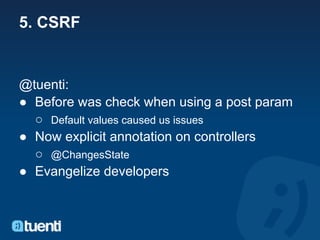
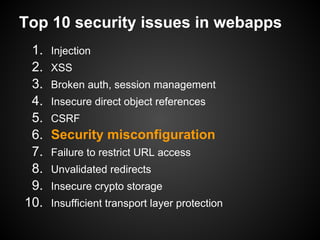
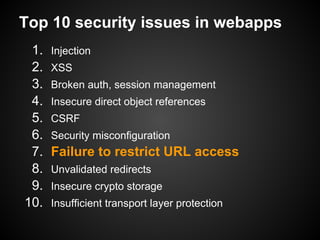
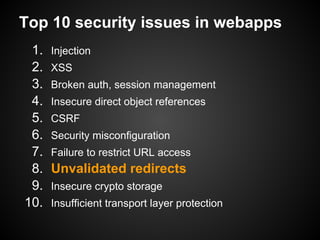
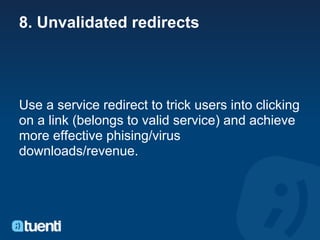
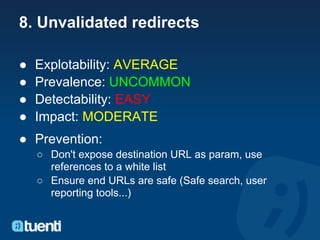
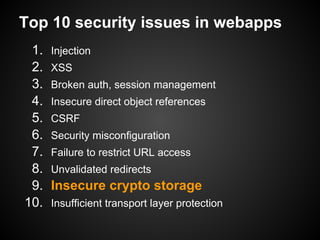
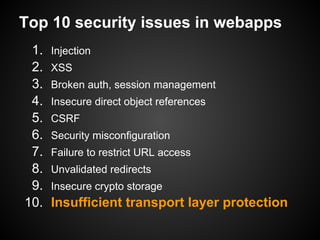
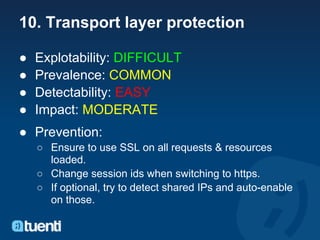
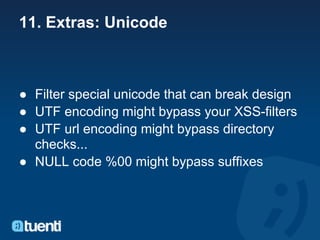
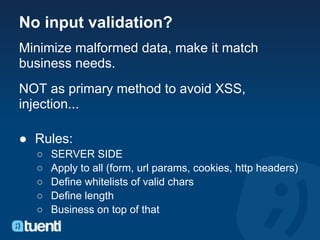
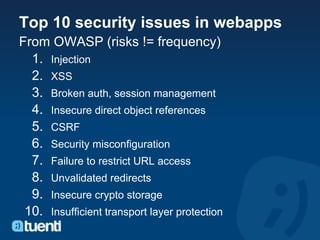
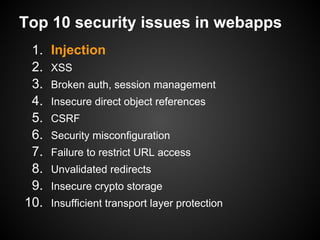
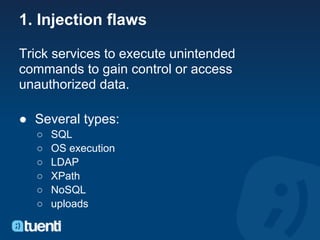
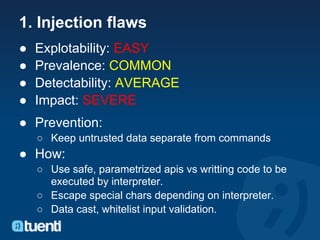
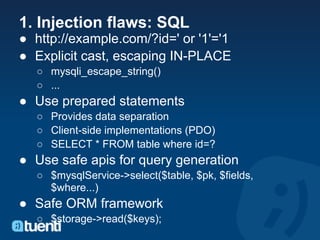
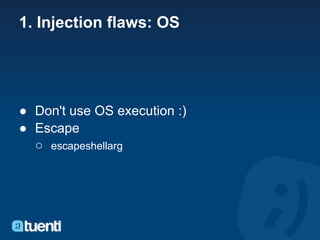
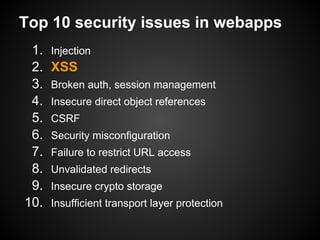
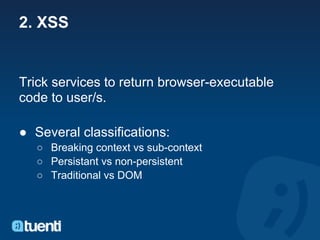
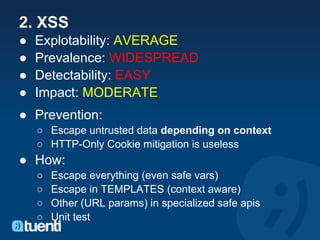
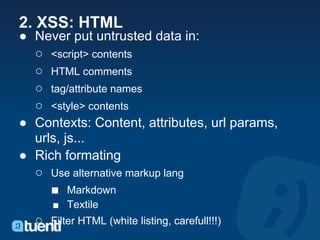
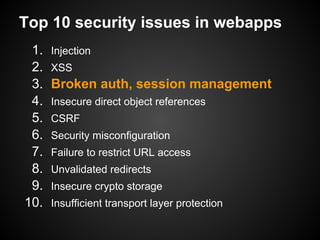
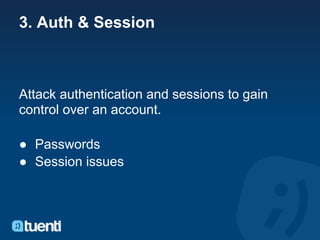
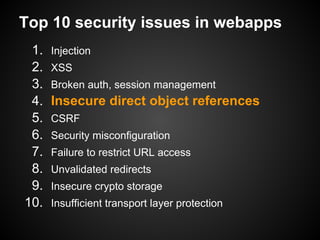
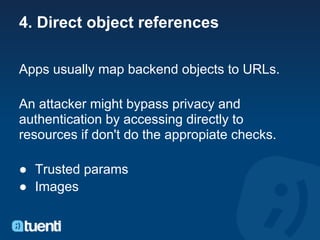
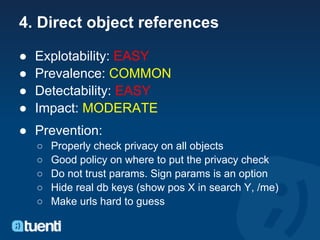
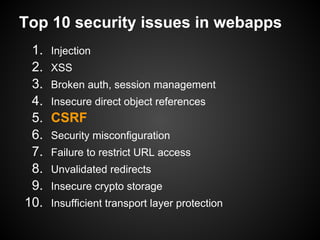
