Security fundamentals
•Download as PPTX, PDF•
0 likes•71 views
This presentation was given to some fresh graduate developers to help them understand how to protect their web apps against some famous attacks like XSS . the presentation was a part of a bigger course that was designed to asset them
Report
Share
Report
Share
Recommended
Dmytro Kochergin - "The OWASP TOP 10 - Typical Attacks on Web Applications an...

Dmytro Kochergin - "The OWASP TOP 10 - Typical Attacks on Web Applications and How to Protect Against Them"
Don't get stung - an introduction to the OWASP Top 10

An updated version of my OWASP Top 10 presentation, new and improved for the updated 2010 OWASP list.
How to secure web applications

I presented this presentation at owasp hyderabad oct 2012 meet. you can find more details at https://www.owasp.org/index.php/Hyderabad
Діана Пінчук "Як відрізнити авторизацію від аутентифікації та перестати бояти...

Діана Пінчук "Як відрізнити авторизацію від аутентифікації та перестати боятись їх тестувати"
Bit flipping attack on aes cbc - ashutosh ahelleya

Bit flipping attack on aes cbc - ashutosh ahelleya
More info : https://cysinfo.com/10th-quarterly-meetup-29th-july-2017/
Recommended
Dmytro Kochergin - "The OWASP TOP 10 - Typical Attacks on Web Applications an...

Dmytro Kochergin - "The OWASP TOP 10 - Typical Attacks on Web Applications and How to Protect Against Them"
Don't get stung - an introduction to the OWASP Top 10

An updated version of my OWASP Top 10 presentation, new and improved for the updated 2010 OWASP list.
How to secure web applications

I presented this presentation at owasp hyderabad oct 2012 meet. you can find more details at https://www.owasp.org/index.php/Hyderabad
Діана Пінчук "Як відрізнити авторизацію від аутентифікації та перестати бояти...

Діана Пінчук "Як відрізнити авторизацію від аутентифікації та перестати боятись їх тестувати"
Bit flipping attack on aes cbc - ashutosh ahelleya

Bit flipping attack on aes cbc - ashutosh ahelleya
More info : https://cysinfo.com/10th-quarterly-meetup-29th-july-2017/
Nguyen Phuong Truong Anh - Some new vulnerabilities in modern web application

Nguyen Phuong Truong Anh - Some new vulnerabilities in modern web application
Sembang2 Keselamatan It 2004

Sembang2 Keselamatan It 2004 Pokleyzz, wyse, obelicks, pengalir by SK from Scan Associates
Browser Security by pratimesh Pathak ( Buldhana) 

Helpful Seminar Topics For Computer Science Student
.NET Security Topics

XSS, SQL Injection, CSRF, ClickJacking, Secure File Handling, Odds & Ends for .NET
Security awareness for information security team

Let's talk about gathering information, staying aware and new generation threats.
AuthN & AuthZ testing: it’s not only about the login form

Presentation in Google Slides http://bit.ly/AuthZ-AuthN-Diana
Testers are often asked at interviews to test a login form. And this is where their acquaintance with authentication testing ends.
We'll talk about authorization and authentication (AuthZ & AuthN) testing: what is the difference between them and how to stop confusing them; what are the specifics of the work of the Oauth 2.0 protocol; what are the best practices of AuthZ & AuthN security testing; what is Identity and Access Management system and where to practice testing of that famous login form.
The talk will be useful for functional testers and those who are interested in the technological aspects of AuthZ & AuthN.
"Introduction to Bug Hunting", Yasser Ali

Have you ever dreamed of getting paid to hack?!
As a Bug Hunter, this is what its all about, you hack and find vulnerabilities in software and websites, then end up with profit and fame.
In this session, I will explain to you how to start your journey in bug hunting, Are you ready?
Security Issues in Android Custom ROM

This paper attempts to look behind the wheels of android and keeping special focus on custom rom’s and basically check for security misconfiguration’s which could yield to device compromise, which may result in malware infection or data theft.
Csrf not all defenses are created equal

