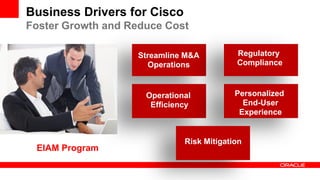
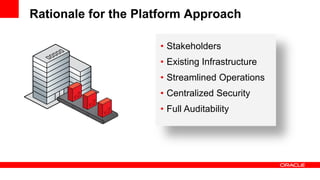
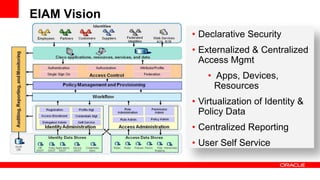
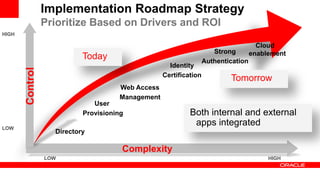
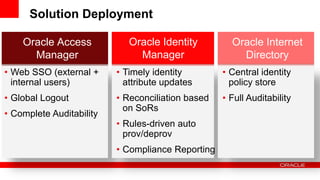
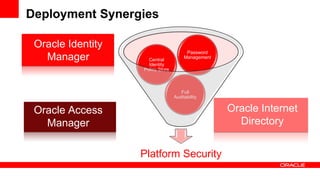
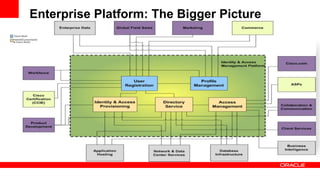
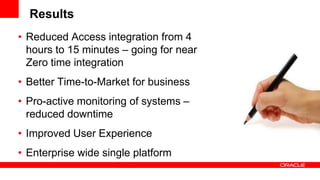
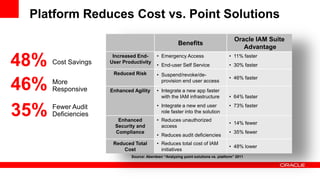
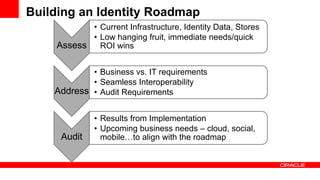
This document summarizes a presentation given by Ranjan Jain of Cisco and Michael Neuenschwander of Oracle about best practices for adopting a platform approach to identity and access management (IAM). The speakers discussed Cisco's business drivers for improving IAM, their rationale for choosing a platform over point solutions, and how they implemented Oracle's IAM products. They provided recommendations based on Cisco's experiences and highlighted potential benefits like cost savings and increased responsiveness compared to individual point solutions.