The document discusses web application security and summarizes the top 10 security issues according to OWASP (Open Web Application Security Project). It provides details on each issue, including examples, prevalence, impact, and recommendations for prevention. The top issues are injection, XSS, broken authentication and session management, insecure direct object references, CSRF, security misconfiguration, failure to restrict URL access, unvalidated redirects, insecure cryptographic storage, and insufficient transport layer protection.





![2. XSS: Classification by context
● Breaking context:
○ <a href="?id<?=$_GET['id']?>">
○ "<script> ...
○ Easy to detect & test
■ Unit-test templates with all injections for all vars
and validate html
● Non breaking context:
○ <a href="<?=$_GET['url']?>">
○ javascript: ...
○ HARD TO DETECT](https://image.slidesharecdn.com/bcnwebapplicationsecurity-111121081815-phpapp01/85/Tuenti-Web-Application-Security-17-320.jpg)


![5. CSRF
Cross site request forgery [CSFR in tuenti :)]
Trick a authenticated user to submit requests to
a service and do actions without consent. The
browser will send the cookies and the request
might look legit.
● Image tags (get)
● Forms (post)
● ...](https://image.slidesharecdn.com/bcnwebapplicationsecurity-111121081815-phpapp01/85/Tuenti-Web-Application-Security-37-320.jpg)