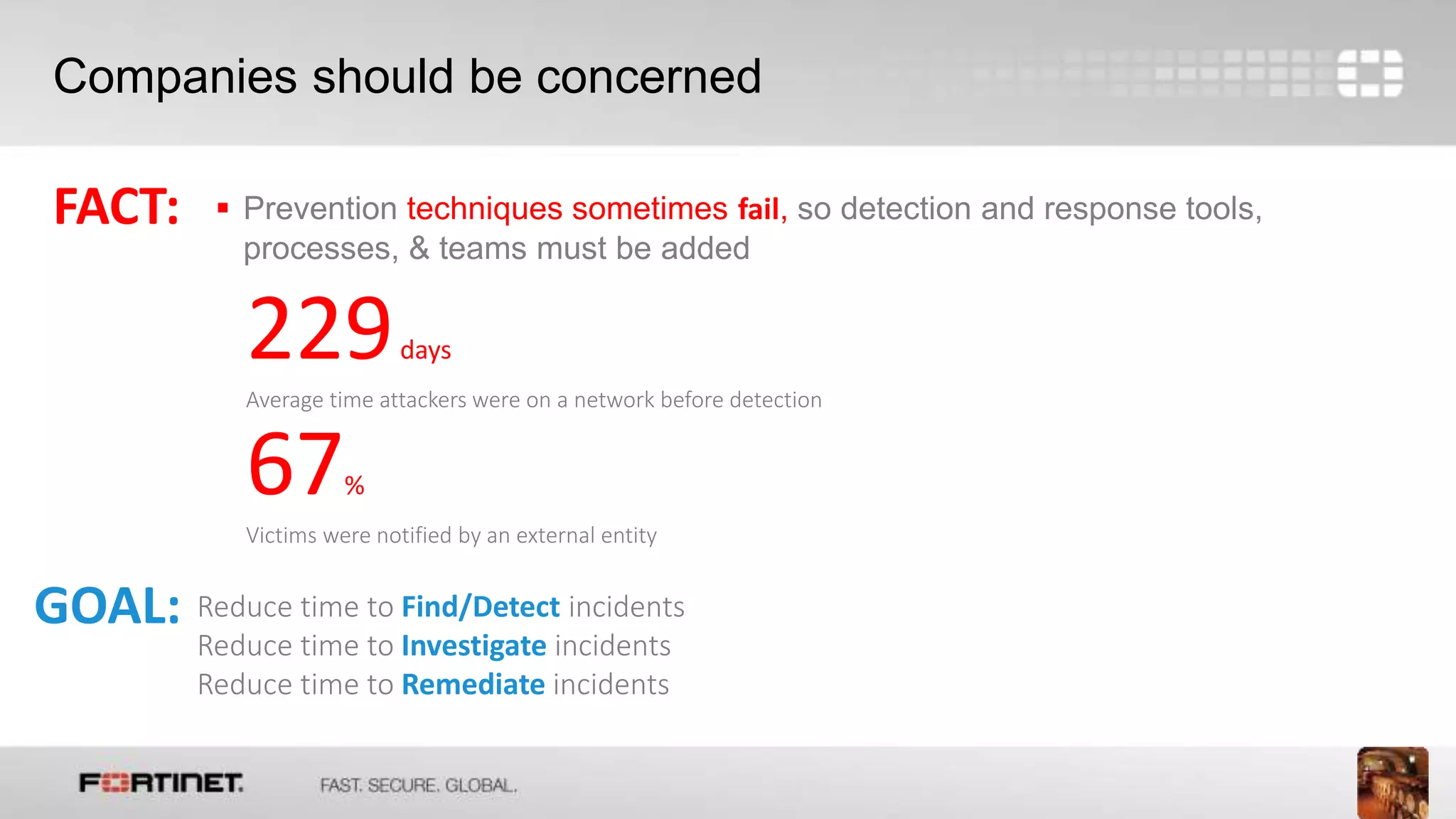
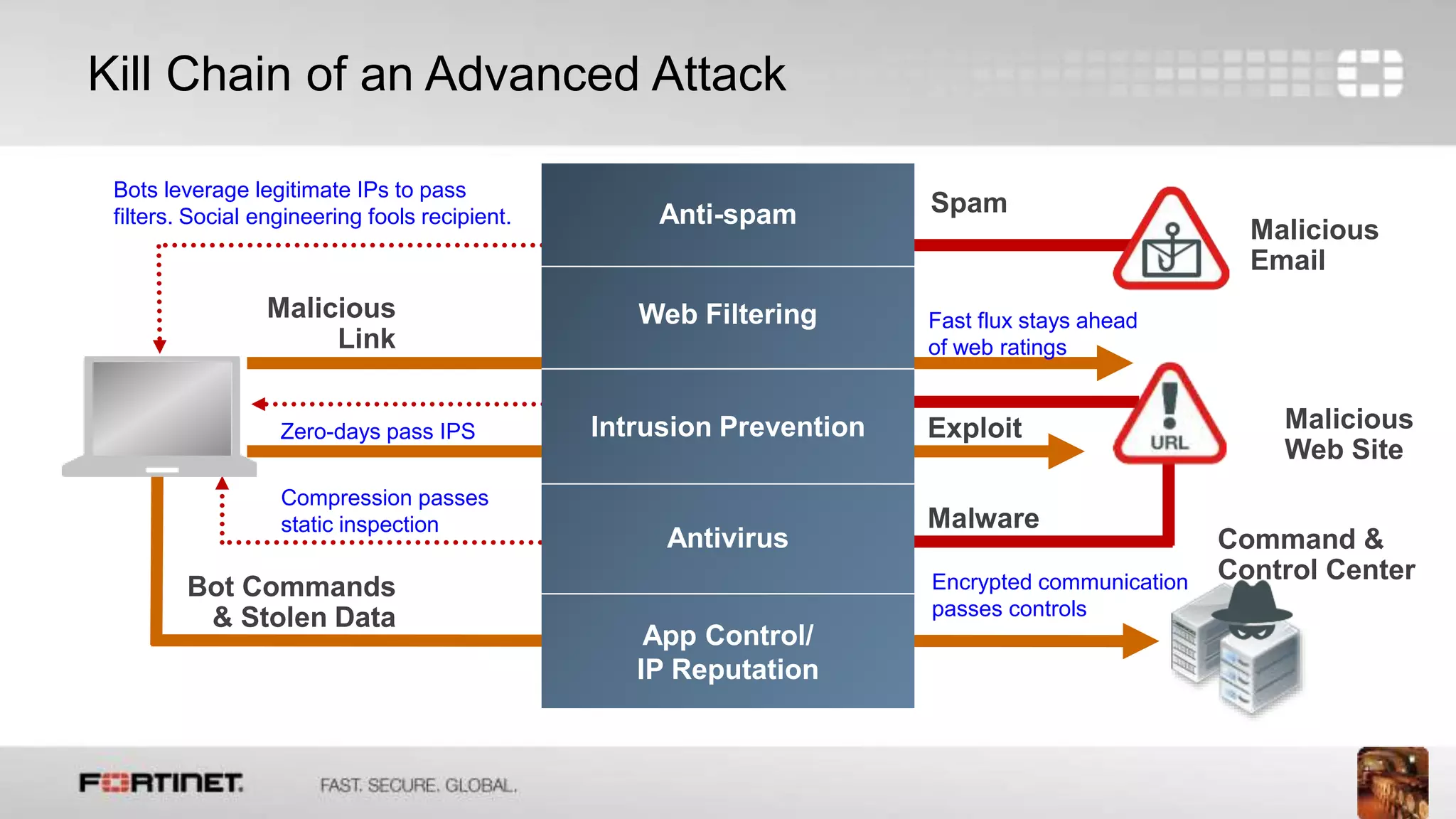
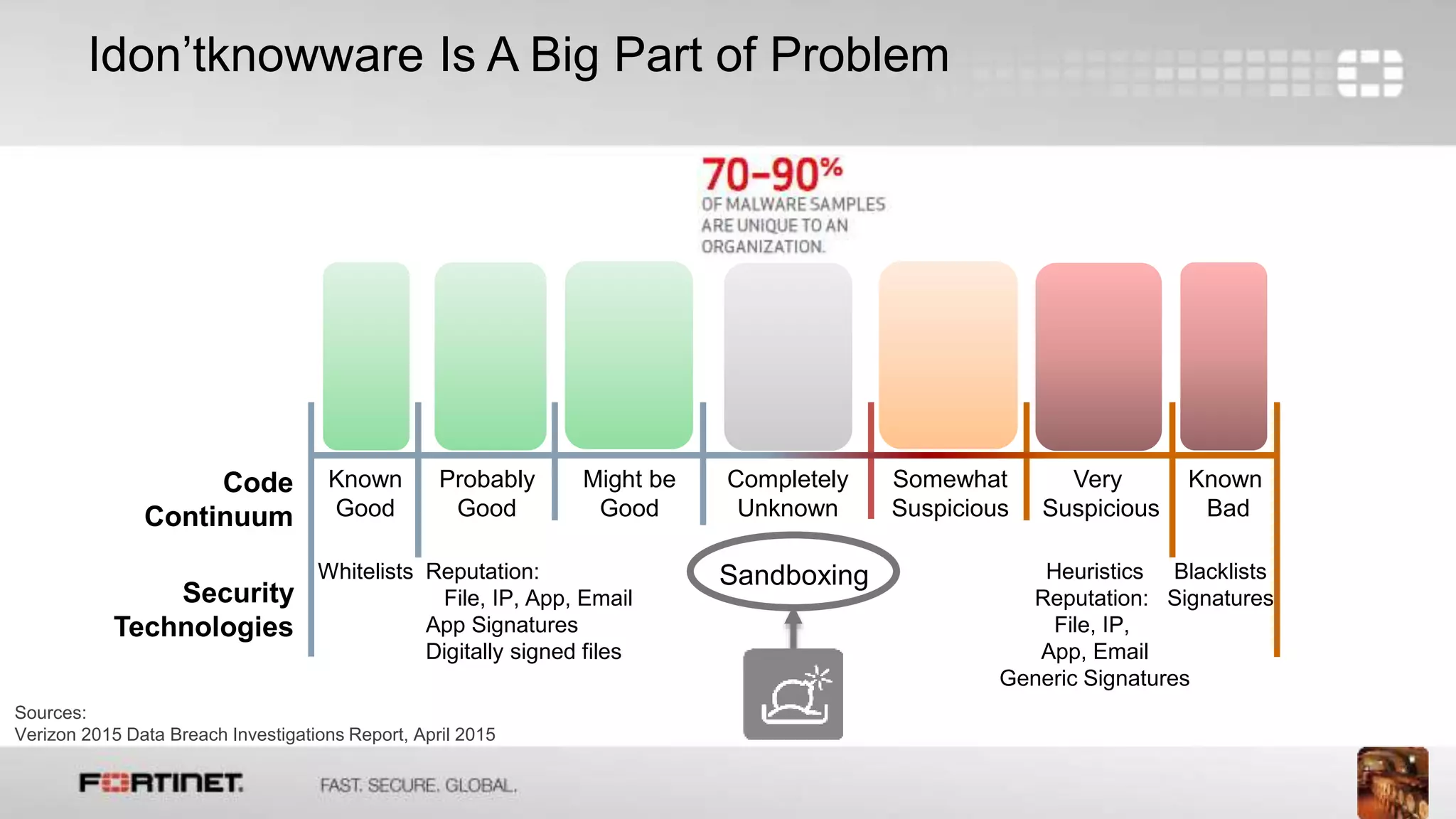
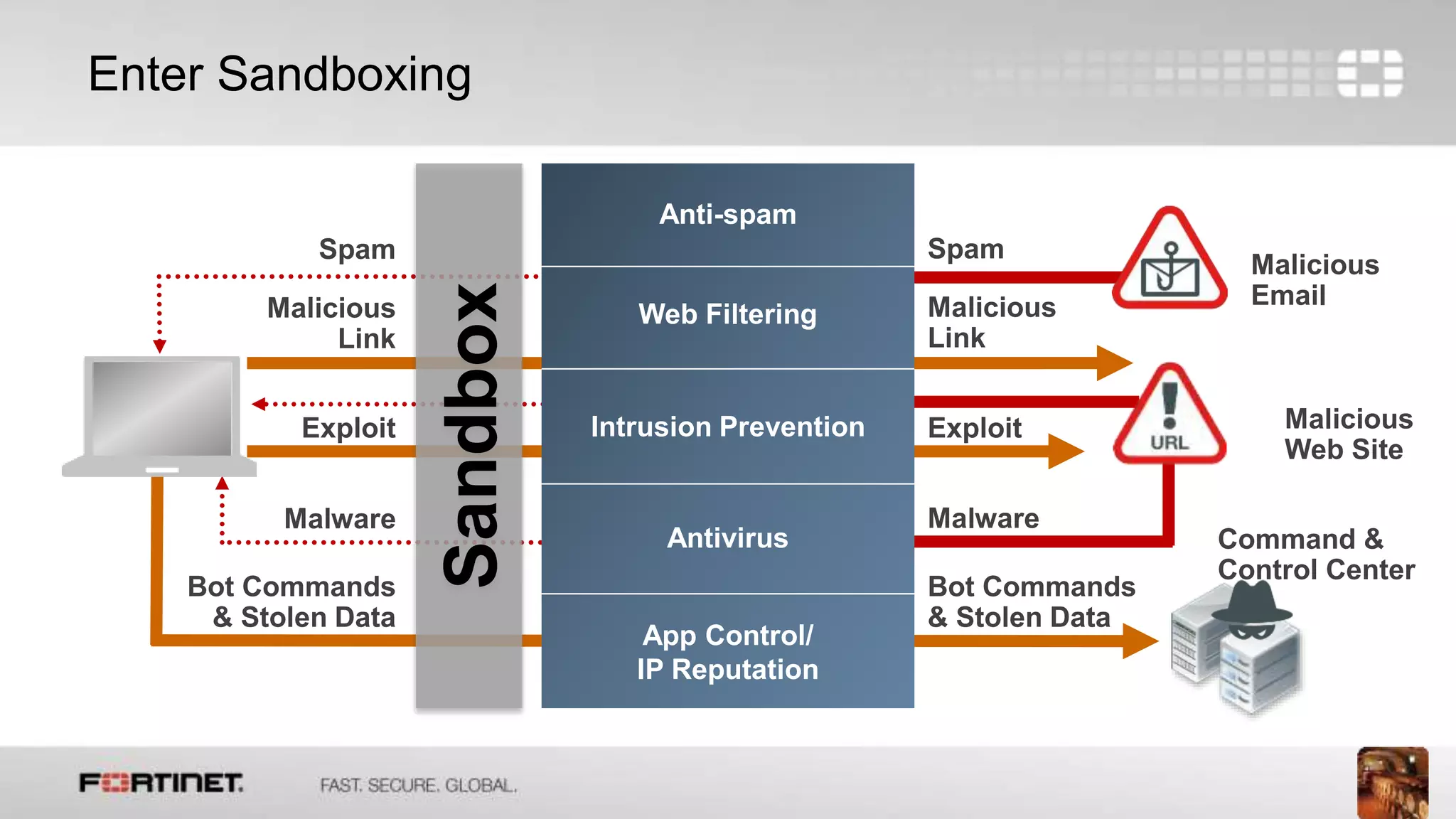
