This document provides an outline for a tutor session on UNIX shell script programming. It introduces shells and shell scripts, and covers topics like variables, data operations, decision statements like if-else and switch-case, and iteration statements like for loops and while loops. Examples are provided throughout to illustrate different shell script programming concepts and syntax. Links to additional online resources on shell scripting are also included at the end.








![Tutor Session - 3
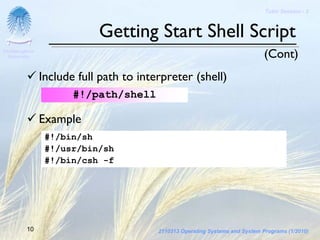
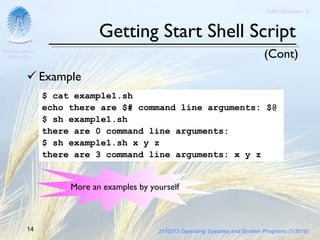
Getting Start Shell Script
Chulalongkorn
University (Cont)
Using vi command to create shell script file
Running shell script by using the command below
sh [file]
Example
$ vi test.sh
...
$ sh test.sh
11 2110313 Operating Systems and System Programs (1/2010)](https://image.slidesharecdn.com/tutor03-unixshellscriptprogramming-130413144657-phpapp02/85/SysProg-Tutor-03-Unix-Shell-Script-Programming-11-320.jpg)
![Tutor Session - 3
Getting Start Shell Script
Chulalongkorn
University (Cont)
Interaction with user
Output value
echo [texts/variables]
Input value
read [variables]
Comment line
# your comments
12 2110313 Operating Systems and System Programs (1/2010)](https://image.slidesharecdn.com/tutor03-unixshellscriptprogramming-130413144657-phpapp02/85/SysProg-Tutor-03-Unix-Shell-Script-Programming-12-320.jpg)


![Tutor Session - 3
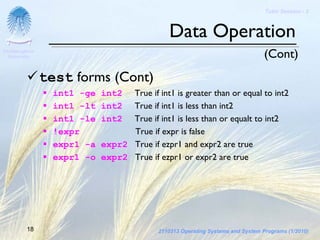
Data Operation
Chulalongkorn
University (Cont)
Conditional Expressions
test [expression]
test returns a zero exit code if expression evaluates to true;
otherwise, nonzero exit status
test forms
-d filename True if filname exists as a directory file
-f filename True if filname exists as a nondirectory file
-l string True if length of string is nonzero
-n string True if string contains at least one character
16 2110313 Operating Systems and System Programs (1/2010)](https://image.slidesharecdn.com/tutor03-unixshellscriptprogramming-130413144657-phpapp02/85/SysProg-Tutor-03-Unix-Shell-Script-Programming-16-320.jpg)

![Tutor Session - 3
Decision Statement
Chulalongkorn
University
If-else statement
if [condition]
then [result]
elif [condition]
then [result]
else
[result]
fi
19 2110313 Operating Systems and System Programs (1/2010)](https://image.slidesharecdn.com/tutor03-unixshellscriptprogramming-130413144657-phpapp02/85/SysProg-Tutor-03-Unix-Shell-Script-Programming-19-320.jpg)
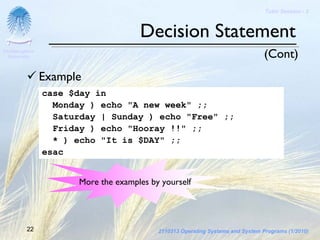
![Tutor Session - 3
Decision Statement
Chulalongkorn
University (Cont)
Example
if test -r file1
then echo "file1"
elif [ -r file2 ] test –r file2
then cp file2 file3
echo "file2 copy to file3"
else
echo "no file"
fi
More the examples by yourself
20 2110313 Operating Systems and System Programs (1/2010)](https://image.slidesharecdn.com/tutor03-unixshellscriptprogramming-130413144657-phpapp02/85/SysProg-Tutor-03-Unix-Shell-Script-Programming-20-320.jpg)
![Tutor Session - 3
Decision Statement
Chulalongkorn
University (Cont)
Switch-case statement
case $var in
value1) [result] ;;
value2) [result] ;;
...
*) [result] ;;
Default case
esac
21 2110313 Operating Systems and System Programs (1/2010)](https://image.slidesharecdn.com/tutor03-unixshellscriptprogramming-130413144657-phpapp02/85/SysProg-Tutor-03-Unix-Shell-Script-Programming-21-320.jpg)
![Tutor Session - 3
Iteration Statement
Chulalongkorn
University
For statement
for var {in [word]+}
do
[result]
done
Iterate the value of the variable var through each word in the word
list
Evaluate the command in list after each iteration
If no word is supplied, $@ ($1 ..) is used instead
A break command causes the loop to terminate
A continue command causes the loop to jump to the next iteration
23 2110313 Operating Systems and System Programs (1/2010)](https://image.slidesharecdn.com/tutor03-unixshellscriptprogramming-130413144657-phpapp02/85/SysProg-Tutor-03-Unix-Shell-Script-Programming-23-320.jpg)

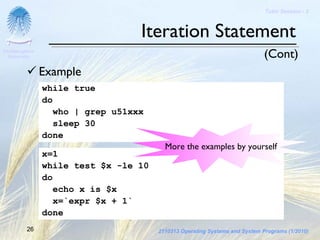
![Tutor Session - 3
Iteration Statement
Chulalongkorn
University (Cont)
While statement
while [condition]
do test $var1 –opt $var2
[result]
done
25 2110313 Operating Systems and System Programs (1/2010)](https://image.slidesharecdn.com/tutor03-unixshellscriptprogramming-130413144657-phpapp02/85/SysProg-Tutor-03-Unix-Shell-Script-Programming-25-320.jpg)
![Tutor Session - 3
See More
Chulalongkorn
University
[1] http://www.grymoire.com/Unix/Sh.html
[2] http://www.ooblick.com/text/sh/
[3] http://www.injunea.demon.co.uk/pages/page204.htm
27 2110313 Operating Systems and System Programs (1/2010)](https://image.slidesharecdn.com/tutor03-unixshellscriptprogramming-130413144657-phpapp02/85/SysProg-Tutor-03-Unix-Shell-Script-Programming-27-320.jpg)
