Embed presentation
Downloaded 223 times
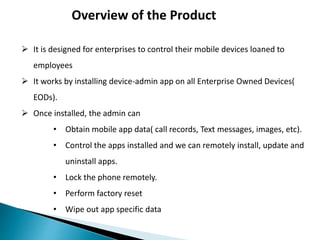
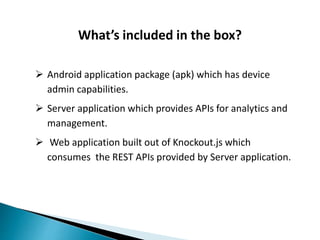
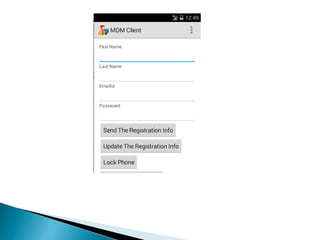
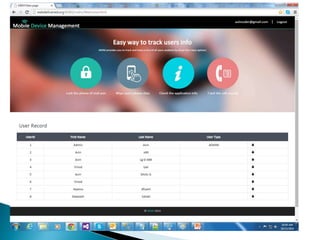
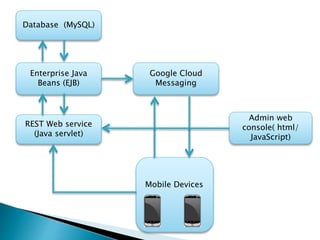
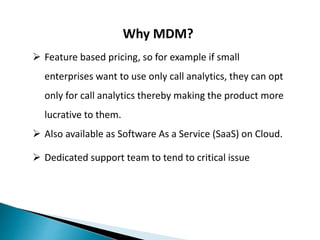
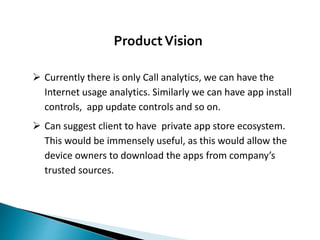
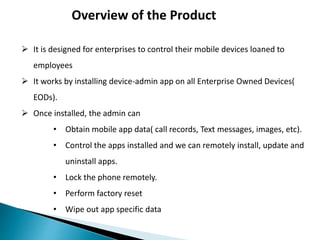
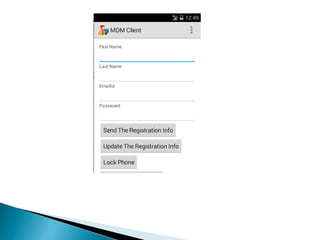
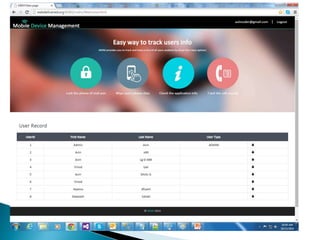
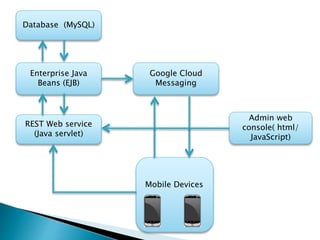
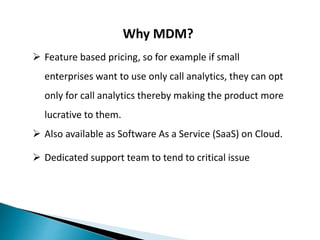
Mobile Device Management (MDM) software allows companies to secure, manage, and monitor mobile devices used by employees. The MDM software installs an admin app on company-owned devices, allowing IT administrators to obtain mobile data, control app installation and updates, remotely lock or wipe devices, and enforce company policies. The MDM system includes an Android/iOS app, server software with REST APIs, and an admin web console to control and analyze device usage from a central dashboard. MDM provides security, analytics, and remote management capabilities to enterprises at different subscription levels.