A description of Cross-site request forgery (CSRF) attacks and defenses, with a focus on the commonly used libraries and functions which are used for CSRF defense. This presentation goes into each of them, and shows it's strengths, weaknesses, and shortcomings.
Django �(Web Applications that are Secure by Default�)

* Django is a Web Application Framework, written in Python
* Allows rapid, secure and agile web development.
* Write better web applications in less time & effort.
Defeating public exploit protections (EMET v5.2 and more)

Presented by Raghav Pande in SecurityXploded cyber security meet. visit: http://www.securitytrainings.net for more information.
Case Study of Django: Web Frameworks that are Secure by Default

A case study of security features inside the popular python-based web framework, Django. Made by Mohammed ALDOUB (@Voulnet)
Application and Website Security -- Fundamental Edition

This is the first presentation in the 200 level, specifically targeting developers with a more hardcore training program. This program includes numerous case studies and live demonstrations and is considered technical, but does not require a working knowledge of the languages discussed.
Owasp top 10_openwest_2019

My presentation at OpenWest 2019 on the OWASP Top 10 since the 2017 update. Examples of how they're exploited, and how to prevent them.
More Related Content
What's hot
Nguyen Phuong Truong Anh - Some new vulnerabilities in modern web application

Nguyen Phuong Truong Anh - Some new vulnerabilities in modern web application
Sembang2 Keselamatan It 2004

Sembang2 Keselamatan It 2004 Pokleyzz, wyse, obelicks, pengalir by SK from Scan Associates
Browser Security by pratimesh Pathak ( Buldhana) 

Helpful Seminar Topics For Computer Science Student
.NET Security Topics

XSS, SQL Injection, CSRF, ClickJacking, Secure File Handling, Odds & Ends for .NET
Security awareness for information security team

Let's talk about gathering information, staying aware and new generation threats.
AuthN & AuthZ testing: it’s not only about the login form

Presentation in Google Slides http://bit.ly/AuthZ-AuthN-Diana
Testers are often asked at interviews to test a login form. And this is where their acquaintance with authentication testing ends.
We'll talk about authorization and authentication (AuthZ & AuthN) testing: what is the difference between them and how to stop confusing them; what are the specifics of the work of the Oauth 2.0 protocol; what are the best practices of AuthZ & AuthN security testing; what is Identity and Access Management system and where to practice testing of that famous login form.
The talk will be useful for functional testers and those who are interested in the technological aspects of AuthZ & AuthN.
"Introduction to Bug Hunting", Yasser Ali

Have you ever dreamed of getting paid to hack?!
As a Bug Hunter, this is what its all about, you hack and find vulnerabilities in software and websites, then end up with profit and fame.
In this session, I will explain to you how to start your journey in bug hunting, Are you ready?
Security Issues in Android Custom ROM

This paper attempts to look behind the wheels of android and keeping special focus on custom rom’s and basically check for security misconfiguration’s which could yield to device compromise, which may result in malware infection or data theft.
Csrf not all defenses are created equal

A description of Cross-site request forgery (CSRF) attacks and defenses, with a focus on the commonly used libraries and functions which are used for CSRF defense. This presentation goes into each of them, and shows it's strengths, weaknesses, and shortcomings.
Django �(Web Applications that are Secure by Default�)

* Django is a Web Application Framework, written in Python
* Allows rapid, secure and agile web development.
* Write better web applications in less time & effort.
Defeating public exploit protections (EMET v5.2 and more)

Presented by Raghav Pande in SecurityXploded cyber security meet. visit: http://www.securitytrainings.net for more information.
Case Study of Django: Web Frameworks that are Secure by Default

A case study of security features inside the popular python-based web framework, Django. Made by Mohammed ALDOUB (@Voulnet)
What's hot (20)
Nguyen Phuong Truong Anh - Some new vulnerabilities in modern web application

