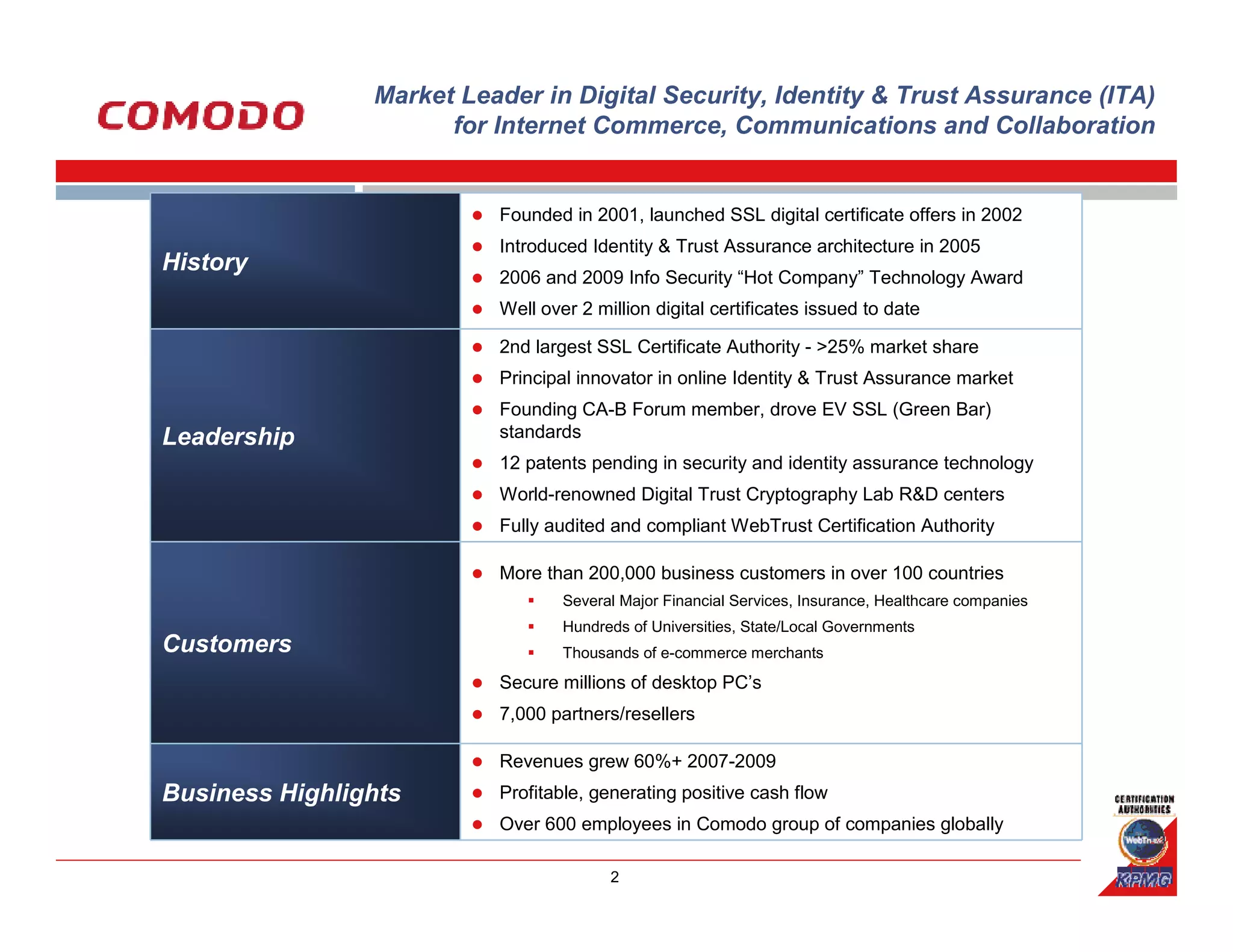
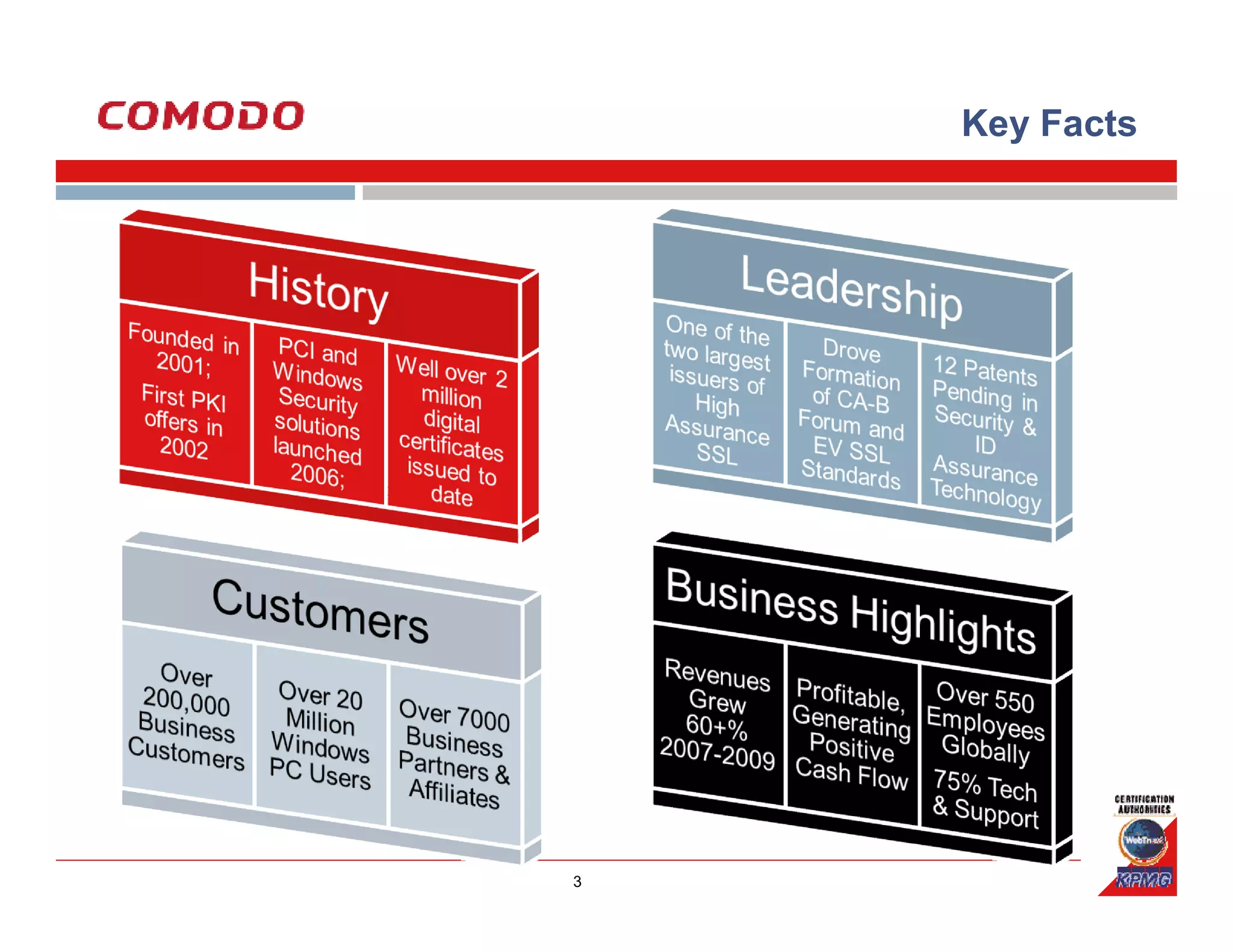
