Fundamentals of Database Systems Questions and Answers
•
18 likes•23,356 views
Fundamentals of Database Systems questions and answers with explanation for fresher's and experienced for interview, competitive examination and entrance test.
Report
Share
Report
Share
Download to read offline
Recommended
Fundamentals of Database Systems Questions and Answers

Fundamentals of Database Systems questions and answers with explanation for fresher's and experienced for interview, competitive examination and entrance test.
DBMS Question bank

COMPUTER SCIENCE & ENGG. DBMS QUESTION PAPERS UNIT WISE ACCORDING TO GONDAWANA UNIVERSITY.
Recommended
Fundamentals of Database Systems Questions and Answers

Fundamentals of Database Systems questions and answers with explanation for fresher's and experienced for interview, competitive examination and entrance test.
DBMS Question bank

COMPUTER SCIENCE & ENGG. DBMS QUESTION PAPERS UNIT WISE ACCORDING TO GONDAWANA UNIVERSITY.
Fragmentation and types of fragmentation in Distributed Database

Definition,
Characteristics of Fragmentation,
Horizontal Fragmentation,
Vertical Fragmentation,
Mixed Fragmentation.,
Types of Horizontal fragmentation,
Primary Horizontal Fragmentation,
Derived horizontal fragmentation,
Complete horizontal fragmentation,
Disjoint horizontal fragmentation,
Reconstruction of original relation,
Complete vertical fragmentation,
Fragmentation aims to improve...
Dbms Introduction and Basics

In this Presentation you will be able to learn Basic of dbms with definitions and trends in dbms.
Data Redundancy & Update Anomalies

DBMS's one of the important topic "Data Redundancy & Update Anomalies" is describe here very nicely.
Data models

● Data Modeling and Data Models.
● Business Rules (Translating Business Rules into Data Model Components).
● Emerging Data Models: Big Data and NoSQL.
● Degrees of Data Abstraction (External, Conceptual, Internal and Physical model).
Data Models

Introduction of Data Models,Comparison between hierarchical ,network and relational model
Distributed database management system

DDBMS, characteristics, Centralized vs. Distributed Database, Homogeneous DDBMS, Heterogeneous DDBMS, Advantages, Disadvantages, What is parallel database, Data fragmentation, Replication, Distribution Transaction
Distributed dbms architectures

Distributed DBMS Architectures, Client - Server Architecture for DDBMS,Peer- to-Peer Architecture for DDBMS, Multi - DBMS Architectures
Deductive databases

A presentation on a special category of databases called Deductive Databases. It is an attempt to merge logic programming with relational database. Other types include Object-oriented databases, Graph databases, XML databases, Multi-model databases, etc.
More Related Content
What's hot
Fragmentation and types of fragmentation in Distributed Database

Definition,
Characteristics of Fragmentation,
Horizontal Fragmentation,
Vertical Fragmentation,
Mixed Fragmentation.,
Types of Horizontal fragmentation,
Primary Horizontal Fragmentation,
Derived horizontal fragmentation,
Complete horizontal fragmentation,
Disjoint horizontal fragmentation,
Reconstruction of original relation,
Complete vertical fragmentation,
Fragmentation aims to improve...
Dbms Introduction and Basics

In this Presentation you will be able to learn Basic of dbms with definitions and trends in dbms.
Data Redundancy & Update Anomalies

DBMS's one of the important topic "Data Redundancy & Update Anomalies" is describe here very nicely.
Data models

● Data Modeling and Data Models.
● Business Rules (Translating Business Rules into Data Model Components).
● Emerging Data Models: Big Data and NoSQL.
● Degrees of Data Abstraction (External, Conceptual, Internal and Physical model).
Data Models

Introduction of Data Models,Comparison between hierarchical ,network and relational model
Distributed database management system

DDBMS, characteristics, Centralized vs. Distributed Database, Homogeneous DDBMS, Heterogeneous DDBMS, Advantages, Disadvantages, What is parallel database, Data fragmentation, Replication, Distribution Transaction
Distributed dbms architectures

Distributed DBMS Architectures, Client - Server Architecture for DDBMS,Peer- to-Peer Architecture for DDBMS, Multi - DBMS Architectures
Deductive databases

A presentation on a special category of databases called Deductive Databases. It is an attempt to merge logic programming with relational database. Other types include Object-oriented databases, Graph databases, XML databases, Multi-model databases, etc.
What's hot (20)
Fragmentation and types of fragmentation in Distributed Database

Fragmentation and types of fragmentation in Distributed Database
Previous question papers of Database Management System (DBMS) By SHABEEB

Previous question papers of Database Management System (DBMS) By SHABEEB
Viewers also liked
Ch 17 disk storage, basic files structure, and hashing

Modified version of Chapter 17 of the book Fundamentals_of_Database_Systems,_6th_Edition with review questions
as part of database management system course
Int306 03

Data Models, Object Oriented, Object Relational, Relational, Network Model, Hierarchical Model, Relational Query languages, relational Algebra, Tuple Calculus, Domain Calculus
Int306 01

DBMS - Introduction, DBMS Applications, Database system architecture, dbms components, database users,
Computer math

Overview of computer math and numbers targeted at middle and high school. Covers computer use of numbers including binary numbers, a flip-flop, exponents. A few binary number games and projects are included.
Viewers also liked (20)
2009 Punjab Technical University B.C.A Database Management System Question paper

