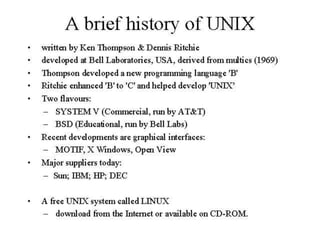
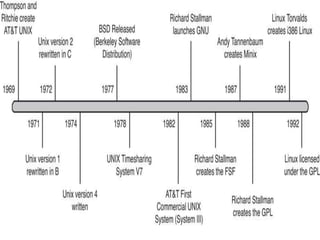
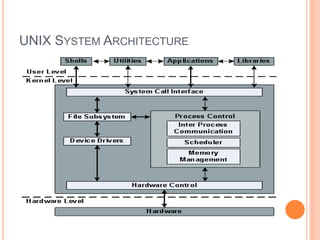
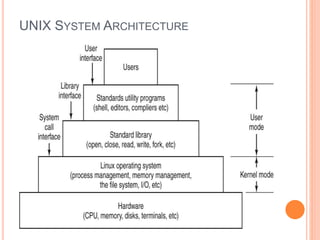
This document provides an introduction to the UNIX operating system. It discusses the history and development of UNIX, the key components of the UNIX system architecture including the kernel, shells/GUIs, and file system. It also outlines common UNIX commands and sessions, describing how to log in and out, change passwords, and view system information. The document is intended to explain the basic concepts and components of UNIX to new users.

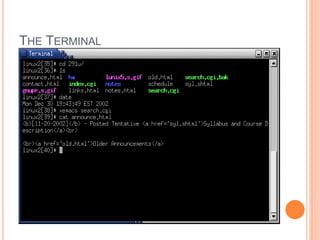


![UNAME
uname command displays features of the operating
system running on you machine.
By default, it displays the name of operating
system.
Syntax: uname [options]
Option Purpose
-m Prints the machine hardware name.
-n It tells hostname
-r Print the operating system release level
-s Print the name of the operating system
-v Print the operating system version](https://image.slidesharecdn.com/chapter1introductiontounix-230704162201-f7fb7a47/85/CHAPTER-1-INTRODUCTION-TO-UNIX-pptx-40-320.jpg)