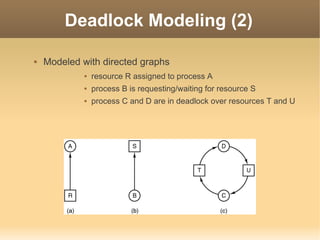
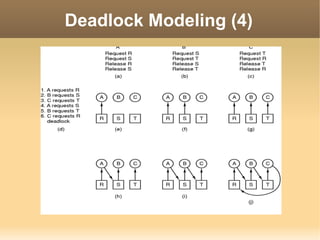
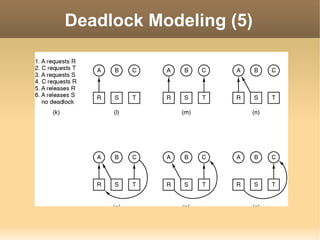
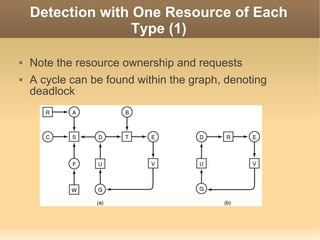
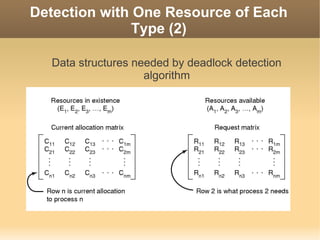
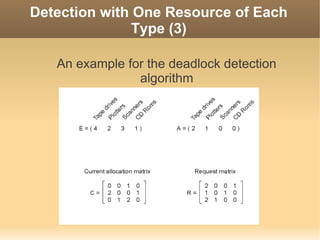
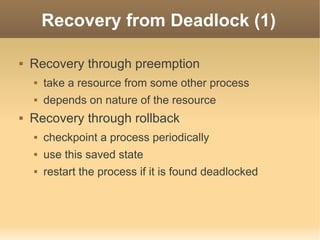
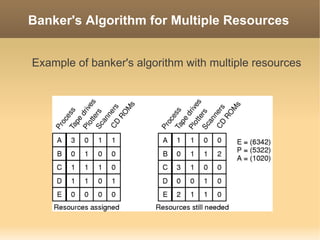
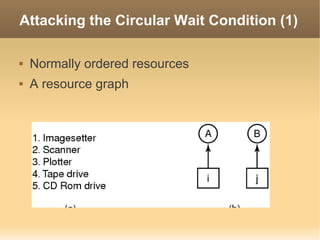
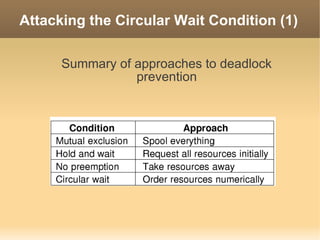
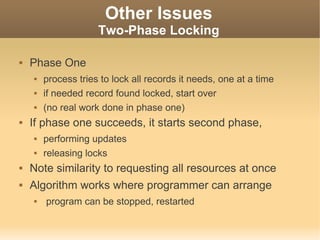
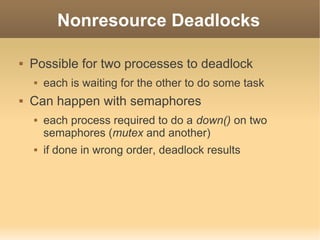
The document discusses deadlocks in operating systems. It defines deadlock and outlines the four conditions required for deadlock: mutual exclusion, hold and wait, no preemption, and circular wait. It then describes different strategies for handling deadlocks, including ignoring the problem, detection and recovery, avoidance through careful resource allocation, and prevention by negating one of the four conditions. Detection methods involve modeling resource allocation as a directed graph and searching for cycles. Prevention focuses on attacking the mutual exclusion, hold and wait, and circular wait conditions.