2009 Punjab Technical University B.C.A Database Management System Question paper
Chapter 1 Fundamentals of Database Management System

Chapter 1 Fundamentals of Database Management System
Ch 17 disk storage, basic files structure, and hashing

Ch 17 disk storage, basic files structure, and hashing
Similar to Fundamentals of Database Systems Questions and Answers
Identity Resolution across Different Social Networks using Similarity Analysis

Today the Social Networking Sites have become very popular and are used by most of the people. This is because the Social Networking sites are playing different roles in different fields and facilitating the needs of its users from time to time. The most common purpose why people join in to these websites is to get connected with people and sharing information. An individual may be signed in on more than one Social Networking Site so identifying the same individual on different Social Networking sites is a task. To accomplish this task the proposed system uses the Similarity Analysis method on the available information details.
Social Friend Overlying Communities Based on Social Network Context

https://irjet.net/archives/V4/i3/IRJET-V4I3111.pdf
Profile Analysis of Users in Data Analytics Domain

Data Analytics and Data Science is in the fast forward
mode recently. We see a lot of companies hiring people for data
analysis and data science, especially in India. Also, many
recruiting firms use stackoverflow to fish their potential
candidates. The industry has also started to recruit people based
on the shapes of expertise. Expertise of a personal is
metaphorically outlined by shapes of letters like I, T, M and
hyphen betting on her experiencein a section (depth) and
therefore the variety of areas of interest (width).This proposal
builds upon the work of mining shapes of user expertise in a
typical online social Question and Answer (Q&A) community
where expert users often answer questions posed by other
users.We have dealt with the temporal analysis of the expertise
among the Q&A community users in terms how the user/ expert
have evolved over time.
Keywords— Shapes of expertise, Graph communities, Expertise
evolution, Q&A community
Review and analysis of machine learning and soft computing approaches for use...

The adequacy of user models depends mainly on the accuracy and precision of information that is retrieved to the user. The real challenge in user modelling studies is due to the inadequacy of data, improper use of techniques, noise within the data and imprecise nature of human behavior. For the best results of user modelling, one should choose an appropriate way to do it i.e. by selecting the best suitable approach for the desired domain. Machine learning and Soft computing Techniques have the ability to handle the uncertainty and are extensively being used for user modeling purpose. This paper reviews various approaches of user modeling and critically analyzes the machine learning and soft computing techniques that have successfully captured and formally modelled the human behavior.
Systems Analysis and Design 8th Edition Kendall Solutions Manual

Full download : http://alibabadownload.com/product/systems-analysis-and-design-8th-edition-kendall-solutions-manual/ Systems Analysis and Design 8th Edition Kendall Solutions Manual
INTELLIGENT SOCIAL NETWORKS MODEL BASED ON SEMANTIC TAG RANKING

Social Networks has become one of the most popular platforms to allow users to communicate, and share their interests without being at the same geographical location. With the great and rapid growth of Social Media sites such as Facebook, LinkedIn, Twitter…etc. causes huge amount of user-generated content. Thus, the improvement in the information quality and integrity becomes a great challenge to all social media sites, which allows users to get the desired content or be linked to the best link relation using improved search / link technique. So introducing semantics to social networks will widen up the representation of the social networks. In this paper, a new model of social networks based on semantic tag ranking is introduced. This model is based on the concept of multi-agent systems. In this proposed model the representation of social links will be extended by the semantic relationships found in the vocabularies which are known as (tags) in most of social networks.The proposed model for the social media engine is based on enhanced Latent Dirichlet Allocation(E-LDA) as a semantic indexing algorithm, combined with Tag Rank as social network ranking algorithm. The improvements on (E-LDA) phase is done by optimizing (LDA) algorithm using the optimal parameters. Then a filter is introduced to enhance the final indexing output. In ranking phase, using Tag Rank based on the indexing phase has improved the output of the ranking. Simulation results of the proposed model have shown improvements in indexing and ranking output.
INTELLIGENT SOCIAL NETWORKS MODEL BASED ON SEMANTIC TAG RANKING

Social Networks has become one of the most popular platforms to allow users to communicate, and share their interests without being at the same geographical location. With the great and rapid growth of Social Media sites such as Facebook, LinkedIn, Twitter…etc. causes huge amount of user-generated content. Thus, the improvement in the information quality and integrity becomes a great challenge to all social media sites, which allows users to get the desired content or be linked to the best link relation using improved search / link technique. So introducing semantics to social networks will widen up the representation of the social networks. In this paper, a new model of social networks based on semantic tag ranking is introduced. This model is based on the concept of multi-agent systems. In this proposed model the representation of social links will be extended by the semantic relationships found in the vocabularies which are known as (tags) in most of social networks.The proposed model for the social media engine is based on enhanced Latent Dirichlet Allocation(E-LDA) as a semantic indexing algorithm, combined with Tag Rank as social network ranking algorithm. The improvements on (E-LDA) phase is done by optimizing (LDA) algorithm using the optimal parameters. Then a filter is introduced to enhance the final indexing output. In ranking phase, using Tag Rank based on the indexing phase has improved the output of the ranking. Simulation results of the proposed model have shown improvements in indexing and ranking output.
INTELLIGENT SOCIAL NETWORKS MODEL BASED ON SEMANTIC TAG RANKING

