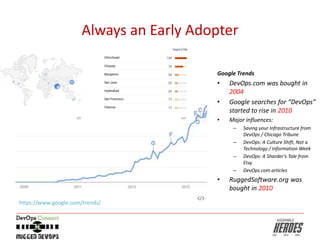
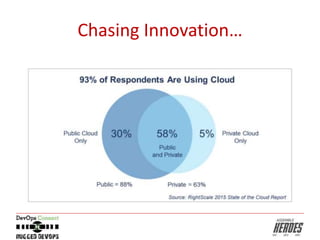
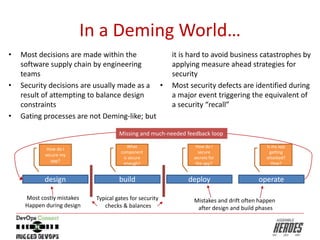
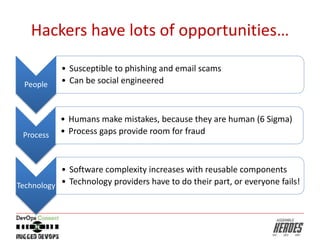
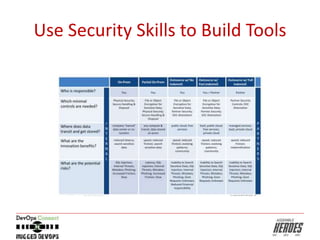
This document discusses the evolution of DevSecOps and provides guidance for security professionals. It notes that DevSecOps approaches have gained popularity as DevOps has grown over the past decade. It recommends that security professionals focus on detection over protection, embrace a blameless culture of continuous improvement, and get involved in DevSecOps communities to help build security tools and practices.