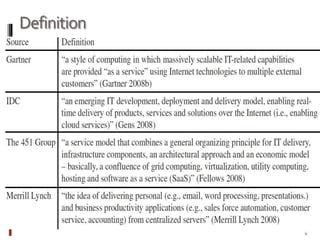
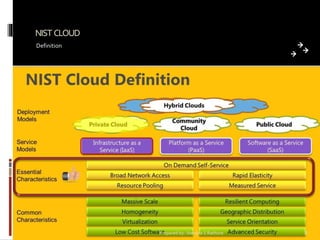
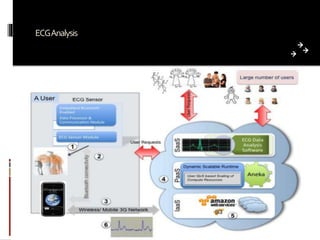
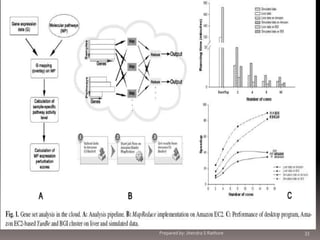
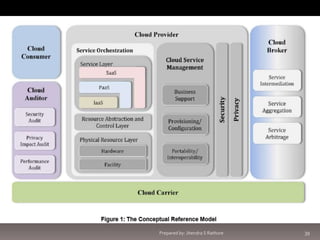
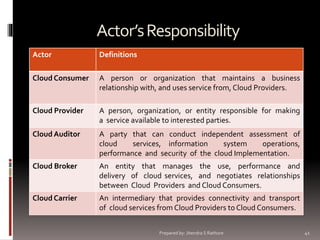
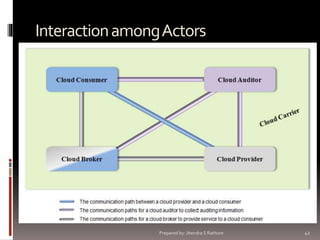
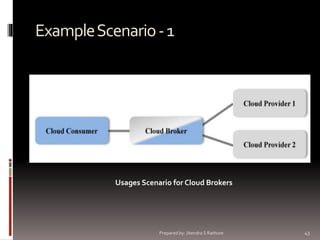
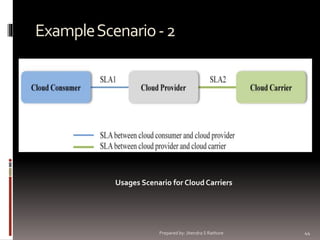
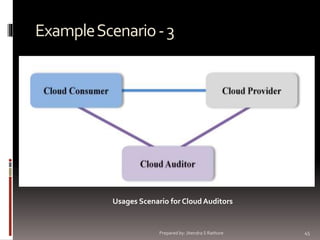
This document provides an overview of cloud computing, including definitions, models, and applications. It begins with definitions of cloud computing from various experts and the National Institute of Standards and Technology (NIST). It describes the essential characteristics, service models (SaaS, PaaS, IaaS), and deployment models of cloud computing. The document discusses the differences between clusters, grids, and clouds. It provides examples of cloud applications like ECG analysis, protein structure prediction, and social networking. Finally, it outlines the actors in cloud computing reference architecture like cloud providers, consumers, brokers and carriers along with example usage scenarios.

![Cloud Auditor
•A cloud auditor is a party that can
•
perform
an
independent
examination of cloud service
controls with the intent to express
an opinion thereon.
•Audits are performed to verify
conformance to standards through
review of objective evidence.
•A cloud auditor can evaluate the
services provided by a cloud
provider in terms of security
controls,
privacy
impact,
performance, etc.
•
Auditing is especially important
for federal agencies as “agencies
should include a contractual
clause enabling third parties to
assess security controls of cloud
providers” [4] (by Vivek Kundra,
Federal Cloud Computing Strategy,
Feb. 2011.).
Security controls [3] are the
management, operational, and
technical
safeguards
or
countermeasures employed within
an
organizational
information
system
to
protect
the
confidentiality,
integrity,
and
availability of the system and its
information.
Prepared by: Jitendra S Rathore
53](https://image.slidesharecdn.com/cloudcomputingit703-130915004442-phpapp01-140302074045-phpapp01/85/Cloud-computing-53-320.jpg)



