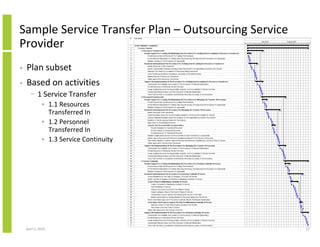
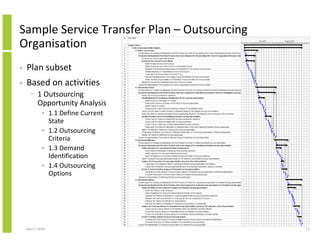
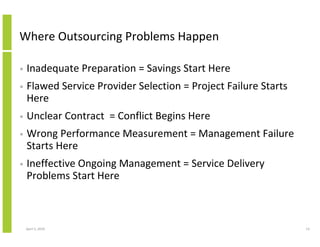
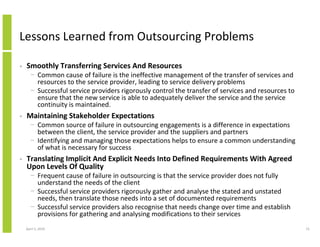
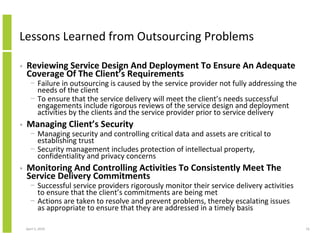
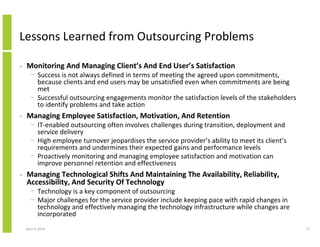
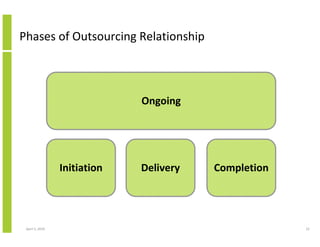
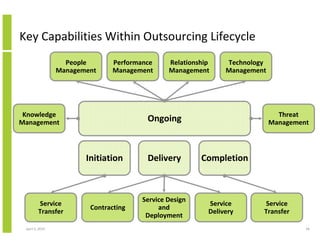
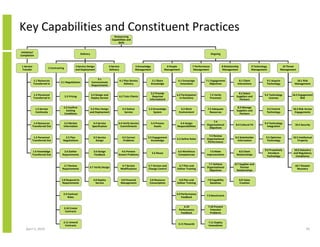
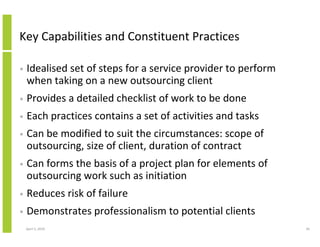
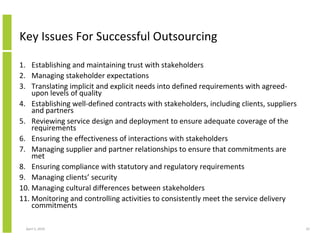
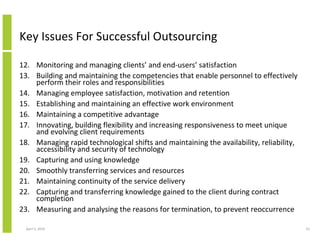
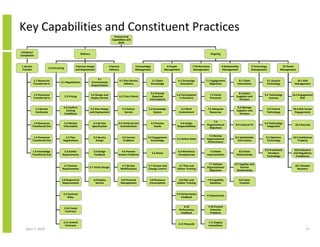
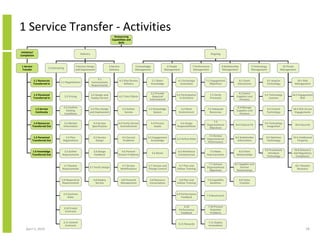
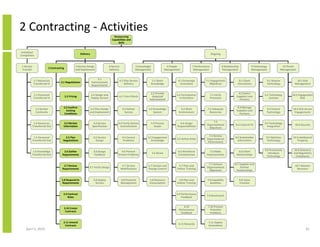
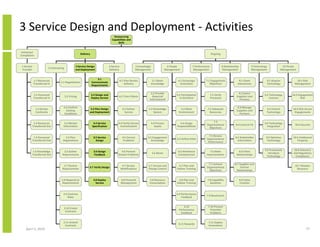
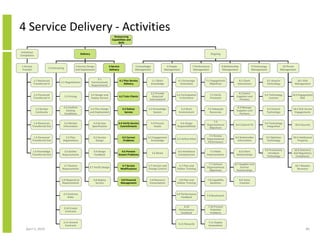
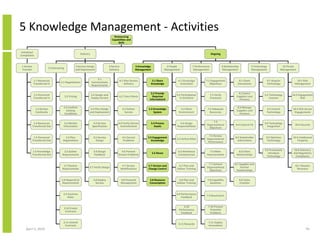
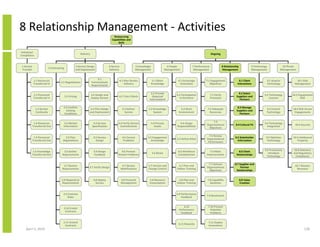
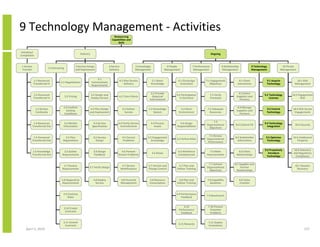
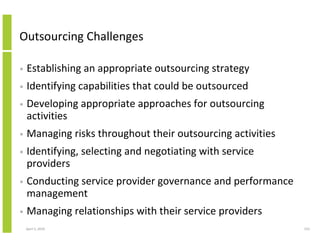
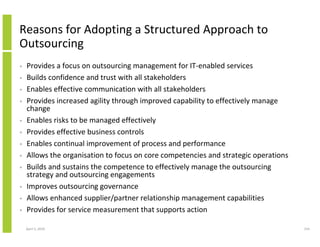
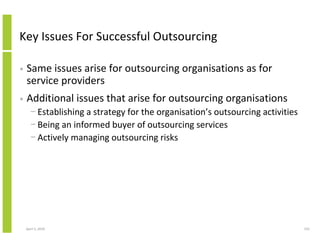