Nguyen Phuong Truong Anh - Some new vulnerabilities in modern web application
Black magic of web attacks Detection and Prevention

Black magic of web attacks Detection and Prevention
[OWASP Poland Day] Application security - daily questions & answers![[OWASP Poland Day] Application security - daily questions & answers](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
![[OWASP Poland Day] Application security - daily questions & answers](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
[OWASP Poland Day] Application security - daily questions & answers
AuthN & AuthZ testing: it’s not only about the login form

AuthN & AuthZ testing: it’s not only about the login form
Django �(Web Applications that are Secure by Default�)

Django �(Web Applications that are Secure by Default�)
Defeating public exploit protections (EMET v5.2 and more)

Defeating public exploit protections (EMET v5.2 and more)
Case Study of Django: Web Frameworks that are Secure by Default

Case Study of Django: Web Frameworks that are Secure by Default
Similar to Security fundamentals
Application and Website Security -- Fundamental Edition

This is the first presentation in the 200 level, specifically targeting developers with a more hardcore training program. This program includes numerous case studies and live demonstrations and is considered technical, but does not require a working knowledge of the languages discussed.
Owasp top 10_openwest_2019

My presentation at OpenWest 2019 on the OWASP Top 10 since the 2017 update. Examples of how they're exploited, and how to prevent them.
Shields up - improving web application security

How can you significantly improve your web-app security by addressing the most common problems and incorporating the educational approach into the development process
Pci compliance writing secure code

Writing secure applications is critical. Whether you're writing code at the SMT level, MivaScript level, server level or anywhere else, it's important to keep security in mind. Come in and learn how to mitigate exploits, initiate exploits, and learn about incidence handling.
S8-Session Managment

Table Of Content
Description Mechanism of Cookies
Introducing Session Management Attacks
Session Fixation
Session Brute-Forcing
Session Hijacking
Session Poisoning
Strategies Of Session Storage
Strategies For Providing Secure Session Management
Understanding and preventing sql injection attacks

SQL Injection attacks are one of the most common hacker tricks used on the web. Learn what a SQL injection attack is and why you should be concerned about them.
This all new session is loaded with demos. You’ll get to witness first-hand several different types of SQL injection attacks, how to find them, and how to block them.
ASP.NET Web Security

ASP.NET Web Security
Key considerations, attacks & how to protect your solutions
Intro to Web Application Security

Introduction to Web Application Security presented at for the Penn State Information Assurance Club (Fall 2007)
Top Ten Java Defense for Web Applications v2

The presentation describes a series of secure coding techniques to help Java developers build secure web applications.
OWASP TOP 10

The OWASP top 10 is a list of the most prolific security issues facing web developers today. In this talk, Robert, will take you through all 10 and demonstrate the problems (we will hack for real… in a safe way) and talk about the solutions. This is an introductory talk, so no prior experience is needed in web dev or security. Not doing web dev? Many of these apply to all development! So join in for a lively session of demos, learning and fun
Video of this talk: https://www.youtube.com/watch?v=p5YCHNnQNyg
Security In PHP Applications

Seminar on various security issues faced by PHP developers and ways to avoid them.
The Examples used in the seminar can be downloaded from -> http://www.sanisoft.com/blog/wp-content/uploads/2009/08/security.tar.gz
rsa-usa-2019-keynote-paula-januszkiewicz

[CQURE] Top 10 ways to make hackers excited: All about the shortcuts not worth taking
Designing a secure architecture can always be more expensive, time-consuming, and complicated. But does it make sense to cut corners when hackers invent new attacks every day? Taking shortcuts will sooner or later translate to more harm and backfire. Learn what mistakes we eliminated when working with our customers.
Similar to Security fundamentals (20)
Application and Website Security -- Fundamental Edition

Application and Website Security -- Fundamental Edition
PCI security requirements secure coding and code review 2014

PCI security requirements secure coding and code review 2014
Understanding and preventing sql injection attacks

Understanding and preventing sql injection attacks
More from ABDEL RAHMAN KARIM
Date Analysis .pdf

