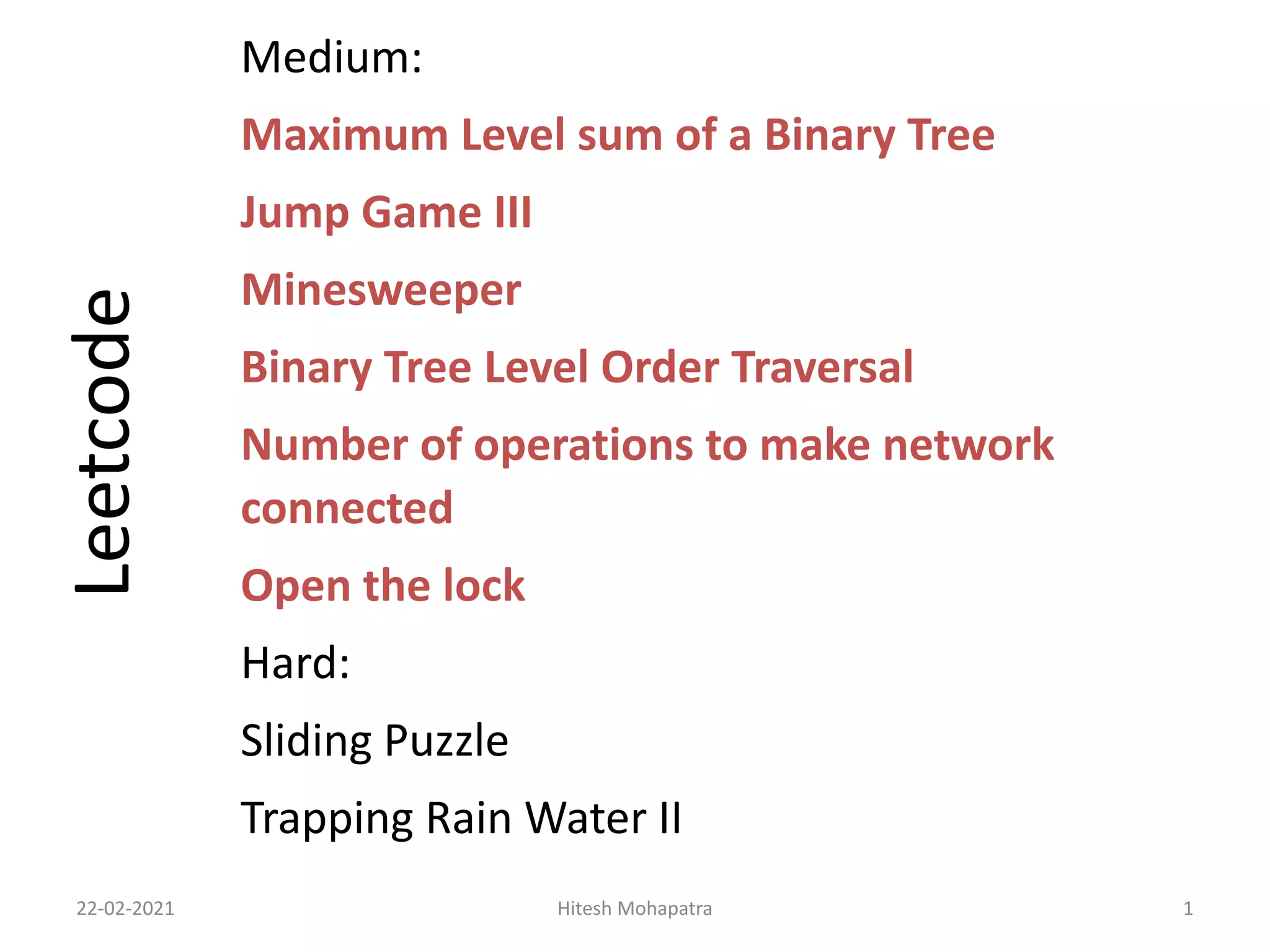
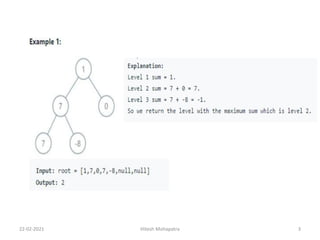
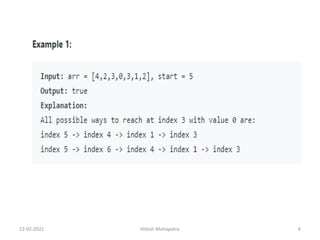
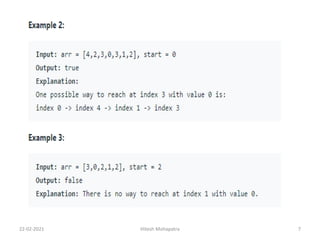
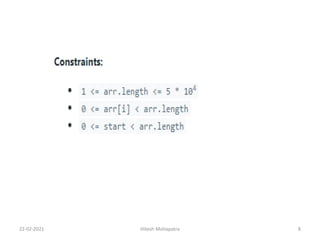
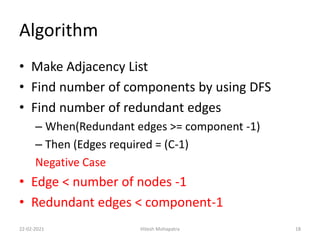
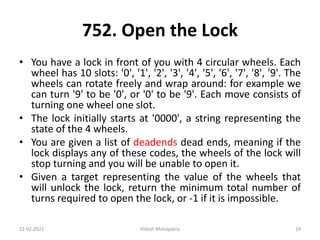
The document contains descriptions of several LeetCode problems ranging from Medium to Hard difficulty. It provides details about the Maximum Level Sum of a Binary Tree, Jump Game III, Minesweeper, Binary Tree Level Order Traversal, Number of Operations to Make Network Connected, Open the Lock, Sliding Puzzle, and Trapping Rain Water II problems. It also includes pseudocode and explanations for solving the Number of Operations to Make Network Connected and Open the Lock problems.



