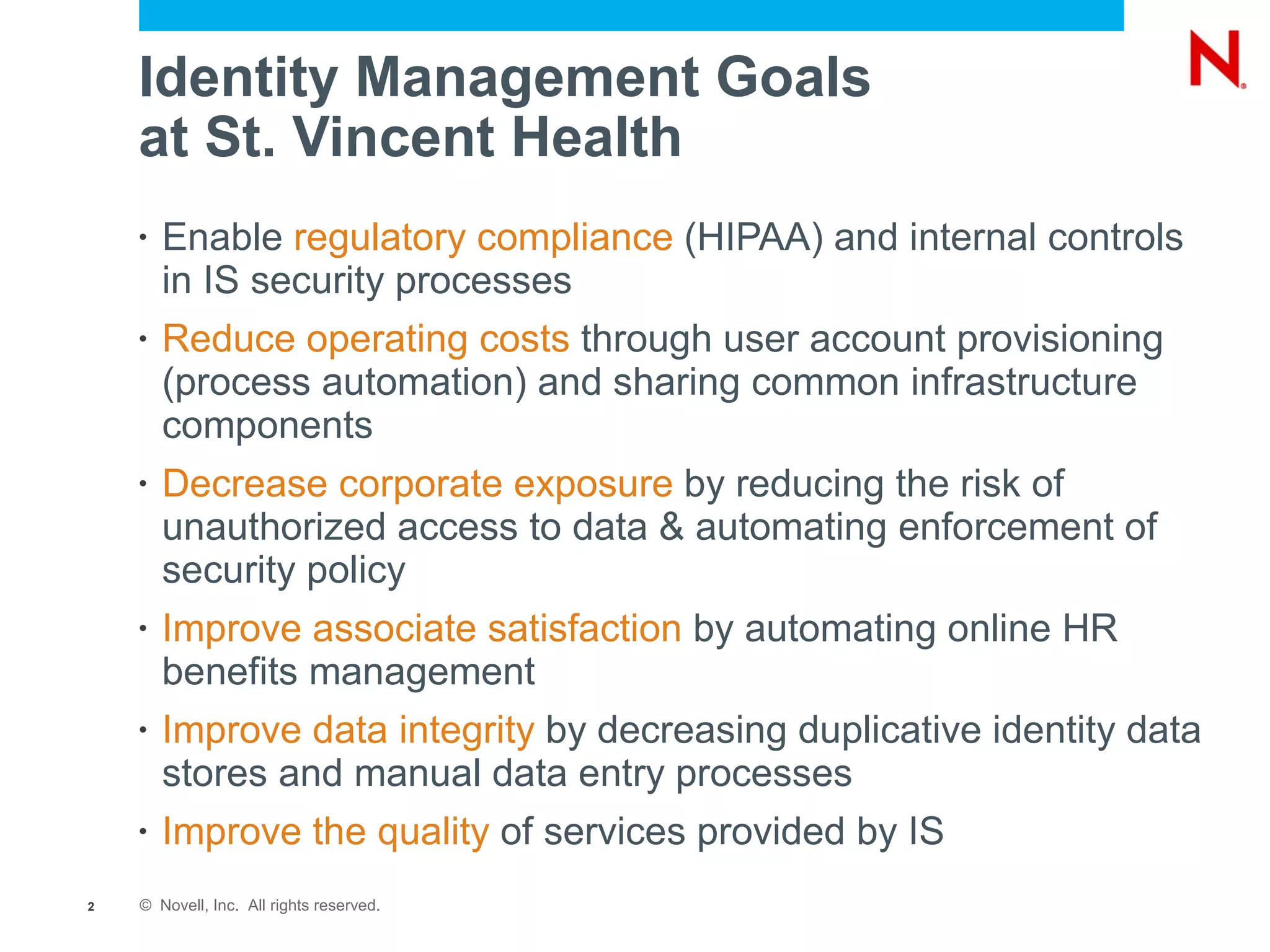
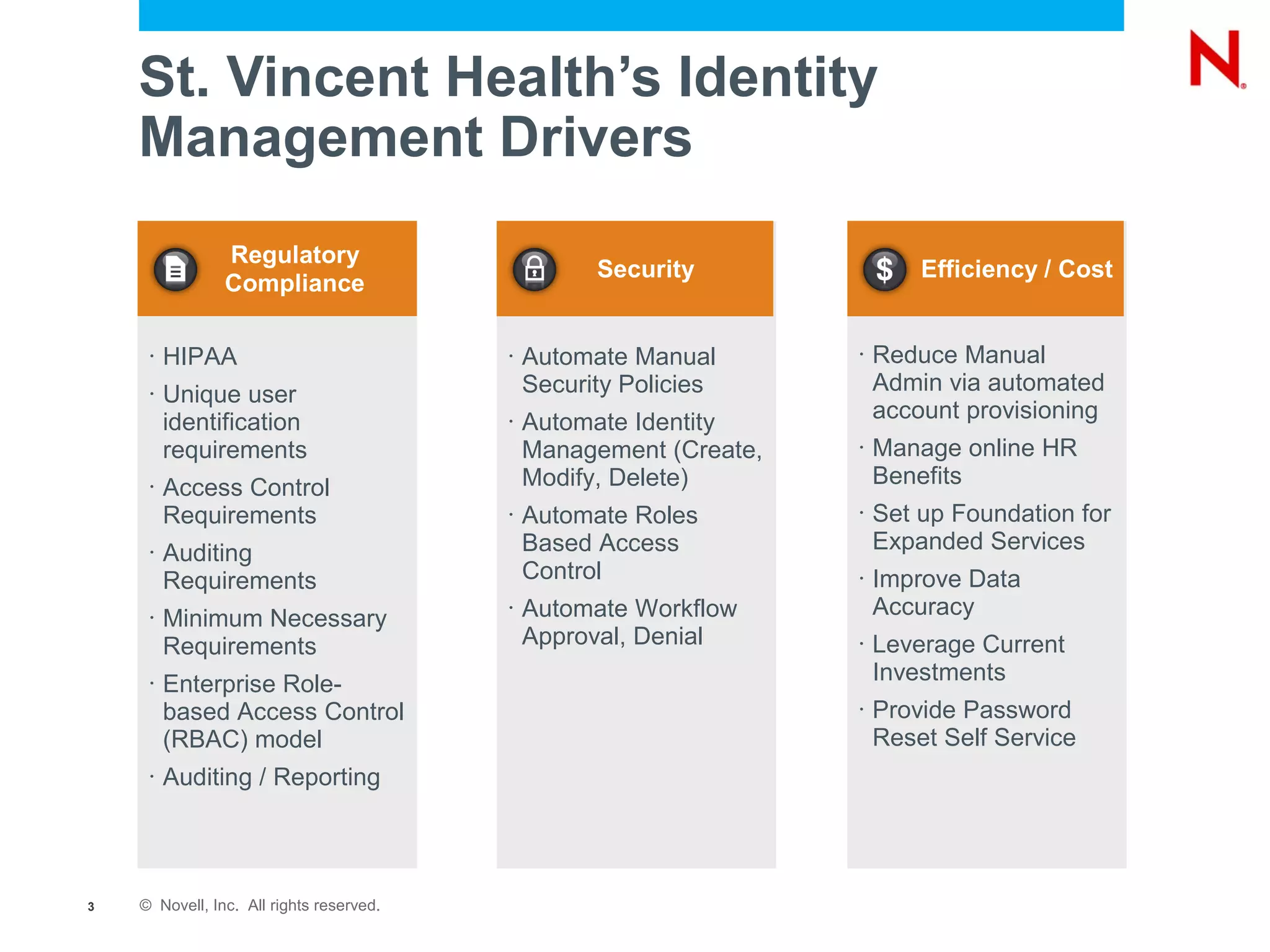
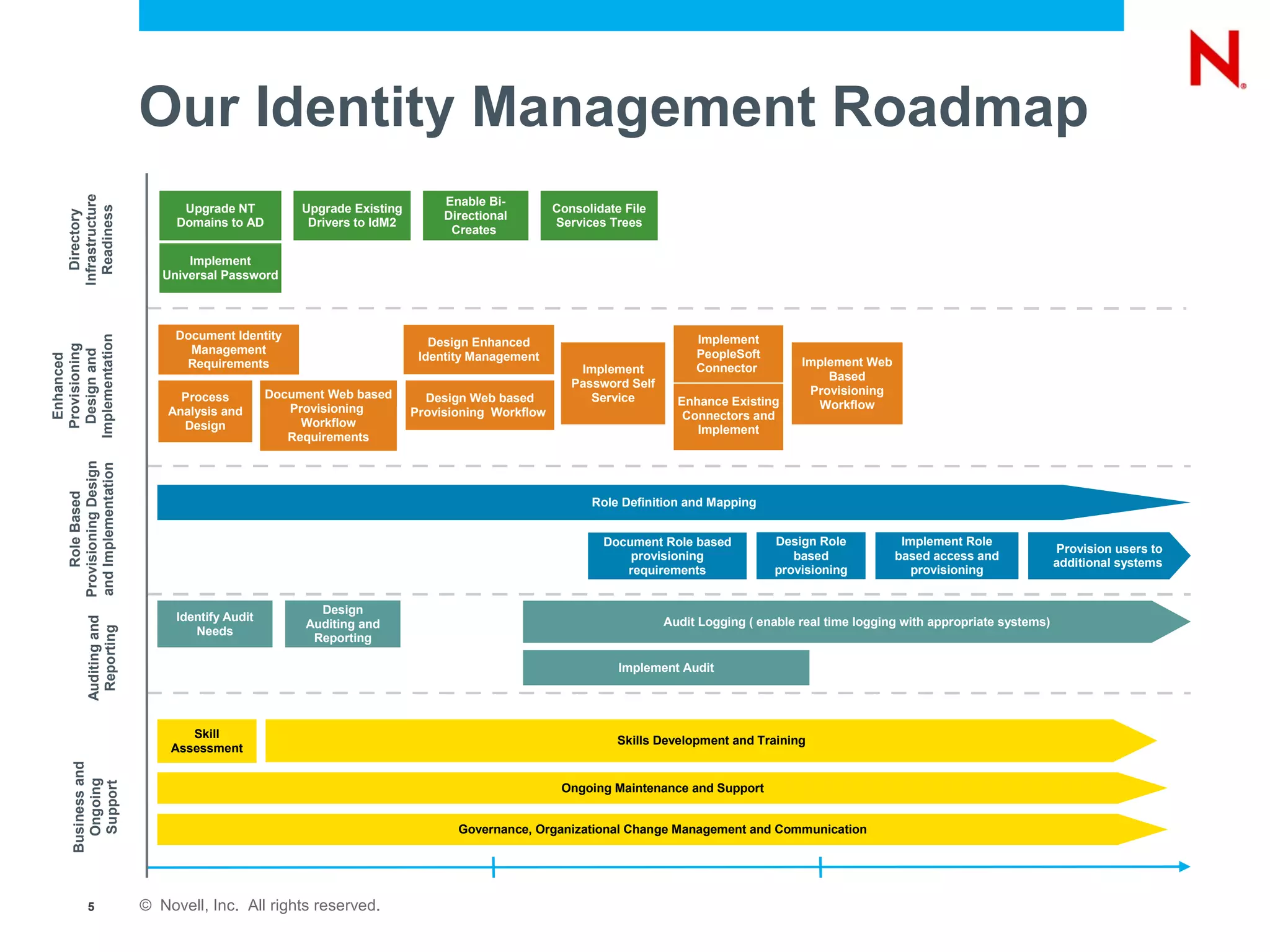