Social Networks has become one of the most popular platforms to allow users to communicate, and share
their interests without being at the same geographical location. With the great and rapid growth of Social
Media sites such as Facebook, LinkedIn, Twitter...etc. causes huge amount of user-generated content.
Thus, the improvement in the information quality and integrity becomes a great challenge to all social
media sites, which allows users to get the desired content or be linked to the best link relation using
improved search / link technique. So introducing semantics to social networks will widen up the
representation of the social networks.
Current trends of opinion mining and sentiment analysis in social networks

IJRET : International Journal of Research in Engineering and Technology is an international peer reviewed, online journal published by eSAT Publishing House for the enhancement of research in various disciplines of Engineering and Technology. The aim and scope of the journal is to provide an academic medium and an important reference for the advancement and dissemination of research results that support high-level learning, teaching and research in the fields of Engineering and Technology. We bring together Scientists, Academician, Field Engineers, Scholars and Students of related fields of Engineering and Technology
Sq lite module4

Module 4 out of 9; SQLite training slides, databases, SQL, ERD, software design, database
Local Service Search Engine Management System LSSEMS

Local Services Search Engine Management System LSSEMS is a web based application which helps user to find serviceman in a local area such as maid, tuition teacher, plumber etc. LSSEMS contain data of serviceman maid, tuition teacher, plumber etc. . The main purpose of LSSEMS is to systematically record, store and update the serviceman records. Kaushik Mishra | Aditya Sharma | Mohak Gund "Local Service Search Engine Management System (LSSEMS)" Published in International Journal of Trend in Scientific Research and Development (ijtsrd), ISSN: 2456-6470, Special Issue | International Conference on Advances in Engineering, Science and Technology - 2021 , May 2021, URL: https://www.ijtsrd.com/papers/ijtsrd42462.pdf Paper URL : https://www.ijtsrd.com/engineering/computer-engineering/42462/local-service-search-engine-management-system-lssems/kaushik-mishra
Similar to Fundamentals of Database Systems Questions and Answers (20)
Identity Resolution across Different Social Networks using Similarity Analysis

Identity Resolution across Different Social Networks using Similarity Analysis
Social Friend Overlying Communities Based on Social Network Context

Social Friend Overlying Communities Based on Social Network Context
Profile Analysis of Users in Data Analytics Domain

Profile Analysis of Users in Data Analytics Domain
Review and analysis of machine learning and soft computing approaches for use...

Review and analysis of machine learning and soft computing approaches for use...
Systems Analysis and Design 8th Edition Kendall Solutions Manual

Systems Analysis and Design 8th Edition Kendall Solutions Manual
INTELLIGENT SOCIAL NETWORKS MODEL BASED ON SEMANTIC TAG RANKING

INTELLIGENT SOCIAL NETWORKS MODEL BASED ON SEMANTIC TAG RANKING
INTELLIGENT SOCIAL NETWORKS MODEL BASED ON SEMANTIC TAG RANKING

INTELLIGENT SOCIAL NETWORKS MODEL BASED ON SEMANTIC TAG RANKING
INTELLIGENT SOCIAL NETWORKS MODEL BASED ON SEMANTIC TAG RANKING

INTELLIGENT SOCIAL NETWORKS MODEL BASED ON SEMANTIC TAG RANKING
Current trends of opinion mining and sentiment analysis in social networks

Current trends of opinion mining and sentiment analysis in social networks
EffectiveCrowdSourcingForProductFeatureIdeation v18

EffectiveCrowdSourcingForProductFeatureIdeation v18
Local Service Search Engine Management System LSSEMS

Local Service Search Engine Management System LSSEMS
More from Abdul Rahman Sherzad
Data is the Fuel of Organizations: Opportunities and Challenges in Afghanistan

A car without fuel cannot be driven; a mobile, a laptop or a PC without power cannot be used; a website without feeding won't have any visitors; likewise, an organization without data will not stand and cannot be survived.
The data quickly becoming one of the most important resources for any country, company, or organizations. It is the data that enables organizations to explain the past and guess the future through data science and business intelligence tools.
This presentation demonstrates how the Kankor data can be used as a resource in the context of Afghanistan, particularly, the candidates’ names that organizations in Afghanistan do not use for anything.
Read the following paper for more information and examples:
https://www.researchgate.net/publication/322695084_Data_is_the_Fuel_of_Organizations_Opportunities_and_Challenges_in_Afghanistan
PHP Unicode Input Validation Snippets

These useful functions/snippets enable you to validate Unicode characters such as Digits, Person names, and Text mainly used in Afghanistan and Iran.
Feature list:
* Validate Person names commonly used in Afghanistan and Iran. Person names may be in Persian/Dari, Arabic, and English and similar languages;
* Validate only Persian Text;
* Validate only Pashtu Text;
* Validate digit in Persian/Dari, Pashtu and Arabic format;
* Validate digit in all common formats.
Iterations and Recursions

This presentation explains and solves problems such as Factorial, Fibonacci, Greatest Common Divisor, Binary Search, and Traversing Directory and Sub-Directories in both recursion and iteration.
In summary, there are similarities between recursion and iteration. Hence, any problems that can be solved with iterations can be solved with recursions and vice versa.
Sorting Alpha Numeric Data in MySQL

In SQL, the ORDER BY keyword is used to sort the result-set in ascending (ASC) or descending (DESC) order by some specified column/columns.
It works great for most of the cases. However, for alphanumeric data, it may not return the result-set that you will be expecting.
This presentation explains how this can be addressed using different techniques.
PHP Variable variables Examples

In PHP, variable variables take the value of one variable, and treat that as the name of another variable.
Variable variables are just variables whose names can be programmatically set and accessed. Hence, they are also called dynamic variable names.
Cross Join Example and Applications

Cross joins are used to return every combination of rows from two and more than two tables. Cross Joins are sometimes called a Cartesian product. This presentation illustrates cross join examples and applications in real life.
Applicability of Educational Data Mining in Afghanistan: Opportunities and Ch...