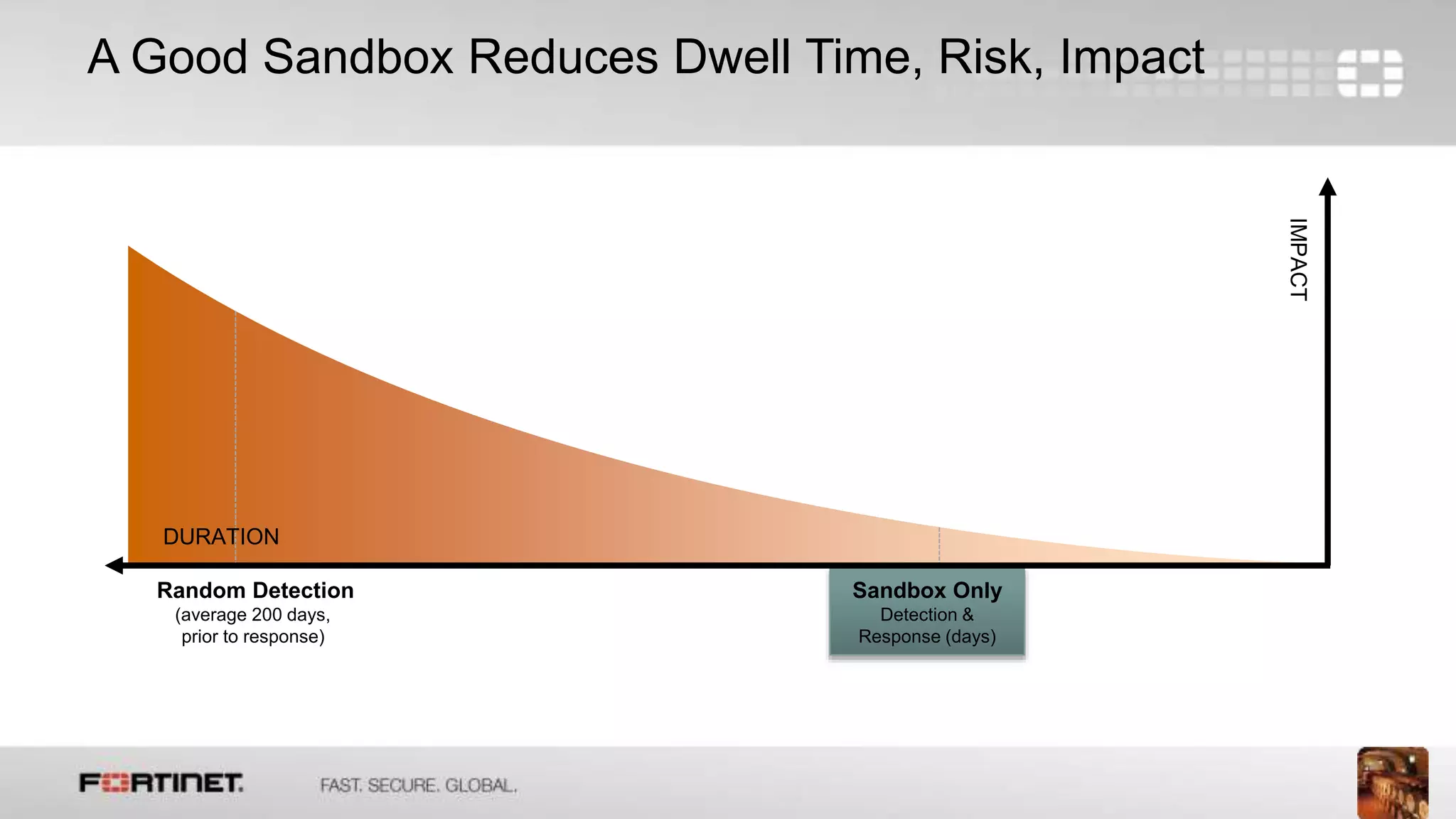
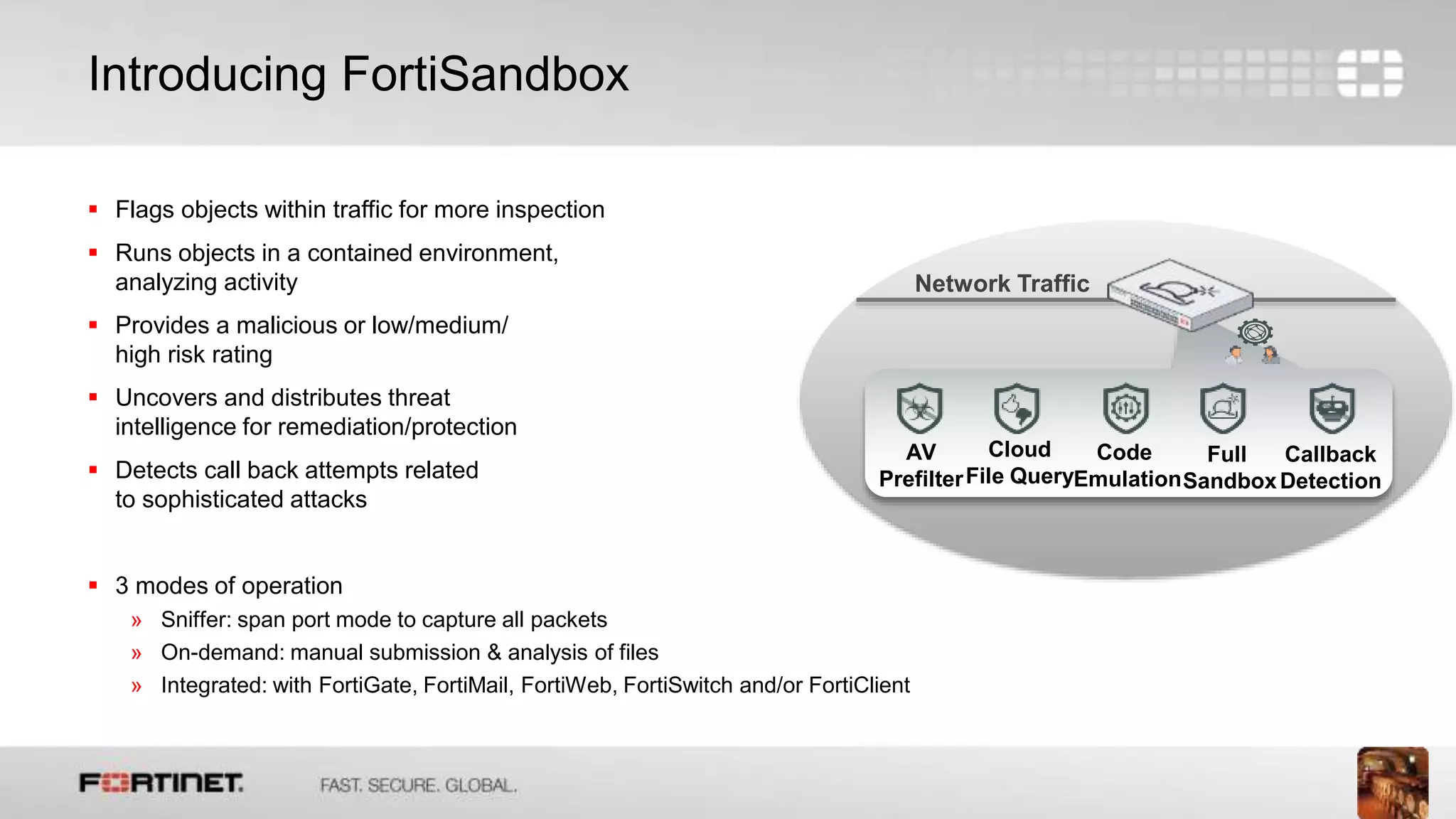
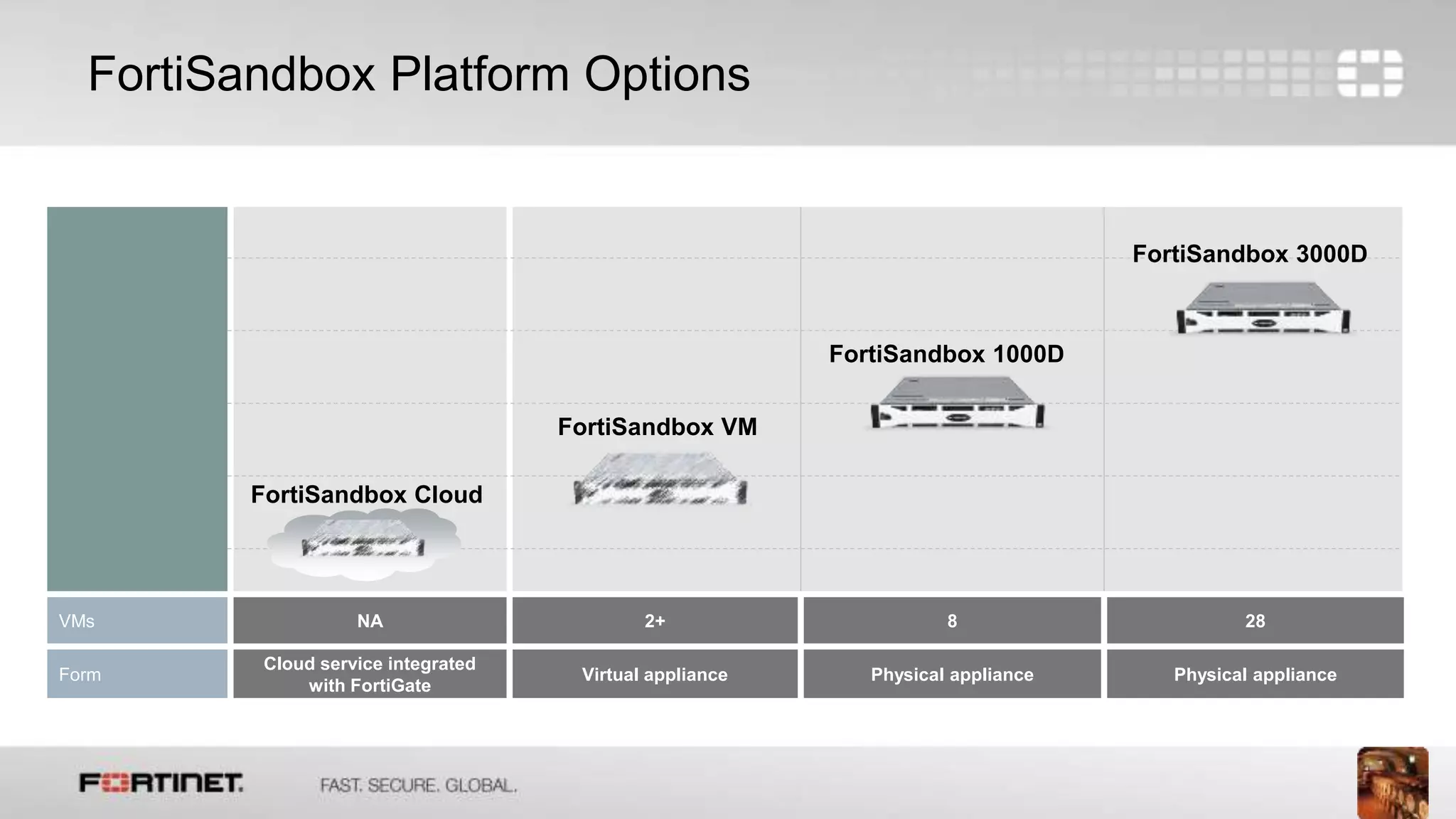
