This lecture discusses access control and permissions in Windows systems. It covers the structure and use of registry keys, how permissions are applied to registry entries and shares, and differences between NTFS, share, and Active Directory permissions. It also discusses printer server topologies like locally attached printers versus printers connected to a print server. The lecture concludes with a brief overview of permissions in old and modern UNIX/Linux systems.
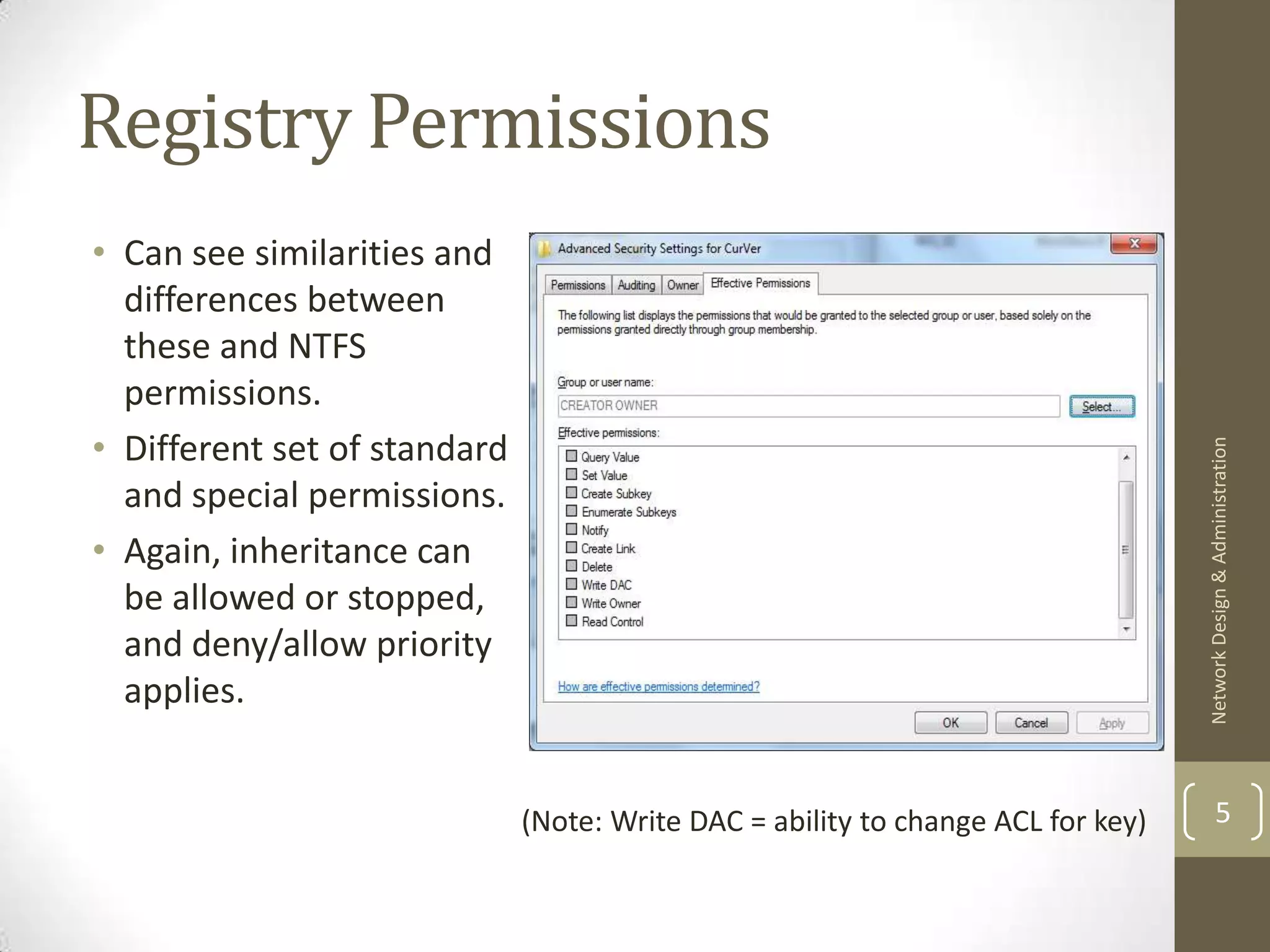
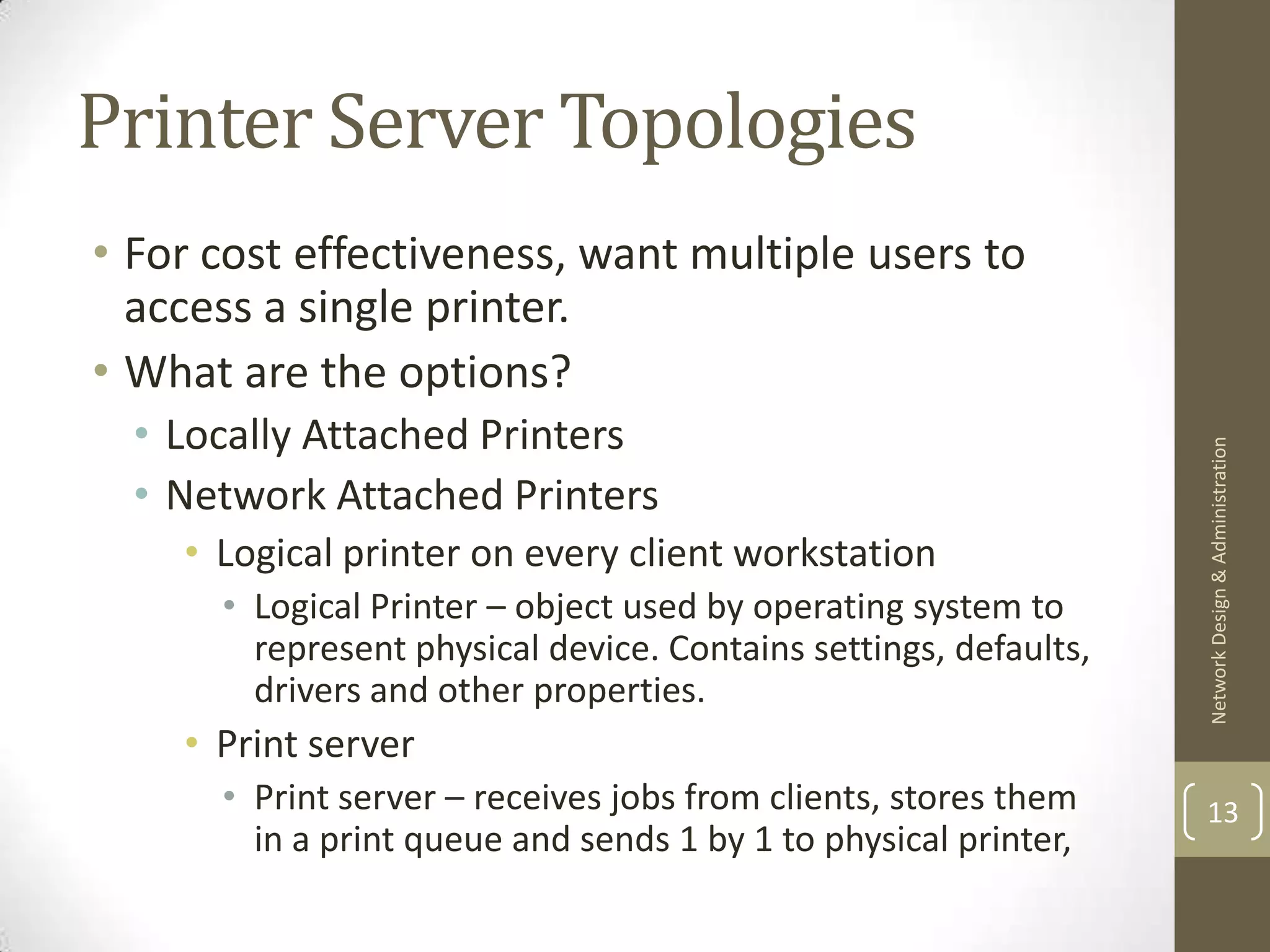
![Locally Attached Printer[1]
Network Design & Administration
• Physical security issues (printer has to be close to server).
