Trie Data Structure
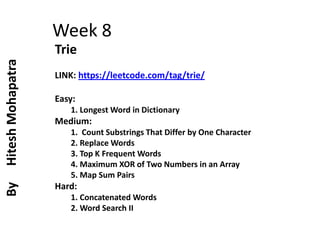
- 1. Week 8 Trie LINK: https://leetcode.com/tag/trie/ Easy: 1. Longest Word in Dictionary Medium: 1. Count Substrings That Differ by One Character 2. Replace Words 3. Top K Frequent Words 4. Maximum XOR of Two Numbers in an Array 5. Map Sum Pairs Hard: 1. Concatenated Words 2. Word Search II By Hitesh Mohapatra
- 2. Trie Data Structure But there’s another structure that was created to solve the very problem of representing a set of words: a trie. The term “trie” comes from the word retrieval, and is usually pronounced “try”, to distinguish it from other “tree” structures.
- 3. Cont.. A trie is a tree-like data structure whose nodes store the letters of an alphabet. By structuring the nodes in a particular way, words and strings can be retrieved from the structure by traversing down a branch path of the tree.
- 4. Cont.. The size of a trie is directly correlated to the size of all the possible values that the trie could represent. Each trie has an empty root node, with links (or references) to other nodes — one for each possible alphabetic value.
- 5. So where do the letters of different words live if the root node doesn’t house them all ? In the example shown here, we have a trie that has an empty root node, which has references to children nodes. If we look at the cross-section of one of these child nodes, we’ll notice that a single node in a trie contains just two things: 1. A value, which might be null 2. An array of references to child nodes, all of which also might be null
- 6. So, once we have a root node, where do we go from there? It’s time to try growing our trie! In the trie shown below, we’re representing the nursery rhyme that starts off with something like “Peter Piper picked a peck of pickled peppers”. We also have six different words that we’re representing in this trie: Peter, piper, picked, peck, pickl ed, and peppers.
- 7. Cont.. But how do we actually go about checking if the word exists? And how do we insert the letters into their correct places? We know that we’ll have an empty root node, which will have a value of "", and an array with 26 references in it, all of which will be empty (pointing to null) to start. Let’s say that we want to insert the word "pie", and give it a value of 5. Another way to think about it is that we have a hash that looks like this: { "pie": 5 }.
- 8. In the future, if we want to retrieve the value for the key "pie", we’ll traverse down from one array to another, using the indices to go from the nodes p, to i, to e; when we get to the node at the index for e, we’ll stop traversing, and retrieve the value from that node, which will be 5. In the illustration shown here, if we search for the key "pie", we traverse down each node’s array, and look to see if there is a value for the branch path: p-i-e. If it does have a value, we can simply return it. This is sometimes referred to as a search hit, since we were able to find a value for the key. If we won’t found then that will be called as search miss.
- 9. Finally, there’s one other action that we might want to do to our trie: delete things! How can we remove a key and its value from our trie structure? To illustrate this, I’ve added another word to our trie. We now have both the keys "pie" and "pies", each with their own values. Let’s say we want to remove the key "pies" from our trie.
- 10. Programs
- 11. Longest Word in Dictionary Given a list of strings words representing an English Dictionary, find the longest word in words that can be built one character at a time by other words in words. If there is more than one possible answer, return the longest word with the smallest lexicographical order. If there is no answer, return the empty string.
- 12. Example
- 13. Solution Trie + Depth-First Search Intuition • As prefixes of strings are involved, this is usually a natural fit for a trie (a prefix tree.) Algorithm • Put every word in a trie, then depth-first-search from the start of the trie, only searching nodes that ended a word. Every node found (except the root, which is a special case) then represents a word with all it's prefixes present. We take the best such word.
- 14. Count Substrings That Differ by One Character Given two strings s and t, find the number of ways you can choose a non-empty substring of s and replace a single character by a different character such that the resulting substring is a substring of t. In other words, find the number of substrings in s that differ from some substring in t by exactly one character. For example, the underlined substrings in "computer" and "computation" only differ by the 'e'/'a', so this is a valid way. Return the number of substrings that satisfy the condition above. A substring is a contiguous sequence of characters within a string.
