This document provides an overview of network security concepts including:
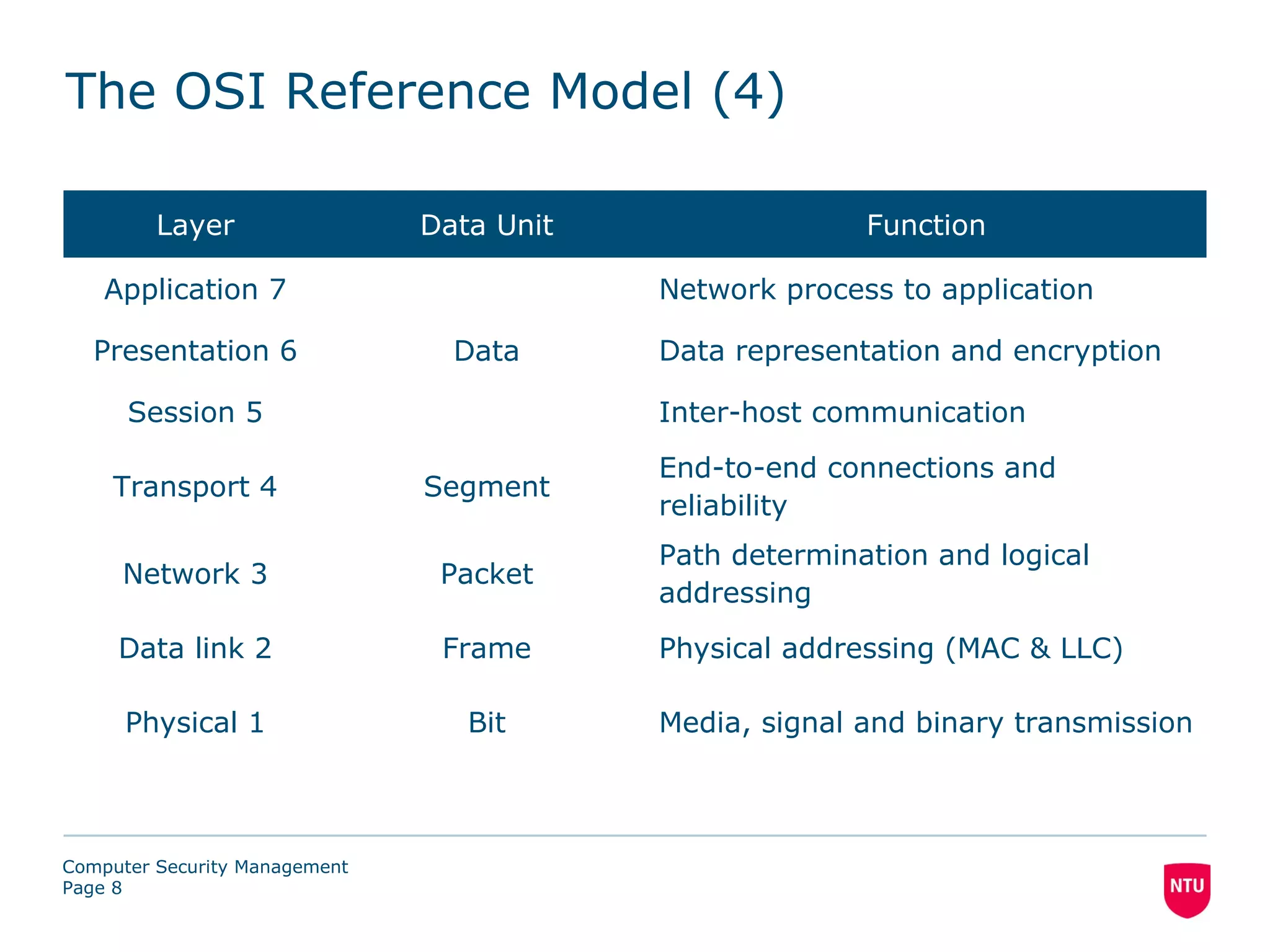