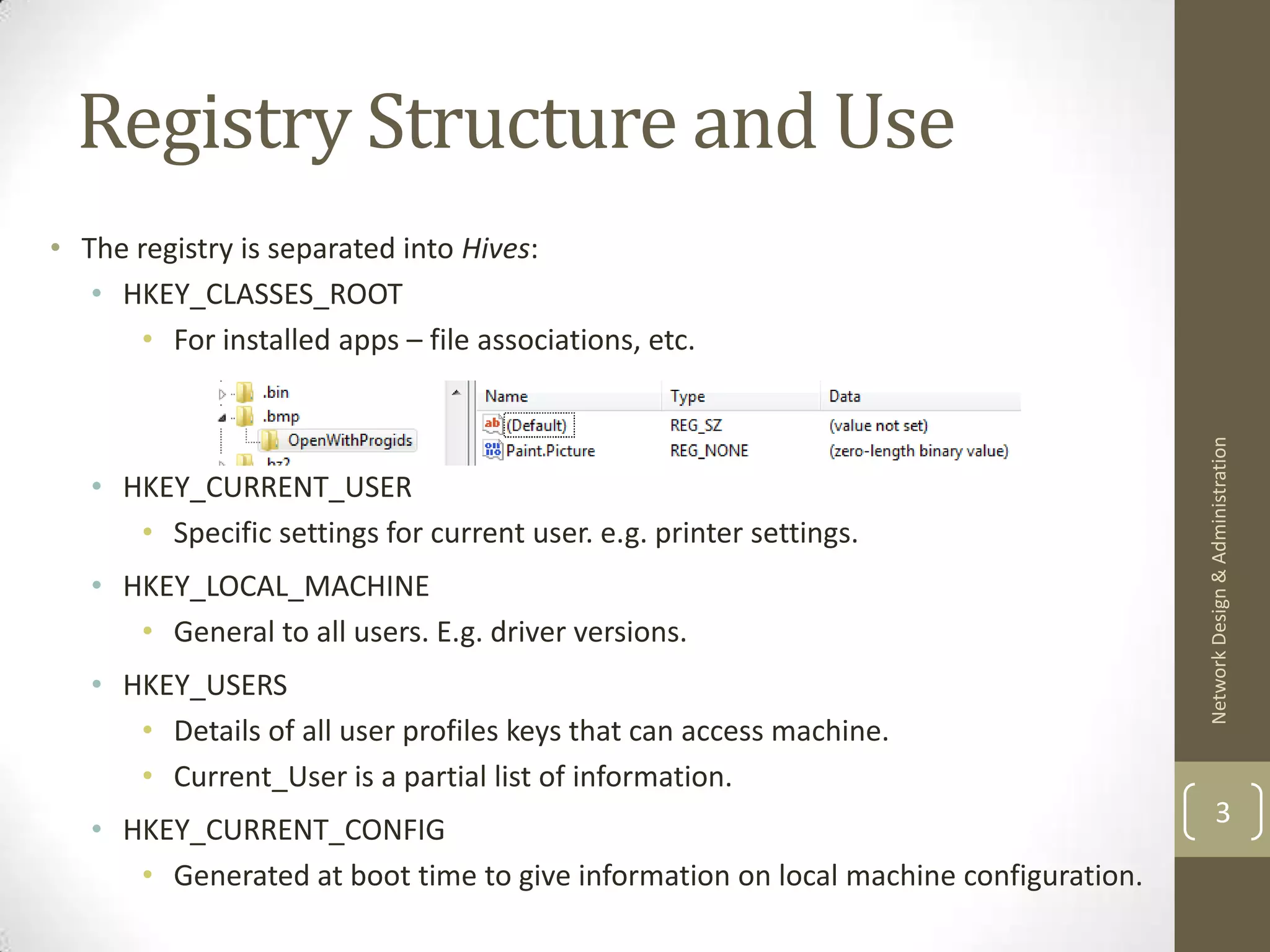
• When printer share is created the attached server functions as 14
the print server.](https://image.slidesharecdn.com/lecture9-furtherpermissions-130204184332-phpapp02/75/Lecture-9-further-permissions-14-2048.jpg)