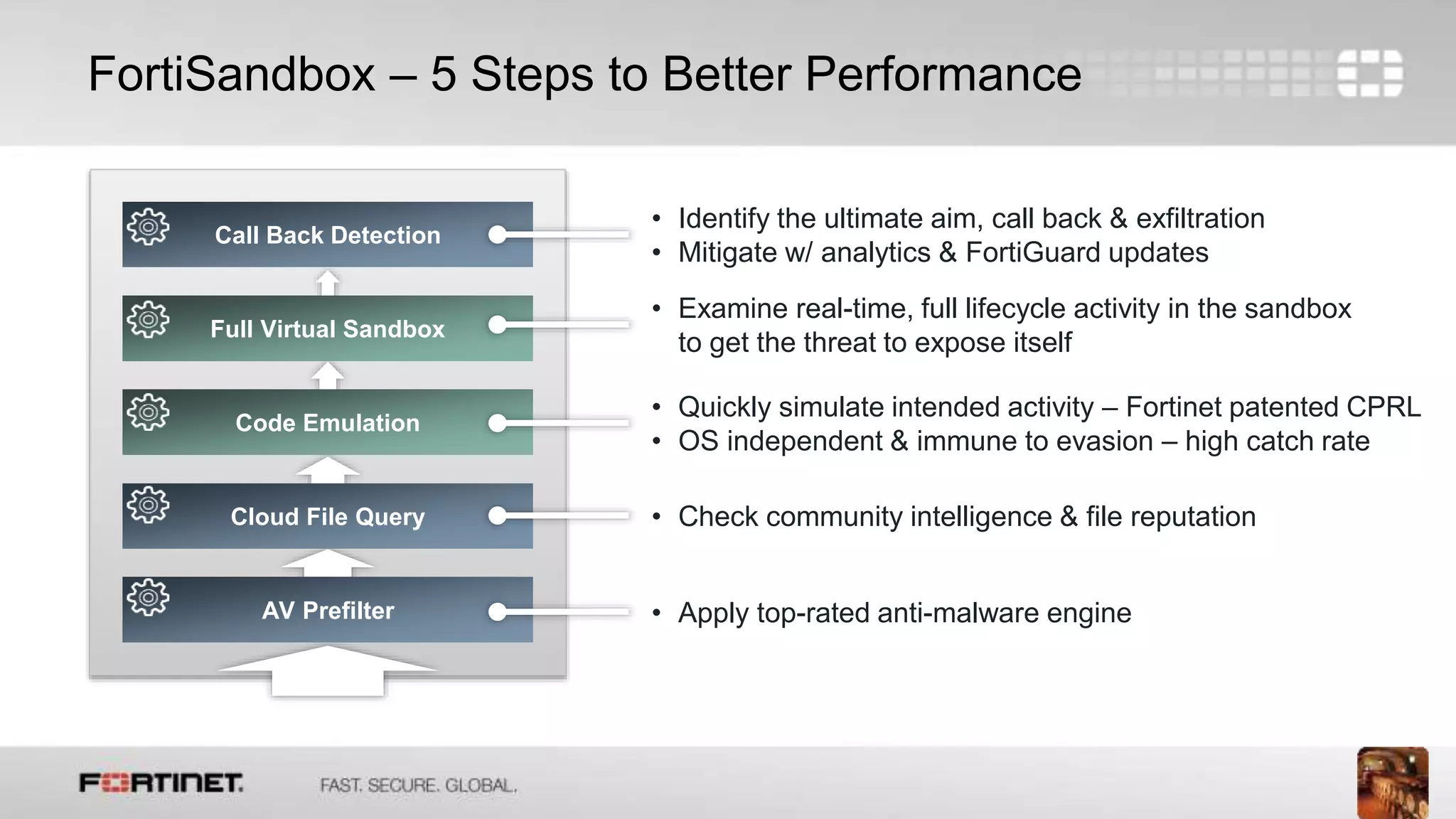
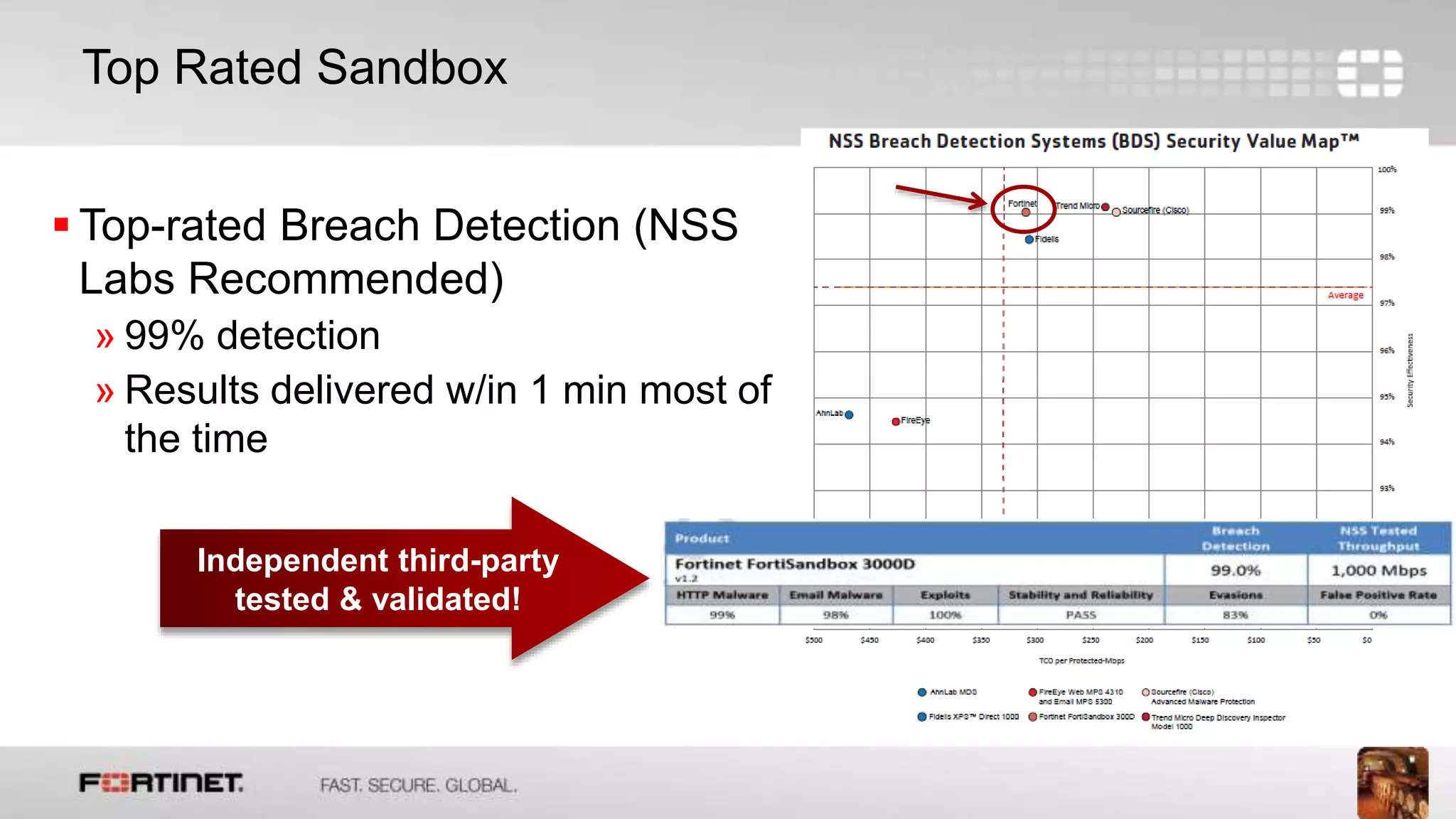
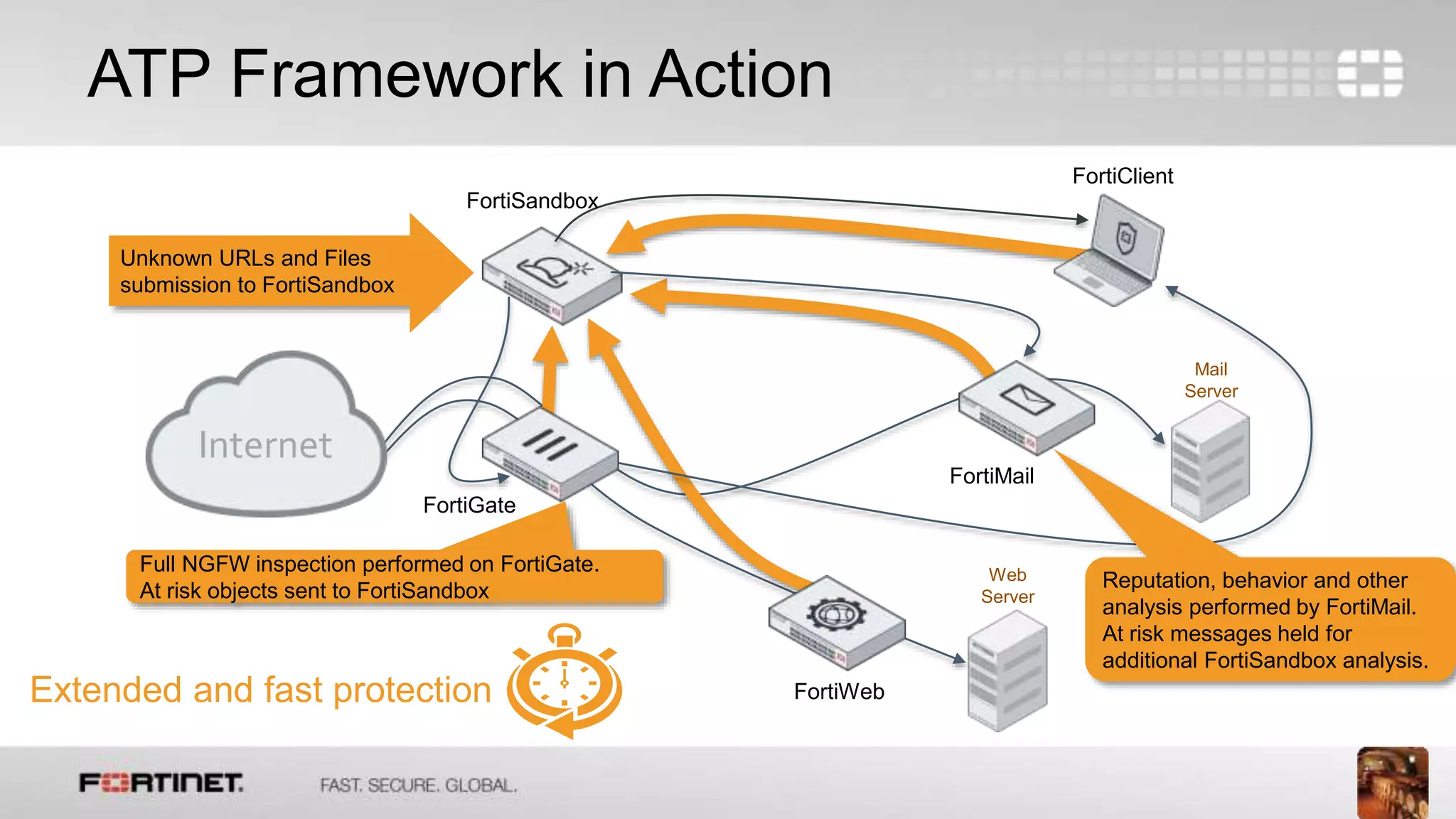
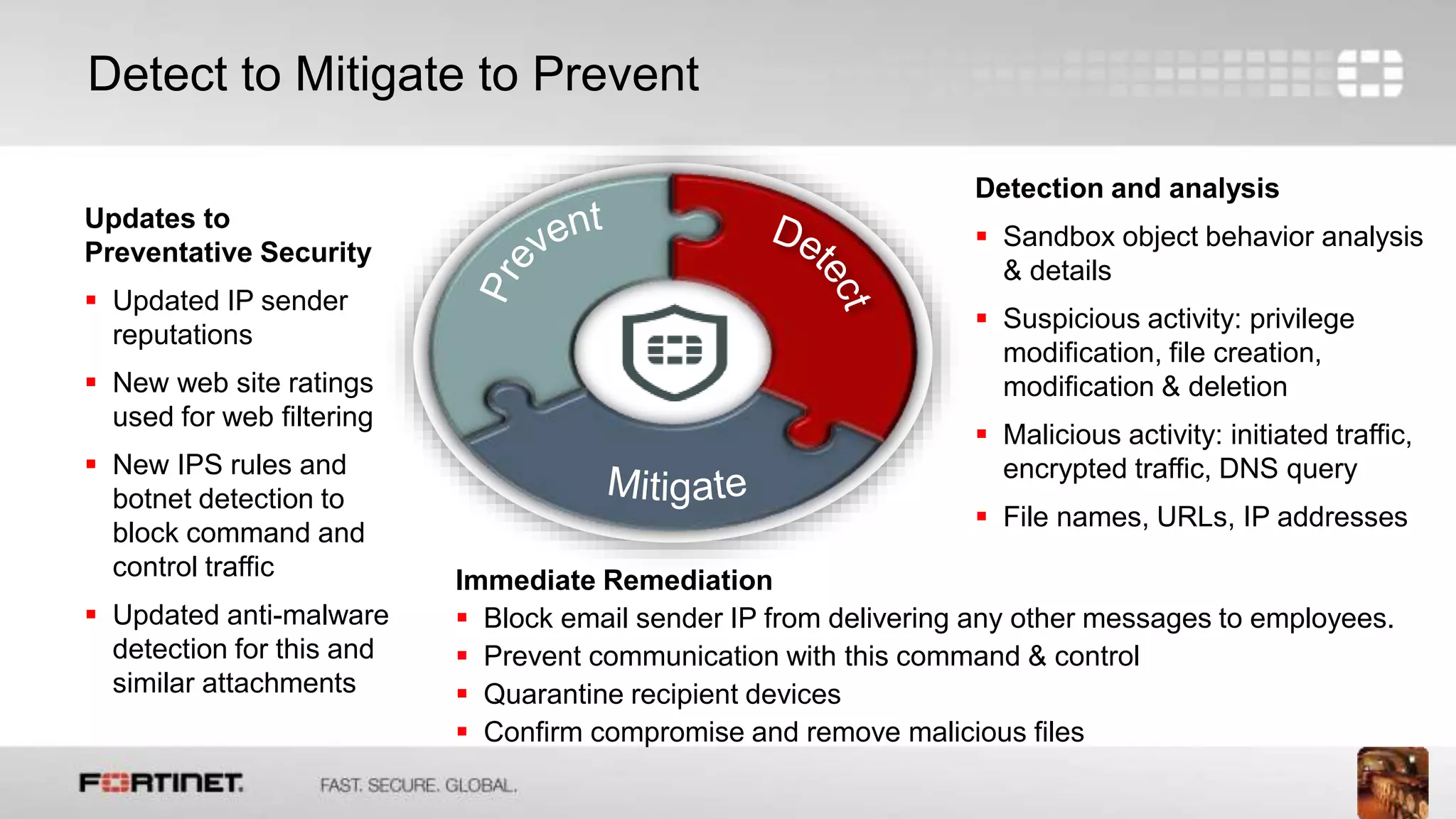