Applicability of Educational Data Mining in Afghanistan: Opportunities and Ch...Abdul Rahman Sherzad
The increase in enrollment in education and higher education institutions, the increase in the use of the Internet as well as the emergence of technology in educational systems have led to the aggregation of large amounts of student data at educational institutions (schools, colleges, and universities), which makes it vital to use data mining methods to improve the educational settings.
Although educational institutions collect an enormous amount of student data, this data is utilized to produce basic insights and is not used for decisions to improve the educational settings.
To get essential benefits from the data, powerful techniques are required to extract the useful knowledge which is valuable and significant for the decision and policy makers.Web Application Security and Awareness

Secure web programming plus end users' awareness are the last line of defense against attacks targeted at the corporate systems, particularly web applications, in the era of world-wide web.
Most web application attacks occur through Cross Site Scripting (XSS), and SQL Injection. On the other hand, most web application vulnerabilities arise from weak coding with failure to properly validate users' input, and failure to properly sanitize output while displaying the data to the visitors.
The literature also confirms the following web application weaknesses in 2010: 26% improper output handling, 22% improper input handling, and 15% insufficient authentication, and others.
Abdul Rahman Sherzad, lecturer at Computer Science Faculty of Herat University, and Ph.D. student at Technical University of Berlin gave a presentation at 12th IT conference on Higher Education for Afghanistan in MoHE, and then conducted a seminar at Hariwa Institute of Higher Education in Herat, Afghanistan introducing web application security threats by demonstrating the security problems that exist in corporate systems with a strong emphasis on secure development. Major security vulnerabilities, secure design and coding best practices when designing and developing web-based applications were covered.
The main objective of the presentation was raising awareness about the problems that might occur in web-application systems, as well as secure coding practices and principles. The presentation's aims were to build security awareness for web applications, to discuss the threat landscape and the controls users should use during the software development lifecycle, to introduce attack methods, to discuss approaches for discovering security vulnerabilities, and finally to discuss the basics of secure web development techniques and principles.
Database Automation with MySQL Triggers and Event Schedulers

This advanced training seminar on "Database Automation using MySQL Triggers and Event Schedulers" is dedicated to the Computer Science graduates and students of both public and private universities.
In this seminar we are going to look in depth at MySQL Triggers and Event Schedulers– powerful features supported by most popular commercial and open source relational database systems.
The Triggers are powerful tools for protecting the integrity of the data in the databases, logging and auditing of the changes on data, business logic, perform calculations, run further SQL commands, etc.
The Events are very useful to automate some database operations such as optimizing database tables, cleaning up logs, archiving data, or generate complex reports during off-peak time, etc.
The participants will learn about the true concept, implementation and application of MySQL Triggers and Event Schedulers with real life examples and scenarios.
They will also learn how to use the database triggers and event schedulers in many real cases to automate database tasks - such as optimizing database tables, cleaning up logs, archiving data, or generate complex reports during off-peak time.
This seminar is presented by Abdul Rahman Sherzad lecturer at Computer Science faculty of Herat University, and PhD Student at Technical University of Berlin, Germany at Hariwa Institute of Higher Education, Herat, Afghanistan.
Mobile Score Notification System

Education is one of the main pillars and key concerns for each society in general. In developing countries, in particular in Afghanistan, we observe a remarkable increase in enrollment in education and higher education institutions, but most of the students don't have proper access to their scores. For instance, while Kankor result is announced the vast amounts of traffic the visitors generate make the website completely down and inaccessible. Another example, There is no efficient method to access the university scores in particular for students from other provinces. Last but not least, Diploma and certification verification is a lengthy and complicated process, when graduated students apply for jobs and scholarships inside or outside of Afghanistan they are asked to provide their certificate and diploma. One of the solutions can be verification of the graduation documents through SMS.
In Herat Innovation Lab 2015, Education group members under the mentorship of Abdul Rahman Sherzad chose this social and educational domain problem and within three days they designed and developed a prototype solution that enable students to access i.e. Kankor Scores Result, University Scores Result, Faculties Announcements and Events, and Certificate/Diploma Verification via SMS, Mobile and Web Applications effectively and efficiently.
Herat Innovation Lab 2015

Innovation Labs (iLabs) is a social innovation program covering a series of conferences. One the one hand, the goal is to bring social and technology experts together for the networking purpose. On the other hand, the motivation is to harness technology to solve the most challenging social and environmental problems and to build tech-based systems.
Evaluation of Existing Web Structure of Afghan Universities

