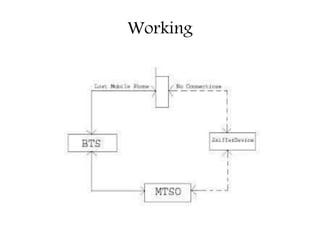
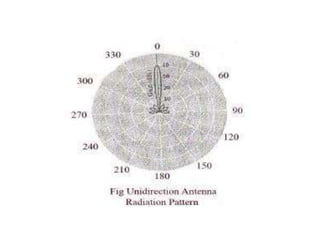
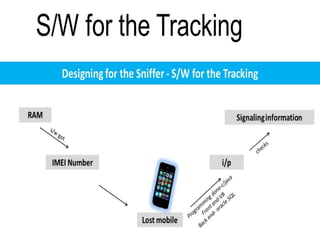
This document describes a proposed sniffer device to detect lost mobile phones. Each mobile has a unique IMEI number transmitted when turned on, which the sniffer would detect using a small base station and directional antenna. The sniffer would operate at a different frequency than local cell towers to avoid interference. Software would track the IMEI number of lost phones and the design aims to be low-cost, low-power, and mobile to help recover lost phones.