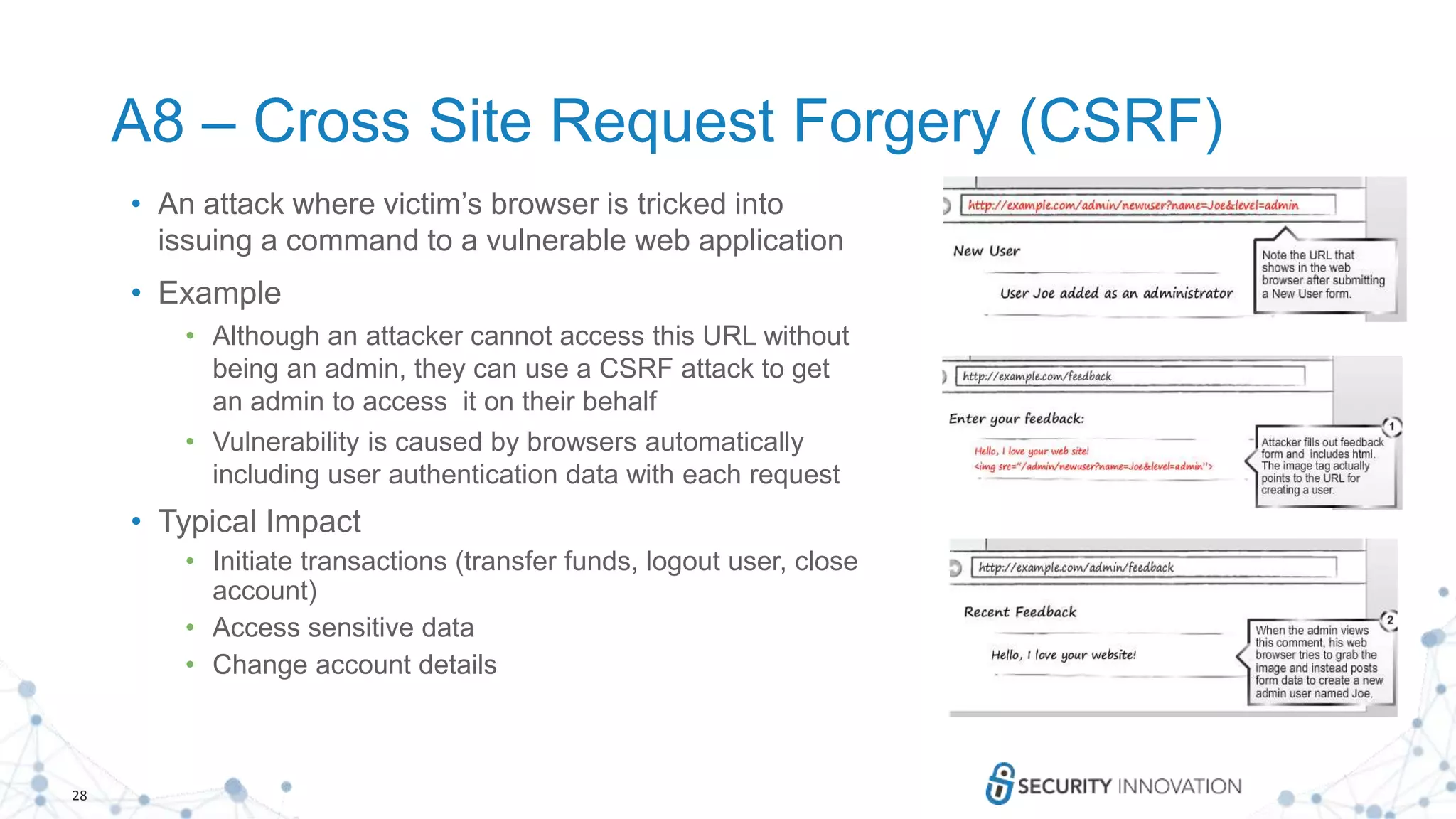
The document presents a comprehensive overview of how to test for the OWASP Top Ten security vulnerabilities in web applications, detailing specific threats such as injection attacks, broken authentication, and cross-site scripting. It outlines steps to identify vulnerabilities, create test data, and analyze responses to safeguard against unauthorized access and data exposure. Additionally, it emphasizes the importance of security best practices and offers resources for further training and assessment in application security.