This presentation looks into the existing web structure and services of all Afghan universities, not only to evaluate the entire infrastructure but also to systematically analyze the gaps and design challenges of web platforms and services as a means of communication and collaboration among various stakeholders including the Ministry of Higher Education, its subsidiaries, students and other related audience.
The presentation finds that the environment for necessary ICT infrastructure and services is up to the expected required standard to provide access to various online resources and systems. The next important finding is the increasing demand by students to access information online rather than the existing traditional paper-based systems. Another very important finding is related to the non-existence of a formal managerial oversight to all the online resources and thus has resulted to a very poor quality of content, outdated information and the services that don't meet the expected needs and challenges.
PHP Basic and Fundamental Questions and Answers with Detail Explanation

These PHP basic and fundamental questions and answers with detail explanation help students and learners to think comprehensive, and to seek more to understand the concept and the root of each topic concretely.
Java Applet and Graphics

This presentation introduces Java Applet and Java Graphics in detail with examples and finally using the concept of both applet and graphics code the analog clock project to depict how to use them in real life challenges and applications.
Everything about Database JOINS and Relationships

Today, we continue our journey into the world of RDBMS (relational database management systems) and SQL (Structured Query Language).
In this presentation, you will understand about some key definitions and then you will learn how to work with multiple tables that have relationships with each other.
First, we will go covering some core concepts and key definitions, and then will begin working with JOINs queries in SQL.
Create Splash Screen with Java Step by Step

This presentation guide you how to make a custom Splash Screen step by step using Java Programming. In addition, you will learn the concept and usage of Java Timer, Java Progress Bar and Window ...
Fal-e-Hafez (Omens of Hafez) Cards in Persian using Java

This presentation explains step by step how to develop and code Fal-e Hafez (Omens of Hafez) Cards in Persian Using JAVA. There are several applications which are coded by different programming languages i.e. Java languages for Desktops and Mobiles, HTML and CSS and PHP for Web Pages, etc. and this shows the importance of Omens of Hafez among the Persian people.
Web Design and Development Life Cycle and Technologies

This presentation is an introduction to the design, creation, and maintenance of web design and development life cycle and web technologies. With it, you will learn about the web technologies, the life cycle of developing an efficient website and web application and finally some web essentials questions will be provided and reviewed.
Java Virtual Keyboard Using Robot, Toolkit and JToggleButton Classes

A Virtual Keyboard is considered to be a component to use on computers without a real keyboard e.g. Touch Screen Computers and Smart Phones; where a mouse can utilize the keyboard functionalities and features.
In addition, Virtual Keyboard used for the following subjects: Foreign Character Sets, Touchscreen, Bypass Key Loggers, etc.
Java Unicode with Live GUI Examples

With Unicode you can program and accomplish many funny, cool and useful programs and tools as for instance, Abjad Calculator, Bubble Text Generator to write letters in circle, Flip Text Generator to write letters upside down, Google Transliteration to convert English names to Persian/Arabic, etc...
More from Abdul Rahman Sherzad (20)
Data is the Fuel of Organizations: Opportunities and Challenges in Afghanistan

Data is the Fuel of Organizations: Opportunities and Challenges in Afghanistan
Applicability of Educational Data Mining in Afghanistan: Opportunities and Ch...

Applicability of Educational Data Mining in Afghanistan: Opportunities and Ch...
Database Automation with MySQL Triggers and Event Schedulers

Database Automation with MySQL Triggers and Event Schedulers
Evaluation of Existing Web Structure of Afghan Universities

Evaluation of Existing Web Structure of Afghan Universities
PHP Basic and Fundamental Questions and Answers with Detail Explanation

PHP Basic and Fundamental Questions and Answers with Detail Explanation
Fal-e-Hafez (Omens of Hafez) Cards in Persian using Java

Fal-e-Hafez (Omens of Hafez) Cards in Persian using Java
Web Design and Development Life Cycle and Technologies

Web Design and Development Life Cycle and Technologies
Java Virtual Keyboard Using Robot, Toolkit and JToggleButton Classes

Java Virtual Keyboard Using Robot, Toolkit and JToggleButton Classes
Recently uploaded
The French Revolution Class 9 Study Material pdf free download

The French Revolution, which began in 1789, was a period of radical social and political upheaval in France. It marked the decline of absolute monarchies, the rise of secular and democratic republics, and the eventual rise of Napoleon Bonaparte. This revolutionary period is crucial in understanding the transition from feudalism to modernity in Europe.
For more information, visit-www.vavaclasses.com
Introduction to AI for Nonprofits with Tapp Network

Dive into the world of AI! Experts Jon Hill and Tareq Monaur will guide you through AI's role in enhancing nonprofit websites and basic marketing strategies, making it easy to understand and apply.
2024.06.01 Introducing a competency framework for languag learning materials ...

http://sandymillin.wordpress.com/iateflwebinar2024
Published classroom materials form the basis of syllabuses, drive teacher professional development, and have a potentially huge influence on learners, teachers and education systems. All teachers also create their own materials, whether a few sentences on a blackboard, a highly-structured fully-realised online course, or anything in between. Despite this, the knowledge and skills needed to create effective language learning materials are rarely part of teacher training, and are mostly learnt by trial and error.
Knowledge and skills frameworks, generally called competency frameworks, for ELT teachers, trainers and managers have existed for a few years now. However, until I created one for my MA dissertation, there wasn’t one drawing together what we need to know and do to be able to effectively produce language learning materials.
This webinar will introduce you to my framework, highlighting the key competencies I identified from my research. It will also show how anybody involved in language teaching (any language, not just English!), teacher training, managing schools or developing language learning materials can benefit from using the framework.
Biological Screening of Herbal Drugs in detailed.

