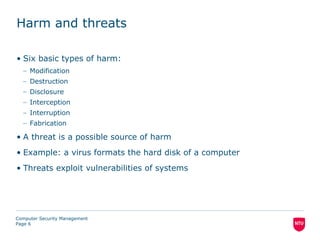
This document summarizes a lecture on computer security threats and vulnerabilities. It defines harm, threats, and vulnerabilities, and outlines six basic types of harm: modification, destruction, disclosure, interception, interruption, and fabrication. It also discusses common vulnerabilities like password flaws, software bugs, and social engineering. Finally, it notes that defenses against threats aim to satisfy security requirements through encryption, software controls, and physical/hardware controls.