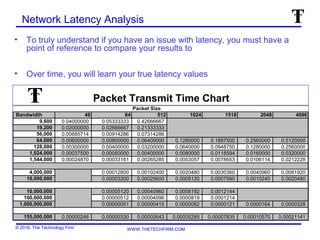
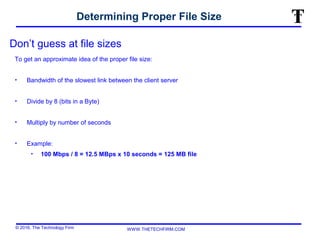
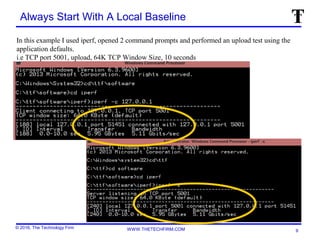
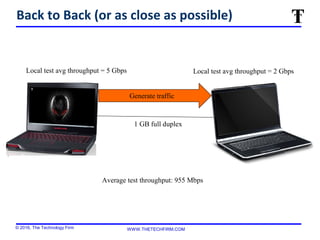
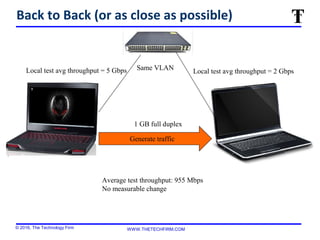
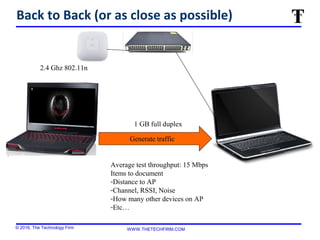
The document outlines procedures for measuring network performance, emphasizing the importance of documenting various parameters, establishing a local baseline, and selecting appropriate tools and methodologies. It discusses the need to analyze network latency, automate traffic generation, and properly size test files based on network bandwidth. Various tools and methods for testing throughput, such as iperf and wget, are illustrated with examples to guide accurate performance measurements.

![© 2016, The Technology Firm WWW.THETECHFIRM.COM
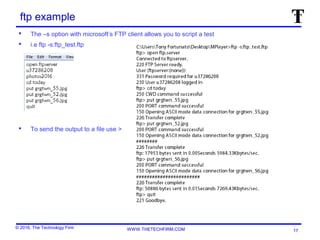
wget To Measure Throughput With HTTP
D:softwarewget>wget http://churchill/300mb
--2013-09-27 21:24:05-- http://churchill/300mb
Resolving churchill... 10.44.10.94
Connecting to churchill|10.44.10.94|:80... connected.
HTTP request sent, awaiting response... 200 OK
Length: 333202944 (318M) [application/octet-stream]
Saving to: `300mb'
100%[======================================>] 333,202,944 1.47M/s in 3m 20s
2013-09-27 21:27:25 (1.59 MB/s) - `300mb' saved [333202944/333202944]
D:softwarewget>wget http://churchill/8mb
--2013-09-27 21:35:07-- http://churchill/8mb
Resolving churchill... 10.44.10.94
Connecting to churchill|10.44.10.94|:80... connected
HTTP request sent, awaiting response... 200 OK
Length: 9062704 (8.6M) [application/octet-stream]
Saving to: `8mb.1'
100%[======================================>] 9,062,704 1.38M/s in 6.9s
2013-09-27 21:35:14 (1.25 MB/s) - `8mb.1' saved [9062704/9062704]](https://image.slidesharecdn.com/performancetest-160622193839/85/Performance-test-18-320.jpg)