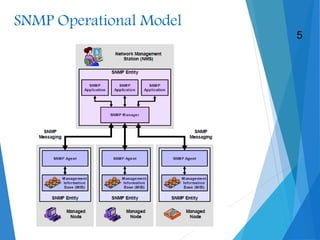
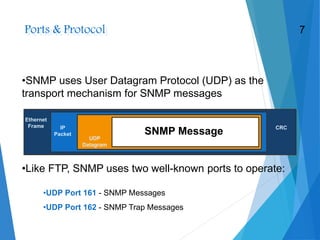
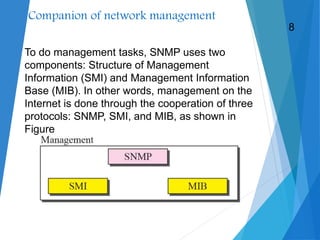
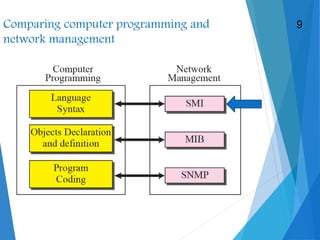
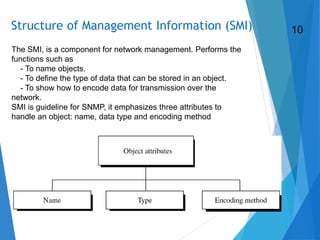
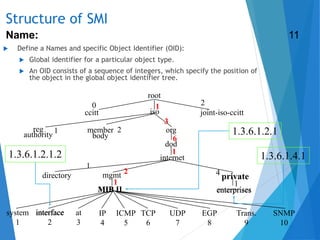
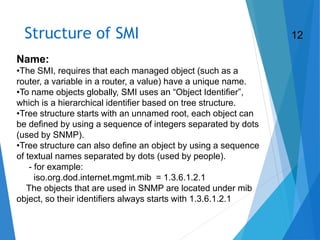
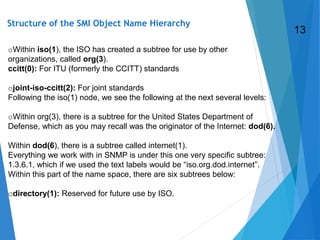
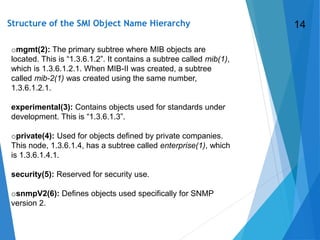
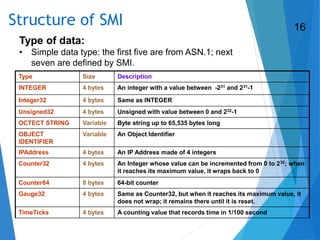
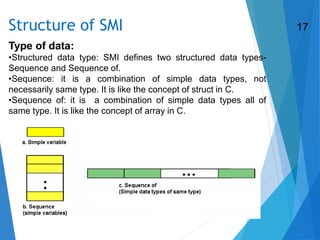
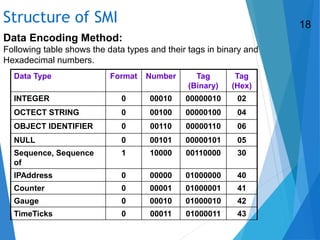
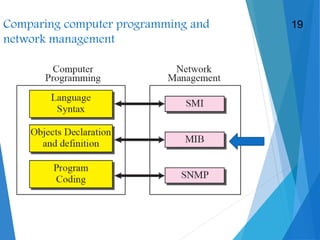
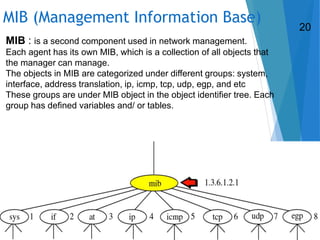
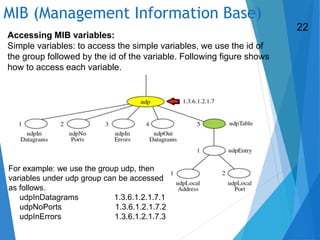
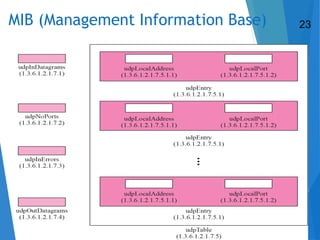
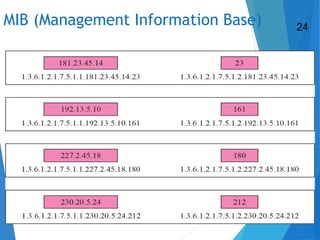
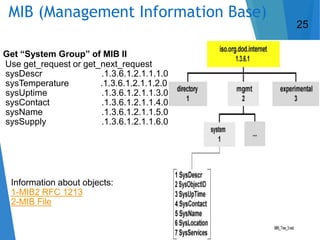
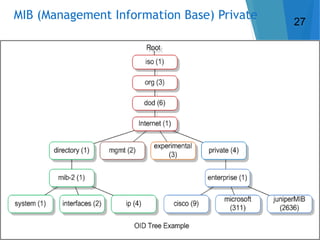
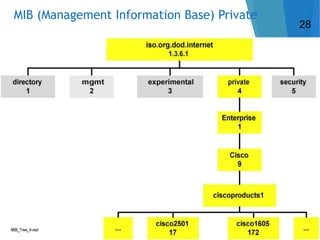
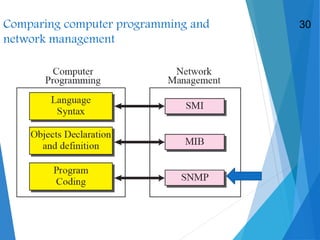
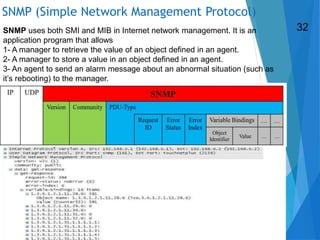
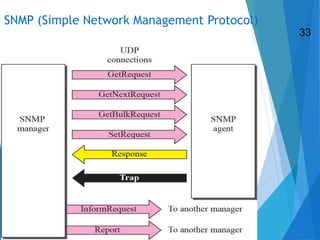
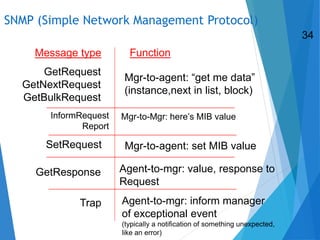
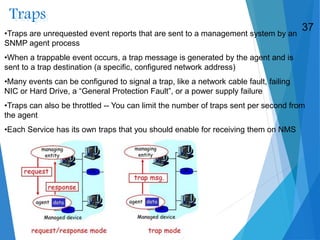
SNMP allows for remote management of network devices. It uses agents running on devices to collect information and send it to Network Management Systems upon request. The Simple Network Management Protocol operates over UDP using ports 161 and 162. Management information is defined through the Structure of Management Information and stored in Management Information Bases which provide standardized names and organization of managed objects.