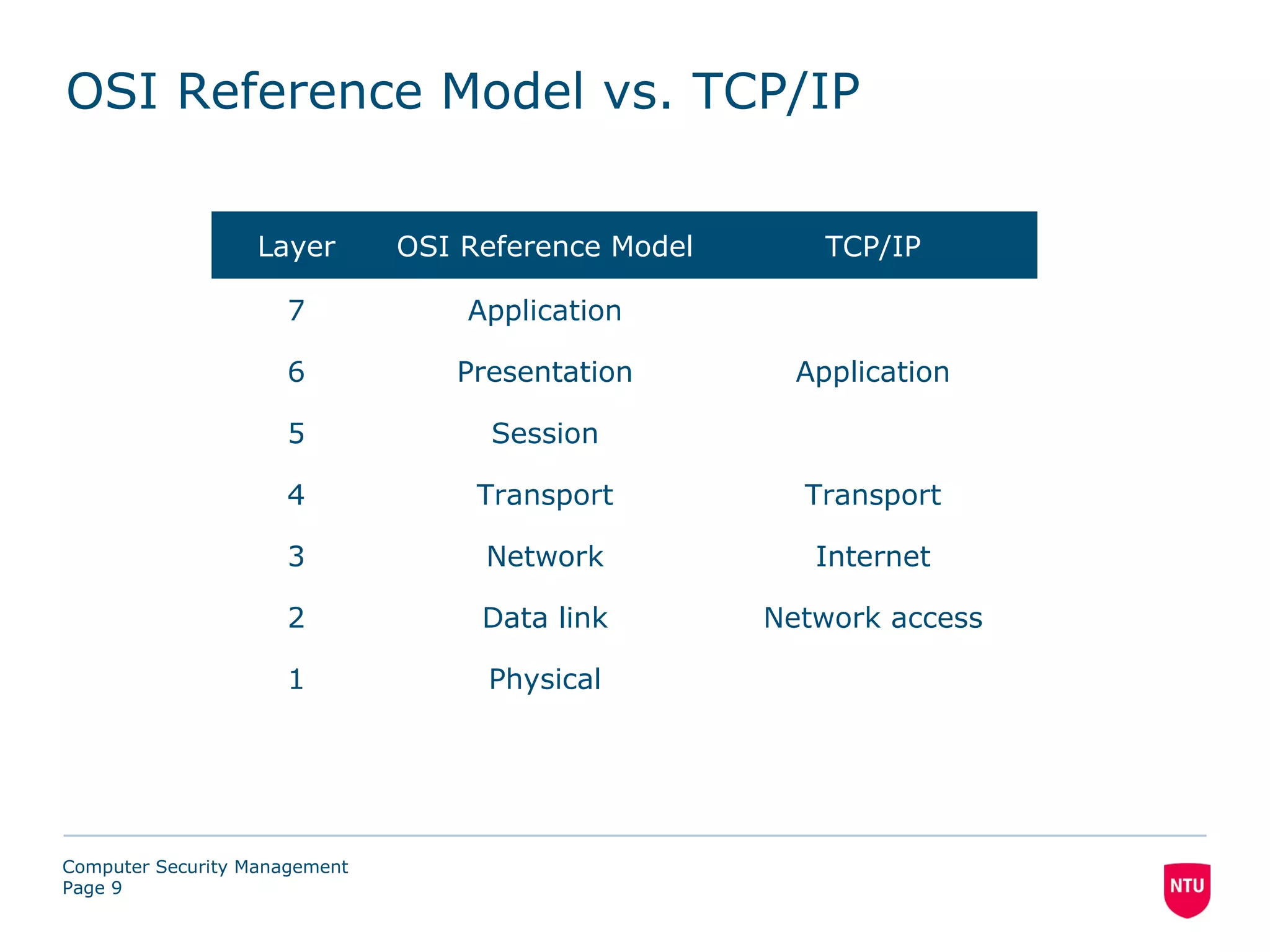
- The OSI reference model which defines 7 layers of network architecture.