![6
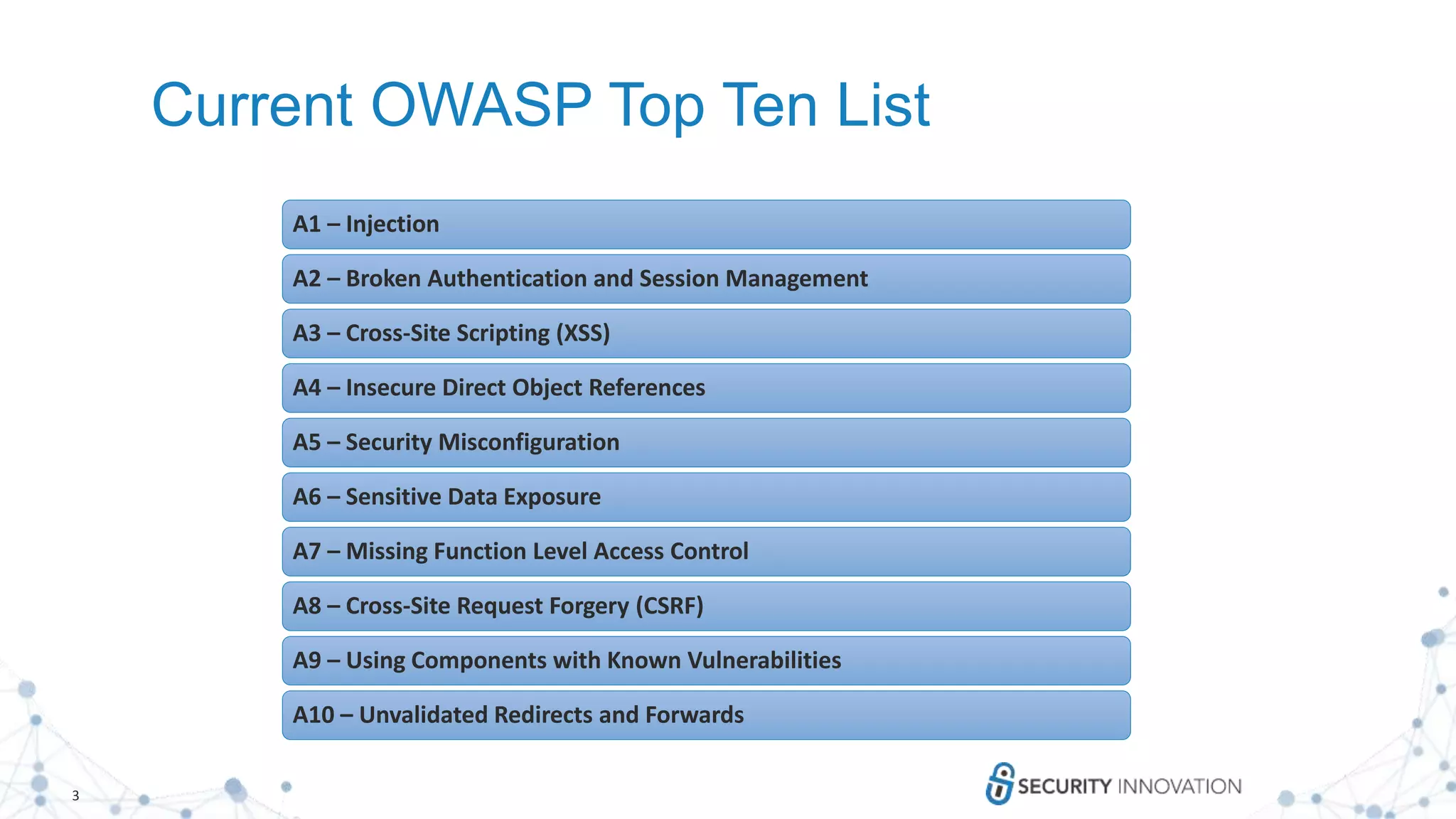
SQL Injection
1. Identify Entry Points
1. Does the feature interact with a backend database?
2. Does it seem like input is used to form the query?
2. Create Test Data
1. ‘ is a string terminator
2. ; is a statement terminator
3. Fuzz data like: xyz') "]
3. Analyze the Response
1. Often will get a server error, sometimes a full stack trace
2. Other times you may see unusual application behavior
4. Dig In
1. xyz' OR 1=1; --
