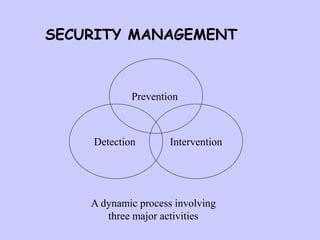
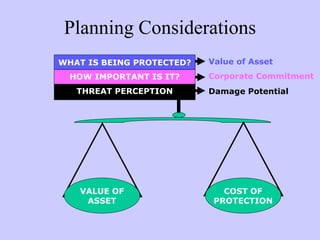
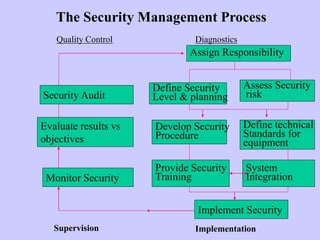
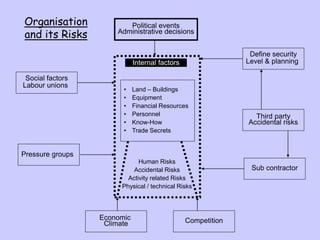
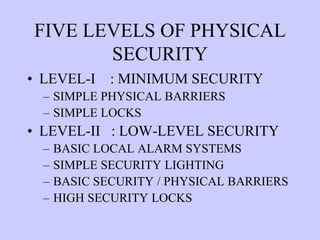
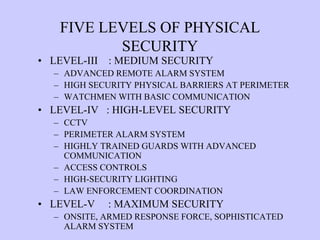
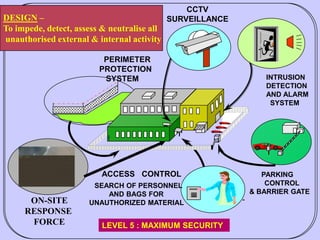
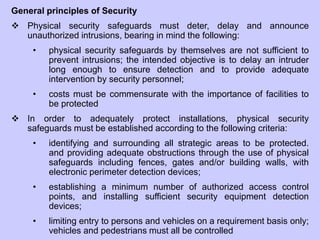
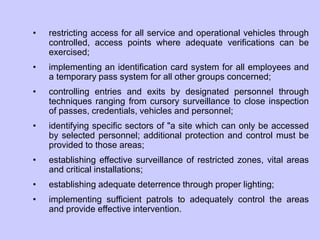
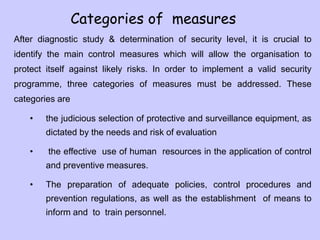
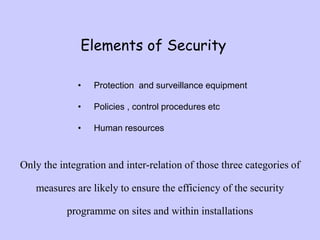
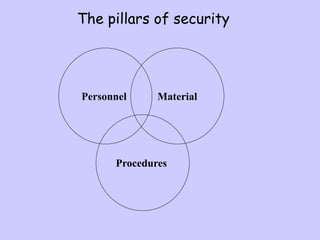
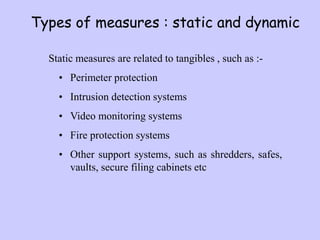
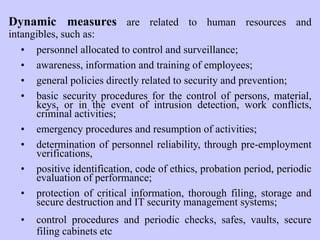
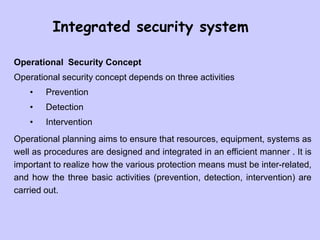
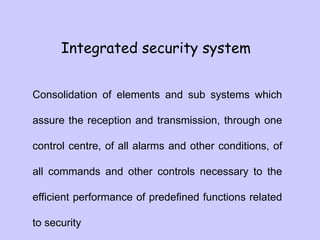
This document outlines important factors to consider when integrating security systems. It discusses that security demands are increasing due to the current global situation. Organizations need to determine the right security systems for their needs. The document then provides perspectives on security threats and considerations for planning security systems. It discusses prevention, detection, and intervention as the main activities in security management. Finally, it discusses integrated security systems and the methodological approach to planning security.