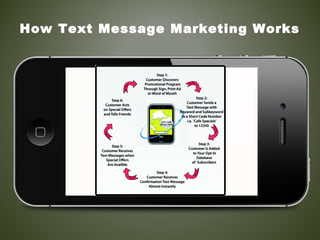
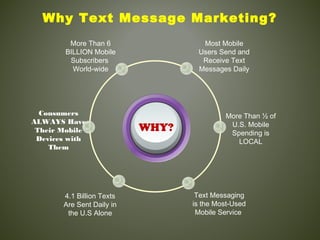
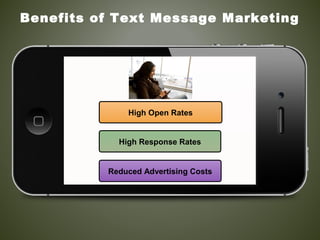
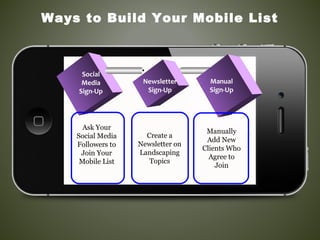
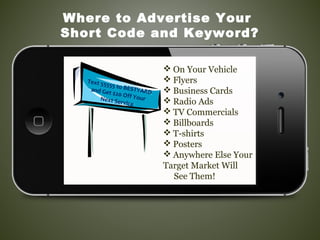
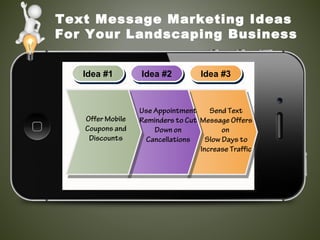
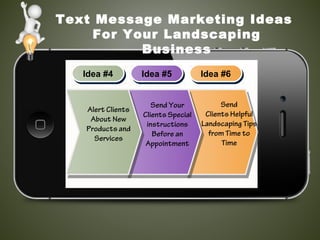
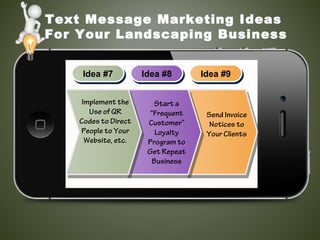
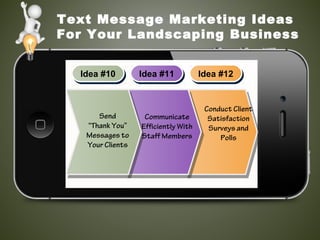
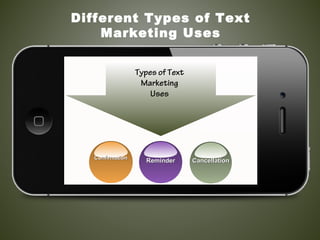
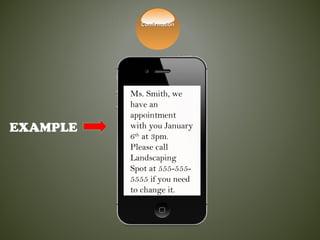
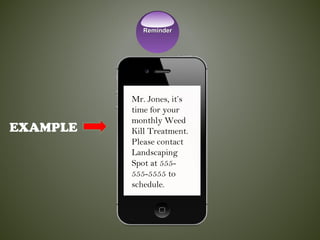
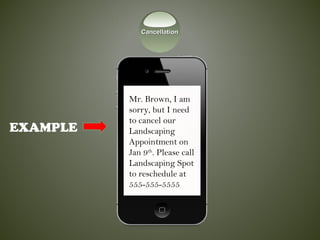
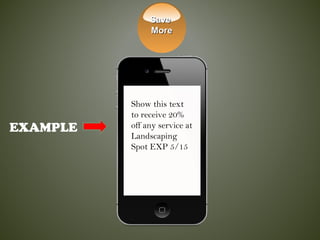
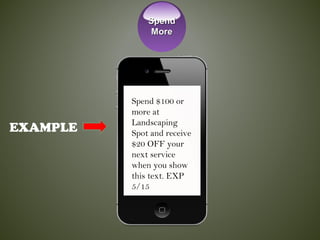
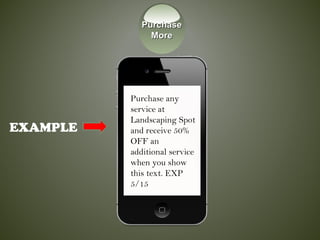
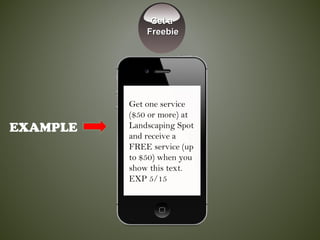
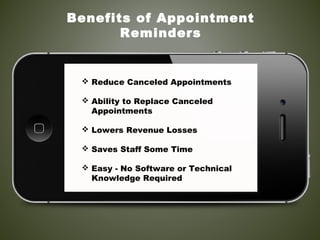
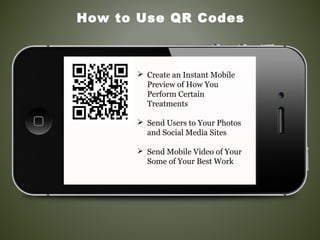
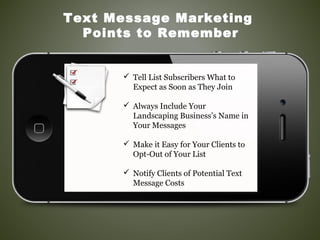
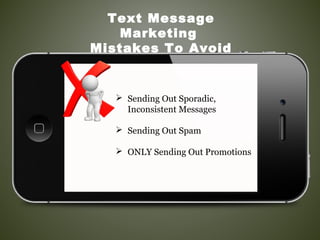
This document provides tips and ideas for using text message marketing for a landscaping business. It explains what text message marketing is, the benefits which include high response rates and building loyalty. Ideas are given for different types of text campaigns including discounts, reminders and cancellations. It also outlines best practices such as only sending relevant messages and allowing opt-out to avoid mistakes. The goal is to use the powerful yet limited text format to boost business and reduce issues like canceled appointments.