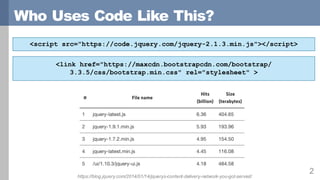
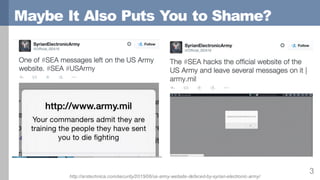
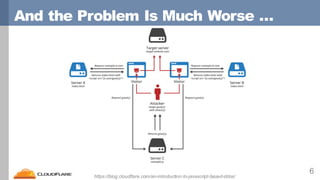
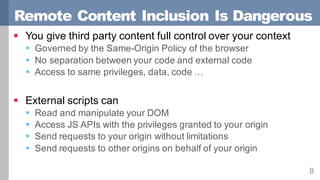
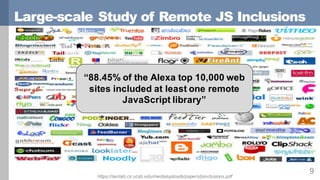
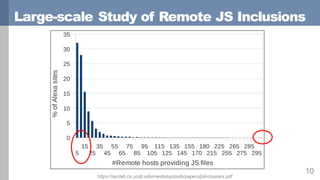
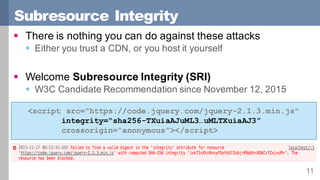
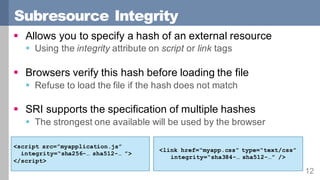
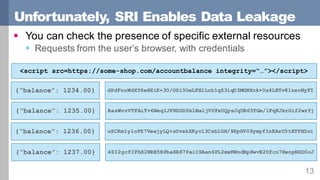
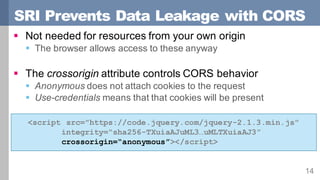
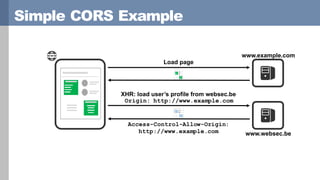
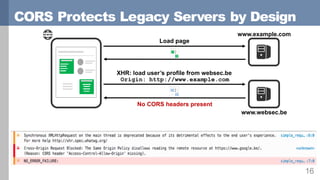
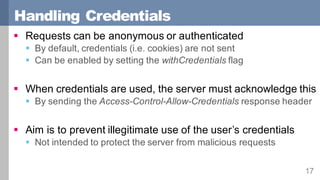
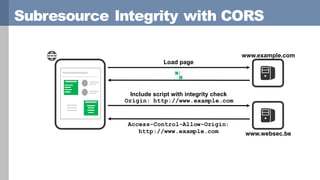
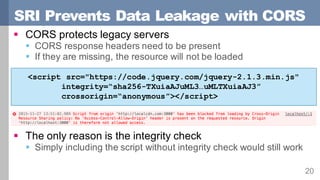
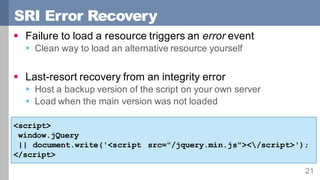
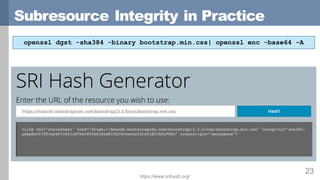
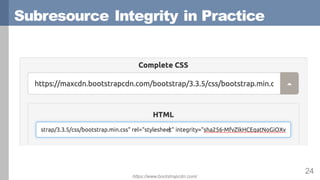
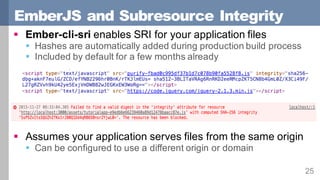
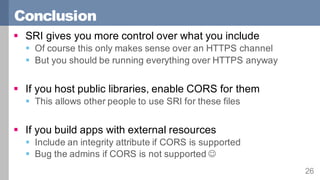
Subresource Integrity (SRI) allows websites to specify a cryptographic hash for external scripts and stylesheets to verify their integrity before loading. A study found 88% of top websites include external JavaScript libraries. SRI helps prevent attacks from compromised CDNs by only loading resources that match the expected hash value. SRI also uses the crossorigin attribute to implement Cross-Origin Resource Sharing (CORS) and prevent data leakage when checking external resources. CORS headers must be present for SRI integrity checks to prevent loading alternative scripts. SRI provides more control over included external content and is supported by libraries like Ember.js.