Overview of :
- Data Analysis
- Business Intelligence
- Data warehouses
- Dimensional Modeling / Data Cubes.
- Summery Tables.
-
Agile Course

- Agile values and manifesto
- Scrum in details
- Themes, epics, and user stories
- Combining and splitting user stories.
- What could go wrong in Scrum and why?
- Overview in Other Agile methodologies:
- XP Agile Methodology
- KanBan Agile Methodology.
Search engine optimization 

Search engine optimization course :
- Google ranking signals (overview)
- Spam types
- Google algorithms
- Panda
- Penguin
- Google tools
- Google web Master
- Google speed insights
- Google analytics
- Google disavow tool
- Other famous SEO tools
- Google penalty indicators
- Understanding website traffic sources
- Crawling and indexing
- On page SEO checklist
- Metadata famous errors
- How to optimize a blog article
- Yoast plugin
- Sitemaps file
- Robots files
- Off page SEO
- Links types
- Good link building strategy
- Bad link building strategy
OverView to PMP

This is an overview of PMP presentation given at a public Event in the ITI by Abdel Rahman karim and Ahmed Abdel Halim
Software Design principales

This presentation was presented many times in many places such as : ITI (twice) , Softxpert, Ibtikar and Qvision
تلخيص مختصر لكتاب التوحيد و التوكل للامام الغزالى من سلسلة احياء علوم الدين

تلخيص مختصر لكتاب التوحيد و التوكل للامام الغزالى من سلسلة احياء علوم الدين
يشرح فيه الامام فنون التوكل على الله لجلب النفع او استبقاؤه او دفع الضر او قطعه و يوضح احوال المتوكلين على الله
More from ABDEL RAHMAN KARIM (15)
تلخيص مختصر لكتاب التوحيد و التوكل للامام الغزالى من سلسلة احياء علوم الدين

تلخيص مختصر لكتاب التوحيد و التوكل للامام الغزالى من سلسلة احياء علوم الدين
Recently uploaded
Launch Your Streaming Platforms in Minutes

The claim of launching a streaming platform in minutes might be a bit of an exaggeration, but there are services that can significantly streamline the process. Here's a breakdown:
Pros of Speedy Streaming Platform Launch Services:
No coding required: These services often use drag-and-drop interfaces or pre-built templates, eliminating the need for programming knowledge.
Faster setup: Compared to building from scratch, these platforms can get you up and running much quicker.
All-in-one solutions: Many services offer features like content management systems (CMS), video players, and monetization tools, reducing the need for multiple integrations.
Things to Consider:
Limited customization: These platforms may offer less flexibility in design and functionality compared to custom-built solutions.
Scalability: As your audience grows, you might need to upgrade to a more robust platform or encounter limitations with the "quick launch" option.
Features: Carefully evaluate which features are included and if they meet your specific needs (e.g., live streaming, subscription options).
Examples of Services for Launching Streaming Platforms:
Muvi [muvi com]
Uscreen [usencreen tv]
Alternatives to Consider:
Existing Streaming platforms: Platforms like YouTube or Twitch might be suitable for basic streaming needs, though monetization options might be limited.
Custom Development: While more time-consuming, custom development offers the most control and flexibility for your platform.
Overall, launching a streaming platform in minutes might not be entirely realistic, but these services can significantly speed up the process compared to building from scratch. Carefully consider your needs and budget when choosing the best option for you.
Developing Distributed High-performance Computing Capabilities of an Open Sci...

