Embed presentation
Download to read offline

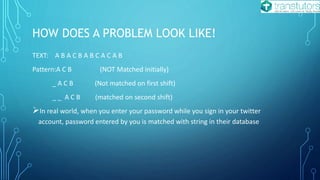


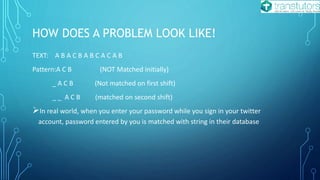
The document defines string matching and classifies algorithms into single and multiple pattern matching. It discusses real-world applications such as security systems, DNA analysis, and password verification, alongside various algorithms like Rabin-Karp, naïve, and Knuth-Morris-Pratt (KMP). The summary highlights different matching approaches and emphasizes the importance of efficient algorithms in solving string matching problems.