Biological screening of herbal drugs: Introduction and Need for
Phyto-Pharmacological Screening, New Strategies for evaluating
Natural Products, In vitro evaluation techniques for Antioxidants, Antimicrobial and Anticancer drugs. In vivo evaluation techniques
for Anti-inflammatory, Antiulcer, Anticancer, Wound healing, Antidiabetic, Hepatoprotective, Cardio protective, Diuretics and
Antifertility, Toxicity studies as per OECD guidelines
Unit 8 - Information and Communication Technology (Paper I).pdf

This slides describes the basic concepts of ICT, basics of Email, Emerging Technology and Digital Initiatives in Education. This presentations aligns with the UGC Paper I syllabus.
Embracing GenAI - A Strategic Imperative

Artificial Intelligence (AI) technologies such as Generative AI, Image Generators and Large Language Models have had a dramatic impact on teaching, learning and assessment over the past 18 months. The most immediate threat AI posed was to Academic Integrity with Higher Education Institutes (HEIs) focusing their efforts on combating the use of GenAI in assessment. Guidelines were developed for staff and students, policies put in place too. Innovative educators have forged paths in the use of Generative AI for teaching, learning and assessments leading to pockets of transformation springing up across HEIs, often with little or no top-down guidance, support or direction.
This Gasta posits a strategic approach to integrating AI into HEIs to prepare staff, students and the curriculum for an evolving world and workplace. We will highlight the advantages of working with these technologies beyond the realm of teaching, learning and assessment by considering prompt engineering skills, industry impact, curriculum changes, and the need for staff upskilling. In contrast, not engaging strategically with Generative AI poses risks, including falling behind peers, missed opportunities and failing to ensure our graduates remain employable. The rapid evolution of AI technologies necessitates a proactive and strategic approach if we are to remain relevant.
June 3, 2024 Anti-Semitism Letter Sent to MIT President Kornbluth and MIT Cor...

Letter from the Congress of the United States regarding Anti-Semitism sent June 3rd to MIT President Sally Kornbluth, MIT Corp Chair, Mark Gorenberg
Dear Dr. Kornbluth and Mr. Gorenberg,
The US House of Representatives is deeply concerned by ongoing and pervasive acts of antisemitic
harassment and intimidation at the Massachusetts Institute of Technology (MIT). Failing to act decisively to ensure a safe learning environment for all students would be a grave dereliction of your responsibilities as President of MIT and Chair of the MIT Corporation.
This Congress will not stand idly by and allow an environment hostile to Jewish students to persist. The House believes that your institution is in violation of Title VI of the Civil Rights Act, and the inability or
unwillingness to rectify this violation through action requires accountability.
Postsecondary education is a unique opportunity for students to learn and have their ideas and beliefs challenged. However, universities receiving hundreds of millions of federal funds annually have denied
students that opportunity and have been hijacked to become venues for the promotion of terrorism, antisemitic harassment and intimidation, unlawful encampments, and in some cases, assaults and riots.
The House of Representatives will not countenance the use of federal funds to indoctrinate students into hateful, antisemitic, anti-American supporters of terrorism. Investigations into campus antisemitism by the Committee on Education and the Workforce and the Committee on Ways and Means have been expanded into a Congress-wide probe across all relevant jurisdictions to address this national crisis. The undersigned Committees will conduct oversight into the use of federal funds at MIT and its learning environment under authorities granted to each Committee.
• The Committee on Education and the Workforce has been investigating your institution since December 7, 2023. The Committee has broad jurisdiction over postsecondary education, including its compliance with Title VI of the Civil Rights Act, campus safety concerns over disruptions to the learning environment, and the awarding of federal student aid under the Higher Education Act.
• The Committee on Oversight and Accountability is investigating the sources of funding and other support flowing to groups espousing pro-Hamas propaganda and engaged in antisemitic harassment and intimidation of students. The Committee on Oversight and Accountability is the principal oversight committee of the US House of Representatives and has broad authority to investigate “any matter” at “any time” under House Rule X.
• The Committee on Ways and Means has been investigating several universities since November 15, 2023, when the Committee held a hearing entitled From Ivory Towers to Dark Corners: Investigating the Nexus Between Antisemitism, Tax-Exempt Universities, and Terror Financing. The Committee followed the hearing with letters to those institutions on January 10, 202
The approach at University of Liverpool.pptx

How libraries can support authors with open access requirements for UKRI funded books
Wednesday 22 May 2024, 14:00-15:00.
How to Make a Field invisible in Odoo 17

It is possible to hide or invisible some fields in odoo. Commonly using “invisible” attribute in the field definition to invisible the fields. This slide will show how to make a field invisible in odoo 17.
Model Attribute Check Company Auto Property

In Odoo, the multi-company feature allows you to manage multiple companies within a single Odoo database instance. Each company can have its own configurations while still sharing common resources such as products, customers, and suppliers.
CACJapan - GROUP Presentation 1- Wk 4.pdf

Macroeconomics- Movie Location
This will be used as part of your Personal Professional Portfolio once graded.
Objective:
Prepare a presentation or a paper using research, basic comparative analysis, data organization and application of economic information. You will make an informed assessment of an economic climate outside of the United States to accomplish an entertainment industry objective.
Digital Tools and AI for Teaching Learning and Research

This Presentation in details discusses on Digital Tools and AI for Teaching Learning and Research
How libraries can support authors with open access requirements for UKRI fund...

