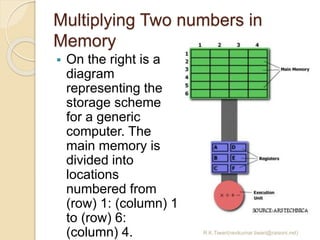
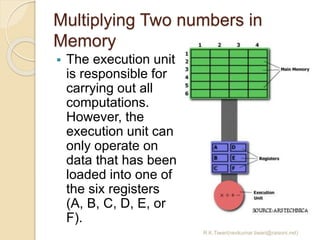
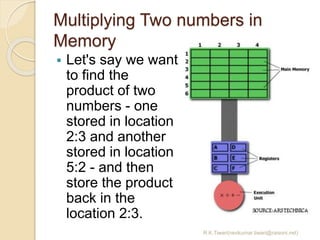
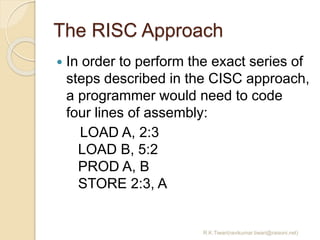
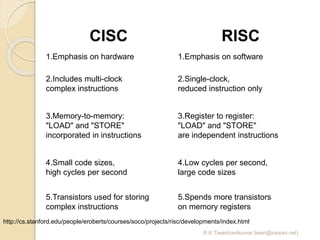
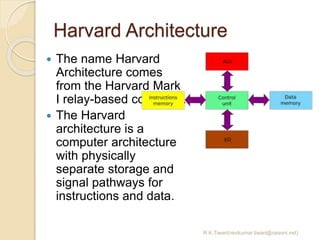
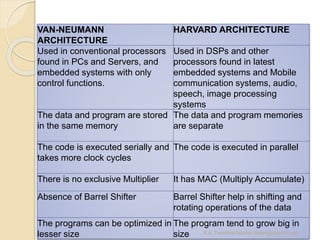
This document discusses RISC vs CISC architectures and the Harvard and von Neumann computer architectures. It provides examples of multiplying two numbers in memory using CISC and RISC approaches. CISC uses complex instructions that perform multiple operations, while RISC breaks operations into simpler instructions. Harvard architecture separates program and data memory while von Neumann uses shared memory.