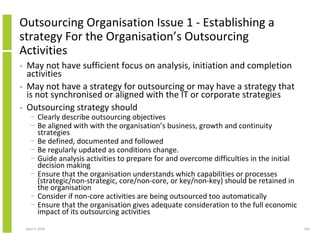
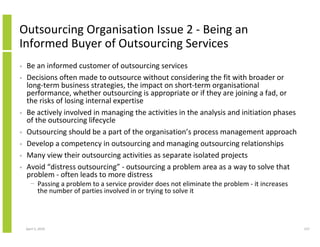
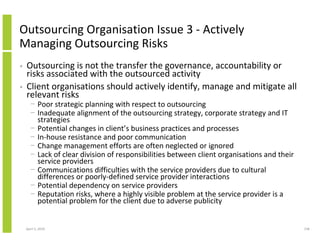
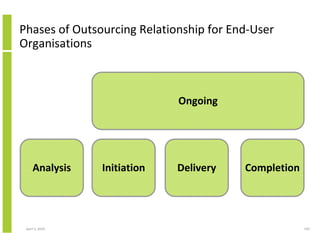
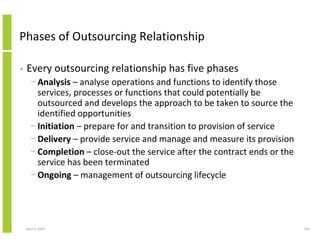
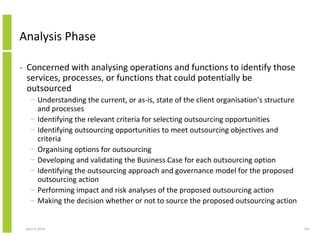
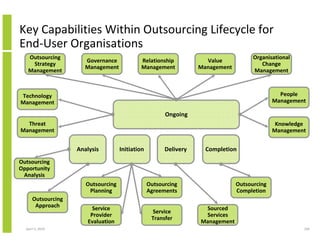
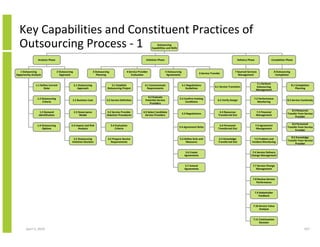
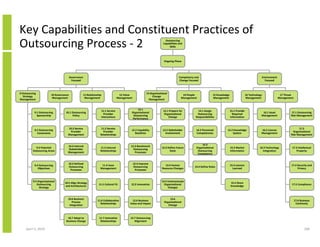
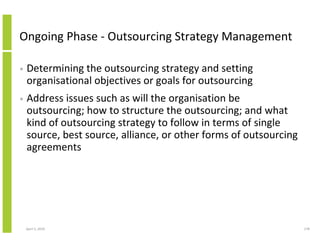
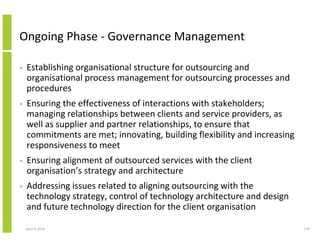
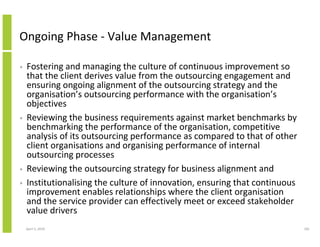
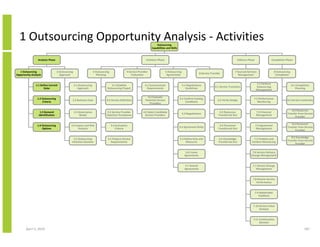
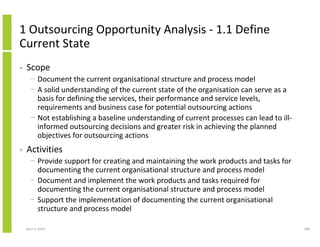
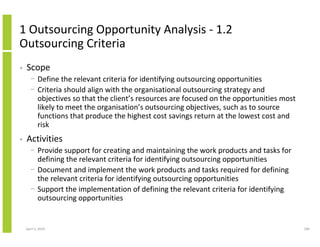
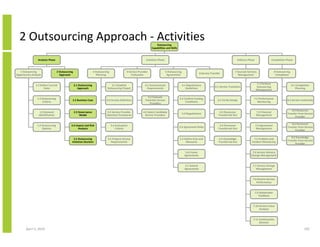
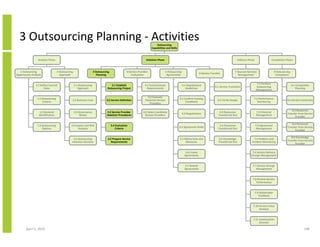
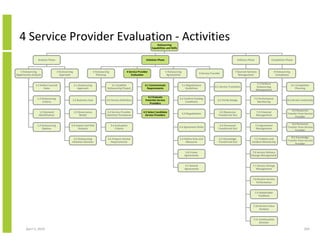
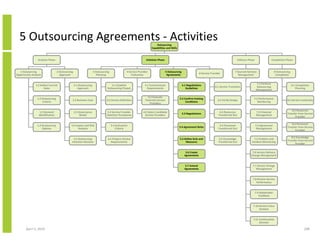
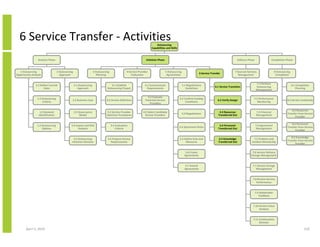
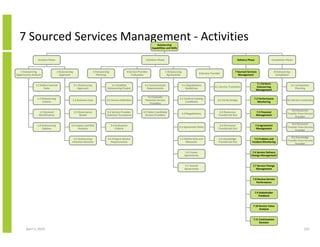
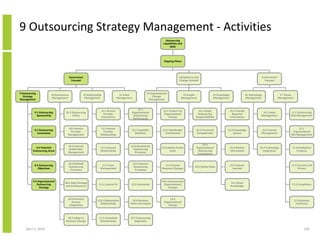
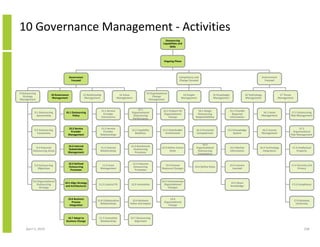