How libraries can support authors with open access requirements for UKRI funded books
Wednesday 22 May 2024, 14:00-15:00.
Honest Reviews of Tim Han LMA Course Program.pptx

Personal development courses are widely available today, with each one promising life-changing outcomes. Tim Han’s Life Mastery Achievers (LMA) Course has drawn a lot of interest. In addition to offering my frank assessment of Success Insider’s LMA Course, this piece examines the course’s effects via a variety of Tim Han LMA course reviews and Success Insider comments.
Mule 4.6 & Java 17 Upgrade | MuleSoft Mysore Meetup #46

Mule 4.6 & Java 17 Upgrade | MuleSoft Mysore Meetup #46
Event Link:-
https://meetups.mulesoft.com/events/details/mulesoft-mysore-presents-exploring-gemini-ai-and-integration-with-mulesoft/
Agenda
● Java 17 Upgrade Overview
● Why and by when do customers need to upgrade to Java 17?
● Is there any immediate impact to upgrading to Mule Runtime 4.6 and beyond?
● Which MuleSoft products are in scope?
For Upcoming Meetups Join Mysore Meetup Group - https://meetups.mulesoft.com/mysore/
YouTube:- youtube.com/@mulesoftmysore
Mysore WhatsApp group:- https://chat.whatsapp.com/EhqtHtCC75vCAX7gaO842N
Speaker:-
Shubham Chaurasia - https://www.linkedin.com/in/shubhamchaurasia1/
Priya Shaw - https://www.linkedin.com/in/priya-shaw
Organizers:-
Shubham Chaurasia - https://www.linkedin.com/in/shubhamchaurasia1/
Giridhar Meka - https://www.linkedin.com/in/giridharmeka
Priya Shaw - https://www.linkedin.com/in/priya-shaw
Shyam Raj Prasad-
https://www.linkedin.com/in/shyam-raj-prasad/
Recently uploaded (20)
The French Revolution Class 9 Study Material pdf free download

The French Revolution Class 9 Study Material pdf free download
Introduction to AI for Nonprofits with Tapp Network

Introduction to AI for Nonprofits with Tapp Network
2024.06.01 Introducing a competency framework for languag learning materials ...

2024.06.01 Introducing a competency framework for languag learning materials ...
Unit 8 - Information and Communication Technology (Paper I).pdf

Unit 8 - Information and Communication Technology (Paper I).pdf
June 3, 2024 Anti-Semitism Letter Sent to MIT President Kornbluth and MIT Cor...

June 3, 2024 Anti-Semitism Letter Sent to MIT President Kornbluth and MIT Cor...
Adversarial Attention Modeling for Multi-dimensional Emotion Regression.pdf

Adversarial Attention Modeling for Multi-dimensional Emotion Regression.pdf
Digital Tools and AI for Teaching Learning and Research

Digital Tools and AI for Teaching Learning and Research
How libraries can support authors with open access requirements for UKRI fund...

How libraries can support authors with open access requirements for UKRI fund...
Mule 4.6 & Java 17 Upgrade | MuleSoft Mysore Meetup #46

