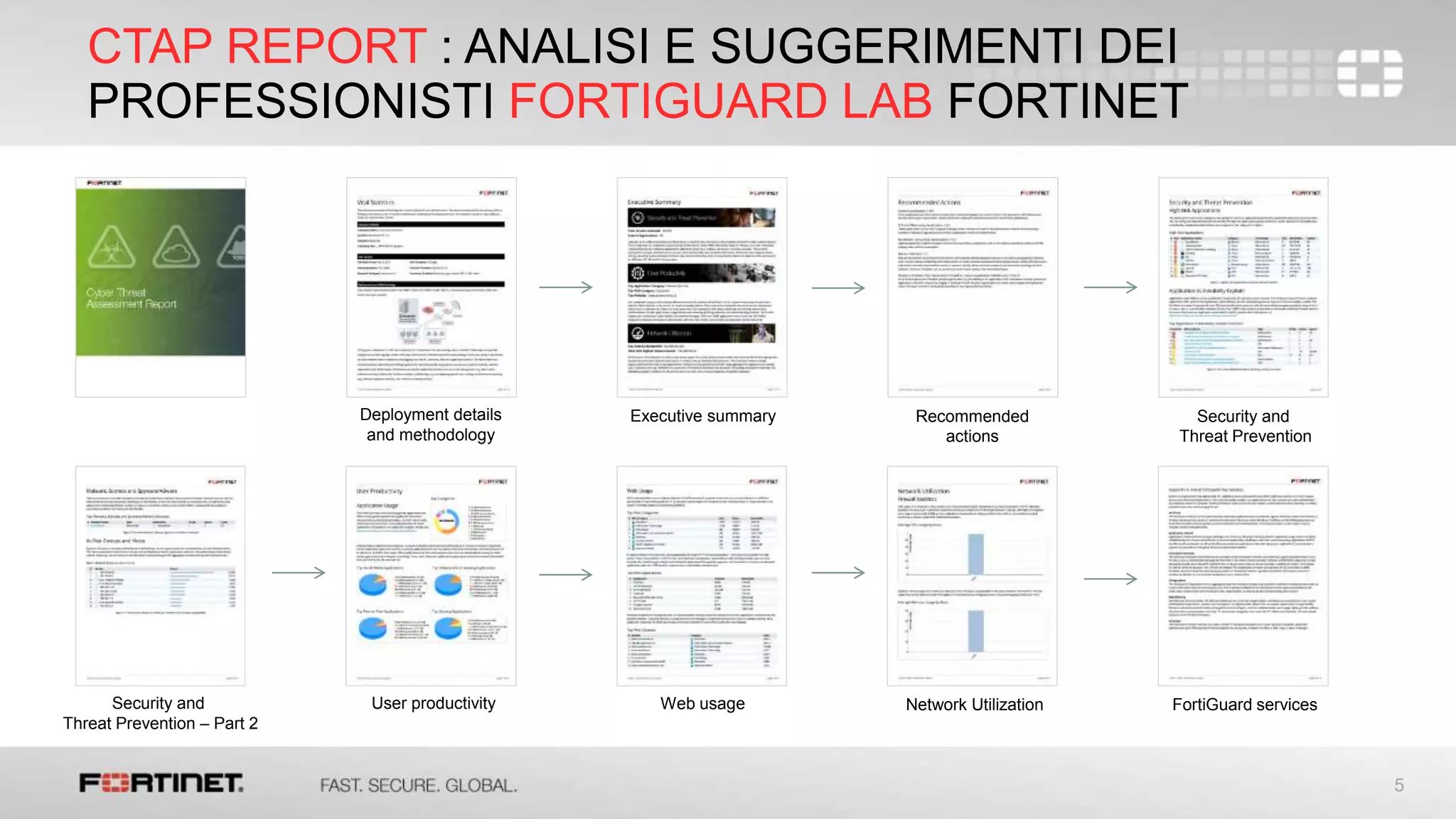
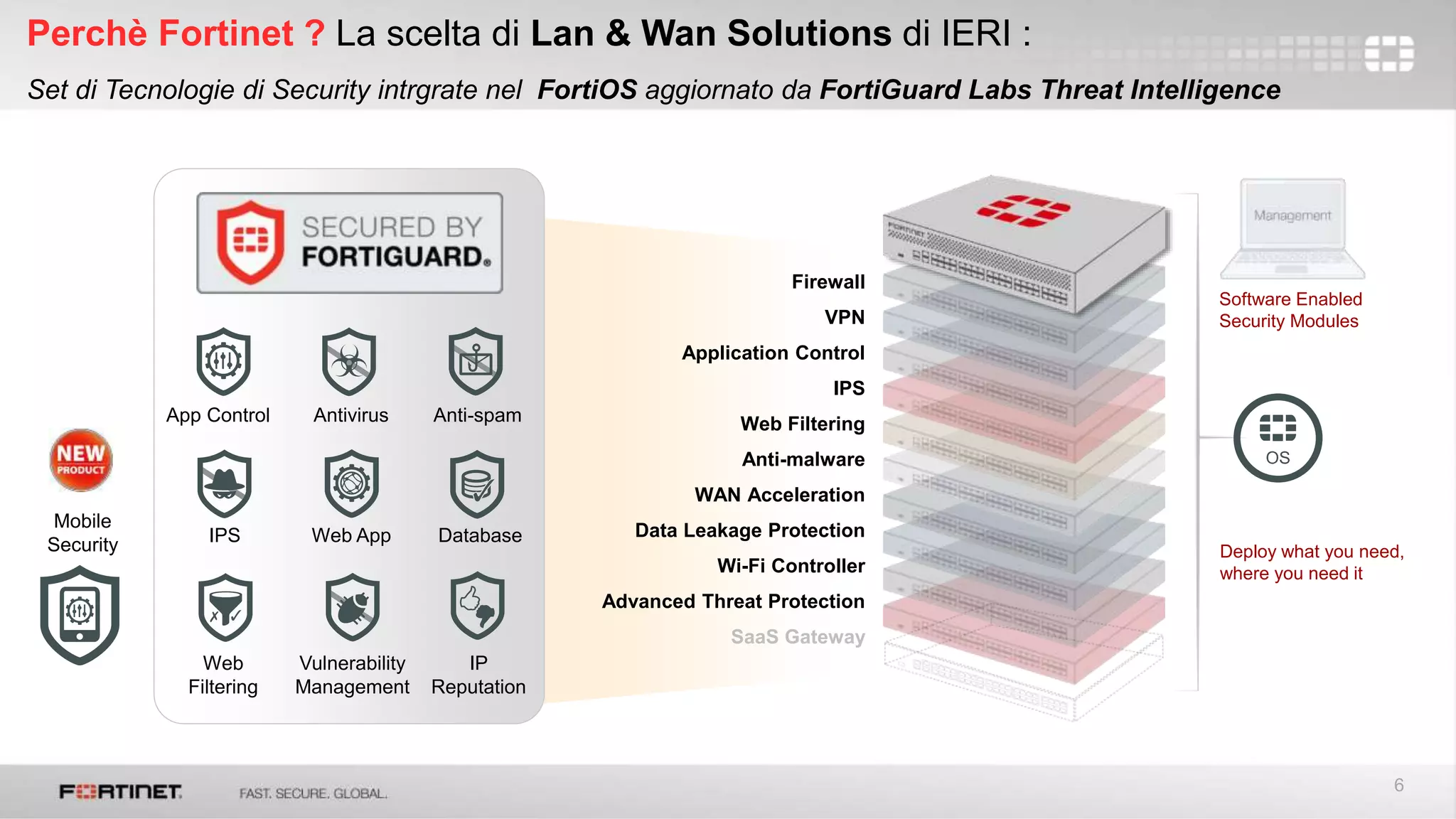
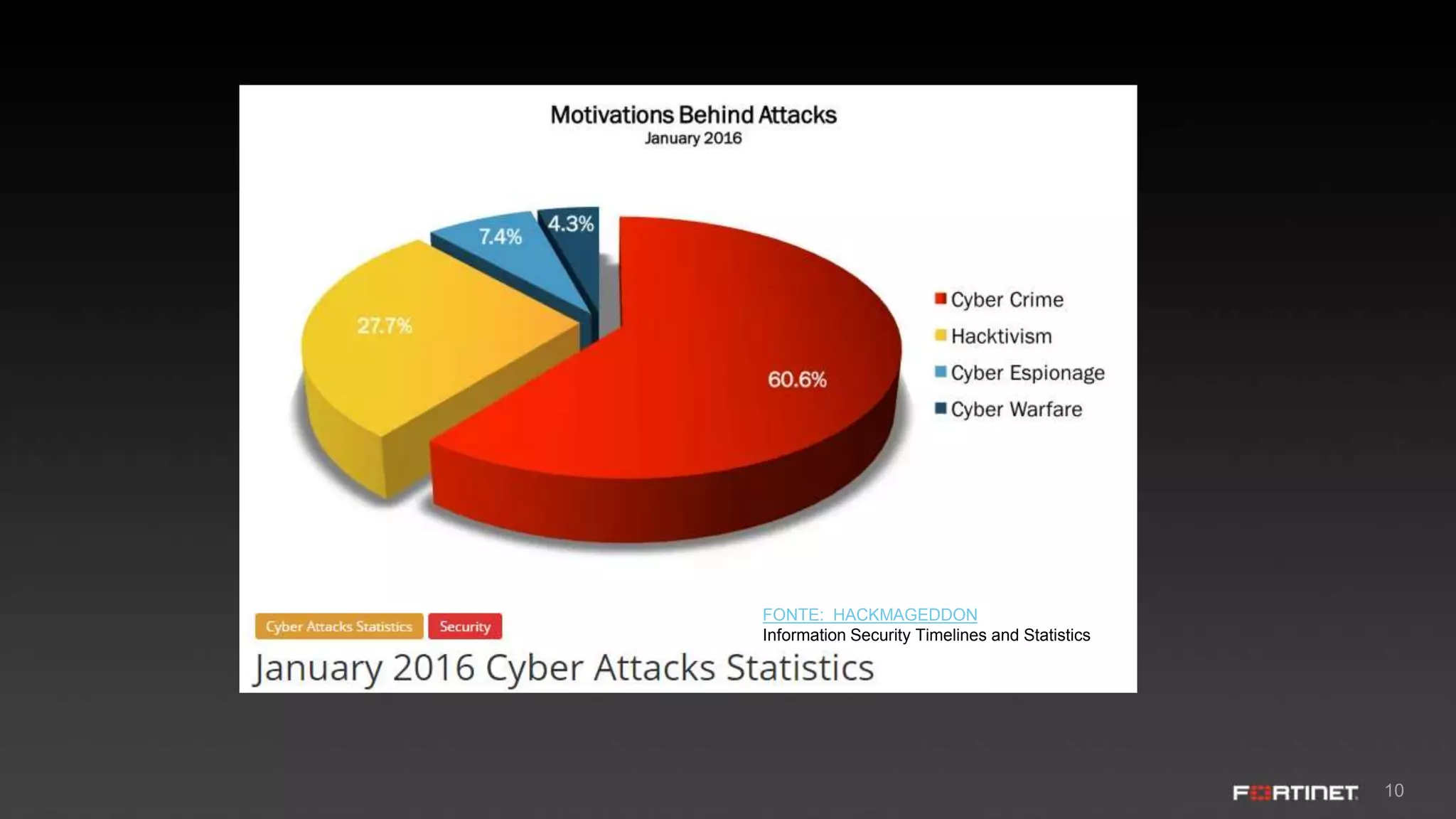
