This document discusses gender identity and its development. It defines sex as biological and refers to physical differences, while gender is psychological and relates to one's sense of masculinity or femininity. It explores several theories on how gender roles and identities form, including:
- Biological factors like evolutionary mating strategies
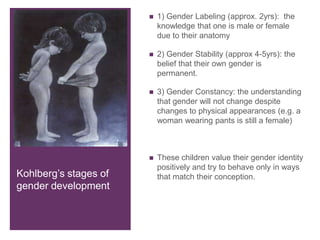
- Kohlberg's cognitive theory of gender constancy in childhood
- Social cognitive theory of learning gender roles through observation and reinforcement
- Gender schema theory of organizing information according to masculine/feminine concepts
- Psychoanalytic theories like Freud's identification theory of gender development through the Oedipus complex.