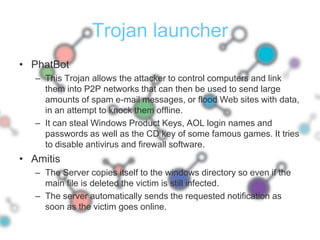
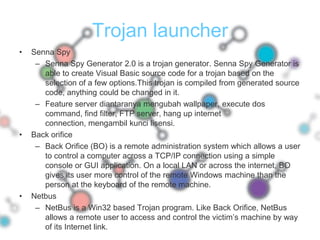
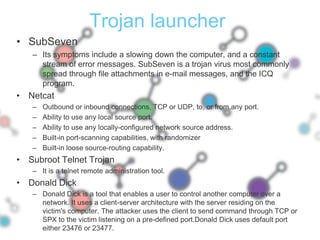
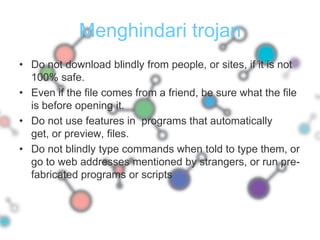
The document discusses various types of trojans and how they work. It describes remote access trojans, password sending trojans, keyloggers, and other types of trojans. It also discusses how trojans are used to gain unauthorized access to systems and steal sensitive information. The document provides signs that a system may be infected with a trojan and outlines best practices for preventing trojan infections.