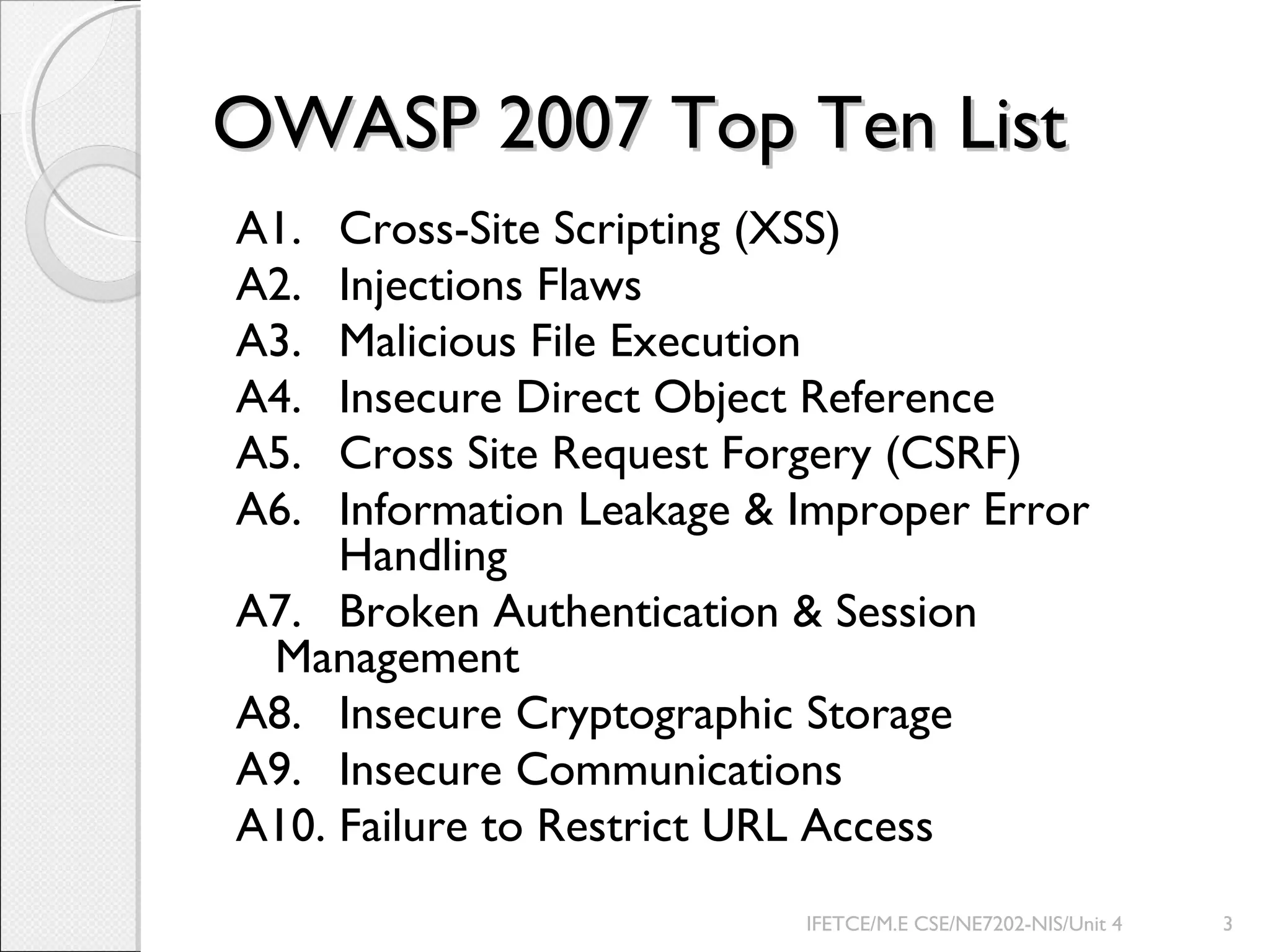
The document discusses the Open Web Application Security Project (OWASP) and its Top 10 vulnerabilities. OWASP is an open source non-profit organization dedicated to web application security. The document outlines the OWASP Top 10 vulnerabilities from 2007, including Cross-Site Scripting (XSS), Injection Flaws, Malicious File Execution, and others. It then provides detailed explanations and examples of each vulnerability, as well as recommendations for prevention and mitigation.