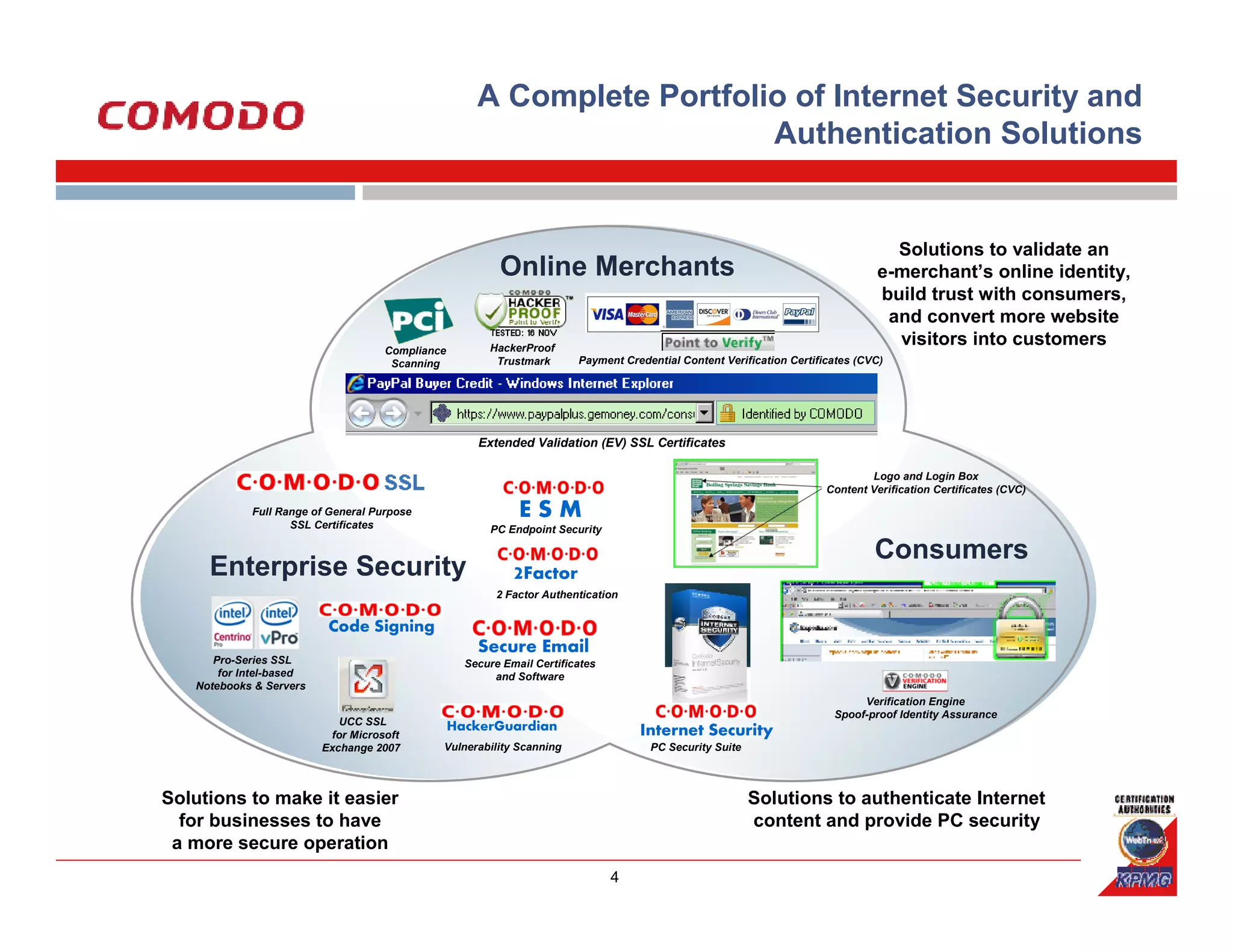
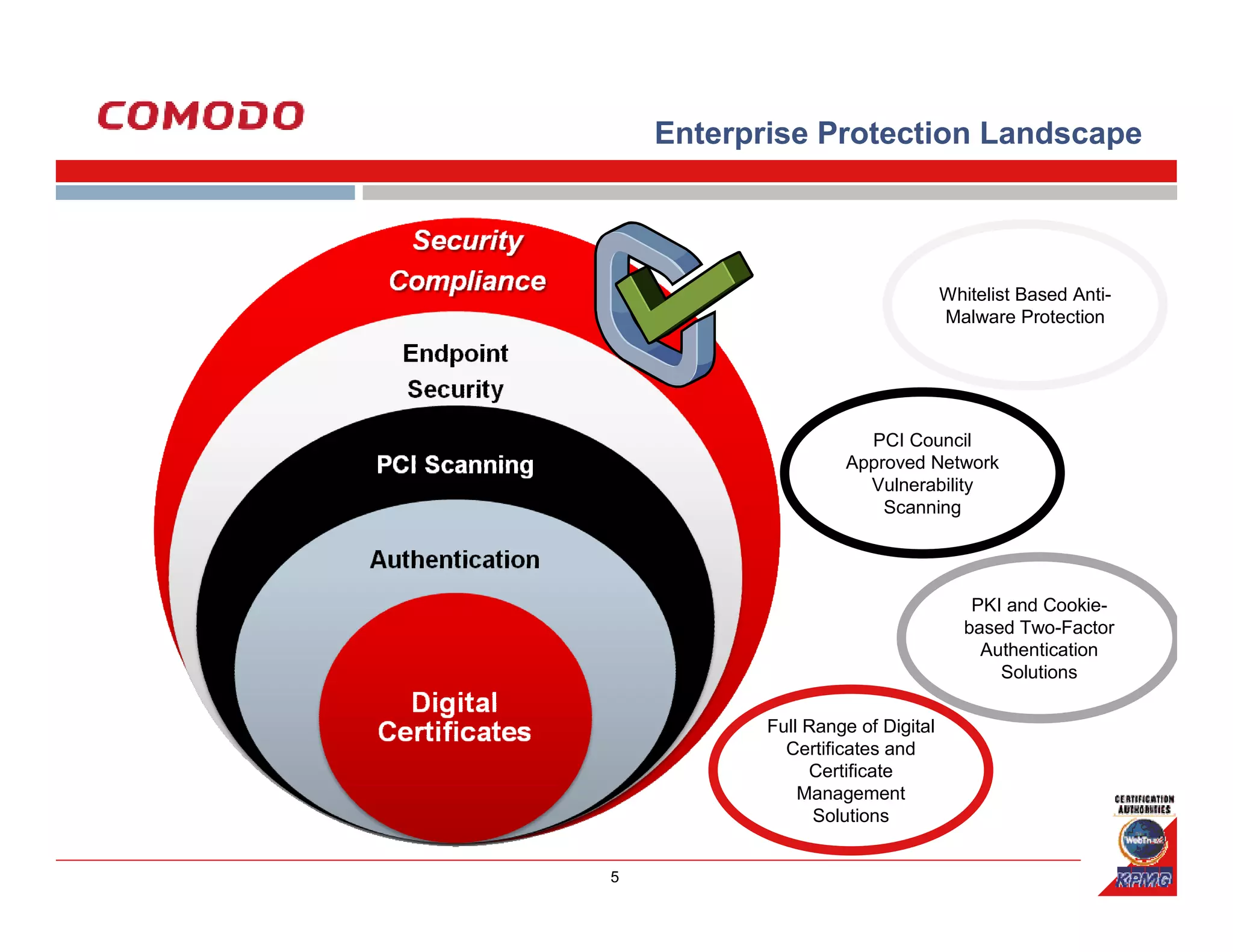
