Embed presentation
Downloaded 26 times

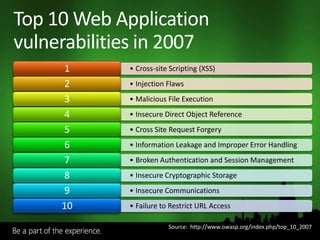
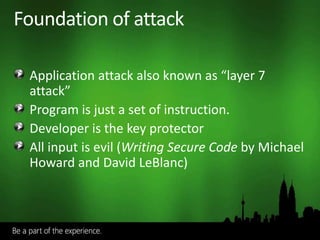
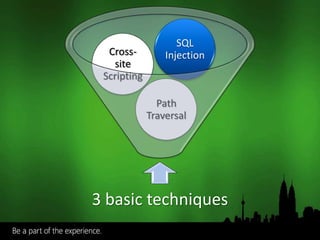
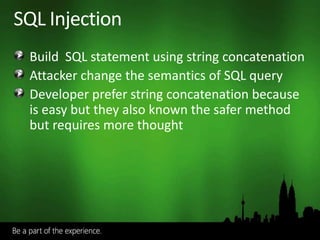


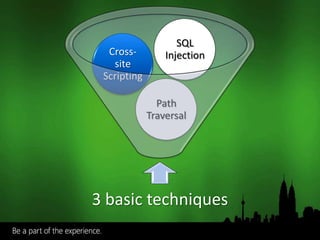
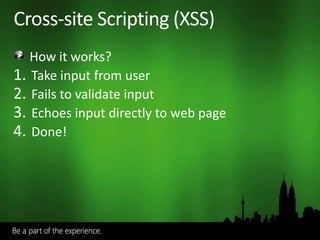
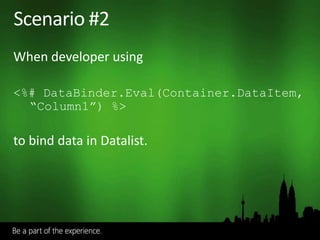

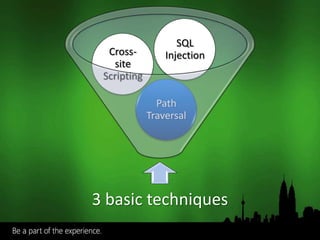
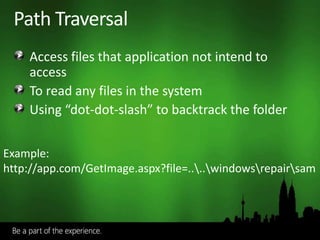
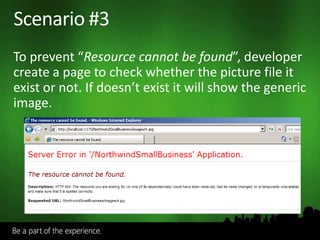


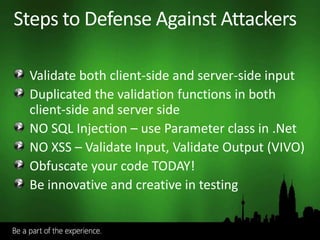



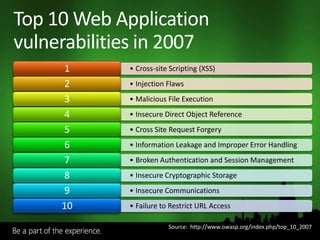
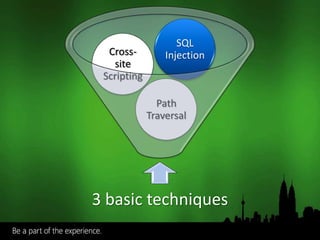
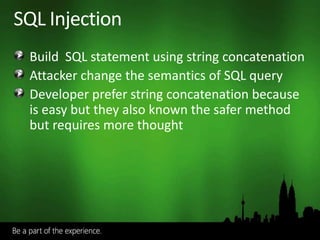
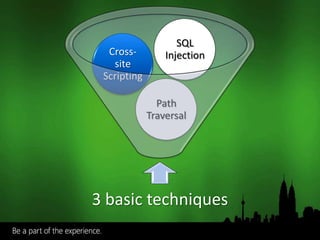
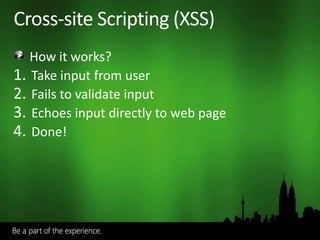
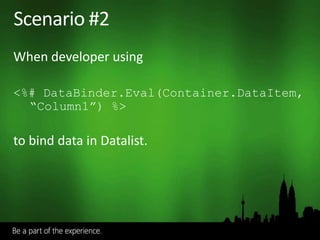
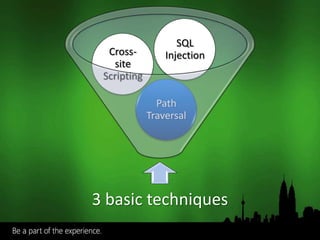
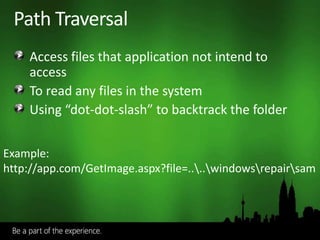
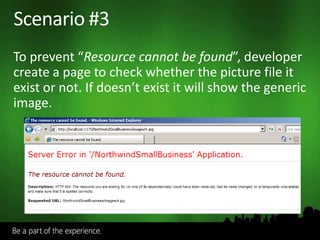
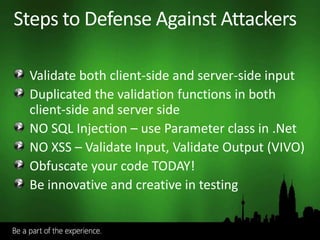
The document outlines the top 10 web application vulnerabilities for 2007, including cross-site scripting, injection flaws, and insecure communications. It discusses fundamental attack techniques, such as SQL injection and path traversal, and emphasizes the importance of validating user input and coding defensively. Additionally, it highlights the significance of obfuscation to protect source code and suggests automated testing methods to improve security.