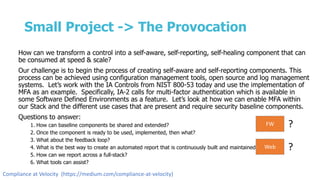
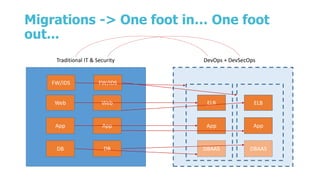
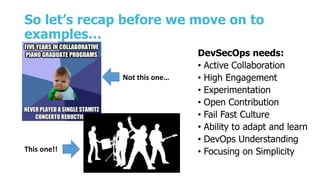
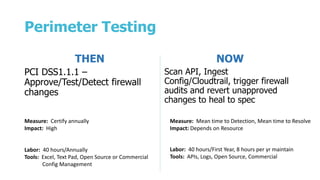
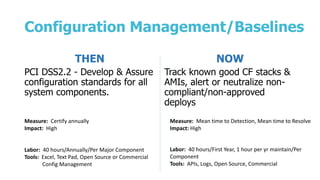
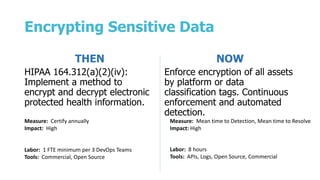
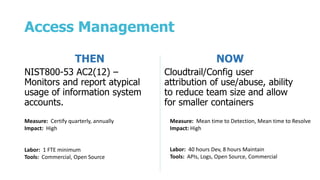
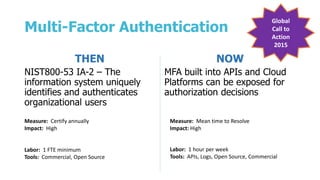
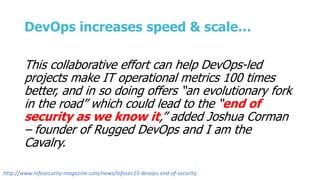
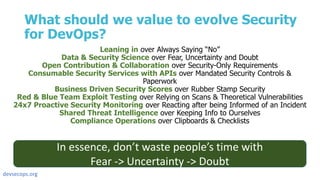
This document discusses the evolution of security practices to enable secure innovation at speed and scale through a DevSecOps approach. It outlines how traditional security controls can be transformed into self-aware, self-reporting components that integrate seamlessly into the DevOps pipeline. Specific examples are provided for how perimeter testing, configuration management, encrypting sensitive data, access management, and multi-factor authentication can move from annual certifications to continuous monitoring and enforcement. The document advocates for collaboration, experimentation, and a focus on simplicity and automation to evolve security practices for DevOps.






![Imagine adding Security into the DevOps
pipeline…
Security Self-Service
skills Biz UX Dev Data App Sec Sec Eng Science
Comp
Ops
Sec Ops Ops Training
Software & Infrastructure Platforms
Software Components & Resources
YOUR APP STACK GOES HERE
Operational Tools & Monitoring
collaboration, partnership, value creation, self-service
[DevOps, Agile, Scrum, Cloud]](https://image.slidesharecdn.com/keynote-final-151022095515-lva1-app6892/85/DevSecCon-KeyNote-London-2015-14-320.jpg)