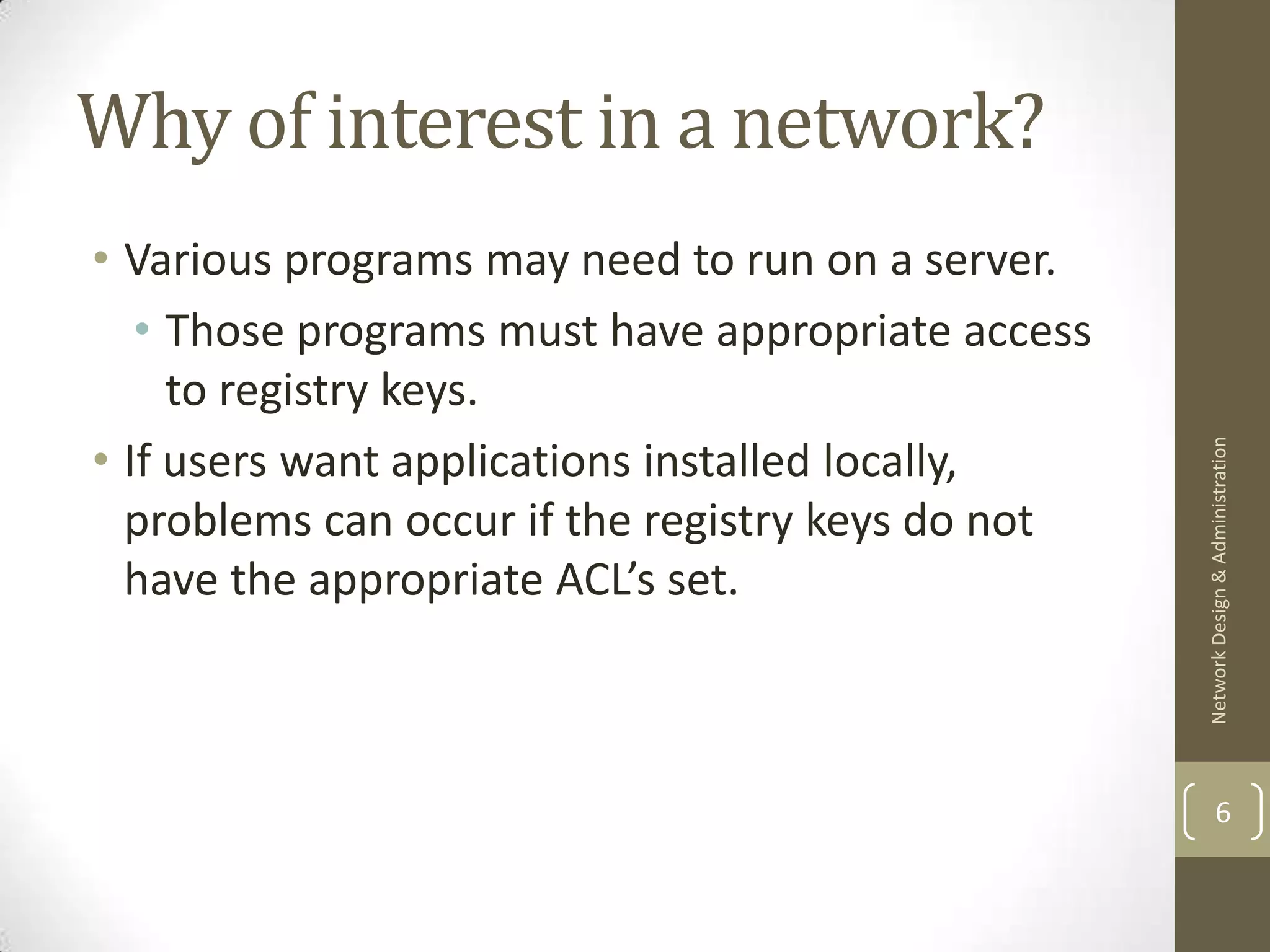
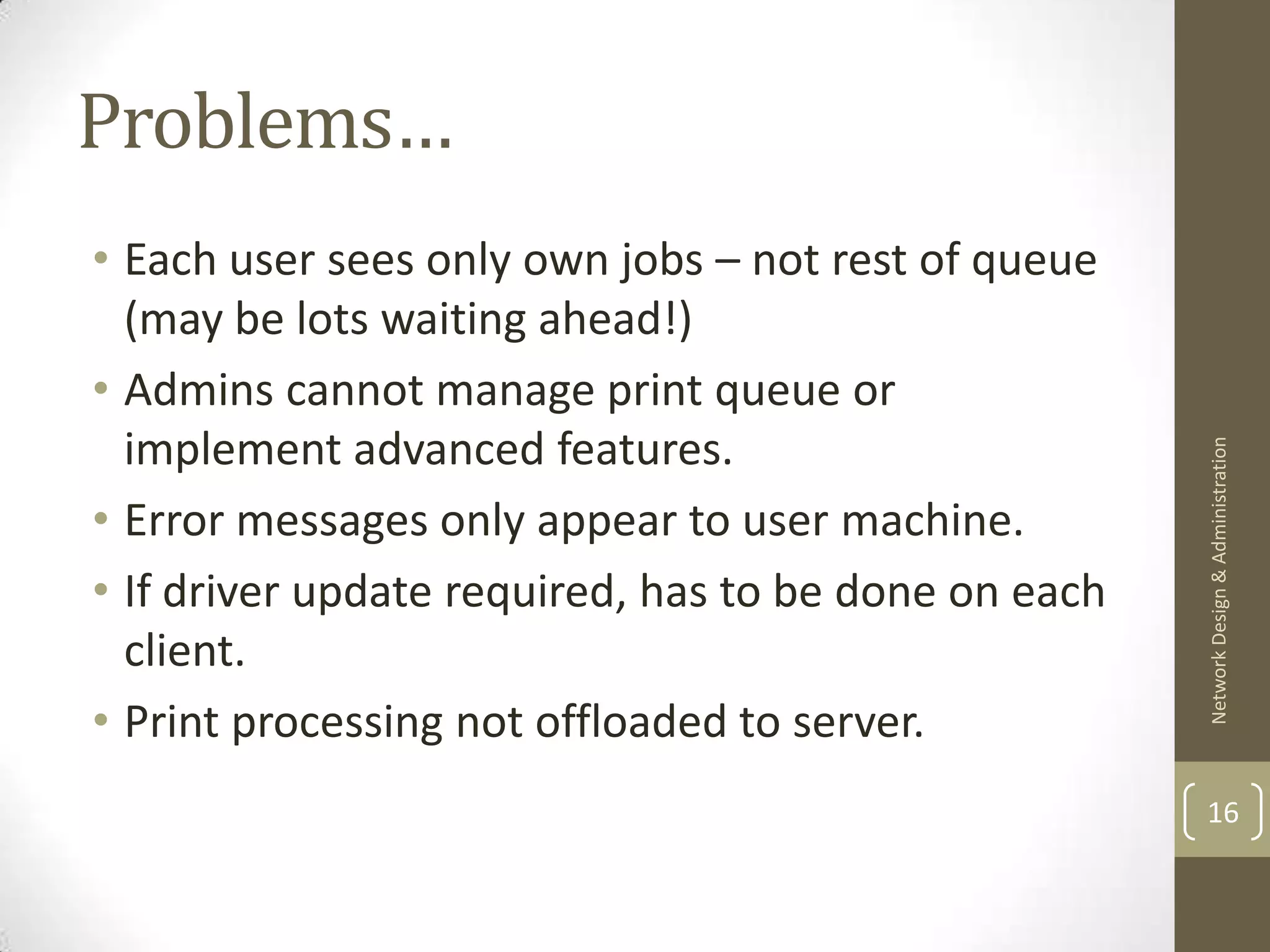
![Network attached printer, with
logical printer in every client[1]
Network Design & Administration
15](https://image.slidesharecdn.com/lecture9-furtherpermissions-130204184332-phpapp02/75/Lecture-9-further-permissions-15-2048.jpg)
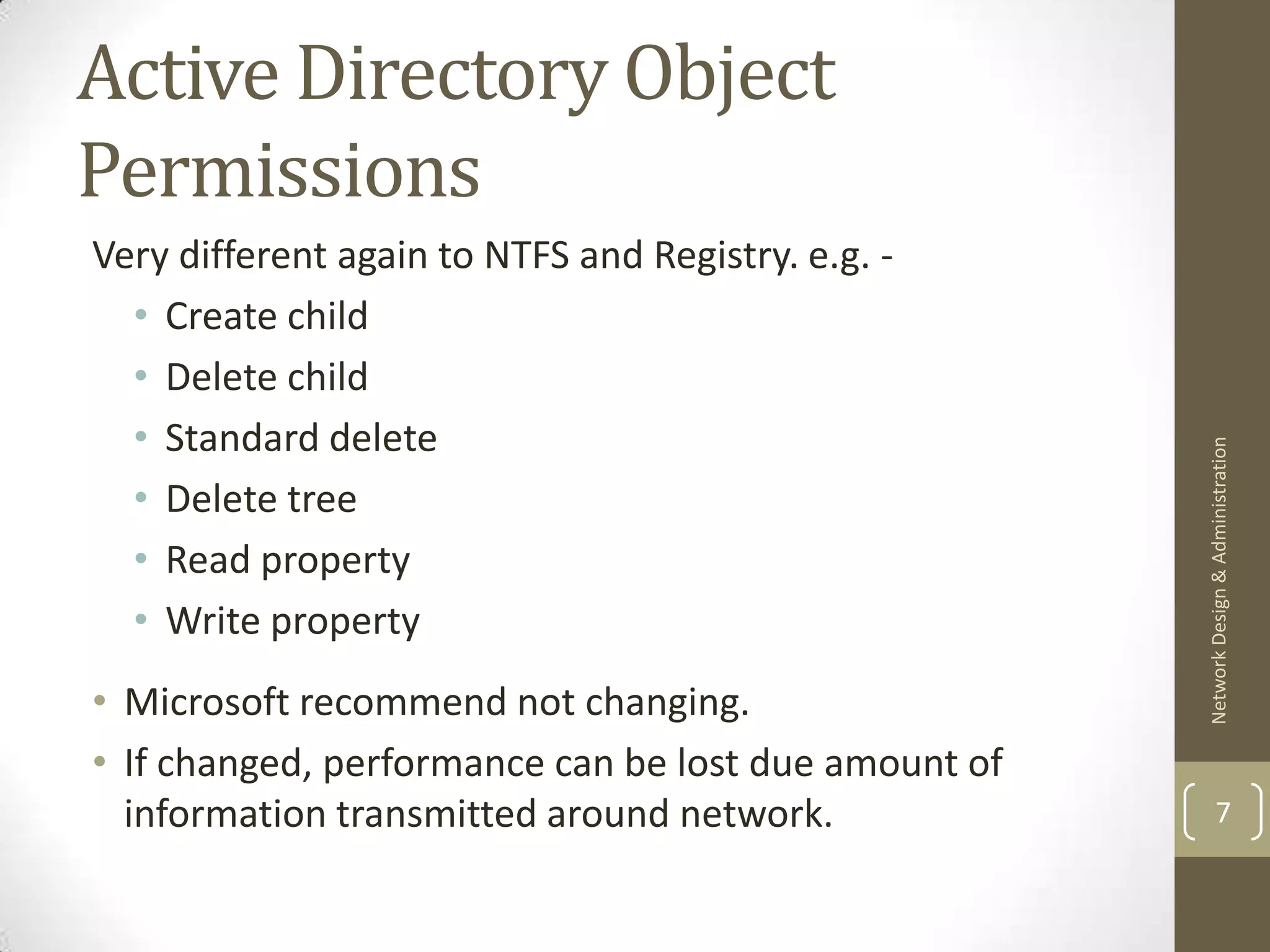
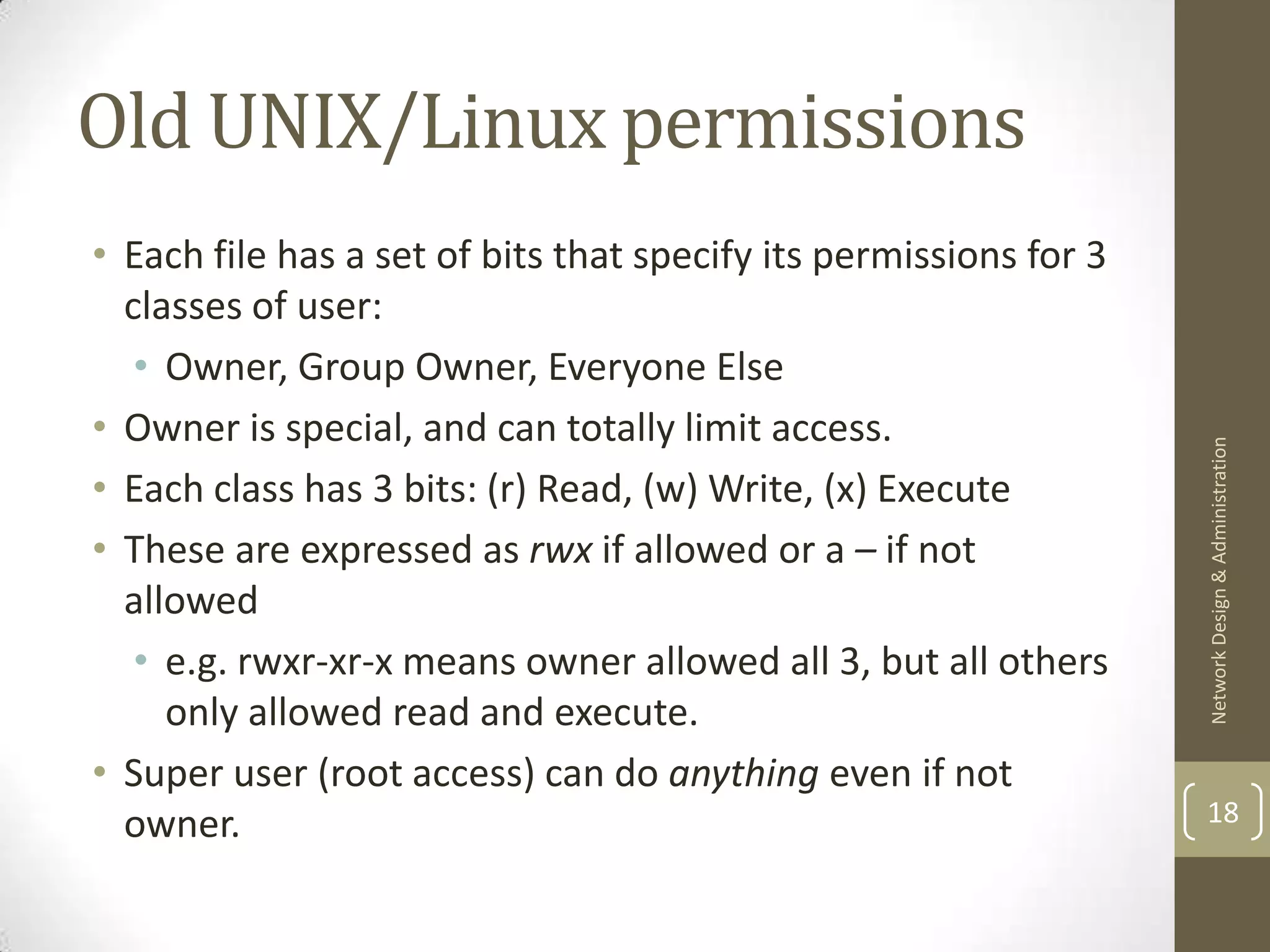
![Network attached printer, with
print server[1]
Network Design & Administration
17
• Advantages…?](https://image.slidesharecdn.com/lecture9-furtherpermissions-130204184332-phpapp02/75/Lecture-9-further-permissions-17-2048.jpg)
![Next Time & references
• Keeping systems up to date.
• Hotfixes vs. Service Packs.
• Managing/automating processes.
Network Design & Administration
• [1] MOAC 290 chapter 10
20](https://image.slidesharecdn.com/lecture9-furtherpermissions-130204184332-phpapp02/75/Lecture-9-further-permissions-20-2048.jpg)