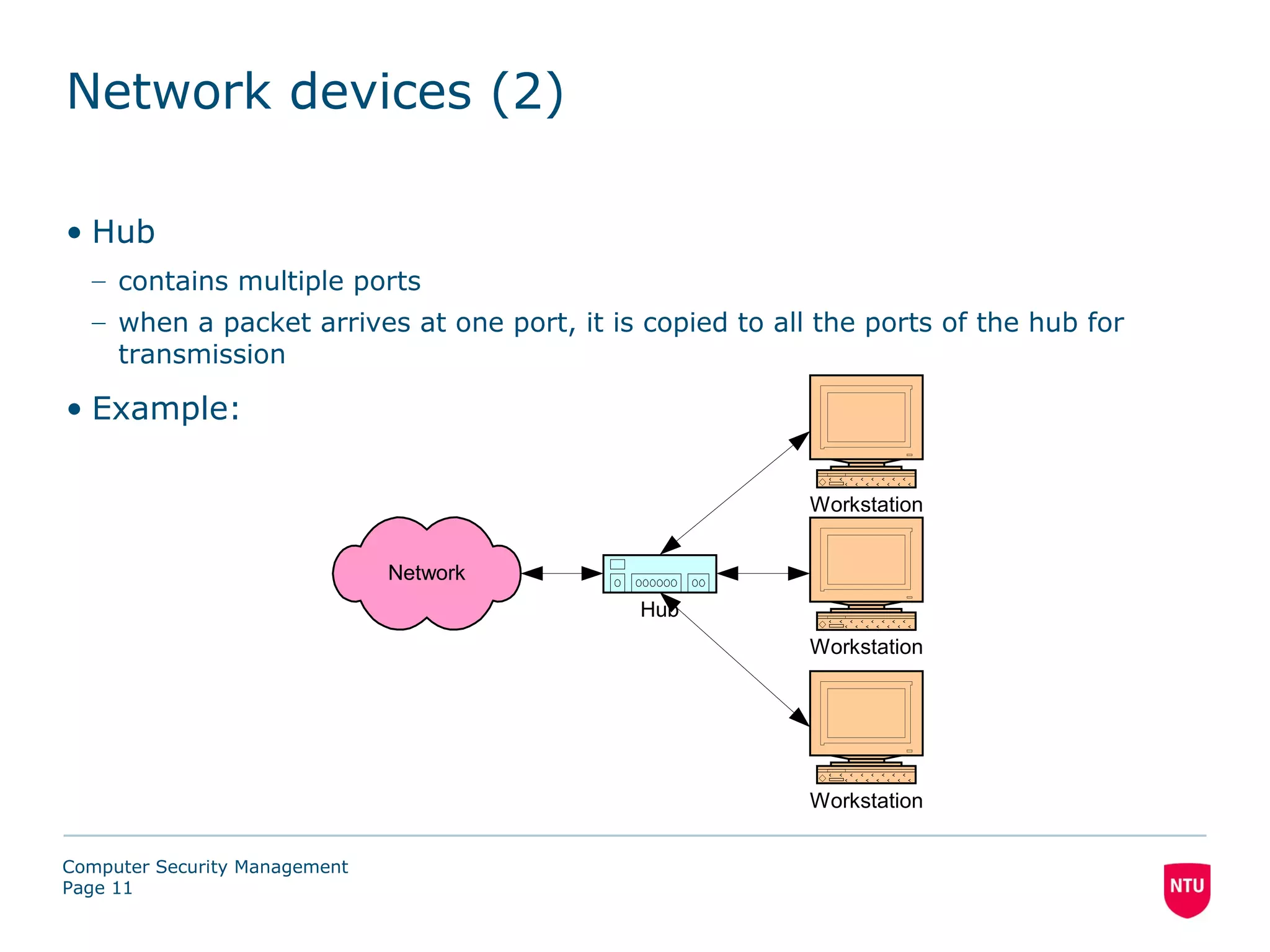
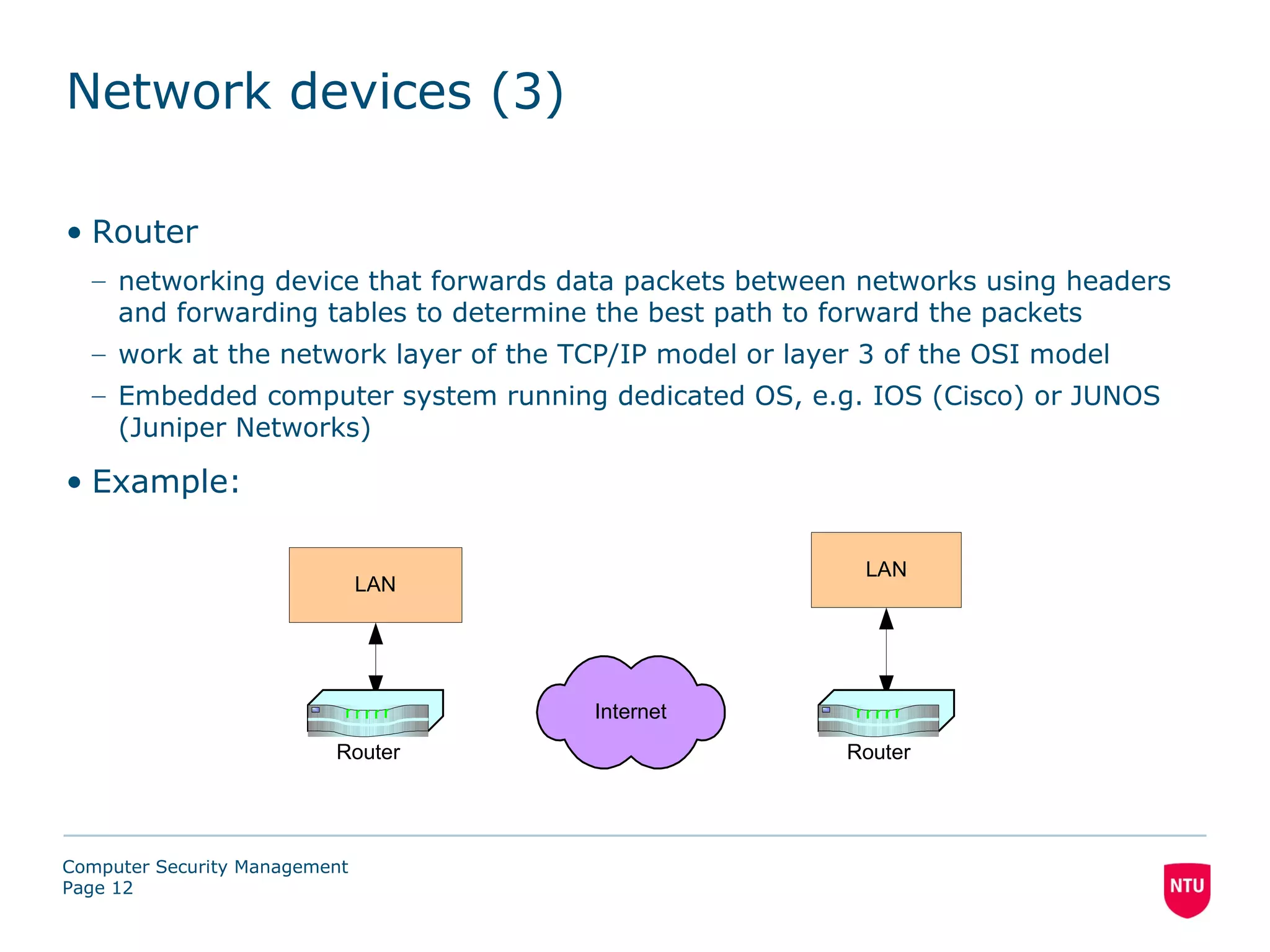
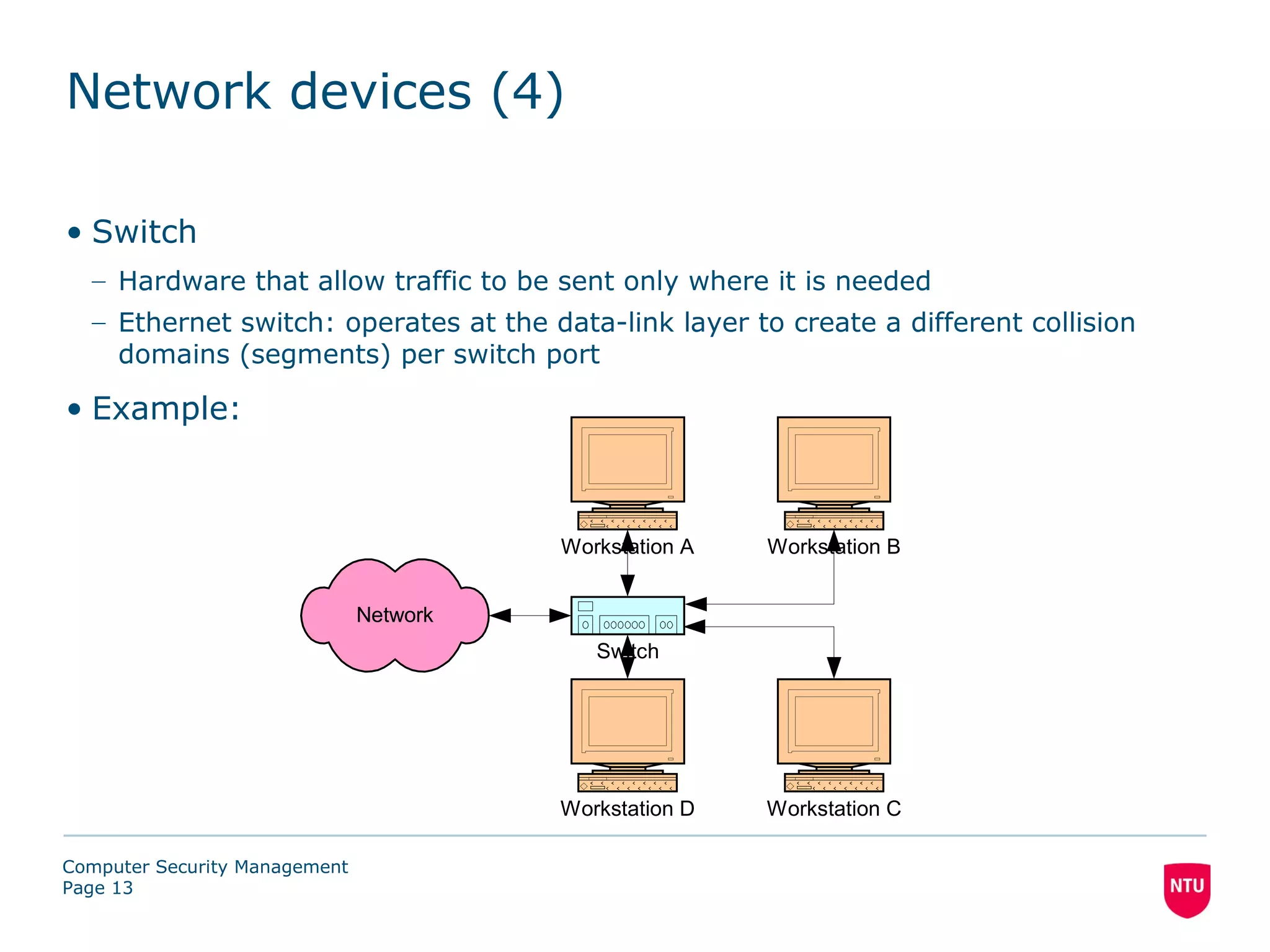
- Common network devices like switches, routers, and hubs.
- Reconnaissance and scanning phases that attackers use to identify vulnerabilities.
- Network-based attacks such as sniffing, spoofing, and denial-of-service attacks.
- Sniffing software and hardware that can intercept and analyze network traffic.