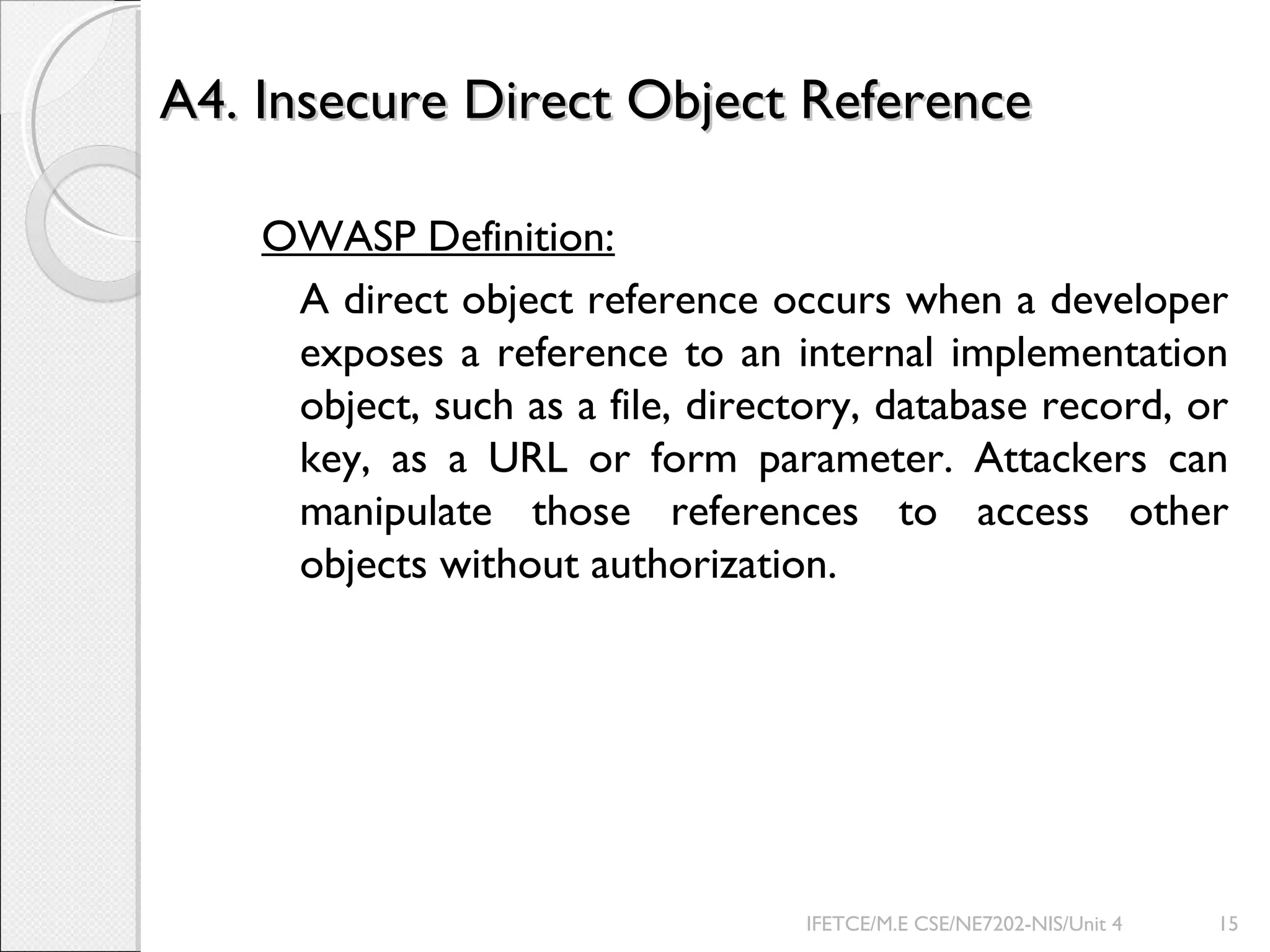
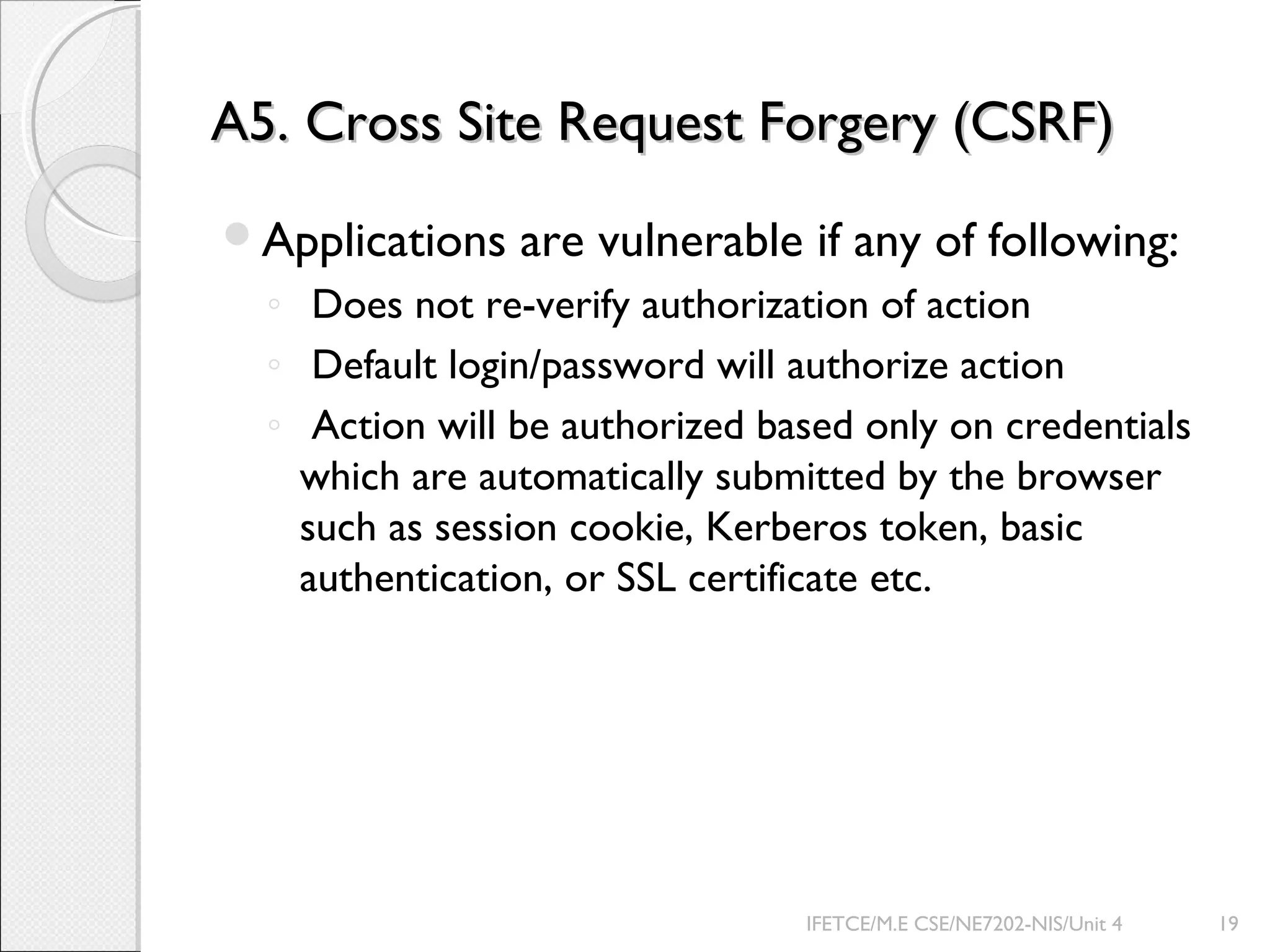
![Improper Error Handling ExamplesImproper Error Handling Examples
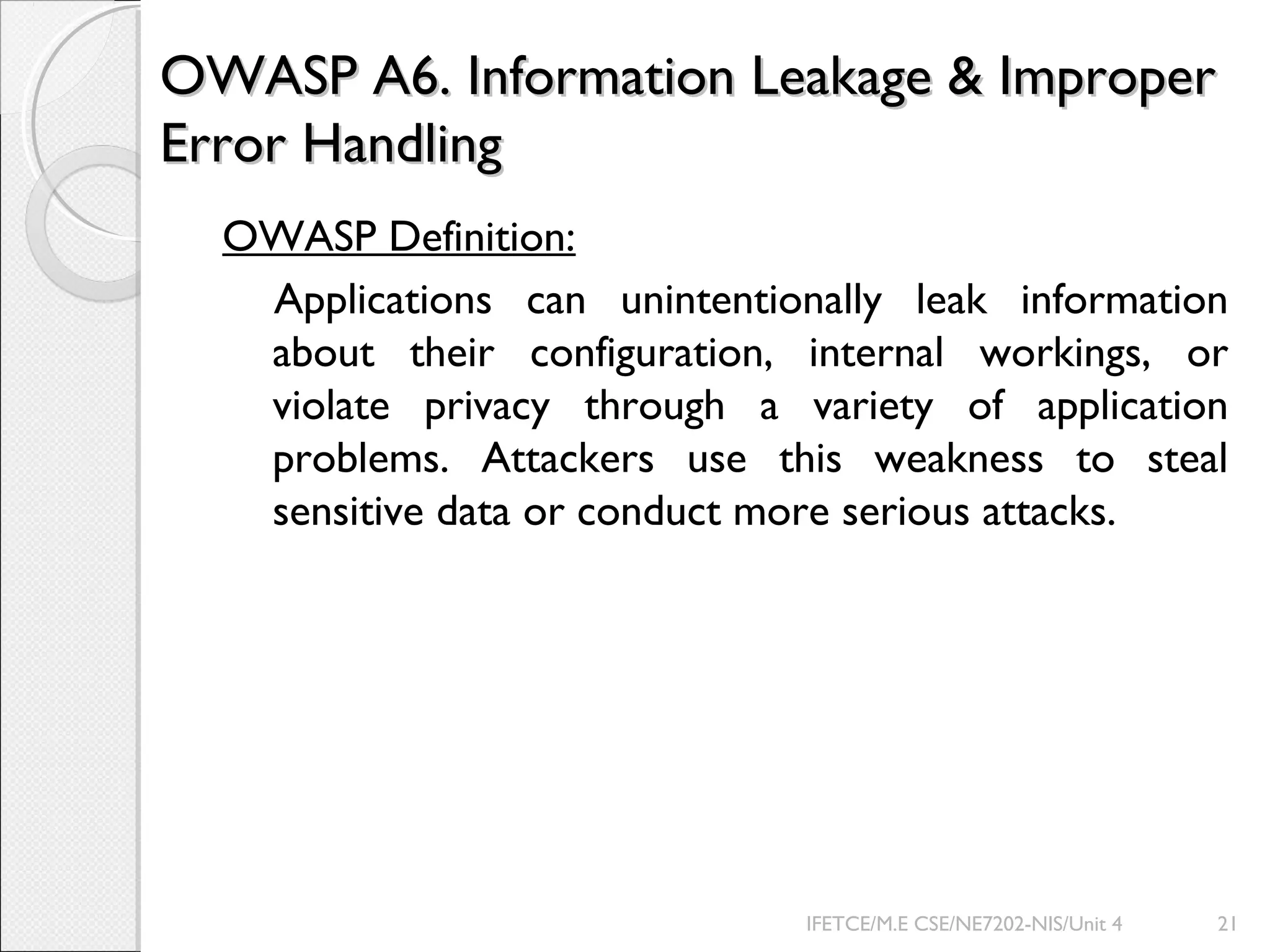
Example 1
Microsoft OLE DB Provider for ODBC Drivers error '80004005'
[Microsoft][ODBC Microsoft Access 97 Driver] Can't open database ‘VDPROD'.
Example 2
java.sql.SQLException: ORA-00600: internal error code, arguments: [ttcgnd-1],
[0], [], [], [],
at oracle.jdbc.dbaccess.DBError.throwSqlException (DBError.java:169)
at oracle.jdbc.ttc7.TTIoer.processError (TTIoer.java:208)
Messages Helpful for Debug
Provides way too much information!
Very helpful to potential attacker
IFETCE/M.E CSE/NE7202-NIS/Unit 4 22](https://image.slidesharecdn.com/owasptop10-140619082943-phpapp02/75/Owasp-top-10-22-2048.jpg)