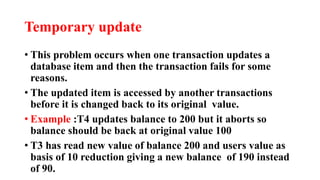
This document discusses recovery management and concurrency controls in databases. It defines recovery management as the process of restoring a database to its most recent consistent state after a failure. There are three states in recovery: pre-condition (consistent), condition (failure occurs), and post-condition (restore to pre-failure state). The types of failures are transaction, system, and media failures. Concurrency control manages simultaneous transactions to maintain consistency and prevent issues like lost updates, temporary updates, and incorrect summaries that can occur from concurrent execution.