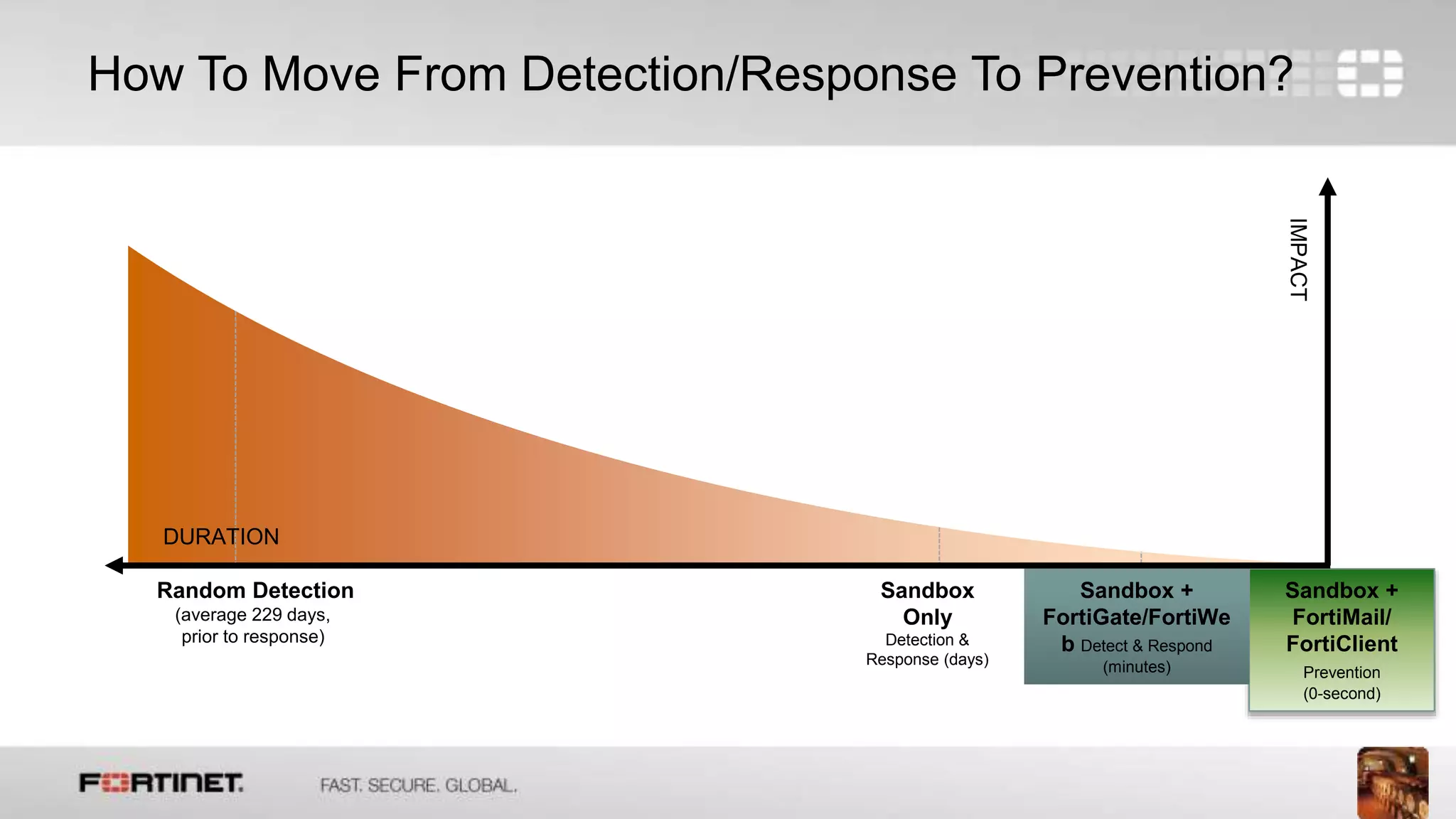
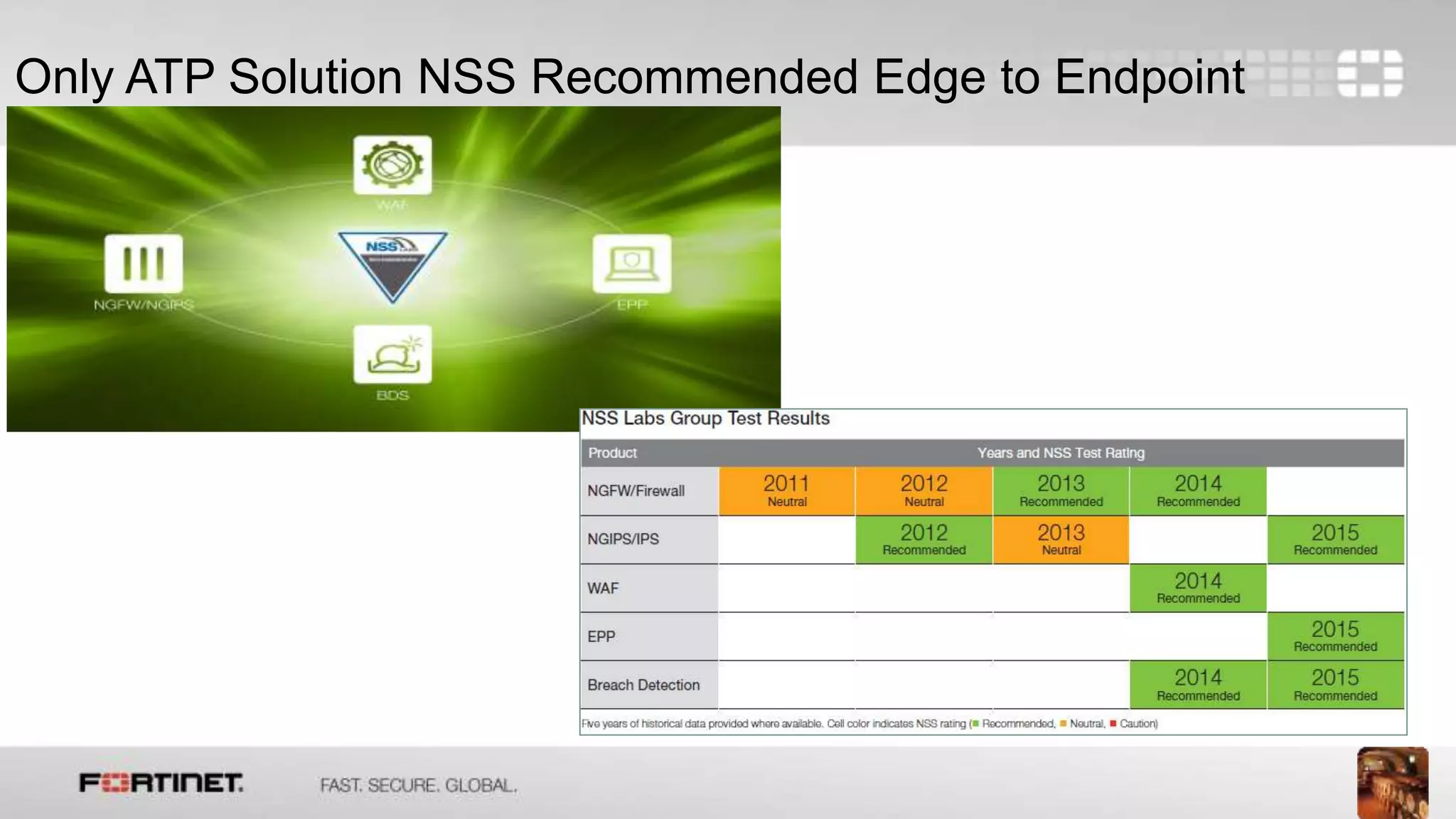
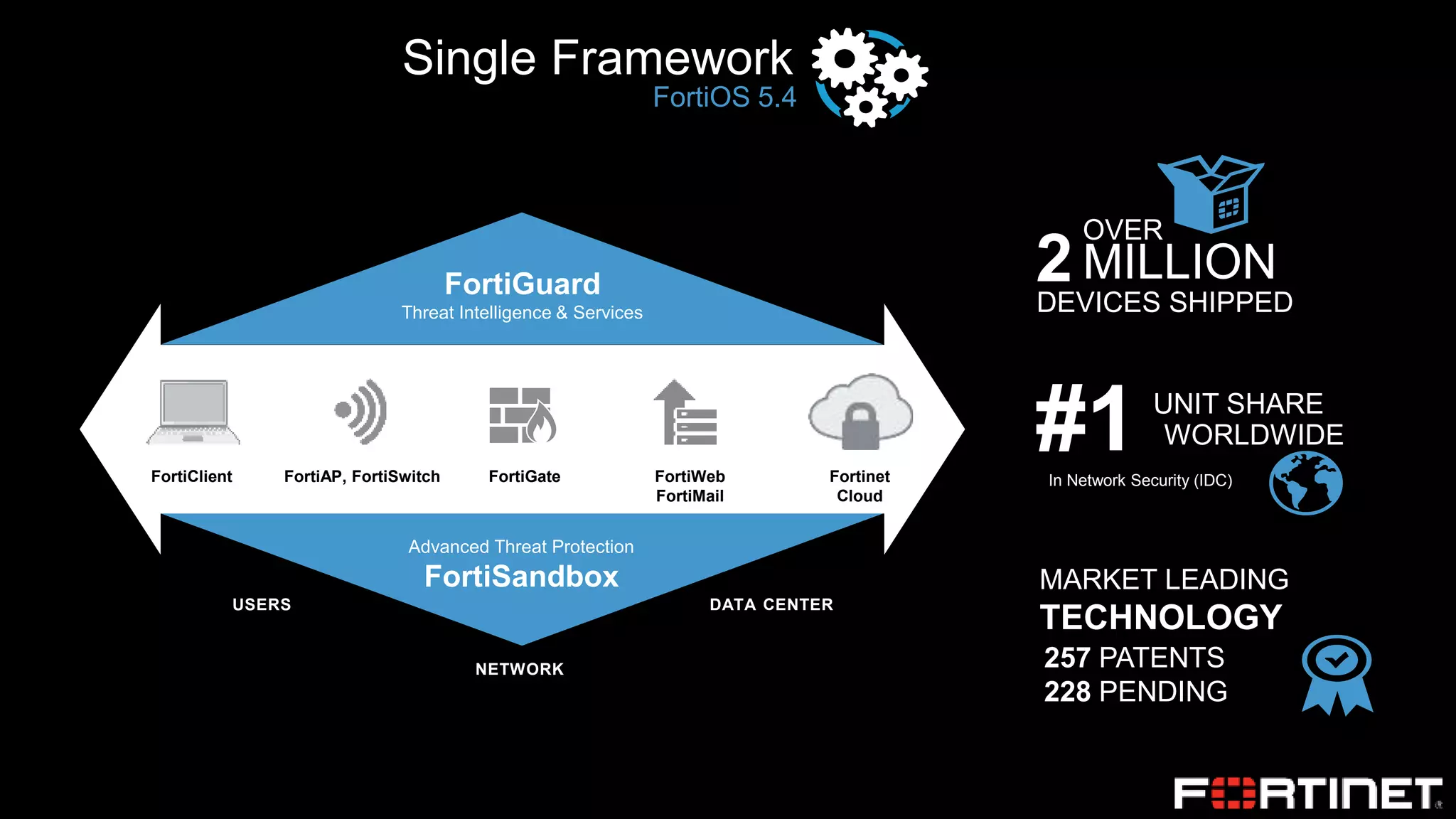
This document discusses advanced threat protection and FortiSandbox. It notes that prevention techniques sometimes fail, so detection and response tools are needed to reduce the time it takes to find, investigate, and remediate incidents. Sandboxing is introduced as an effective technique that runs suspicious objects in a contained virtual environment to analyze behavior and uncover threats. FortiSandbox is highlighted as a solution that integrates with FortiGate and other Fortinet products to provide detection, analysis, and sharing of threat intelligence across the network to improve security.