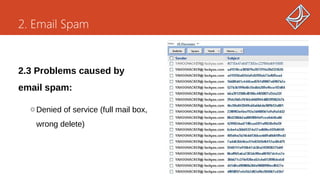
The presentation covers email structure, spam definition and its implications, and various anti-spam techniques, including content-based, header-based, and sender authentication methods. It highlights Gmail's anti-spam solutions and demonstrates how to interpret email headers. The document incorporates insights from Associate Professor Tran Quang Anh and discusses the economic factors behind spam emails.