This document discusses bringing your own device (BYOD) security and Cidway's solutions. It addresses:
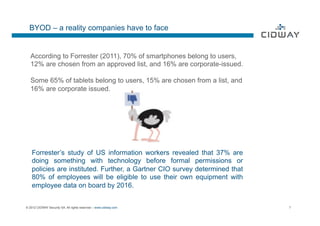
- BYOD as a reality for many companies as personal devices enter the workplace
- Different corporate strategies for BYOD ranging from not allowing to having agreed policies
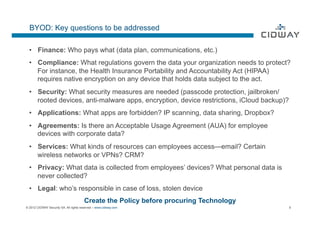
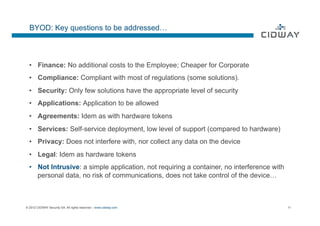
- Key questions around BYOD like who pays for data/devices, compliance, security, applications access
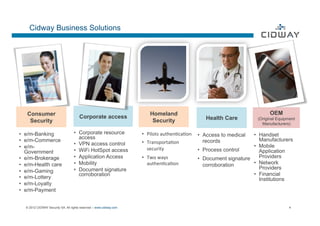
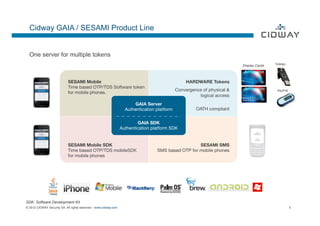
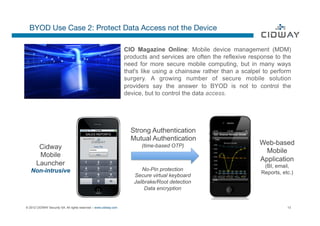
- Cidway's mobile authentication application that allows authentication without intruding on devices
- A mobile launcher application that protects access to corporate data, not the device itself
- Potential issues with requiring employees to purchase their own devices for work (BYOD 2.0)