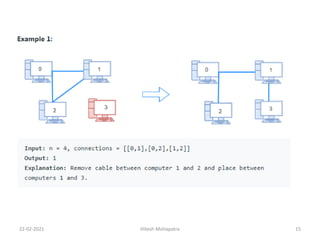
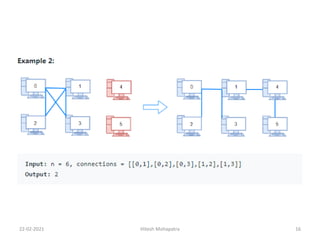
![1319. Number of Operations to Make Network
Connected
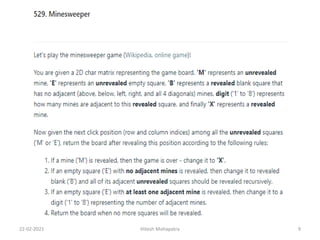
• There are n computers numbered from 0 to n-1 connected
by Ethernet cables connections forming a network
where connections[i] = [a, b] represents a connection
between computers a and b. Any computer can reach any
other computer directly or indirectly through the network.
• Given an initial computer network connections. You can
extract certain cables between two directly connected
computers, and place them between any pair of
disconnected computers to make them directly connected.
Return the minimum number of times you need to do this
in order to make all the computers connected. If it's not
possible, return -1.
22-02-2021 Hitesh Mohapatra 14](https://image.slidesharecdn.com/week3-210222152804/85/Leetcode-Problem-Solution-14-320.jpg)
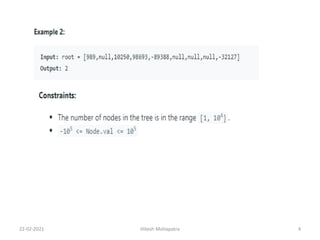
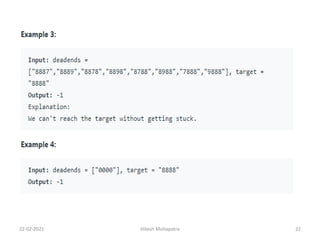
![Target 0202
0000 ------------------------ Initial State
0100 ------------------------1
0200 ------------------------2
0201
0210 ------------------------3
0211 ------------------------4
0212 ------------------------5
0202------------------------ 6 Target
deadends = ["0201","0101","0102","1212","2002"]
22-02-2021 Hitesh Mohapatra 21](https://image.slidesharecdn.com/week3-210222152804/85/Leetcode-Problem-Solution-21-320.jpg)
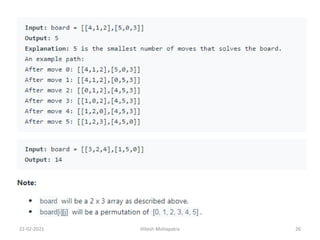
![773. Sliding Puzzle
• On a 2x3 board, there are 5 tiles represented by
the integers 1 through 5, and an empty square
represented by 0.
• A move consists of choosing 0 and a 4-
directionally adjacent number and swapping it.
• The state of the board is solved if and only if
the board is [[1,2,3],[4,5,0]].
• Given a puzzle board, return the least number of
moves required so that the state of the board is
solved. If it is impossible for the state of the
board to be solved, return -1.
22-02-2021 Hitesh Mohapatra 24](https://image.slidesharecdn.com/week3-210222152804/85/Leetcode-Problem-Solution-24-320.jpg)