The document provides an outline for a tutor session on UNIX operating systems. It covers the history of UNIX, the structure of UNIX including the kernel, shells, and file system, getting started with logging in and exiting, and an overview of UNIX commands that will be discussed such as directory navigation, file maintenance, display commands, and text processing. The tutor session aims to introduce students to the basic concepts and usage of UNIX operating systems.

![Tutor Session - 2
Unix Structure
Chulalongkorn
University (Cont)
Unix System Structure
Kernel - controls hardware
- handles input/output
- manages file system
- manages memory
- schedules processes
Hardware
System Calls
Shell - accepts and executes user
Programs=Commands commands [command interpreter]
7 2110313 Operating Systems and System Programs (1/2010)](https://image.slidesharecdn.com/tutor02-introductiontounixoperatingsystem-130413144657-phpapp02/85/SysProg-Tutor-02-Introduction-to-Unix-Operating-System-7-320.jpg)
![Tutor Session - 2
Unix Command Line Structure
Chulalongkorn
University
Unix Command Line Structure
$ command [options] [arguments]
Unix manual / Help
$ man command_name
$ man -k keyword
$ man -k “key words”
19 2110313 Operating Systems and System Programs (1/2010)](https://image.slidesharecdn.com/tutor02-introductiontounixoperatingsystem-130413144657-phpapp02/85/SysProg-Tutor-02-Introduction-to-Unix-Operating-System-19-320.jpg)
![Tutor Session - 2
Unix Command Line Structure
Chulalongkorn
University (Cont)
Directory Navigation and Control
cd [directory]
change directory
ls [options] [directory or file]
list directory contents or file permissions
mkdir [options] directory
make a directory
pwd
print working (current) directory
rmdir [options] directory
remove a directory
23 2110313 Operating Systems and System Programs (1/2010)](https://image.slidesharecdn.com/tutor02-introductiontounixoperatingsystem-130413144657-phpapp02/85/SysProg-Tutor-02-Introduction-to-Unix-Operating-System-23-320.jpg)
![Tutor Session - 2
Unix Command Line Structure
Chulalongkorn
University (Cont)
File Maintenance Commands
chgrp [options] group file
change the group of the file
chmod [options] file
change file or directory access permissions
chown [options] owner file
change the ownership of a file; can only be done by the
superuser
cp [options] file1 file2
copy file1 into file2; file2 shouldn't already exist. This
command creates or overwrites file2.
27 2110313 Operating Systems and System Programs (1/2010)](https://image.slidesharecdn.com/tutor02-introductiontounixoperatingsystem-130413144657-phpapp02/85/SysProg-Tutor-02-Introduction-to-Unix-Operating-System-27-320.jpg)
![Tutor Session - 2
Unix Command Line Structure
Chulalongkorn
University (Cont)
File Maintenance Commands (Cont)
mv [options] file1 file2
move file1 into file2
rm [options] file
remove (delete) a file or directory (-r recursively
deletes the directory and its contents) (-i prompts
before removing files)
28 2110313 Operating Systems and System Programs (1/2010)](https://image.slidesharecdn.com/tutor02-introductiontounixoperatingsystem-130413144657-phpapp02/85/SysProg-Tutor-02-Introduction-to-Unix-Operating-System-28-320.jpg)
![Tutor Session - 2
Unix Command Line Structure
Chulalongkorn
University (Cont)
Display Commands
cat [options] file
concatenate (list) a file
echo [text string]
echo the text string to stdout
head [-number] file
display the first 10 (or number of) lines of a file
more (or less or pg ) [options] file
page through a text file
tail [options] file
display the last few lines (or parts) of a file
29 2110313 Operating Systems and System Programs (1/2010)](https://image.slidesharecdn.com/tutor02-introductiontounixoperatingsystem-130413144657-phpapp02/85/SysProg-Tutor-02-Introduction-to-Unix-Operating-System-29-320.jpg)
![Tutor Session - 2
Special Unix Features
Chulalongkorn
University (Cont)
Wild Cards
? match any single character
* match any string of zero or more characters
[abc] match anyone of the enclosed characters
[a-s] match any character in the range a through s
[!def] (sh) match any characters not one of
[^def] (csh) the enclosed characters
34 2110313 Operating Systems and System Programs (1/2010)](https://image.slidesharecdn.com/tutor02-introductiontounixoperatingsystem-130413144657-phpapp02/85/SysProg-Tutor-02-Introduction-to-Unix-Operating-System-34-320.jpg)
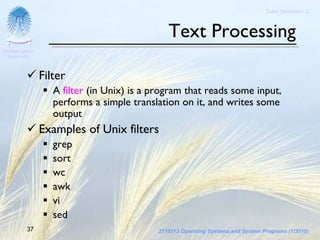
![Tutor Session - 2
Text Processing
Chulalongkorn
University (Cont)
Text Processing Commands
awk [options] file
scan for patterns in a file and process the results
grep [options] 'search string' file
search the argument (in this case probably a file) for all
occurrences of the search string, and list them.