COVID-19 had an unprecedented impact on scientific collaboration. The pandemic and its broad response from the scientific community has forged new relationships among public health practitioners, mathematical modelers, and scientific computing specialists, while revealing critical gaps in exploiting advanced computing systems to support urgent decision making. Informed by our team’s work in applying high-performance computing in support of public health decision makers during the COVID-19 pandemic, we present how Globus technologies are enabling the development of an open science platform for robust epidemic analysis, with the goal of collaborative, secure, distributed, on-demand, and fast time-to-solution analyses to support public health.
Lecture 1 Introduction to games development

Software engineering
Game Development
unity Game Development
OpenFOAM solver for Helmholtz equation, helmholtzFoam / helmholtzBubbleFoam

In this slide, we show the simulation example and the way to compile this solver.
In this solver, the Helmholtz equation can be solved by helmholtzFoam. Also, the Helmholtz equation with uniformly dispersed bubbles can be simulated by helmholtzBubbleFoam.
2024 RoOUG Security model for the cloud.pptx

How we've evolved the MySQL server security model from a single DBA to the cloud.
A Sighting of filterA in Typelevel Rite of Passage

Slide deck home: https://fpilluminated.com/deck/220
In 2015, I used to write extensions for Joomla, WordPress, phpBB3, etc and I ...

In 2015, I used to write extensions for Joomla, WordPress, phpBB3, etc and I didn't get rich from it but it did have 63K downloads (powered possible tens of thousands of websites).
Quarkus Hidden and Forbidden Extensions

Quarkus has a vast extension ecosystem and is known for its subsonic and subatomic feature set. Some of these features are not as well known, and some extensions are less talked about, but that does not make them less interesting - quite the opposite.
Come join this talk to see some tips and tricks for using Quarkus and some of the lesser known features, extensions and development techniques.
Enhancing Research Orchestration Capabilities at ORNL.pdf

Cross-facility research orchestration comes with ever-changing constraints regarding the availability and suitability of various compute and data resources. In short, a flexible data and processing fabric is needed to enable the dynamic redirection of data and compute tasks throughout the lifecycle of an experiment. In this talk, we illustrate how we easily leveraged Globus services to instrument the ACE research testbed at the Oak Ridge Leadership Computing Facility with flexible data and task orchestration capabilities.
BoxLang: Review our Visionary Licenses of 2024

Unleash Unlimited Potential with One-Time Purchase
BoxLang is more than just a language; it's a community. By choosing a Visionary License, you're not just investing in your success, you're actively contributing to the ongoing development and support of BoxLang.
GraphSummit Paris - The art of the possible with Graph Technology

Sudhir Hasbe, Chief Product Officer, Neo4j
Join us as we explore breakthrough innovations enabled by interconnected data and AI. Discover firsthand how organizations use relationships in data to uncover contextual insights and solve our most pressing challenges – from optimizing supply chains, detecting fraud, and improving customer experiences to accelerating drug discoveries.
First Steps with Globus Compute Multi-User Endpoints

In this presentation we will share our experiences around getting started with the Globus Compute multi-user endpoint. Working with the Pharmacology group at the University of Auckland, we have previously written an application using Globus Compute that can offload computationally expensive steps in the researcher's workflows, which they wish to manage from their familiar Windows environments, onto the NeSI (New Zealand eScience Infrastructure) cluster. Some of the challenges we have encountered were that each researcher had to set up and manage their own single-user globus compute endpoint and that the workloads had varying resource requirements (CPUs, memory and wall time) between different runs. We hope that the multi-user endpoint will help to address these challenges and share an update on our progress here.
May Marketo Masterclass, London MUG May 22 2024.pdf

Can't make Adobe Summit in Vegas? No sweat because the EMEA Marketo Engage Champions are coming to London to share their Summit sessions, insights and more!
This is a MUG with a twist you don't want to miss.
Enterprise Software Development with No Code Solutions.pptx

In the ever-evolving landscape of technology, enterprise software development is undergoing a significant transformation. Traditional coding methods are being challenged by innovative no-code solutions, which promise to streamline and democratize the software development process.
This shift is particularly impactful for enterprises, which require robust, scalable, and efficient software to manage their operations. In this article, we will explore the various facets of enterprise software development with no-code solutions, examining their benefits, challenges, and the future potential they hold.
Cyaniclab : Software Development Agency Portfolio.pdf