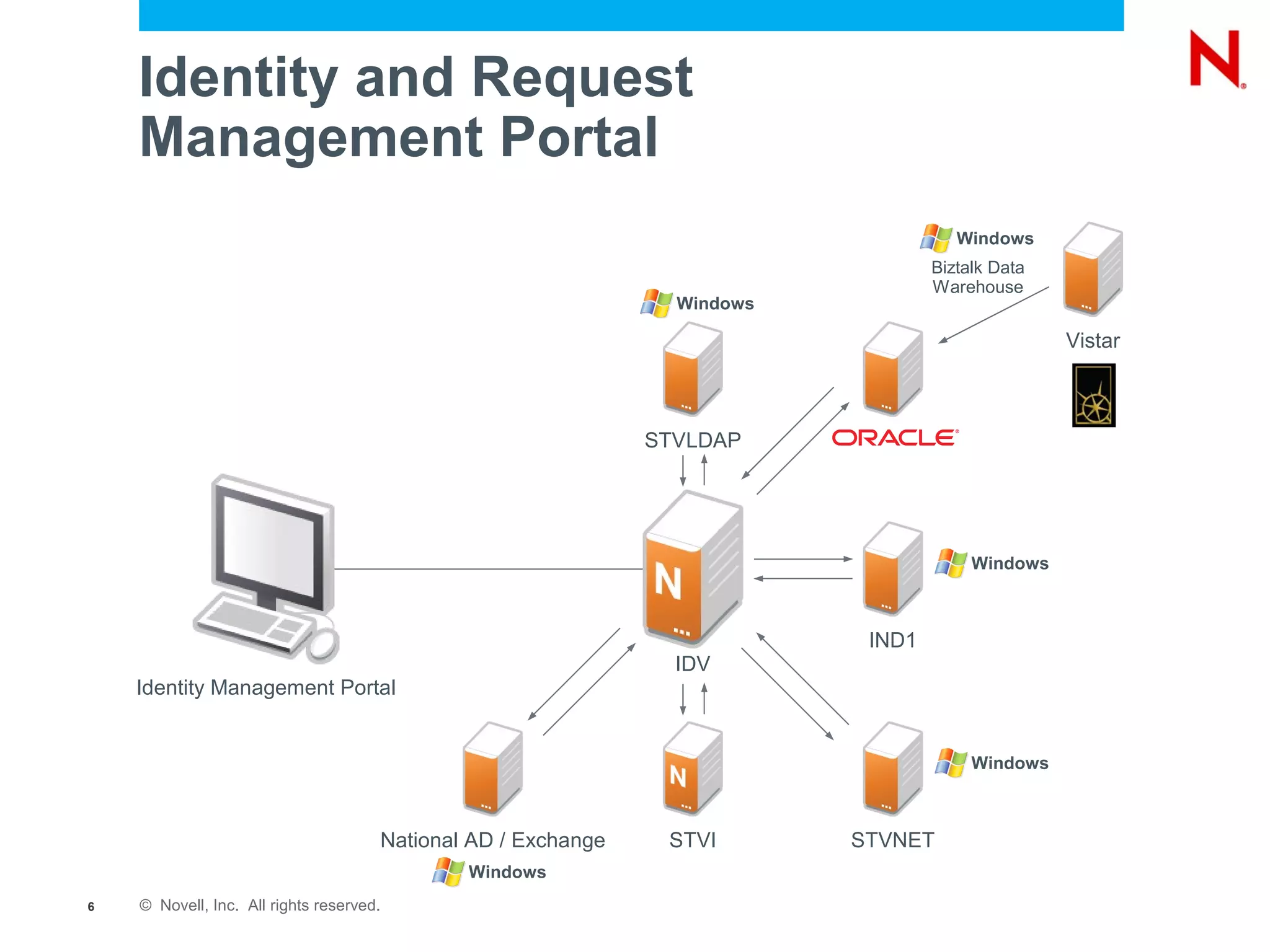
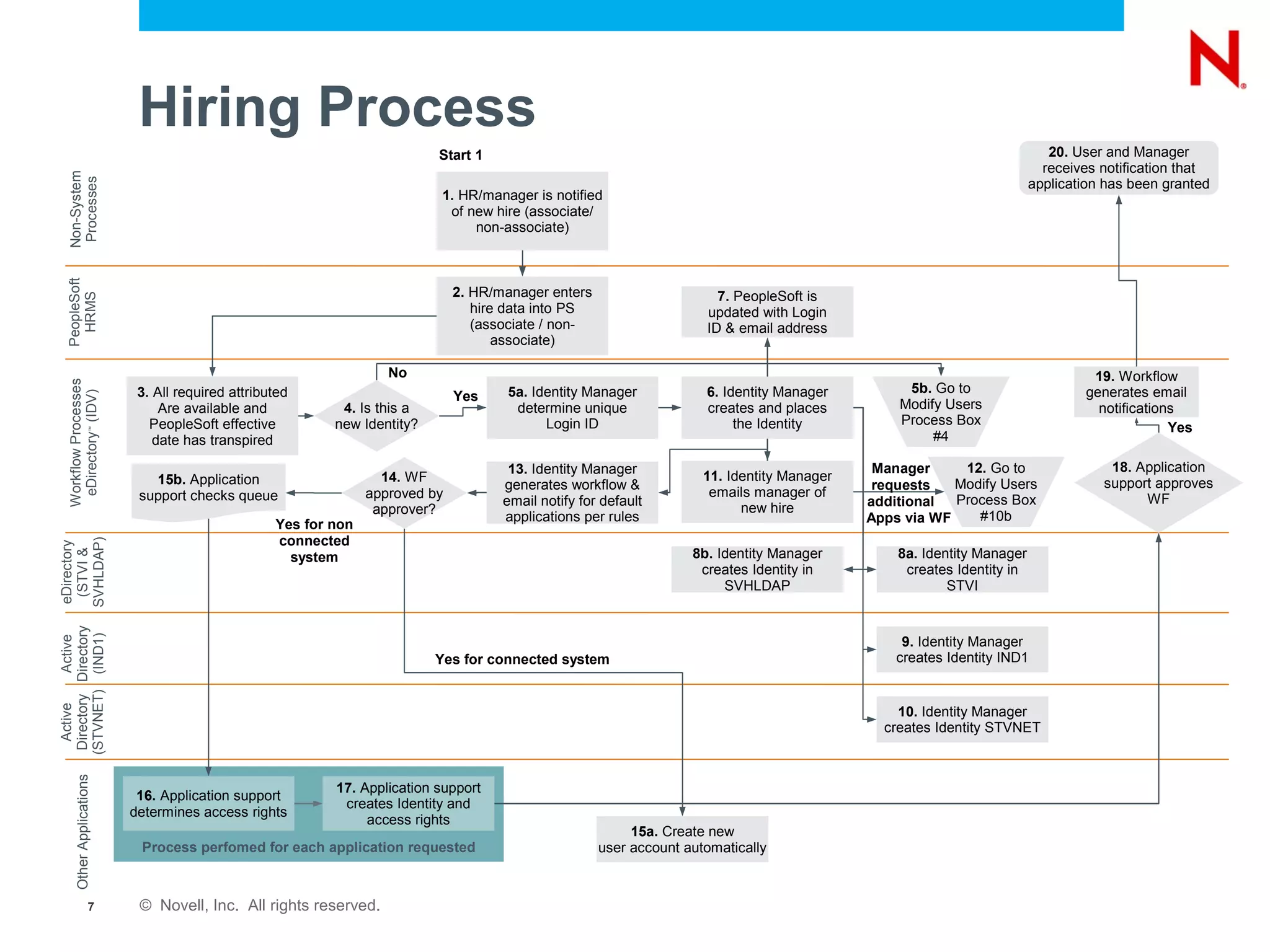
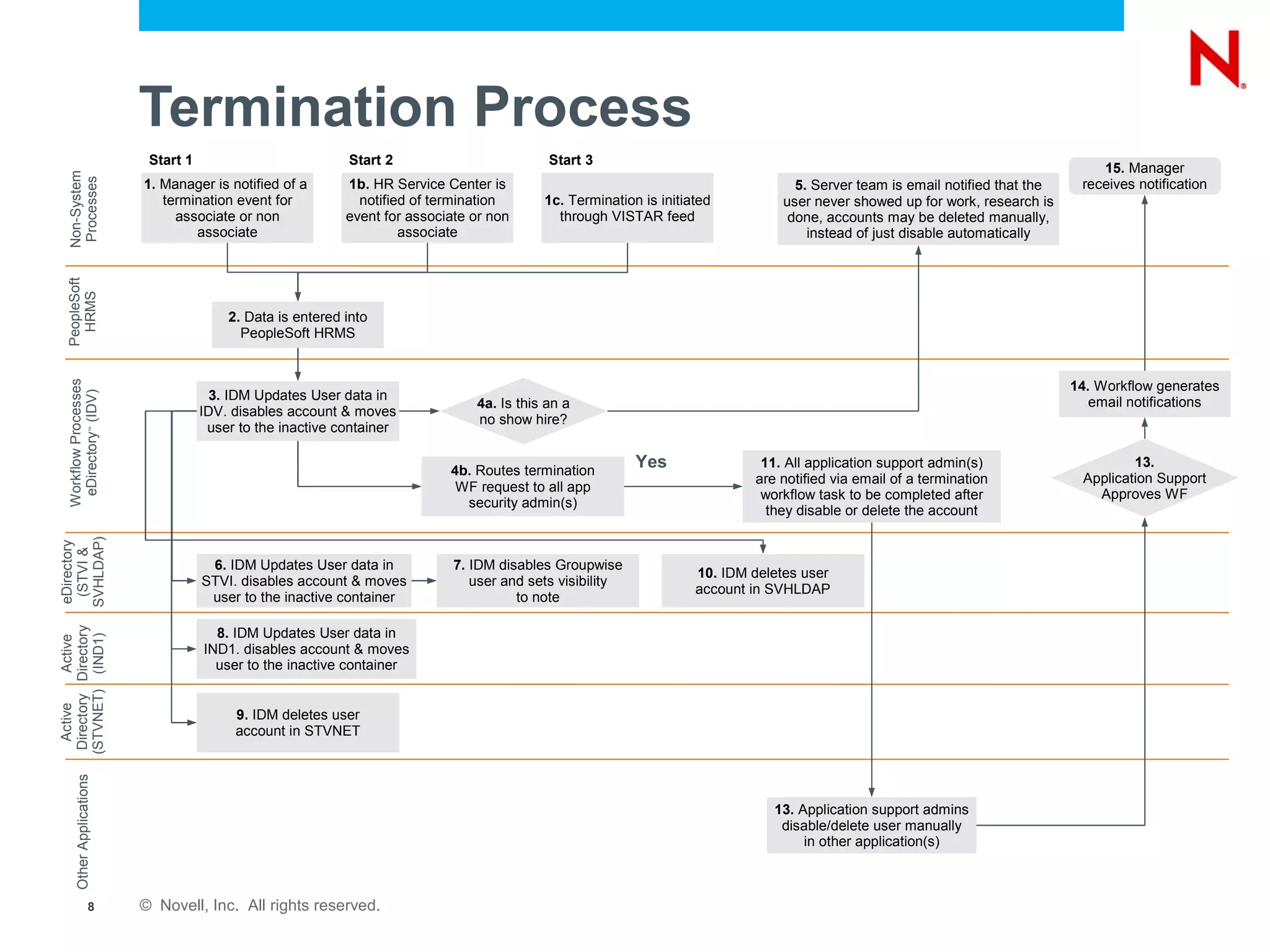
The document outlines the identity management goals and strategies of St. Vincent Health, primarily focused on regulatory compliance, cost reduction, and improving service quality through automation of identity processes. It details the organization's roadmap for implementing identity management solutions, including challenges faced, user management workflows, and lessons learned during the implementation process. The document emphasizes the importance of cooperation with human resources and the necessity for a thorough understanding of business processes to achieve successful identity management.