.2011](https://image.slidesharecdn.com/tutorial3peterkustor-110929151024-phpapp01/75/Tutorial-3-peter-kustor-30-2048.jpg)