sed [options] file
stream editor for editing files from a script or from the
command line
38 2110313 Operating Systems and System Programs (1/2010)](https://image.slidesharecdn.com/tutor02-introductiontounixoperatingsystem-130413144657-phpapp02/85/SysProg-Tutor-02-Introduction-to-Unix-Operating-System-38-320.jpg)
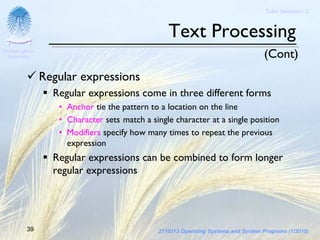
![Tutor Session - 2
Text Processing
Chulalongkorn
University (Cont)
Regular expressions (Cont)
. match any single character except newline
* match zero or more instances of single
expression preceding it
[abc] match any of the characters enclosed
[a-d] match any character in enclosed range
[^abc]match any character NOT in the enclosed set
^exp regular expression must start at the beginning
of the line
40 2110313 Operating Systems and System Programs (1/2010)](https://image.slidesharecdn.com/tutor02-introductiontounixoperatingsystem-130413144657-phpapp02/85/SysProg-Tutor-02-Introduction-to-Unix-Operating-System-40-320.jpg)
![Tutor Session - 2
Other Useful Commands
Chulalongkorn
University
Working With Files
cmp [options] file1 file2
compare two files and list where differences occur
(text or binary files)
cut [options] [file(s)]
cut specified field(s)/character(s) from lines in file(s)
diff [options] file1 file2
compare the two files and display the differences (text
files only)
file [options] file
classify the file type
42 2110313 Operating Systems and System Programs (1/2010)](https://image.slidesharecdn.com/tutor02-introductiontounixoperatingsystem-130413144657-phpapp02/85/SysProg-Tutor-02-Introduction-to-Unix-Operating-System-42-320.jpg)
![Tutor Session - 2
Other Useful Commands
Chulalongkorn
University (Cont)
Working With Files (Cont)
find directory [options] [actions]
find files matching a type or pattern
ln [options] source_file
target link the source_file to the target
paste [options] file
paste field(s) onto the lines in file
sort [options] file
sort the lines of the file according to the options
chosen
43 2110313 Operating Systems and System Programs (1/2010)](https://image.slidesharecdn.com/tutor02-introductiontounixoperatingsystem-130413144657-phpapp02/85/SysProg-Tutor-02-Introduction-to-Unix-Operating-System-43-320.jpg)
![Tutor Session - 2
Other Useful Commands
Chulalongkorn
University (Cont)
Working With Files (Cont)
strings [options] file
report any sequence of 4 or more printable characters
ending in <NL> or <NULL>. Usually used to search
binary files for ASCII strings.
tee [options] file
copy stdout to one or more files
touch [options] [date] file
create an empty file, or update the access time of an
existing file
44 2110313 Operating Systems and System Programs (1/2010)](https://image.slidesharecdn.com/tutor02-introductiontounixoperatingsystem-130413144657-phpapp02/85/SysProg-Tutor-02-Introduction-to-Unix-Operating-System-44-320.jpg)
![Tutor Session - 2
Other Useful Commands
Chulalongkorn
University (Cont)
Working With Files (Cont)
tr [options] string1 string2
translate the characters in string1 from stdin into
those in string2 in stdout
uniq [options] file
remove repeated lines in a file
wc [options] [file(s)]
display word (or character or line) count for file(s)
45 2110313 Operating Systems and System Programs (1/2010)](https://image.slidesharecdn.com/tutor02-introductiontounixoperatingsystem-130413144657-phpapp02/85/SysProg-Tutor-02-Introduction-to-Unix-Operating-System-45-320.jpg)
![Tutor Session - 2
Other Useful Commands
Chulalongkorn
University (Cont)
File Archiving, Compression and Conversion
compress/uncompress/zcat [options]
file[.Z]
compress or uncompress a file. Compressed files are
stored with a .Z ending.
gzip/gunzip/zcat [options] file[.gz]
compress or uncompress a file. Compressed files are
stored with a .gz ending
46 2110313 Operating Systems and System Programs (1/2010)](https://image.slidesharecdn.com/tutor02-introductiontounixoperatingsystem-130413144657-phpapp02/85/SysProg-Tutor-02-Introduction-to-Unix-Operating-System-46-320.jpg)
![Tutor Session - 2
Other Useful Commands
Chulalongkorn
University (Cont)
File Archiving, Compression and Conversion
tar key[options] [file(s)]
tape archiver--refer to man pages for details on
creating, listing, and retrieving from archive files. Tar
files can be stored on tape or disk.
47 2110313 Operating Systems and System Programs (1/2010)](https://image.slidesharecdn.com/tutor02-introductiontounixoperatingsystem-130413144657-phpapp02/85/SysProg-Tutor-02-Introduction-to-Unix-Operating-System-47-320.jpg)
![Tutor Session - 2
Other Useful Commands
Chulalongkorn
University (Cont)
Remote Connections
finger [options] user[@hostname]
report information about users on local and remote
machines
ftp [options] host
transfer file(s) using file transfer protocol
rcp [options] hostname
remotely copy files from this machine to another
machine
48 2110313 Operating Systems and System Programs (1/2010)](https://image.slidesharecdn.com/tutor02-introductiontounixoperatingsystem-130413144657-phpapp02/85/SysProg-Tutor-02-Introduction-to-Unix-Operating-System-48-320.jpg)
![Tutor Session - 2
Other Useful Commands
Chulalongkorn
University (Cont)
Remote Connections
rlogin [options] hostname
login remotely to another machine
rsh [options] hostname
remote shell to run on another machine
telnet [host [port]]
communicate with another host using telnet protocol
49 2110313 Operating Systems and System Programs (1/2010)](https://image.slidesharecdn.com/tutor02-introductiontounixoperatingsystem-130413144657-phpapp02/85/SysProg-Tutor-02-Introduction-to-Unix-Operating-System-49-320.jpg)