2. xyz' OR 1>2; --](https://image.slidesharecdn.com/howtotestfortheowasptopten-v2-170928182841/75/How-to-Test-for-The-OWASP-Top-Ten-6-2048.jpg)

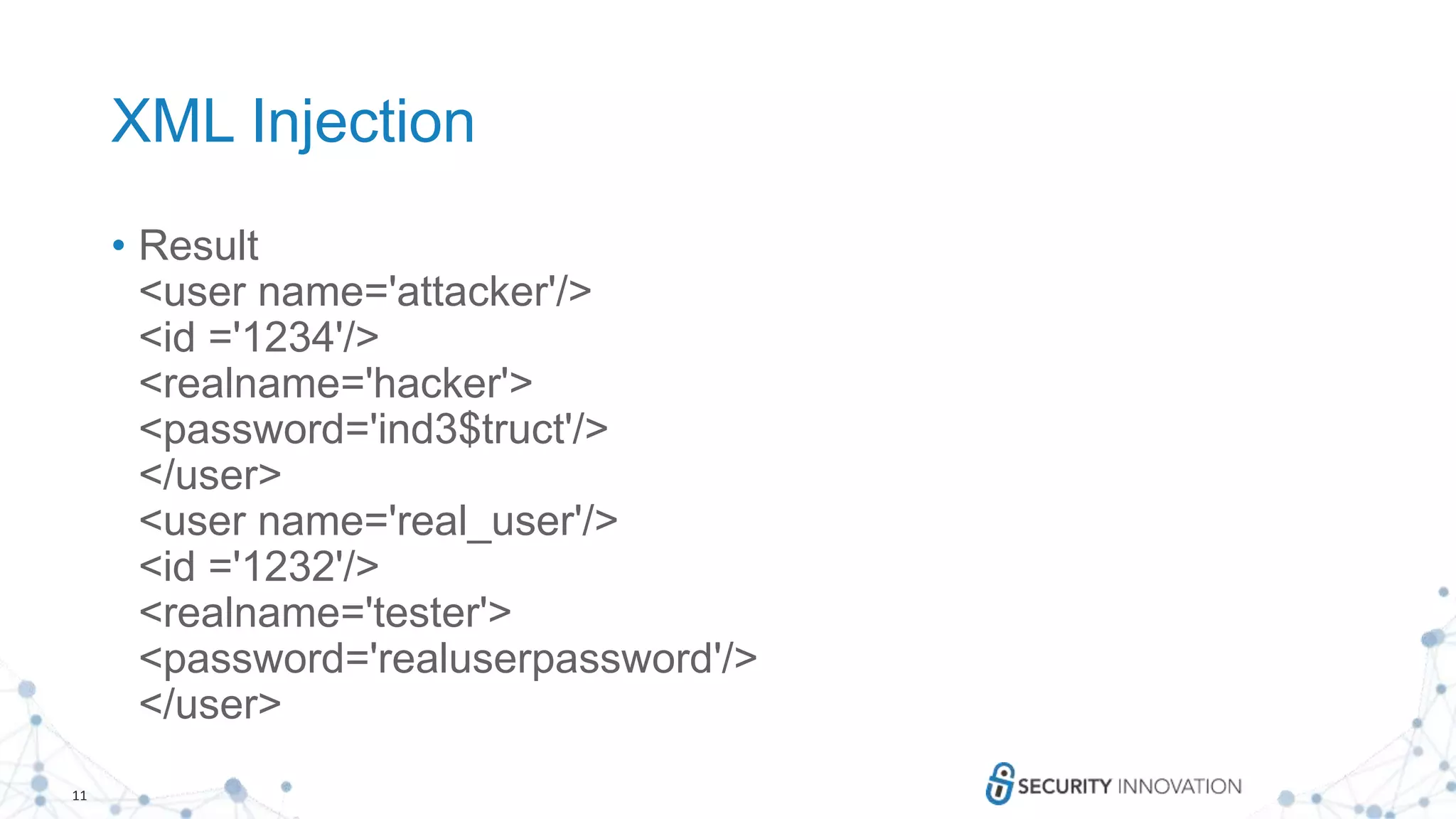
![8
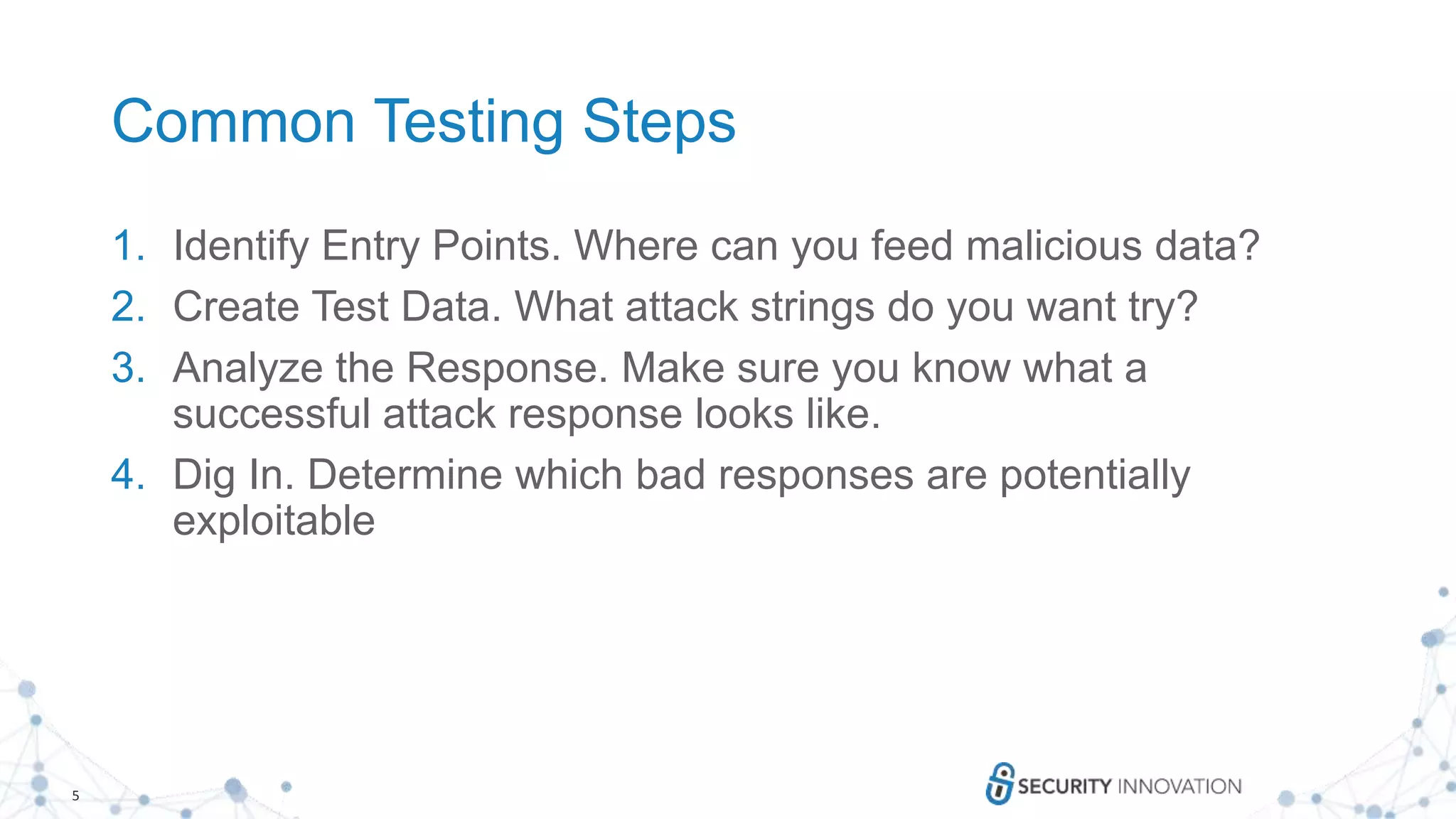
XML Injection
1. Identify Entry Points
1. Look for web services that use XML or SOAP
2. Look for storage of structured XML data
3. Look for XML that is generated by user input
2. Create Test Data
1. Can you add additional tags to store information in the store?
2. Are there CDATA tags that are being used for HTML or Script processing?
3. Create xml fuzz strings using control characters (‘, “, <, >, > ' "<, xyz<!--)
3. Analyze the Response
1. Do you see an XML related error?
2. Do you see your characters added to the XML
4. Dig In
1. Learn from the error message to create a real attack
2. Where is the error coming from? What tags are you impacting?
3. <![CDATA[<script>alert('XSS')</script>]]>](https://image.slidesharecdn.com/howtotestfortheowasptopten-v2-170928182841/75/How-to-Test-for-The-OWASP-Top-Ten-8-2048.jpg)