![Interoperability
According to Author of [3],
interoperability means:
“In cloud computing, interoperability
typically refers to the ability to easily
move workloads and data from one
cloud provider to another or
between private and public clouds. A
common tactic for enabling
interoperability is the use of open
standards,
and
many
cloud
standardization
projects
are
developing standards for the cloud.”
A common tactic for enabling
interoperability is the use of
open standards [ITU 2005].
According to Microsoft [4] –
1. Data portability
2. Standards
3. Ease
of migrations and
deployment
4. Developer choice
are the basic elementary points for
ensuring interoperability in the
cloud
Figure
64](https://image.slidesharecdn.com/cloudcomputingit703-130915004442-phpapp01-140302074045-phpapp01/85/Cloud-computing-64-320.jpg)
![Cloud Ecosystem
According to [5],
Cloud ecosystem is a term used to
describe the complex system of
interdependent components that
work together to enable cloud
services.
Merriam-Webster
defines
an
ecosystem as the complex of a
community of organisms and its
environment functioning as an
ecological unit.
In terms of cloud computing, that
complex includes not only traditional
elements of cloud computing such as
software and infrastructure but also
consultants, integrators, partners,
third parties and anything in their
environments that has a bearing on
the other components.
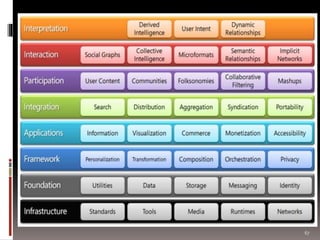
According to Microsoft [6], cloud
ecosystem includes all the things as
shown in the figure
66](https://image.slidesharecdn.com/cloudcomputingit703-130915004442-phpapp01-140302074045-phpapp01/85/Cloud-computing-66-320.jpg)
![Cloud Business Process Management
•According to [wiki],
“Cloud computing business process
management is the use of (BPM)
tools that are delivered as software
services (SaaS) over a network.
Cloud BPM business logic is
deployed on an application server
and the business data resides in
cloud storage.”
•
According to [7],
“Business Process Management
Software in the cloud enables
strategic process improvement,
reduced technology cost, and better
alignment of IT with business goals.
The new IT paradigm and business
model can drive new growth
opportunities,
increase
profit
margins for the private sector, and
achieve more efficient and effective
missions for federal agencies. ”
68](https://image.slidesharecdn.com/cloudcomputingit703-130915004442-phpapp01-140302074045-phpapp01/85/Cloud-computing-68-320.jpg)
![BPM by Oracle [8]
Prepared by: Jitendra S Rathore
69](https://image.slidesharecdn.com/cloudcomputingit703-130915004442-phpapp01-140302074045-phpapp01/85/Cloud-computing-69-320.jpg)



![Cloud Analytics Needs
•According to [9],
“Few decades back , the problem was
the shortage of information or data. In
modern era, this problem is overcome
by the advent of the Internet and
reduced storage cost. ”
•But the new challenge is to how to
analyze data?
•Data is getting generated as much
faster pace than the speed at which it
can be processed with the current
infrastructures.
•Huge and dedicated server were
designed and developed for the same,
but problem is the cost of such
infrastructure which is not affordable
for such companies.
•
•
•
•
•
Such seeking companies seeking
towards cloud computing for this
purpose.
Also termed as utility computing [9].
In general, business Intelligence
application such as
image
processing,
web
searches,
understanding buying and selling
needs, supply chain and ranking
and bio informatics (gene structure
prediction) are data intensive
applications.
Cloud can be the perfect match for
such analytics services.
For example , Google MapReduce
do the same by splitting data into
small chunk and distributed into
computing sources for analyzing.
73](https://image.slidesharecdn.com/cloudcomputingit703-130915004442-phpapp01-140302074045-phpapp01/85/Cloud-computing-73-320.jpg)
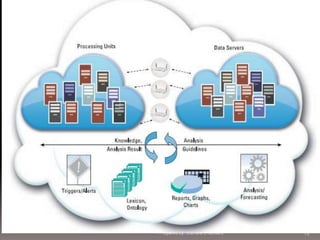
![Cloud Analytics
•Cerri et al,gives the new name to
Single Data Mining Task – Like
this service “Knowledge in the cloud
” rather than “data in the cloud” to
support collaborative task which are
computationally
intensive
and
facilitate
distributed,
heterogeneous knowledge .
Distributed
•According to Talia, knowledge
Data Mining Applications or
service in the cloud can be classified
into 4Single Steps – Compose of KDD
process such as Preprocessing,
filtering and visualization.
classification, Clustering
Association rule discovery.
and
Data
Mining
Pattern- Such as Collective
learning, Meta Learning Models
and Parallel Classification.
KDD Processes – Including all f
services previously discussed.
As shown in figure referred from
[9]-
74](https://image.slidesharecdn.com/cloudcomputingit703-130915004442-phpapp01-140302074045-phpapp01/85/Cloud-computing-74-320.jpg)