Mule 4.6 & Java 17 Upgrade | MuleSoft Mysore Meetup #46
Fundamentals of Database Systems Questions and Answers
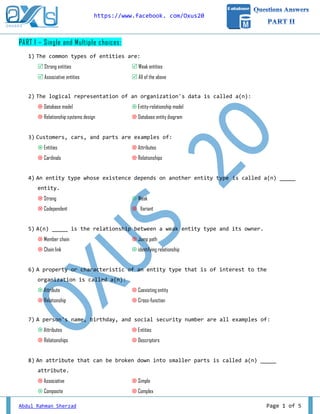
- 1. https://www.facebook. com/Oxus20 Abdul Rahman Sherzad Page 1 of 5 PART I – Single and Multiple choices: 1) The common types of entities are: Strong entities Weak entities Associative entities All of the above 2) The logical representation of an organization's data is called a(n): Database model Entity-relationship model Relationship systems design Database entity diagram 3) Customers, cars, and parts are examples of: Entities Attributes Cardinals Relationships 4) An entity type whose existence depends on another entity type is called a(n) _____ entity. Strong Weak Codependent Variant 5) A(n) _____ is the relationship between a weak entity type and its owner. Member chain Jump path Chain link identifying relationship 6) A property or characteristic of an entity type that is of interest to the organization is called a(n): Attribute Coexisting entity Relationship Cross-function 7) A person's name, birthday, and social security number are all examples of: Attributes Entities Relationships Descriptors 8) An attribute that can be broken down into smaller parts is called a(n) _____ attribute. Associative Simple Composite Complex
- 2. https://www.facebook. com/Oxus20 Abdul Rahman Sherzad Page 2 of 5 9) The following figure shows an example of: A composite attribute A relational attribute A derived attribute A multivalued attribute 10) An attribute that can be calculated from related attribute values is called a(n) _____ attribute. Simple Composite Multivalued Derived 11) The total quiz points for a student for an entire semester is a(n) _____ attribute. Derived Mixed Stored Addressed 12) Which of the following criteria should be considered when selecting an identifier? Choose an identifier that is stable Choose an identifier that will not be null Choose an identifier that doesn’t have large composite attributes All of the above 13) Which of the following conditions should exist if an associative entity is to be created? All the relationships for the participating entities are many-to-many The new associative entity has independent meaning The new associative entity participates in independent relationships All of the above
- 3. https://www.facebook. com/Oxus20 Abdul Rahman Sherzad Page 3 of 5 14) The number of entity types that participate in a relationship is called the: Number identifying characteristic Degree Counter 15) A relationship between the instances of a single entity type is called a(n) _____ relationship. Ternary Primary Binary Unary Part II - Basic Terms and Data Model: 1) Persons can take the following roles around database systems: End users DB designers DB administrators Application Programmers Decide for each of the following activities, to which role it belongs by writing the respective number in the box. Developing the conceptual schema Managing user accounts, hardware resources, and backups during the lifetime of the database Programming of software that is using the database Choice of DBMS Analyze requirements for the database Programming of a graphical user interface for the database Gathering of information about the application field
- 4. https://www.facebook. com/Oxus20 Abdul Rahman Sherzad Page 4 of 5 2) Classification of Database Management Systems: a) Name three different data models that can be used in DBMS: Relational Model Object Relational Model Network Model b) Which data model is used by MySQL? Relational Model c) Is MySQL a single-user or a multi-user DBMS? Multi-User Part III – ER to Relational Mapping: 1) Name and explain in brief (just briefly), the steps that are needed to transform an ER diagram into a relational schema. 1. Mapping Strong Entities 2. Mapping Weak Entities 3. Mapping One-to-One relationship 4. Mapping One-to-Many relationship 5. Mapping Many-to-Many relationship 6. Mapping Multi-Valued attributes 7. Mapping N-ary relationship
- 5. https://www.facebook. com/Oxus20 Abdul Rahman Sherzad Page 5 of 5 Part IV – Challenges: 1) You have the following two figures. Both using the one-to-many relation but in different ways. Are they the same? Yes / No, Give reason. Using the above "One-to-Many" relationship the implementation is simple and easy; but support one depth and level of relationship, as for instance, a sub-forum can't have other sub-forums! Using the above recursive relationship it supports both one level and as many level as possible of nested relationships. For instance, a forum can have a sub-forum; the sub-forum still can have other sub-forums and yet that other sub-forums can have sub-forums and so on, so forth. 2) There is something wrong with the following query (The problem is the single quotation-marks with the string). Try to rewrite it with correct syntax using two different methods. SELECT * FROM lecturers WHERE signatory = 'If you tell the truth, you don't have to remember anything'; SELECT * FROM lecturers WHERE signatory = "If you tell the truth, you don't have to remember anything"; SELECT * FROM lecturers WHERE signatory = 'If you tell the truth, you don't have to remember anything'; Forum Sub Forumhas 1 m Forum has 1 mmain sub Figure 1 - One-to-Man Figure 2 - Recursive
- 6. OXUS20 is a non-profit society with the aim of changing education for the better by providing education and assistance to IT and computer science professionals. آکعیَض02یکاًجويغیراًتفاعیتاّذفتمَیت ٍتغییرپرٍرغ ٍ آهَزغطریك ازِارائآهَزغٍکوکِت هتخصصاىعلَمکاهپیَتراظت. ایي ًاماًجويپر َآه دریای از ِترگرفتآى هَج دظت ِک ًِهیا آظیای رٍد تریي آبتیاًگراظتعذادایي ًِْفت ّایاًجويُتَد،از دریا ایي ٍ هاٍرای ٍ ِگرفت ِظرچؽو پاهیر کْي ّای ٌِداهخذهات ِارای ّذف دریا حالت ایي ِک هیکٌذ آتیاری را افغاًعتاى تاظتاًی ظرزهیي ؼوالی اًجوياًعکاض را.هیذّذ آکعیَض02هاًٌذ خذهاتی تا دارد ًظر درایجادفضایعلوی ؼکَفایی ٍ خاللیت تراًگیختي ٍ اظتعذادّا تجلی ترای هٌاظةداًػ ٍ هحصالى ،پصٍّاىٍ علوی ِترًاه فَق ّای فعالیت ظاختي ًْادهٌذ،کارتردیؼٌاظاییعاللوٌذ ٍ ًِخث ،خالق افراددر آًْا هؽارکت از گیری ُتْر ٍ علوی فضای ارتمایٍ تَلیذ ّوچَى ِجاهع ٍ آهَزؼی هراکس دیگر ٍ ّا پٌَّتَىتخصصی علوی ًؽریات اًتؽارتکٌالَشی ٍ عصری علَم هَثر ؼکل ِت را هعلَهاتیِجاهع افراد آهال ِت رظیذى ّای ُرا ٍ پصٍّػ ٍ تحمیك ،تذریط ٌِزهی ؼذى تْتر ِّرچ راظتای در ِجاهع در آى .هیعازد فراّن را Follow us on Facebook, https://www.facebook.com/Oxus20