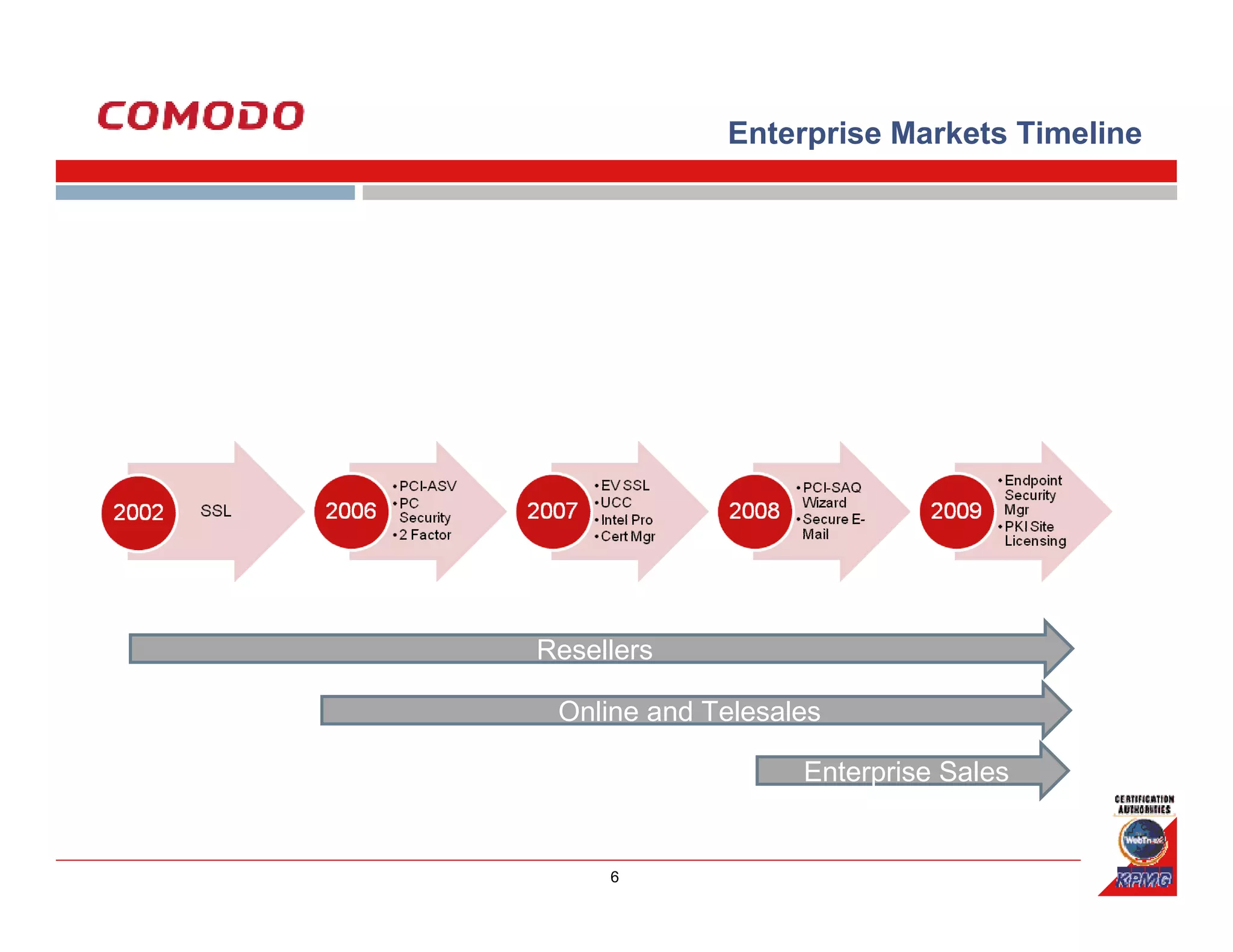
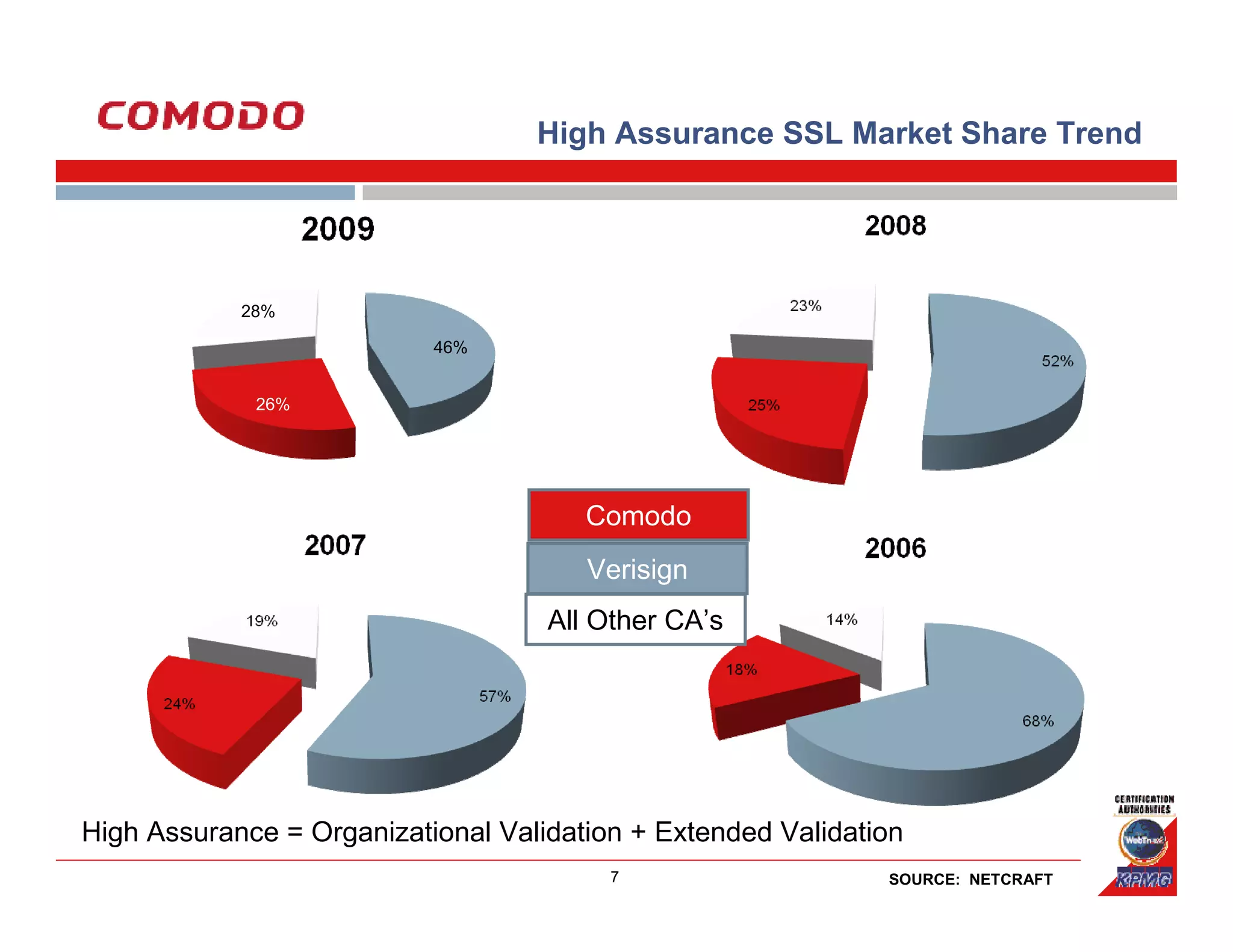
