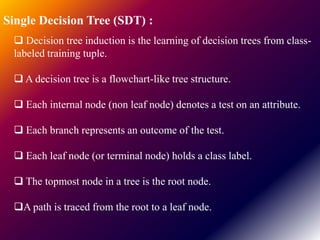
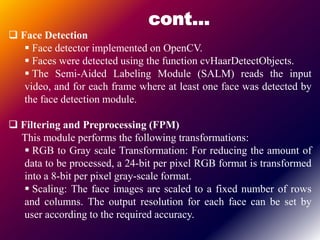
Face recognition technology uses machine learning algorithms to identify or verify a person's identity from digital images or video frames. The process involves detecting faces, applying preprocessing techniques like filtering and scaling, training classifiers using labeled face images, and then classifying new faces. Common machine learning algorithms used include K-nearest neighbors, naive Bayes, decision trees, and locally weighted learning. The proposed system detects faces, builds a tabular dataset from pixel values, trains classifiers, and evaluates performance on a test set. Software applies techniques like detection, alignment, normalization, and matching to encode faces for comparison. Face recognition has advantages like convenience and low cost, and applications in security, banking, and more.