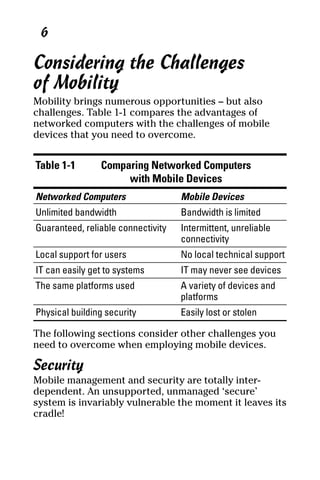
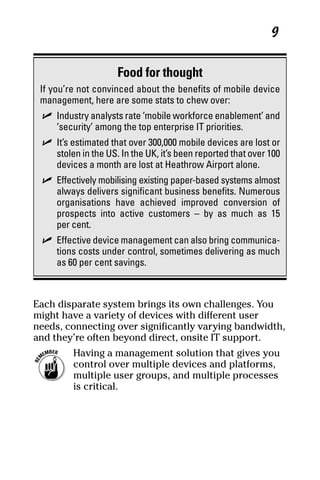
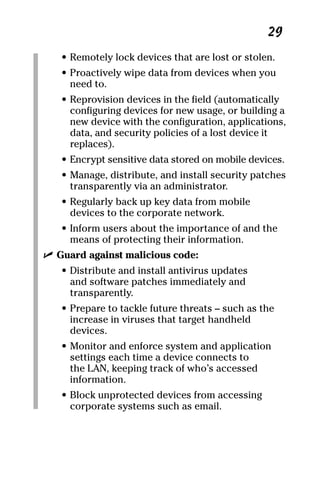
Mobile device management provides security, visibility, and control for organizations using mobile devices. Without proper management, mobile devices face challenges including limited security, inconsistent connectivity, and a lack of centralized visibility and control for IT. Effective device management is needed to overcome these challenges, protect sensitive data, enforce compliance with regulations, and maximize the benefits of an organization's mobile workforce.