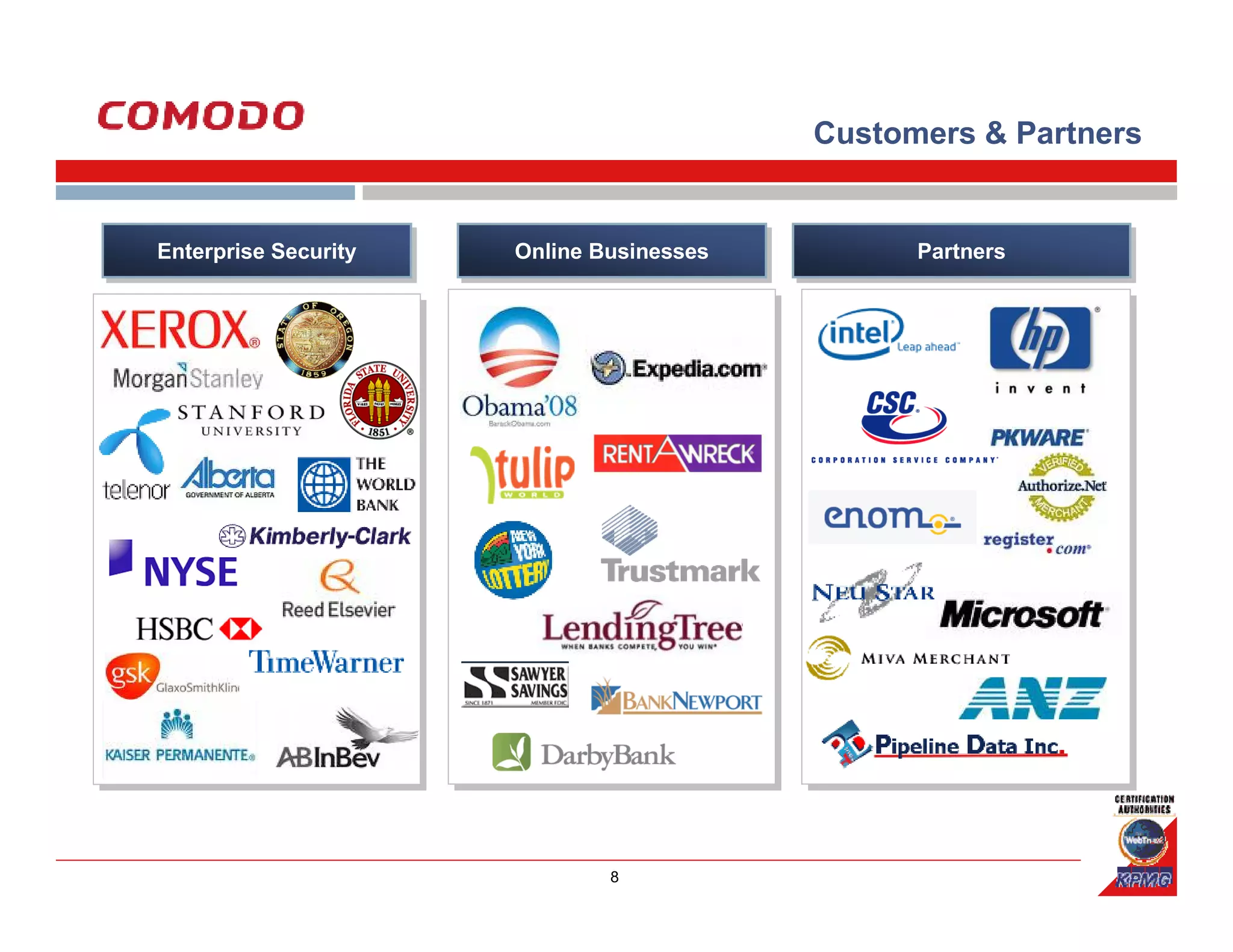
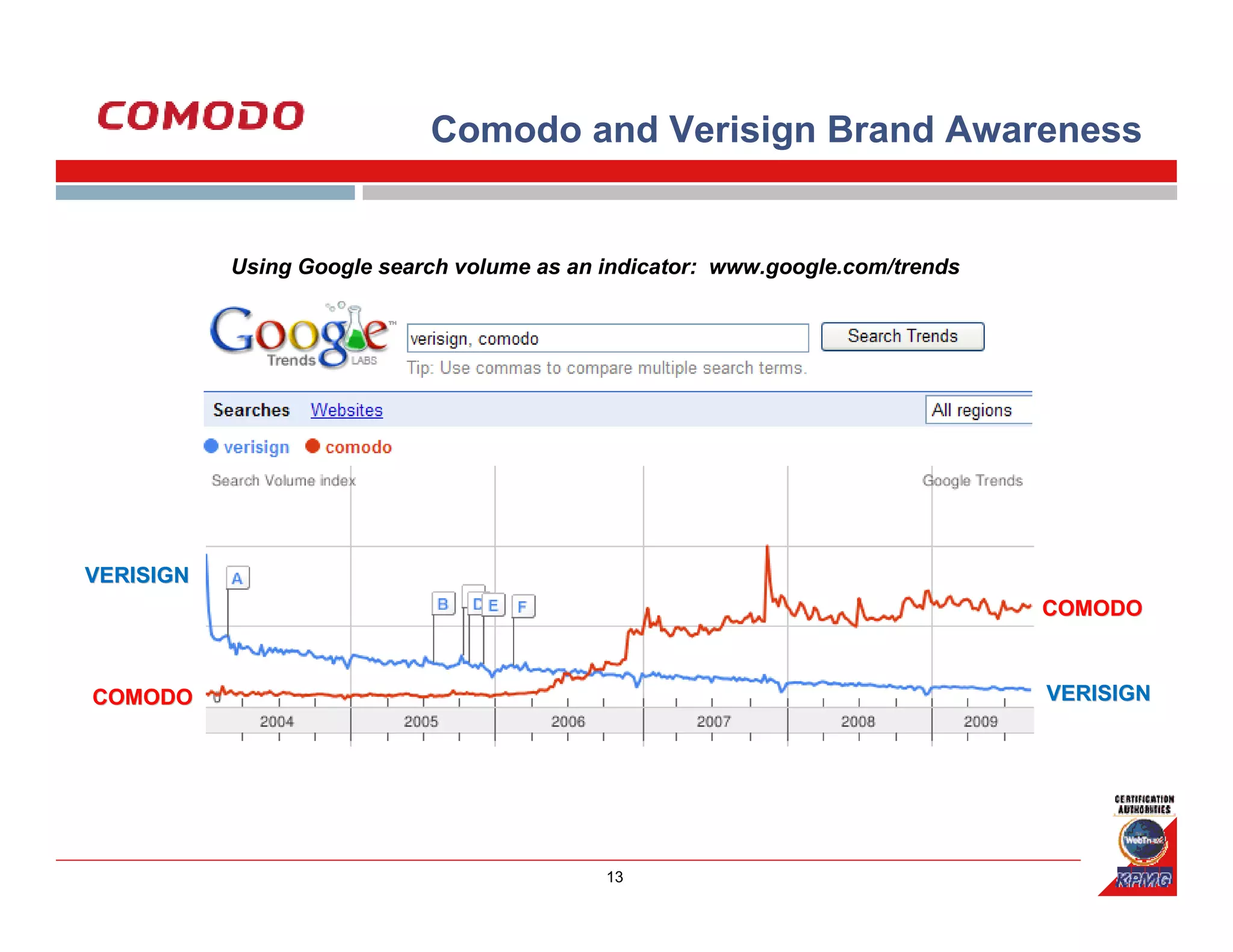
Comodo is a leading digital security company that was founded in 2001. It has over 2 million digital certificates issued and is the 2nd largest SSL certificate authority with over 25% of the market share. Comodo offers a complete portfolio of internet security and authentication solutions for businesses, online merchants, and consumers.