CyanicLab, an offshore custom software development company based in Sweden,India, Finland, is your go-to partner for startup development and innovative web design solutions. Our expert team specializes in crafting cutting-edge software tailored to meet the unique needs of startups and established enterprises alike. From conceptualization to execution, we offer comprehensive services including web and mobile app development, UI/UX design, and ongoing software maintenance. Ready to elevate your business? Contact CyanicLab today and let us propel your vision to success with our top-notch IT solutions.
AI Pilot Review: The World’s First Virtual Assistant Marketing Suite

AI Pilot Review: The World’s First Virtual Assistant Marketing Suite
👉👉 Click Here To Get More Info 👇👇
https://sumonreview.com/ai-pilot-review/
AI Pilot Review: Key Features
✅Deploy AI expert bots in Any Niche With Just A Click
✅With one keyword, generate complete funnels, websites, landing pages, and more.
✅More than 85 AI features are included in the AI pilot.
✅No setup or configuration; use your voice (like Siri) to do whatever you want.
✅You Can Use AI Pilot To Create your version of AI Pilot And Charge People For It…
✅ZERO Manual Work With AI Pilot. Never write, Design, Or Code Again.
✅ZERO Limits On Features Or Usages
✅Use Our AI-powered Traffic To Get Hundreds Of Customers
✅No Complicated Setup: Get Up And Running In 2 Minutes
✅99.99% Up-Time Guaranteed
✅30 Days Money-Back Guarantee
✅ZERO Upfront Cost
See My Other Reviews Article:
(1) TubeTrivia AI Review: https://sumonreview.com/tubetrivia-ai-review
(2) SocioWave Review: https://sumonreview.com/sociowave-review
(3) AI Partner & Profit Review: https://sumonreview.com/ai-partner-profit-review
(4) AI Ebook Suite Review: https://sumonreview.com/ai-ebook-suite-review
APIs for Browser Automation (MoT Meetup 2024)

APIs for Browser Automation:
Selenium, Cypress, Puppeteer, and Playwright. Ministry of Testing Athens. Meetup on the Beach. 30 May 2024.
Exploring Innovations in Data Repository Solutions - Insights from the U.S. G...

The U.S. Geological Survey (USGS) has made substantial investments in meeting evolving scientific, technical, and policy driven demands on storing, managing, and delivering data. As these demands continue to grow in complexity and scale, the USGS must continue to explore innovative solutions to improve its management, curation, sharing, delivering, and preservation approaches for large-scale research data. Supporting these needs, the USGS has partnered with the University of Chicago-Globus to research and develop advanced repository components and workflows leveraging its current investment in Globus. The primary outcome of this partnership includes the development of a prototype enterprise repository, driven by USGS Data Release requirements, through exploration and implementation of the entire suite of the Globus platform offerings, including Globus Flow, Globus Auth, Globus Transfer, and Globus Search. This presentation will provide insights into this research partnership, introduce the unique requirements and challenges being addressed and provide relevant project progress.
Innovating Inference - Remote Triggering of Large Language Models on HPC Clus...

Large Language Models (LLMs) are currently the center of attention in the tech world, particularly for their potential to advance research. In this presentation, we'll explore a straightforward and effective method for quickly initiating inference runs on supercomputers using the vLLM tool with Globus Compute, specifically on the Polaris system at ALCF. We'll begin by briefly discussing the popularity and applications of LLMs in various fields. Following this, we will introduce the vLLM tool, and explain how it integrates with Globus Compute to efficiently manage LLM operations on Polaris. Attendees will learn the practical aspects of setting up and remotely triggering LLMs from local machines, focusing on ease of use and efficiency. This talk is ideal for researchers and practitioners looking to leverage the power of LLMs in their work, offering a clear guide to harnessing supercomputing resources for quick and effective LLM inference.
Recently uploaded (20)
Developing Distributed High-performance Computing Capabilities of an Open Sci...

