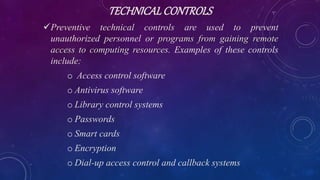
This document provides an overview of information security. It defines information security as protecting information systems, hardware, and data. It then describes different types of security including physical, personal, operations, communications, network, and information security. The document outlines several common threats to information systems such as unauthorized access, cyberespionage, malware, data leakage, mobile device attacks, social engineering, insiders, phishing, spam, and identity theft. It recommends various controls for protecting information systems, including data security plans, access controls, encryption, backups, and employee training.