![What is Desktop Virtualization?
According to [wiki] –
“Desktop
virtualization
is
software
technology that separates the desktop
environment and associated application
software from the physical client device that
is used to access it.”
Desktop virtualization can be used in
conjunction with application virtualization
and (Windows) user profile management
systems, now termed "user virtualization," to
provide
a
comprehensive
desktop
environment management system.
In this mode, all the components of the
desktop are virtualized, which allows for a
highly flexible and much more secure desktop
delivery model.
In addition, this approach supports a more
complete desktop disaster recovery strategy
as all components are essentially saved in the
data center and backed up through traditional
redundant maintenance systems.
If a user's device or hardware is lost, the
restore is much more straightforward
and simple, because basically all the
components will be present at login from
another device.
In addition, because no data is saved to
the user's device, if that device is lost,
there is much less chance that any
critical data can be retrieved and
compromised.
Prepared by: Jitendra S Rathore
77](https://image.slidesharecdn.com/cloudcomputingit703-130915004442-phpapp01-140302074045-phpapp01/85/Cloud-computing-77-320.jpg)
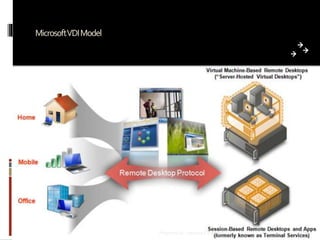
![Virtual Desktop Infrastructure (VDI)
Virtual Desktop Infrastructure (VDI) is a
desktop-centric service that hosts user desktop
environments on remote servers and/or blade
PCs, which are accessed over a network using a
remote display protocol. A connection brokering
service is used to connect users to their assigned
desktop sessions.
For users, this means they can access their
desktop from any location, without being tied to
a single client device.
In other words [10]“Virtual desktop infrastructure (VDI) is the
practice of hosting a desktop operating
system within a virtual machine (VM)
running on a centralized server. VDI is a
variation on the client/server computing
model, sometimes referred to as serverbased computing. The term was coined by
VMware Inc.”
Since the resources are centralized, users
moving between work locations can still access
the same desktop environment with their
applications and data.
For IT administrators, this means a more
centralized, efficient client environment that is
easier to maintain and able to respond more
quickly to the changing needs of the user and
business
78](https://image.slidesharecdn.com/cloudcomputingit703-130915004442-phpapp01-140302074045-phpapp01/85/Cloud-computing-78-320.jpg)
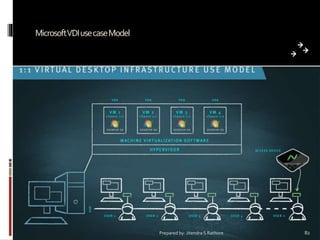
![VDI
According to Microsoft [11] –
1.
Microsoft VDI: allows users to
seamlessly access their rich and full
fidelity
Windows
environment
running in the datacenter, from any
device. Microsoft VDI is powered by
upcoming Windows Server 2012.
2. Experience: RemoteFX provides a
consistently rich user experience,
irrespective of what type of virtual
desktop is being accessed, or where the
users are accessing their desktops from.
With Remote Desktop Services
(RDS) and Hyper-V in Windows
Server 2012, organizations get the
following benefits-
3.
Platform: Windows Server 2012 provides
a single platform to deliver any type of
hosted desktop, making it simple to
deploy and easy to manage.
deployment choices: RDS can host either
Session based desktops, pooled VMs or
personal VMs. So customers have the
flexibility to deploy the right type of VDI
desktop for their users, all from a single
platform.
79](https://image.slidesharecdn.com/cloudcomputingit703-130915004442-phpapp01-140302074045-phpapp01/85/Cloud-computing-79-320.jpg)


![What is Testing in the Cloud?
According to Wikipedia, "cloud testing
is a form of software testing in which
Web applications that leverage Cloud
computing environments ("cloud") seek
to simulate real-world user traffic as a
means of load testing and stress testing
web sites [12].
The ability and costs to simulate Web
traffic for software testing purposes has
been an inhibitor
to overall Web
reliability.“
According of survey of [12], cloud
testing is a –
““Cloud testing basically aligns with the
concept of cloud and SaaS. It
provides the ability to test by
leveraging the cloud, thereby
bringing the same benefits that the
cloud brings to Customers.”
(by Vinita Ananth, Director - APJ
Region, HP Softwareas-aService). ”
85](https://image.slidesharecdn.com/cloudcomputingit703-130915004442-phpapp01-140302074045-phpapp01/85/Cloud-computing-85-320.jpg)
![Objectives of the Cloud Testing
It has four major objectives [12]1. To assure the quality of cloud-based
applications deployed in a cloud,
including their functional services,
business processes, and system
performance as well as scalability
based on a set of application-based
system requirements in a cloud.
2. To validate software as a service
(SaaS) in a cloud environment,
including software performance,
scalability,
security
and
3. To check the provided automatic
cloud-based functional services, for
example auto-provisioned functions.
4. To test cloud compatibility and interoperation capability between SaaS
and applications in a cloud
infrastructure, for example, checking
the APIs of SaaS and their cloud
connectivity to others.
measurement based on
certain
economic scales and pre-defined
SLAs.
86](https://image.slidesharecdn.com/cloudcomputingit703-130915004442-phpapp01-140302074045-phpapp01/85/Cloud-computing-86-320.jpg)
![Scope ofCloud Based SoftwareTesting
From [12]
Prepared by: Jitendra S Rathore
88](https://image.slidesharecdn.com/cloudcomputingit703-130915004442-phpapp01-140302074045-phpapp01/85/Cloud-computing-88-320.jpg)