Developing Distributed High-performance Computing Capabilities of an Open Sci...
OpenFOAM solver for Helmholtz equation, helmholtzFoam / helmholtzBubbleFoam

OpenFOAM solver for Helmholtz equation, helmholtzFoam / helmholtzBubbleFoam
A Sighting of filterA in Typelevel Rite of Passage

A Sighting of filterA in Typelevel Rite of Passage
In 2015, I used to write extensions for Joomla, WordPress, phpBB3, etc and I ...

In 2015, I used to write extensions for Joomla, WordPress, phpBB3, etc and I ...
Enhancing Research Orchestration Capabilities at ORNL.pdf

Enhancing Research Orchestration Capabilities at ORNL.pdf
GraphSummit Paris - The art of the possible with Graph Technology

GraphSummit Paris - The art of the possible with Graph Technology
First Steps with Globus Compute Multi-User Endpoints

First Steps with Globus Compute Multi-User Endpoints
May Marketo Masterclass, London MUG May 22 2024.pdf

May Marketo Masterclass, London MUG May 22 2024.pdf
Enterprise Software Development with No Code Solutions.pptx

Enterprise Software Development with No Code Solutions.pptx
Cyaniclab : Software Development Agency Portfolio.pdf

Cyaniclab : Software Development Agency Portfolio.pdf
AI Pilot Review: The World’s First Virtual Assistant Marketing Suite

AI Pilot Review: The World’s First Virtual Assistant Marketing Suite
Exploring Innovations in Data Repository Solutions - Insights from the U.S. G...

Exploring Innovations in Data Repository Solutions - Insights from the U.S. G...
Innovating Inference - Remote Triggering of Large Language Models on HPC Clus...

Innovating Inference - Remote Triggering of Large Language Models on HPC Clus...
Security fundamentals
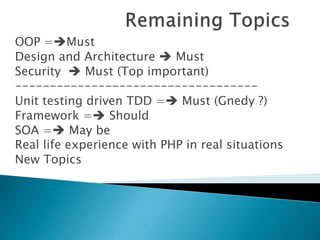
- 1. OOP =Must Design and Architecture Must Security Must (Top important) ----------------------------------- Unit testing driven TDD = Must (Gnedy ?) Framework = Should SOA = May be Real life experience with PHP in real situations New Topics
- 2. The 5 Most Common attacks and how to prevent them ?
- 4. SELECT * FROM users WHERE username='john' AND password='123456' SELECT * FROM users WHERE username='john' OR 1=1; -- ' AND The snippet would possibly allow the user to bypass the login screen without having proper credentials.
- 5. Never trust User input Sanatize by mysqli_real_escape_string Casting Parameter query Limited permission , never use sa Test using http://sqlmap.org/ tool Encrypt sensitive data Don’t store sensitive data if you don’t need it
- 7. Mandate strong passwords Secure reset password mechanism Use Recaptcha or captcha Use security Question Notify by email at any profile changes! Avoid “admin” user name Single token request , also protecte against CSRF attacks . Encrypt password with strong algorism + salt
- 9. Use Session_Regenerate_id to regenerate session ID with each request Delete cookie from client once log out Limit session idle time Enable https or make it easy to be enabled, how ? Protected your cookies not to be accessed by Java Script at all !
- 11. Validate , sanitize each input Escape Each Output Regester Globals OFF Check the security class of codegniter File system permission.
- 13. Prevent error reporting at run time Prevent descriptive responses URL re-writing for SEO and for protection Make sure you got the latest version of any 3rd prty tool you are using .
- 14. You use request token to prevent which attack ? A) CSRF B) Password Brutal attack C) Sql injection D) XSS E) A and B F) C and D G) All the above
- 15. You should configure your cookies to be accessed only via A) Java script B) Cookie C) Http D) all the above .
- 16. A)The cookie can not be accessed by JavaScript B)The cookie will not be sent cross-domain C)Client will send the cookie only over an HTTPS connection
- 17. A client logs in A short idle period (ie. 30 seconds) Any privilege level change Each request