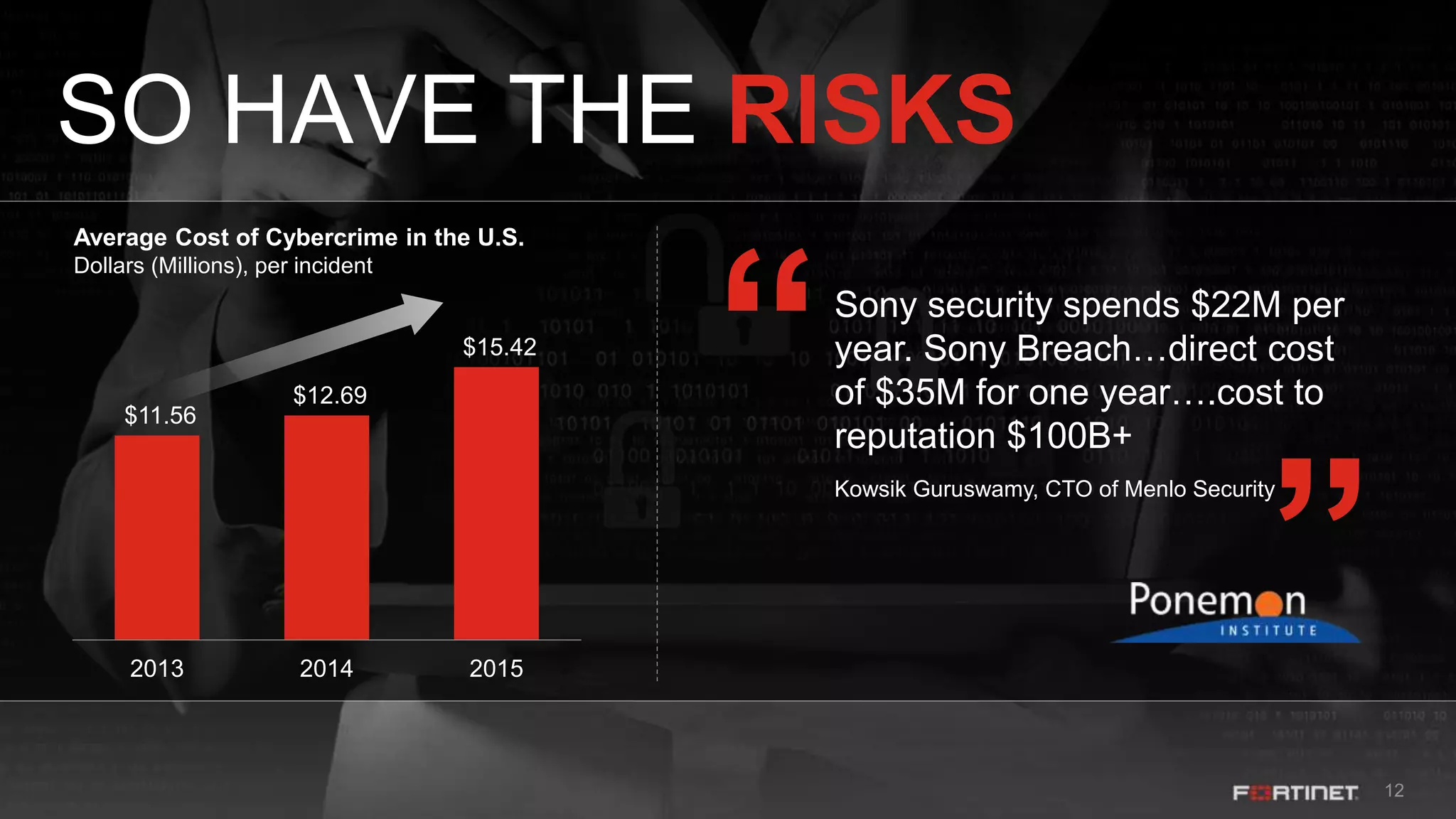
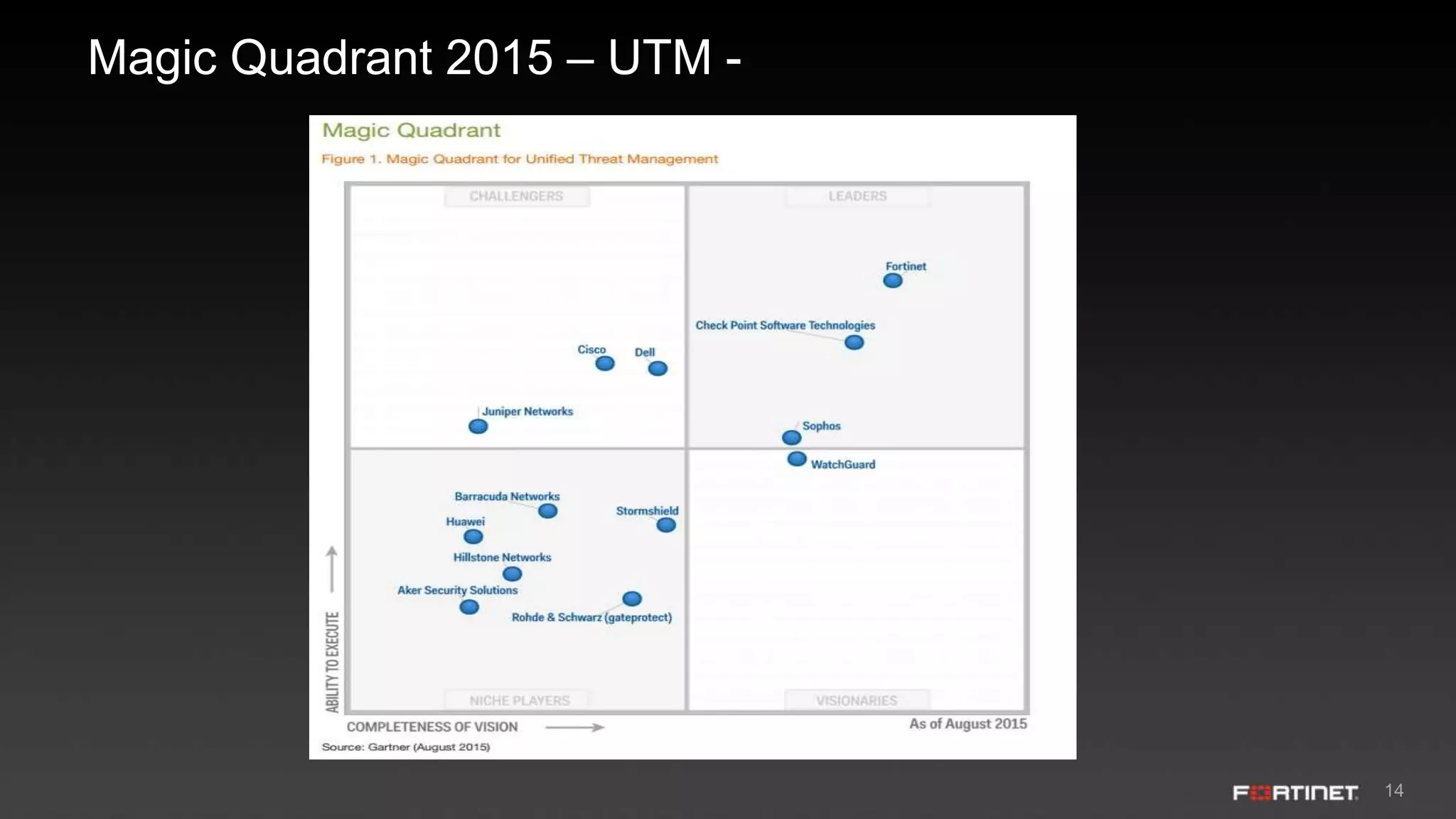