- 16. Example
- 17. Explanation S = a, b, e T= b, b, c a == b, d=1, ans++ (1) ab == bb d=1, ans++ (1,2) abe == bbc d=2, ans++ (1,2), Break ---- S = a, b, e T= b, b, c a == b. d=1, ans++ (1,2,3) ab == bc, d=2, ans++ (1,2,3,) Break ------- S = a, b, e T= b, b, c a == c, d=1, ans ++ (1,2,3,4) S = a, b, e T= b, b, c b == b, d=0, ans++ (1,2,3,4) be == bb, d=1, ans++ (1,2,3,4,5) be == bc, d =1, ans++ (1,2,3,4,5,6), Break ---- S = a, b, e T= b, b, c be == bc, d=1, ans++ (1,2,3,4,5,6,7) Break ----- S = a, b, e T= b, b, c e == b, d=1, ans++ (1,2,3,4,5,6,7,8) e == b, d=1, ans++ (1,2,3,4,5,6,7,8,9) e == c, d =1, ans++ (1,2,3,4,5,6,7,8,9,10), Break ----
- 18. Replace Words • In English, we have a concept called root, which can be followed by some other word to form another longer word - let's call this word successor. For example, when the root "an" is followed by the successor word "other", we can form a new word "another". • Given a dictionary consisting of many roots and a sentence consisting of words separated by spaces, replace all the successors in the sentence with the root forming it. If a successor can be replaced by more than one root, replace it with the root that has the shortest length. • Return the sentence after the replacement.
- 19. Example
- 20. Example
- 21. Solution • Traverse the string, if the current character is not ‘’, add a little bit to generate a word. After each addition, check the dictionary for root. If there is, • Just add root to the answer, and the word will no longer look for root in the dictionary. If the current character is ‘’, it means that a word has been generated. If this word • Without root, then add this complete word to the answer.
- 22. Top K Frequent Words Given a non-empty list of words, return the k most frequent elements. Your answer should be sorted by frequency from highest to lowest. If two words have the same frequency, then the word with the lower alphabetical order comes first.
- 23. Example
- 25. Algorithm
- 26. Maximum XOR of Two Numbers in an Array Given an integer array nums, return the maximum result of nums[i] XOR nums[j], where 0 ≤ i ≤ j < n.
- 28. Solution • Convert the given numbers into binary format • Do XOR operation by the trie tree. • Strore the maximum
- 29. Binary conversion and XOR 3 0 0 0 1 1 10 0 1 0 1 0 5 0 0 1 0 1 25 1 1 0 0 1 2 0 0 0 1 0 8 0 1 0 0 0 0 0 1 0 1 1 0 1 0 1 0 1 1 1 1 0 0 0 0 0 3 0 0 0 1 1 25 1 1 0 0 1 XOR 1 1 0 1 0 0+2+0+8+ 16 = 22 24 23 22 21 20
- 30. Map Sum Pairs Implement the MapSum class: MapSum() Initializes the MapSum object. void insert(String key, int val) Inserts the key-val pair into the map. If the key already existed, the original key- value pair will be overridden to the new one. int sum(string prefix) Returns the sum of all the pairs' value whose key starts with the prefix.
- 31. Example
- 32. Solution • Use a trie to save each string, and use a map in trie for recording value of each string. • Once there is a string be inserted into this trie, update the delta value which is inserted value — current value in nodes on the updating path.
- 33. Concatenated Words Given an array of strings words (without duplicates), return all the concatenated words in the given list of words. A concatenated word is defined as a string that is comprised entirely of at least two shorter words in the given array.
- 36. Solution
- 37. Word Search II Given an m x n board of characters and a list of strings words, return all words on the board. Each word must be constructed from letters of sequentially adjacent cells, where adjacent cells are horizontally or vertically neighboring. The same letter cell may not be used more than once in a word.
- 42. DFS + Hash Map
- 43. DFS + Trie
- 47. The End