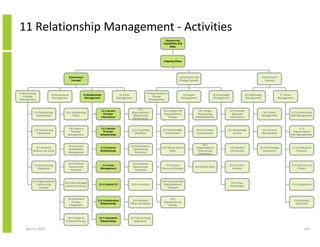
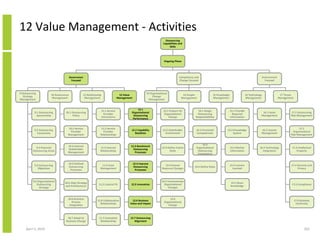
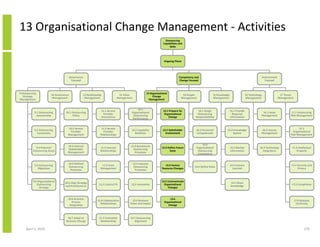
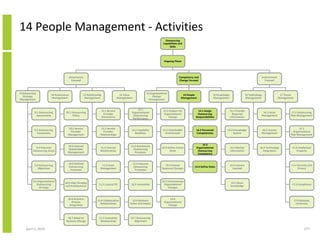
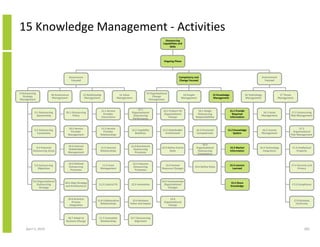
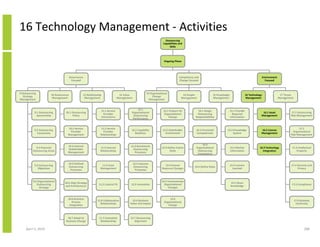
This document outlines a structured approach to implementing outsourcing from both the service provider and client organization perspectives, with a focus on cloud computing. It describes four phases of an outsourcing relationship - initiation, delivery, completion, and ongoing management. Key capabilities for each phase are also identified, such as contracting, service design, performance management, and technology management. The document provides examples of activities within each phase and capability as well as lessons learned from common outsourcing problems. The overall approach is presented as a framework to help both service providers and clients successfully establish and manage outsourcing relationships.