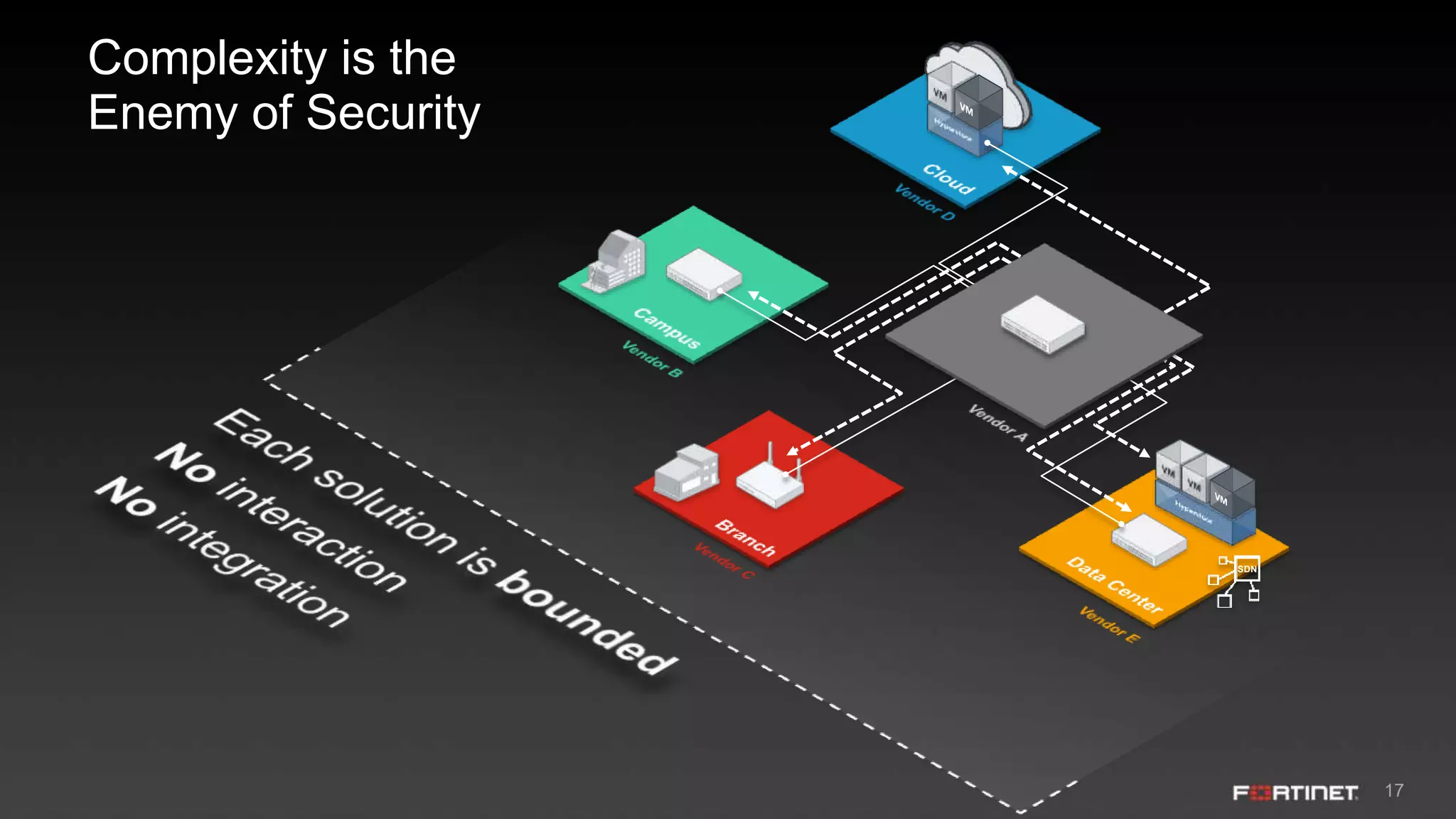
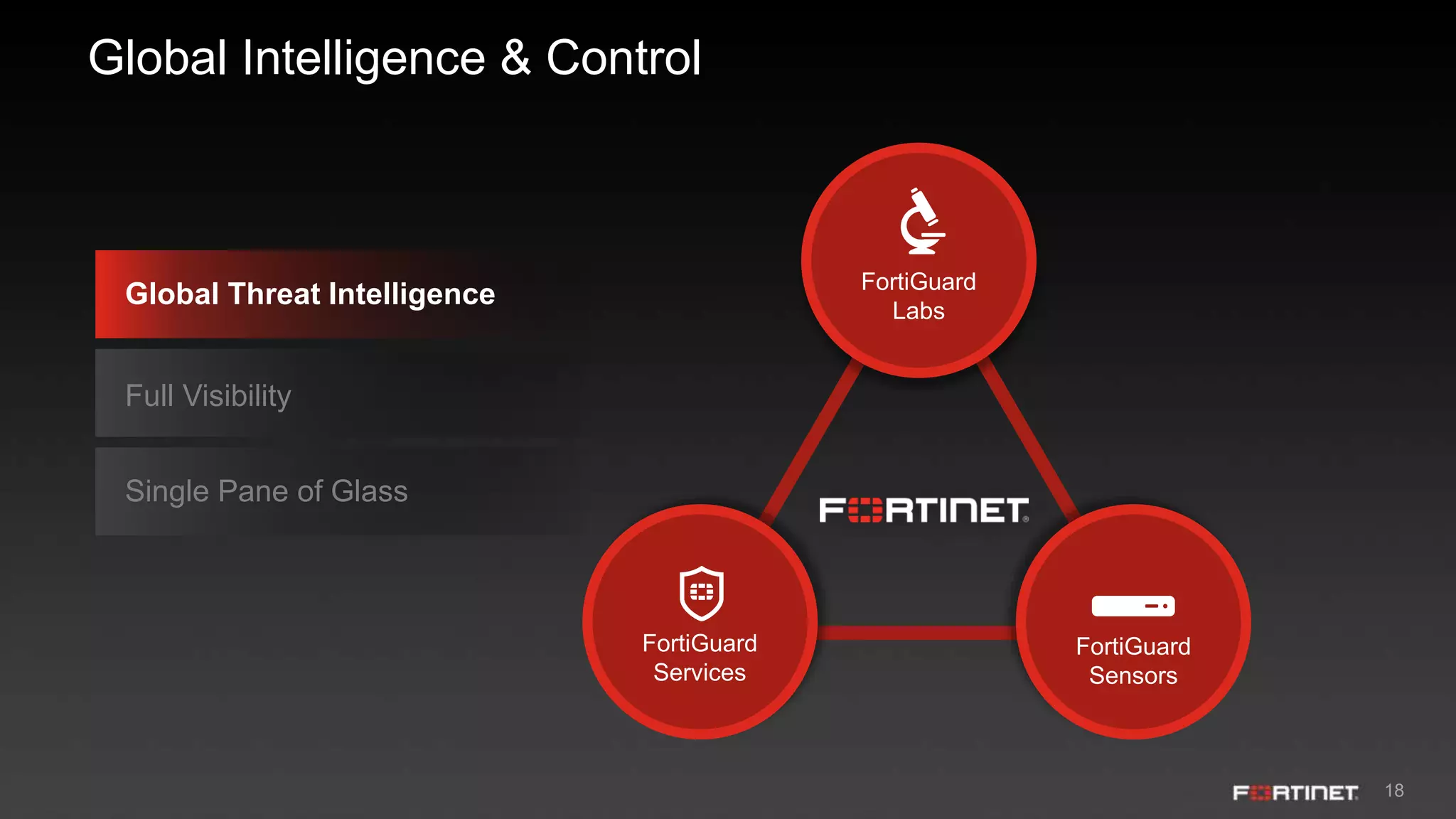
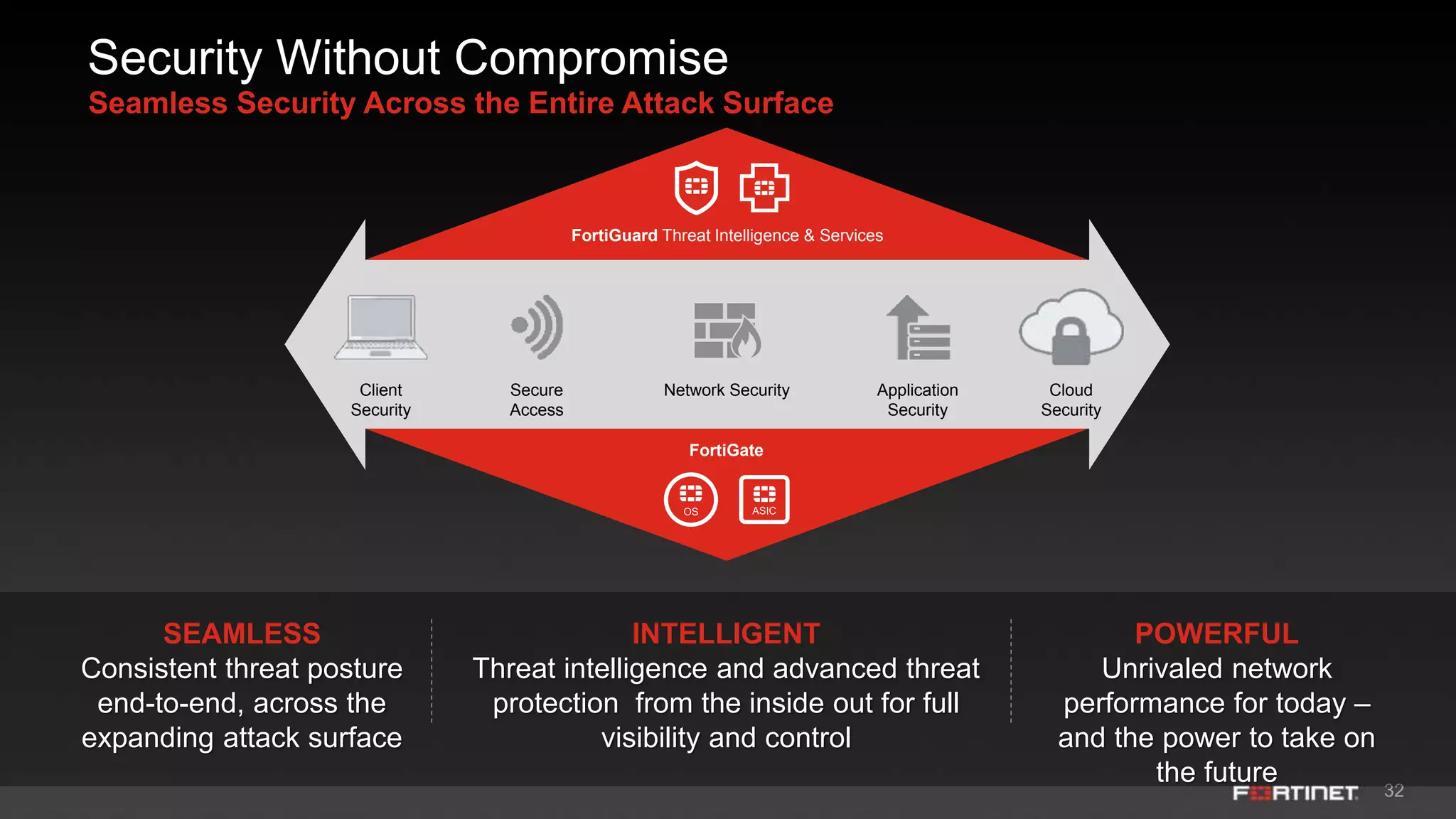
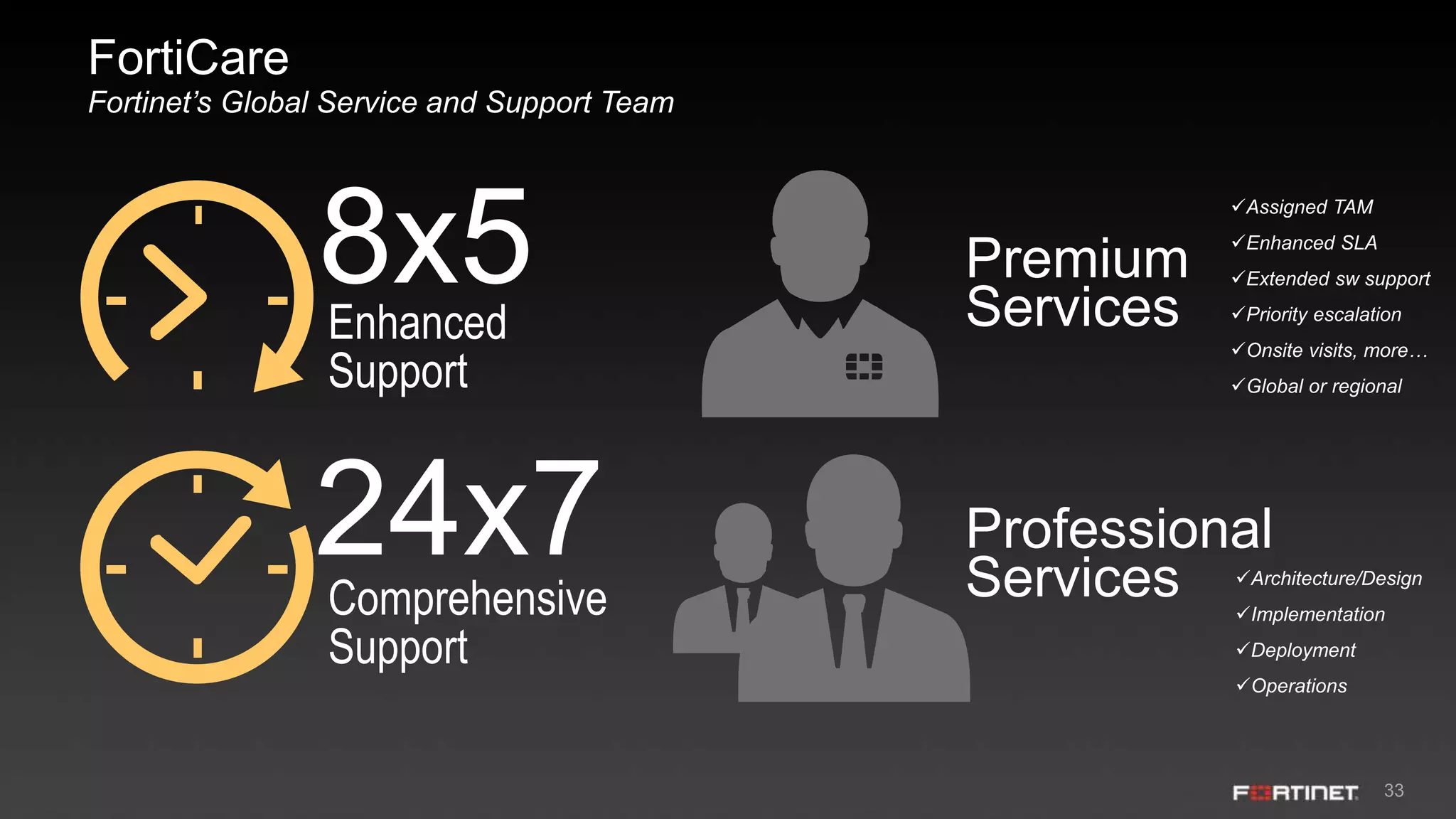
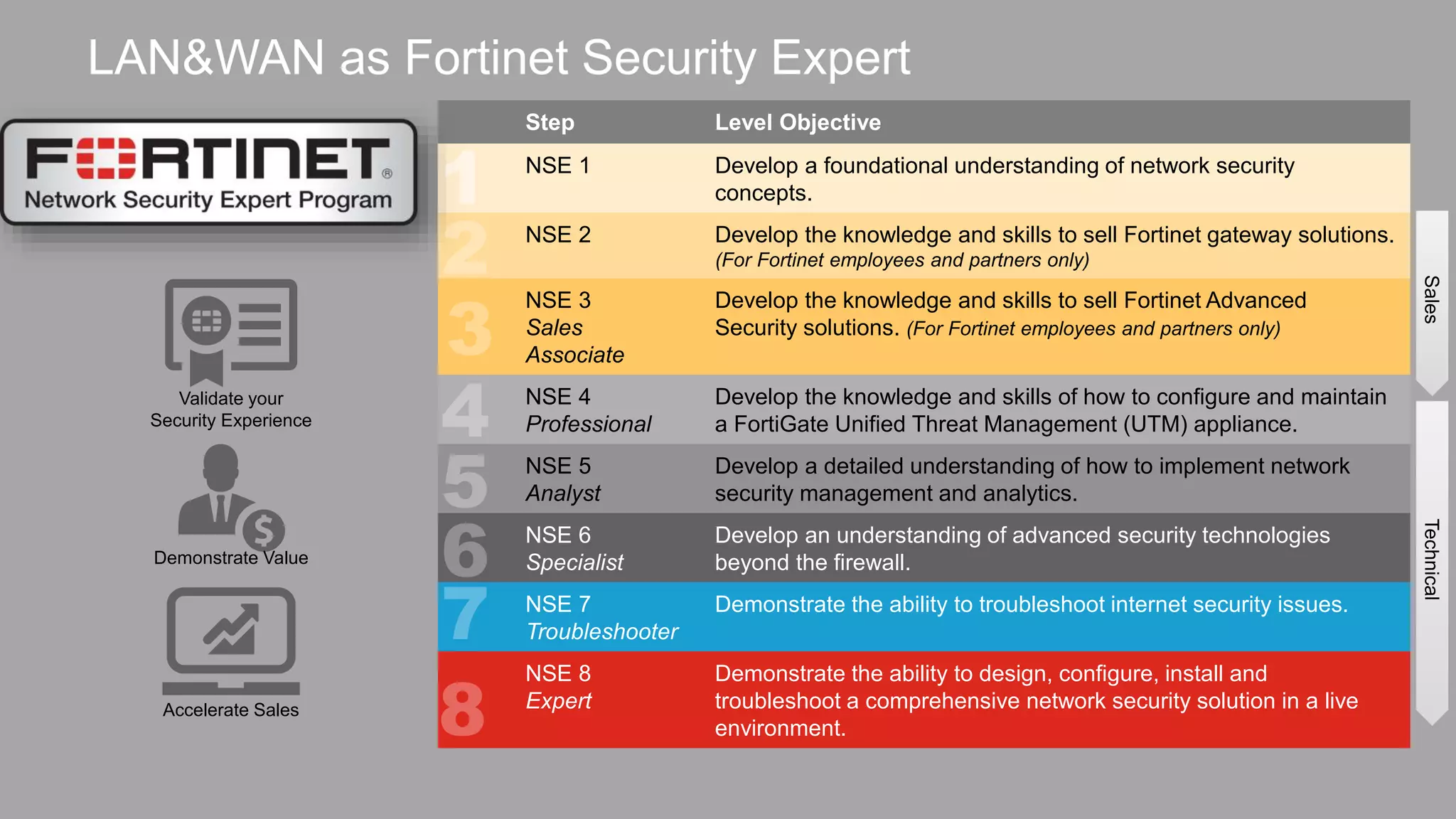
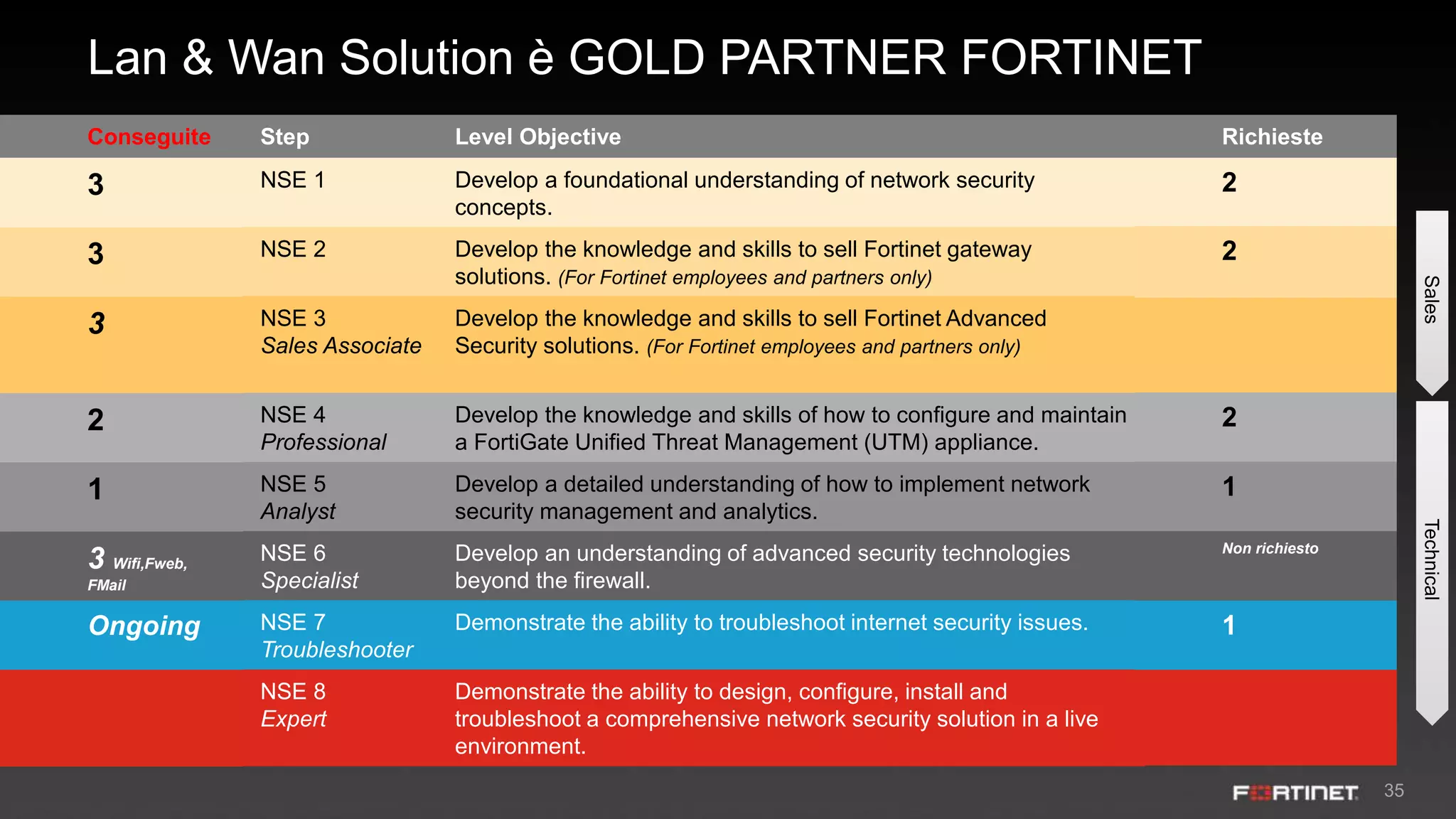
This document summarizes an event hosted by Lan & Wan Solutions and Fortinet Italy to discuss innovating businesses and network security. The agenda includes presentations on Fortinet's security solutions and a free cyber threat assessment program. It promotes Fortinet's integrated security platform and threat intelligence from FortiGuard Labs. The event also includes a network assessment report and lunch at the Zonin winery.